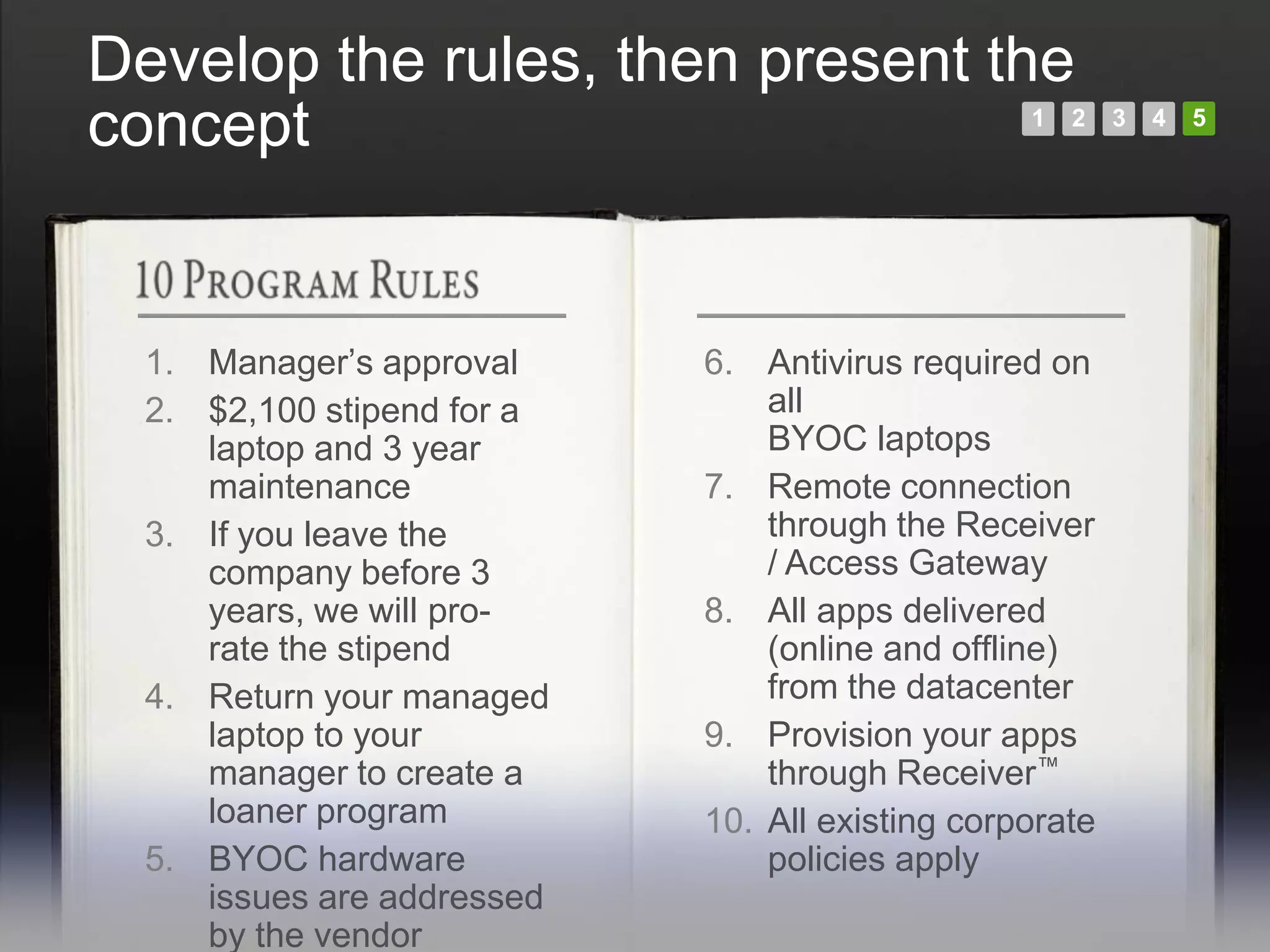
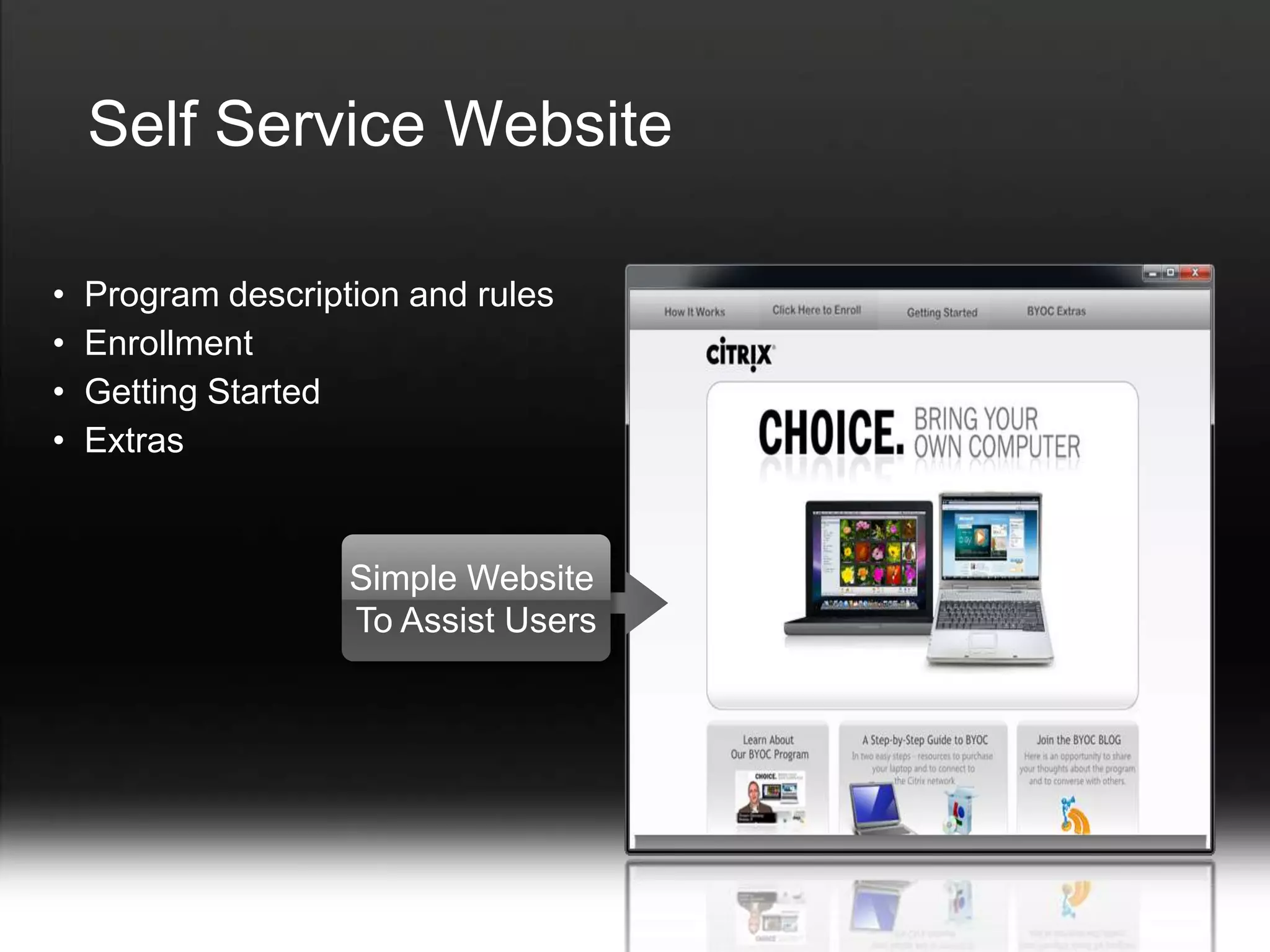
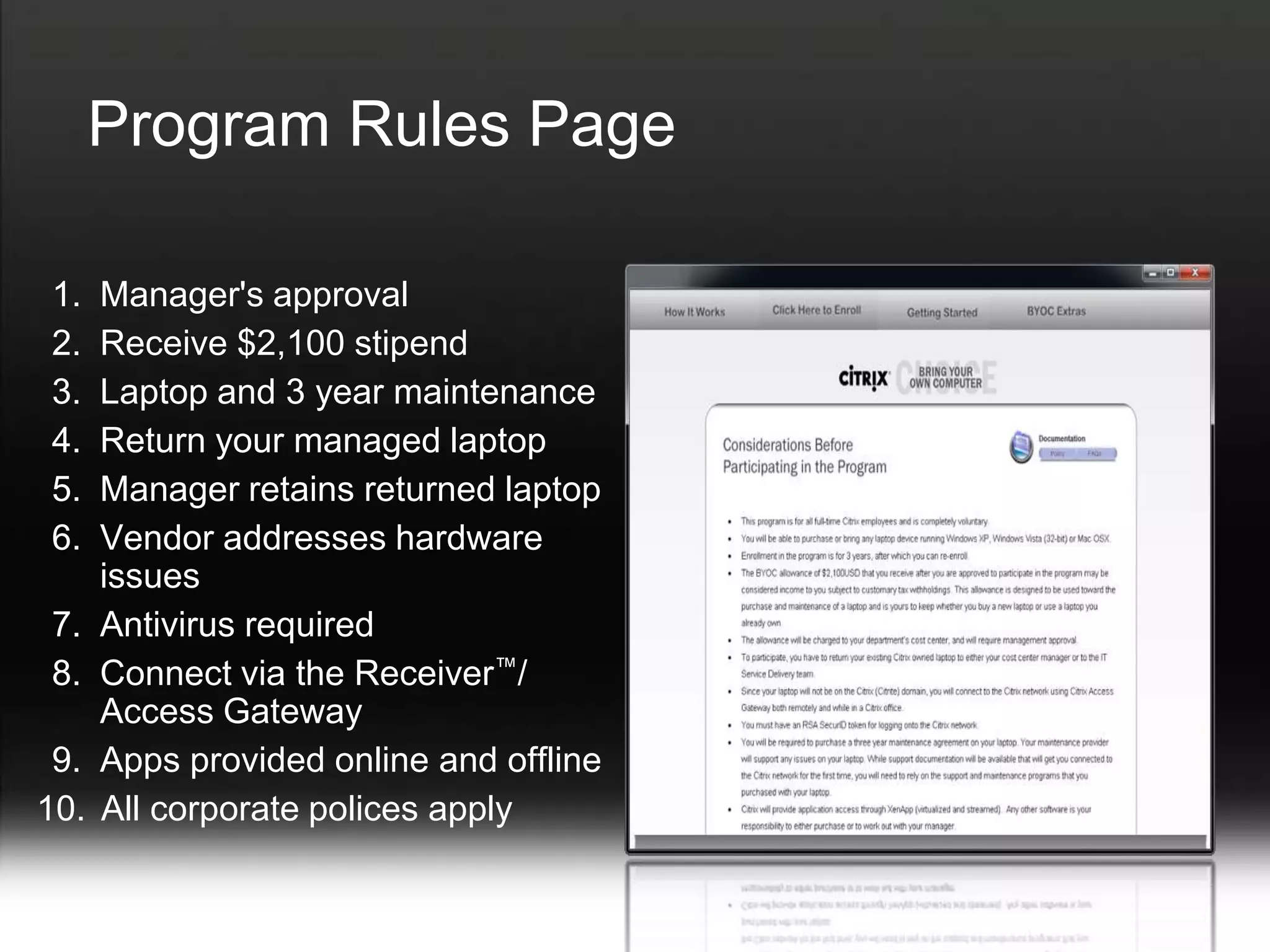
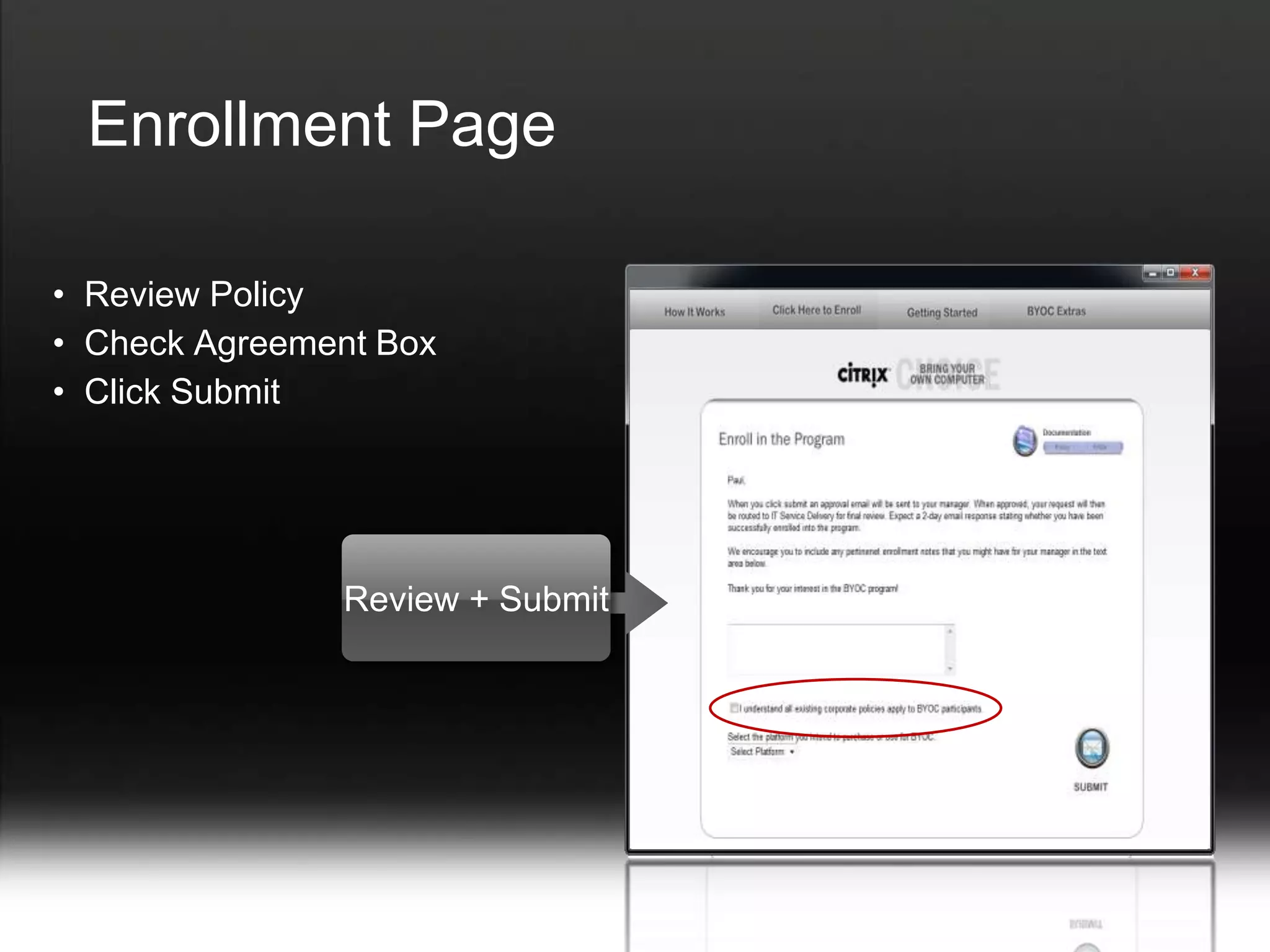
