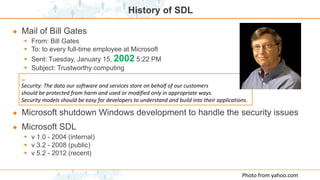
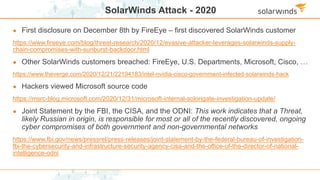
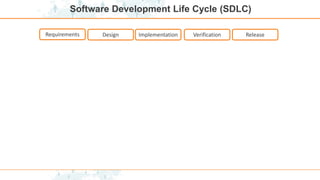
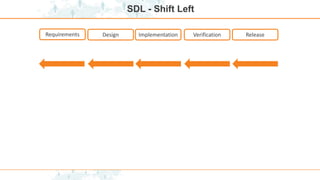
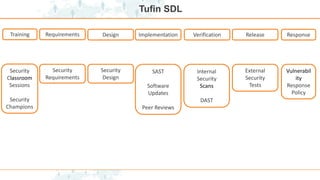
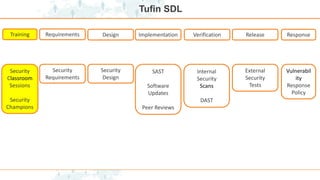
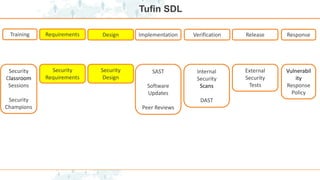
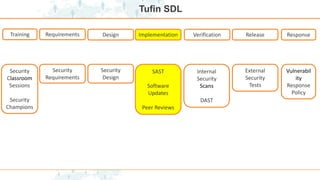
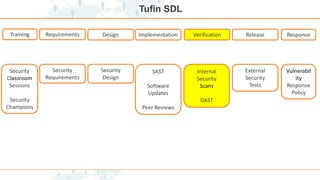
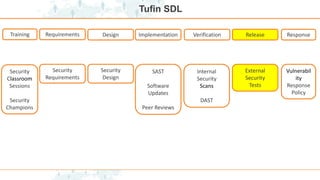
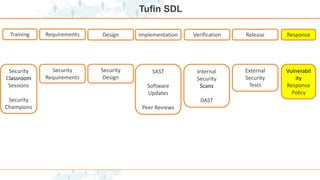
The document discusses the importance of the Security Development Lifecycle (SDL) in creating secure software, emphasizing that SDL systematically incorporates security measures through all phases of development. It outlines the history of SDL, key practices, and the necessary training to enhance security awareness in development teams. Additionally, the document highlights lessons learned from the SolarWinds attack to illustrate the critical need for robust security processes.