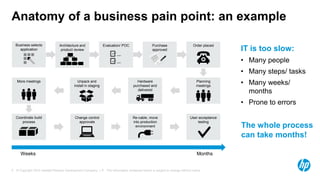
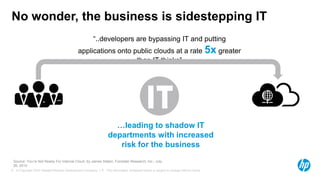
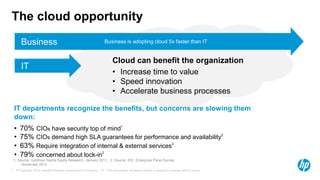
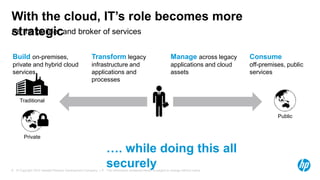
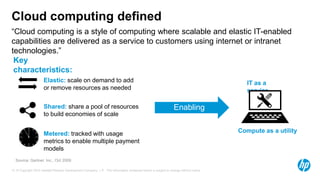
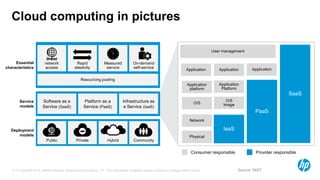
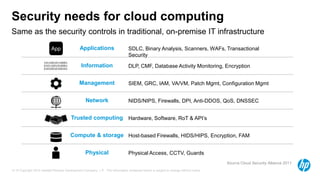
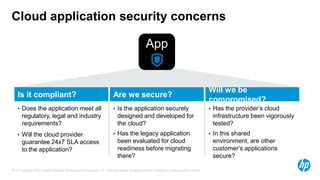
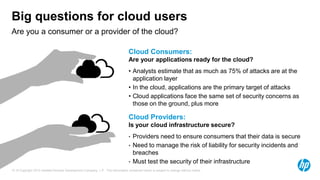
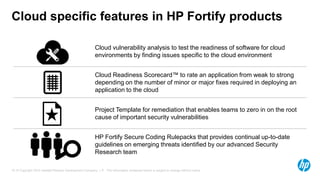
This document discusses the rise of cloud computing and the opportunities and challenges it presents for businesses and IT departments. It notes that businesses are increasingly adopting cloud technologies at a faster rate than IT can support due to the speed and agility benefits of the cloud. However, IT concerns around security, compliance, and control are slowing cloud adoption. The document proposes that providing trusted cloud services that address these IT concerns can help enable broader cloud usage and allow businesses to realize the economic and innovation benefits of the cloud while allowing IT to play a more strategic role.