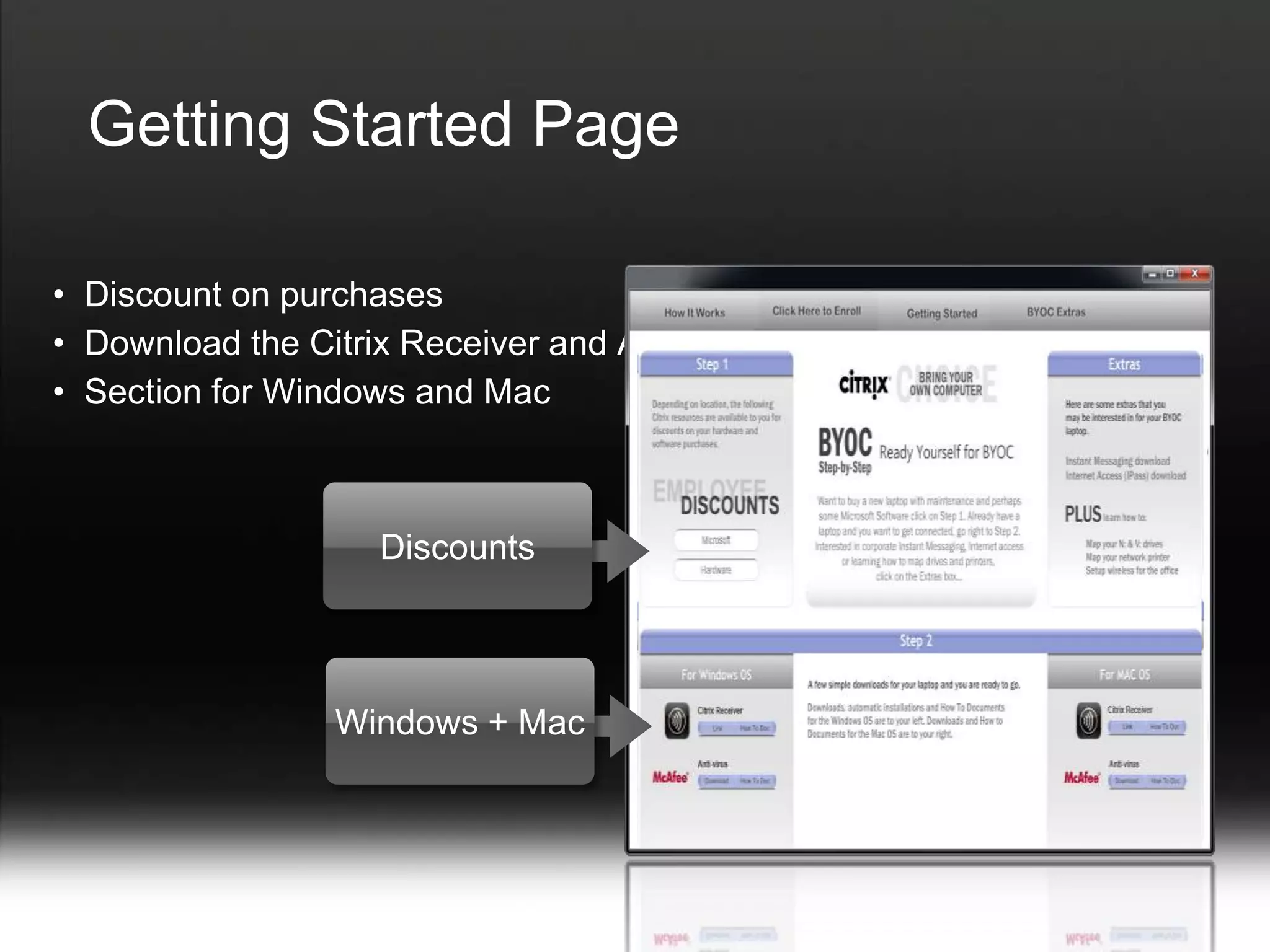
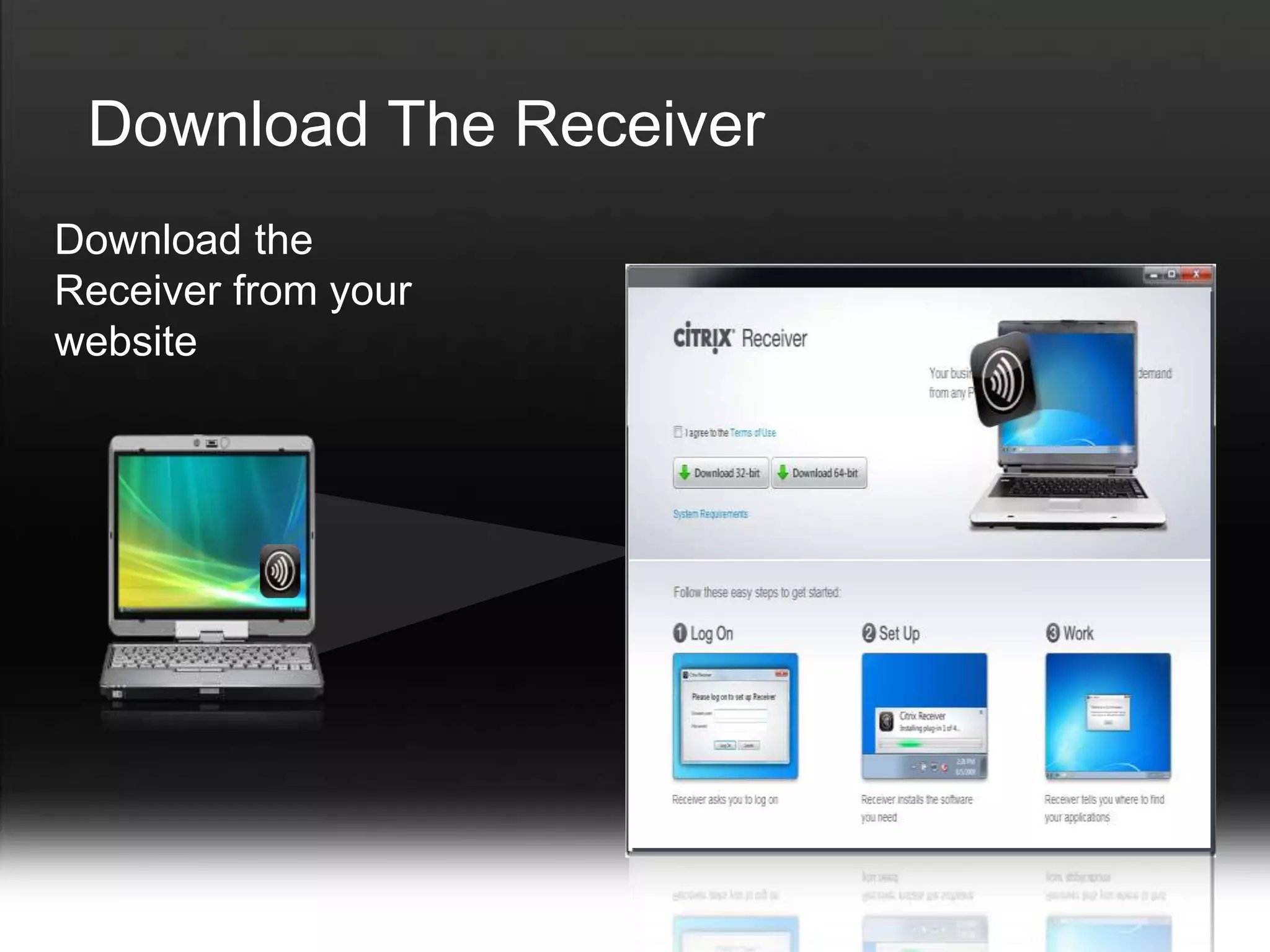
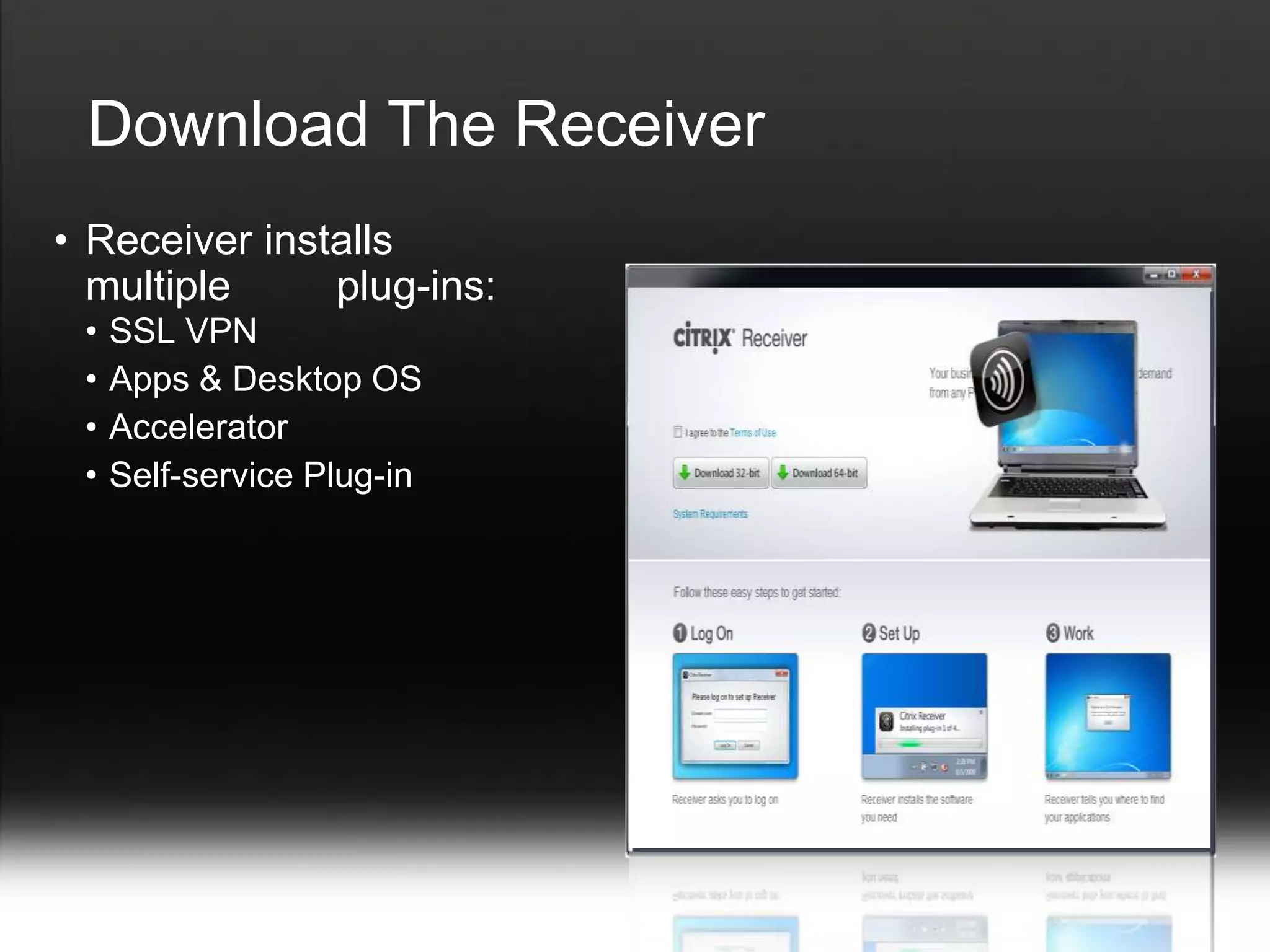
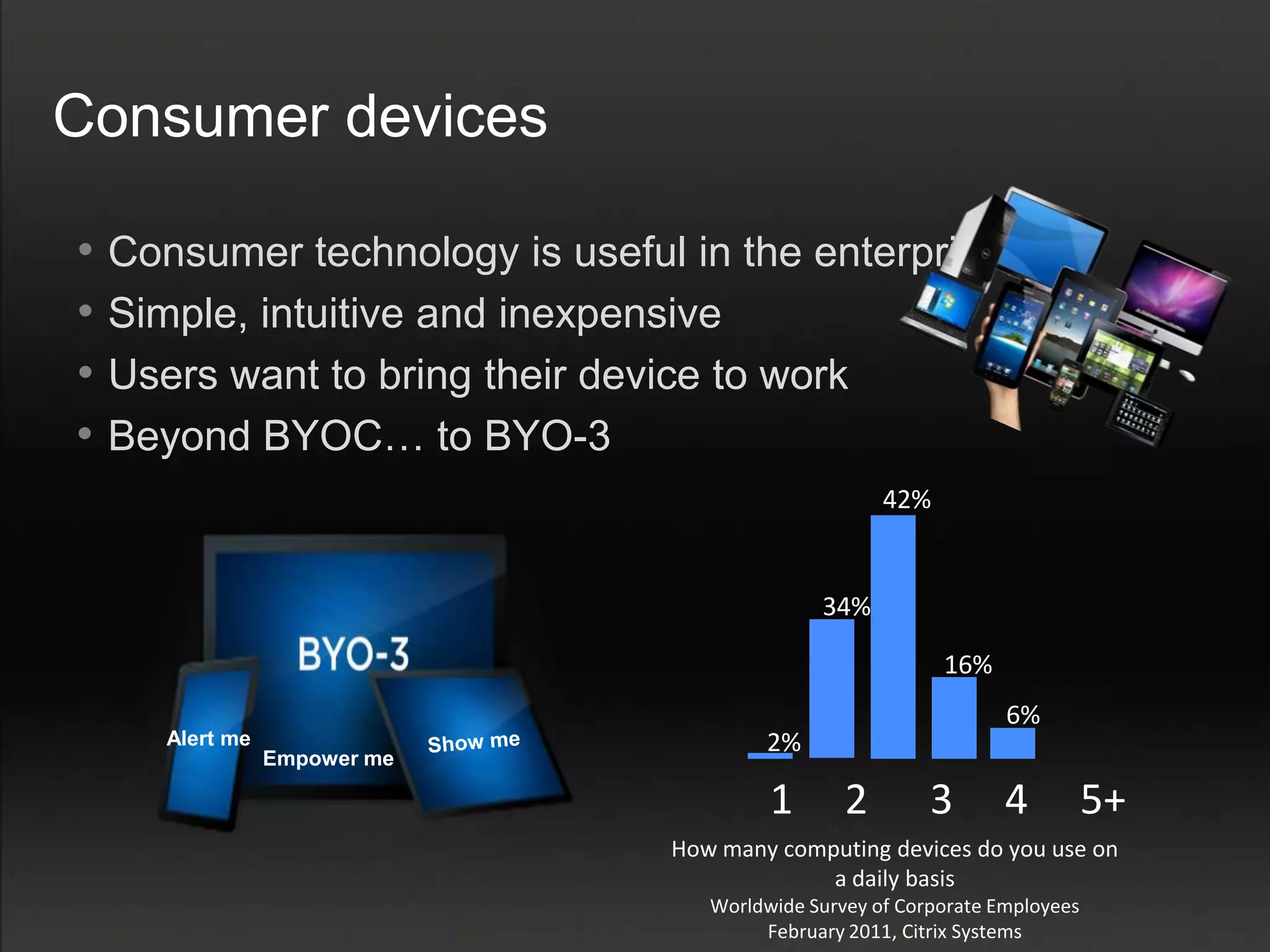
