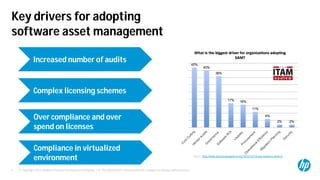
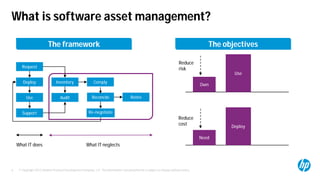
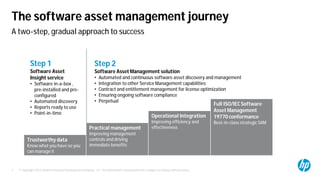
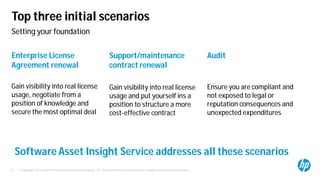
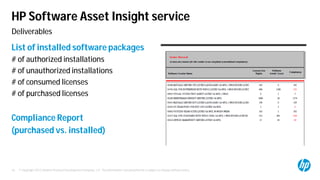
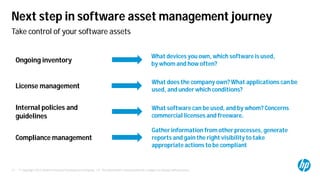
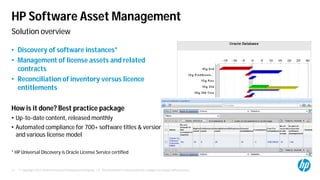
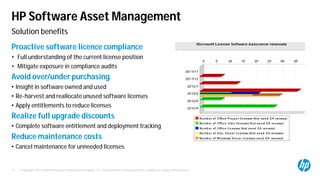
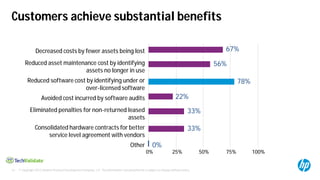
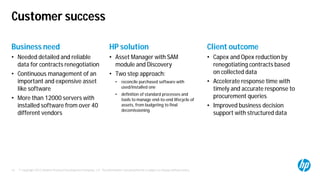
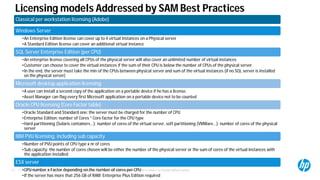
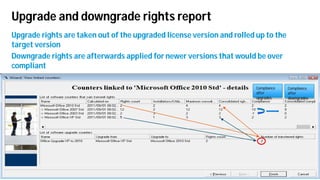
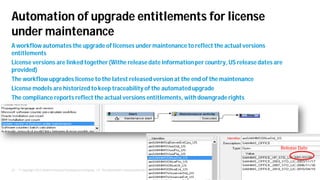
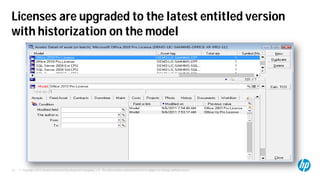
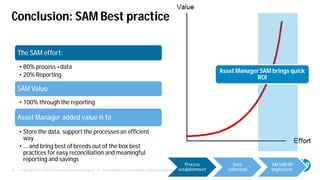
The document discusses HP's software asset management (SAM) strategies presented at the 2013 Software Performance Tour in Baveno, Italy, highlighting the importance of compliance and cost reduction. It covers the benefits of adopting SAM practices, such as inventory management, license compliance, and efficient usage of software assets to mitigate risks associated with vendor audits and over-spending. HP offers comprehensive solutions for organizations to manage their software assets effectively, ensuring proper licensing and reducing ongoing costs.