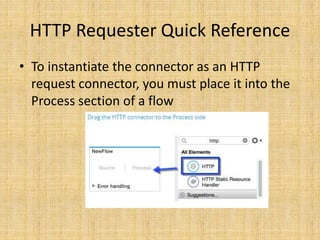
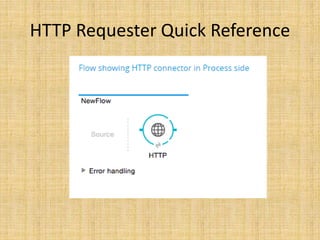
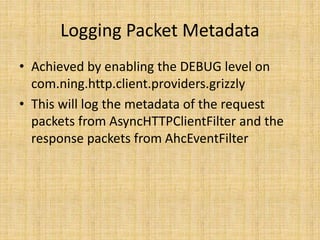
The HTTP connector can be used as an HTTP listener connector to receive HTTP requests at a specified address and generate responses, or as an HTTP requester connector to send requests to an address and receive responses. It supports TLS encryption for HTTPS and authentication via basic, digest, and OAuth. When used as a listener, it is placed in the source of a flow, and as a requester, in the process section. Debugging HTTP activity can be done by enabling loggers for listener/request activity and packet metadata. The connector also supports non-blocking processing.