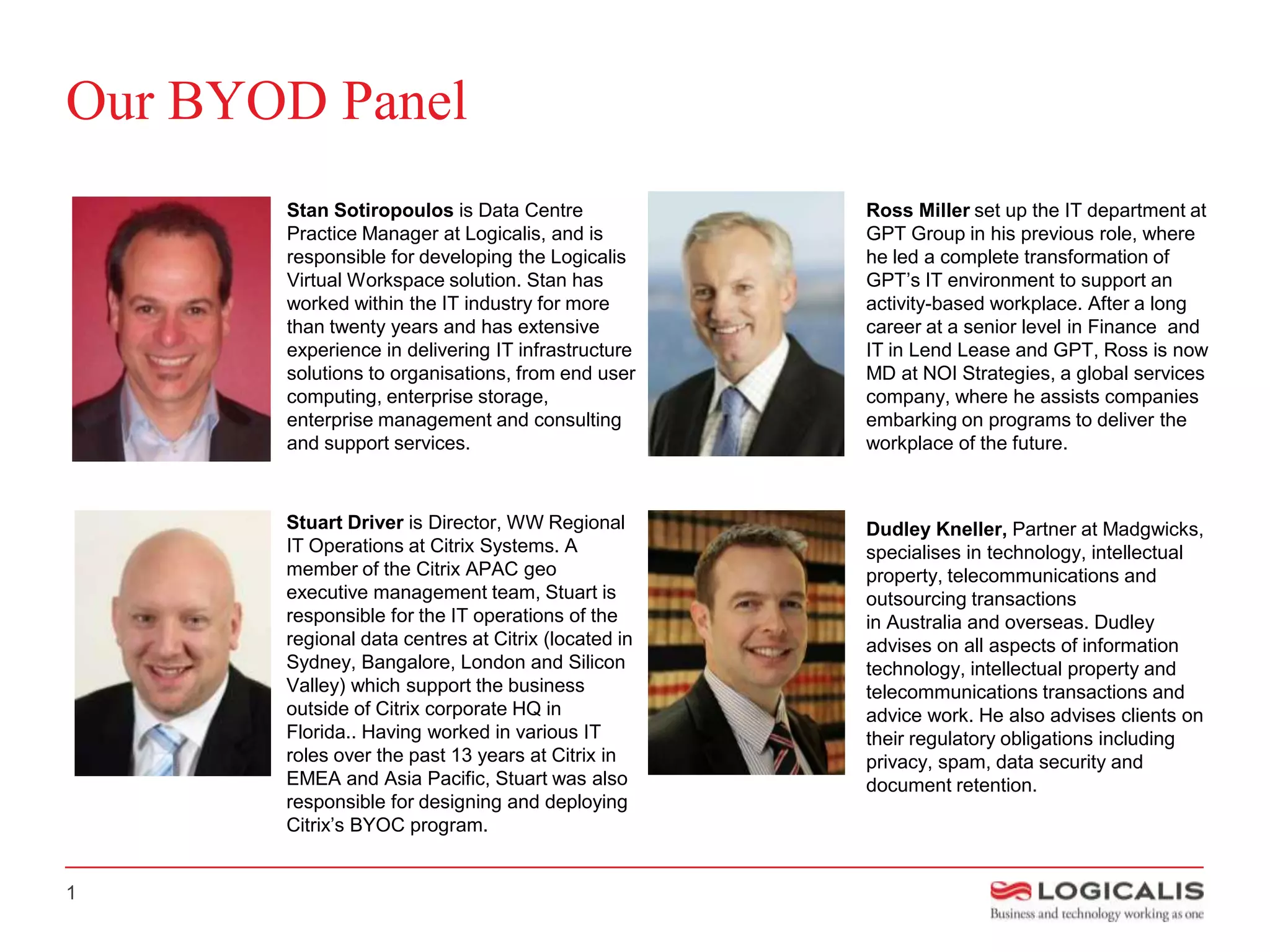
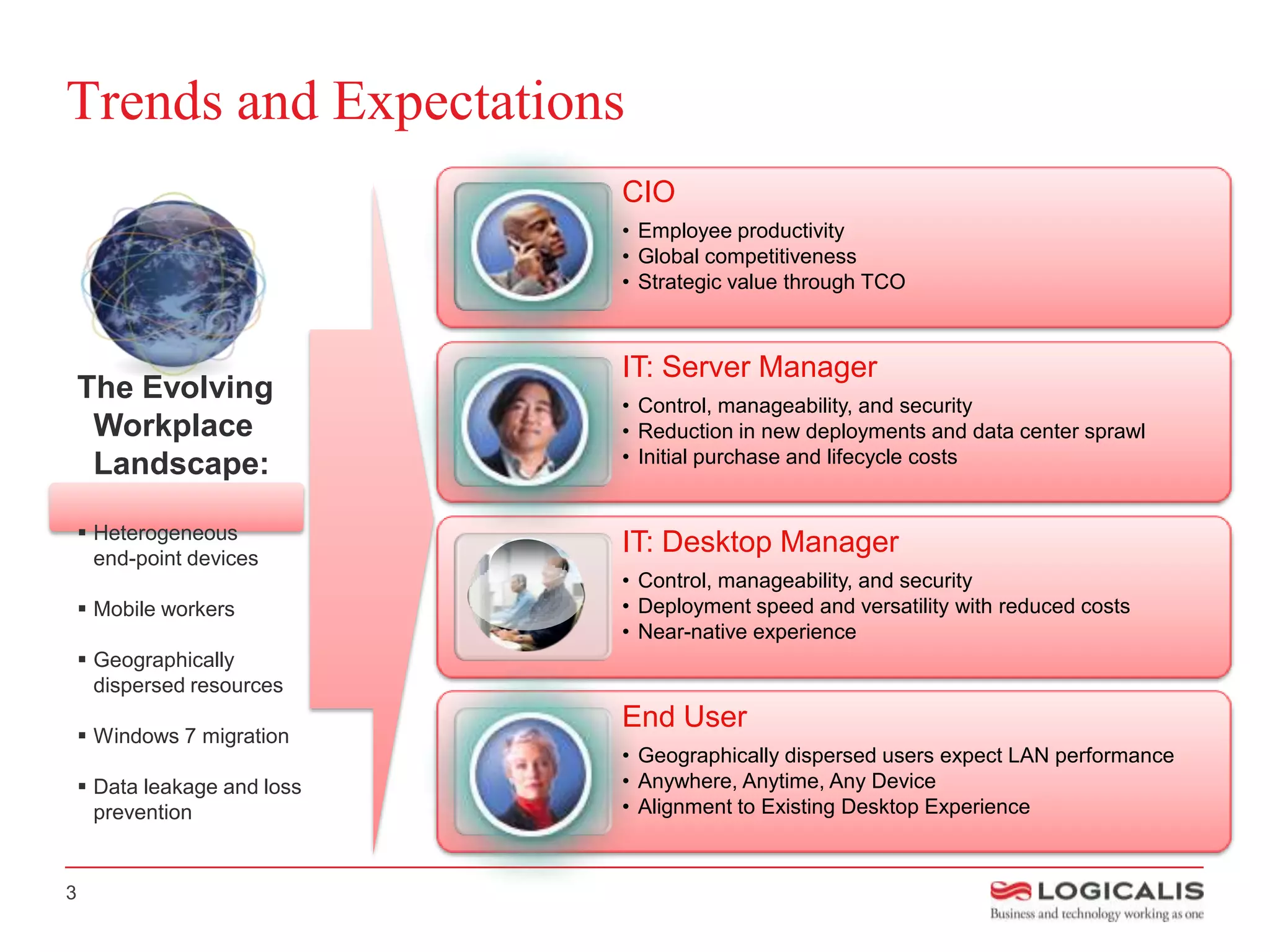
The BYOD (Bring Your Own Device) business briefing discusses the transformative role of technology in workplace environments, highlighting trends and expectations for employee productivity and mobile work solutions. Key insights include the adoption of desktop virtualization and the challenges associated with traditional PC management. The document emphasizes the importance of a well-structured BYOD program that ensures compliance, security, and user satisfaction while supporting organizational strategies for efficient operational outcomes.


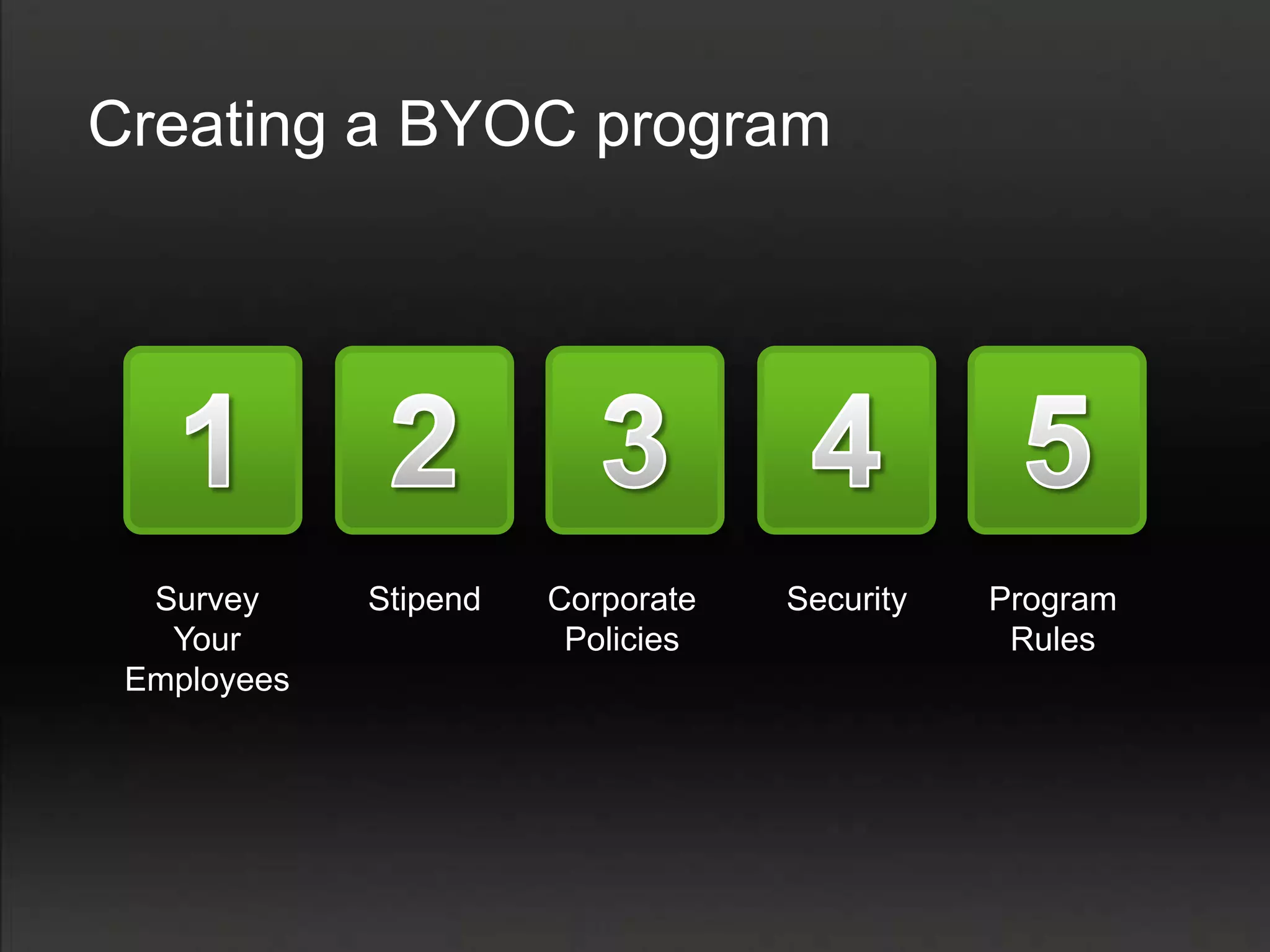
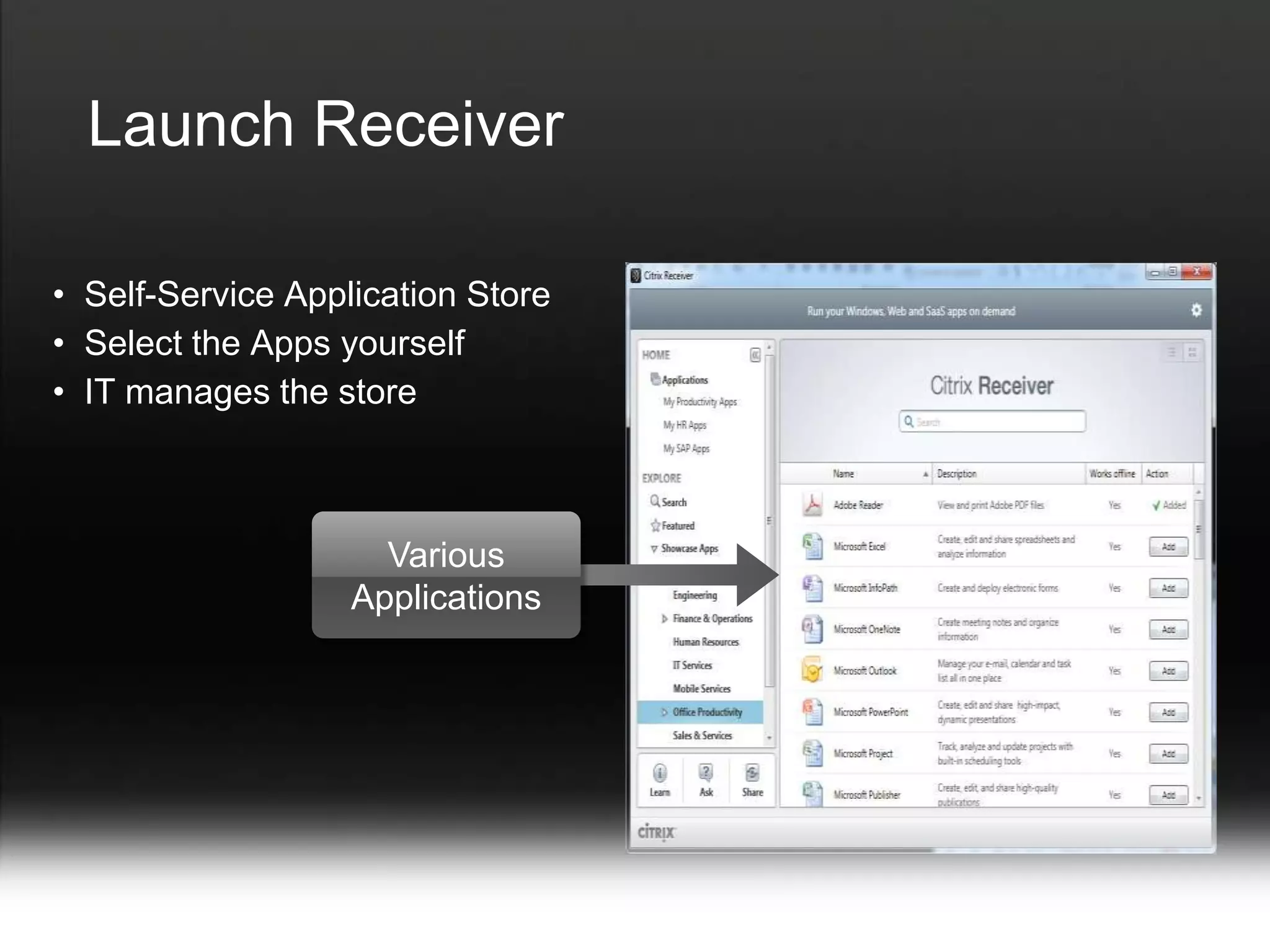
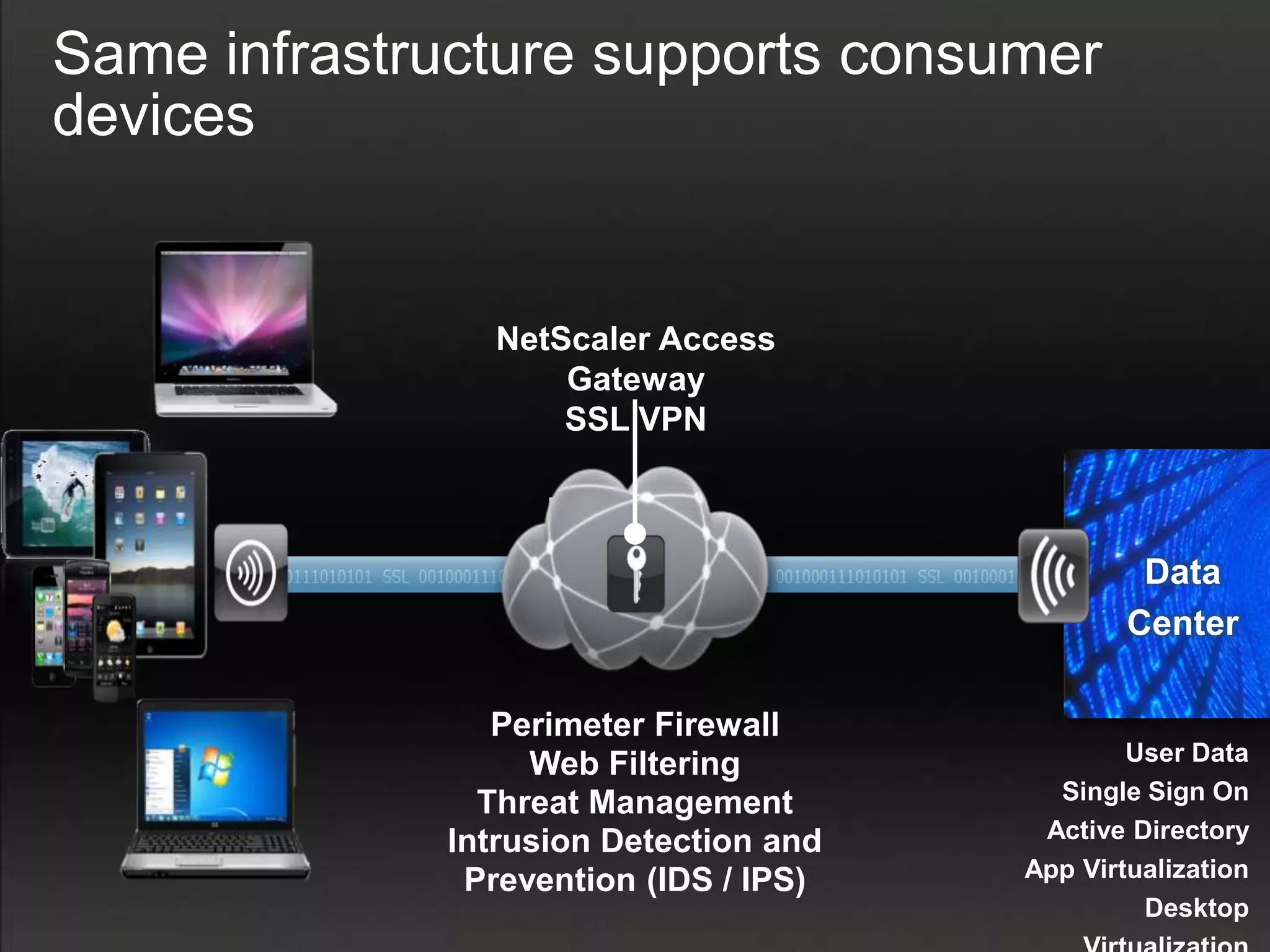
![Market Assessment - Secure mobility is a key CIO Challenge
Desktop virtualisation a key part of IT strategy
45% of respondents to Logicalis survey indicate plans within 12
months or part of IT strategy
44% of respondents to Fujitsu CIO survey indicate “mobile working
solutions” are of High or Top interest
Desktop virtualisation a “Top 5” technology – 20% users implementing
next 12mths / 40% next 24mths [IDC]
91% of organisations to have implemented some form of desktop
virtualisation by the end of 2013 [Citrix]
62% of Australian organisations planning to procure tablets next
12mths (compared to an APAC average of 31%) [IDC]
Countries like China, Germany, the US, India, Australia and NZ have
the most aggressive client virtualisation deployment plans [Forrester]
Adoption of BYOD models by major Australian companies like
Suncorp and Qantas
4](https://image.slidesharecdn.com/logicalisbyodbriefing-120512083737-phpapp01/75/Logicalis-BYOD-Briefing-5-2048.jpg)