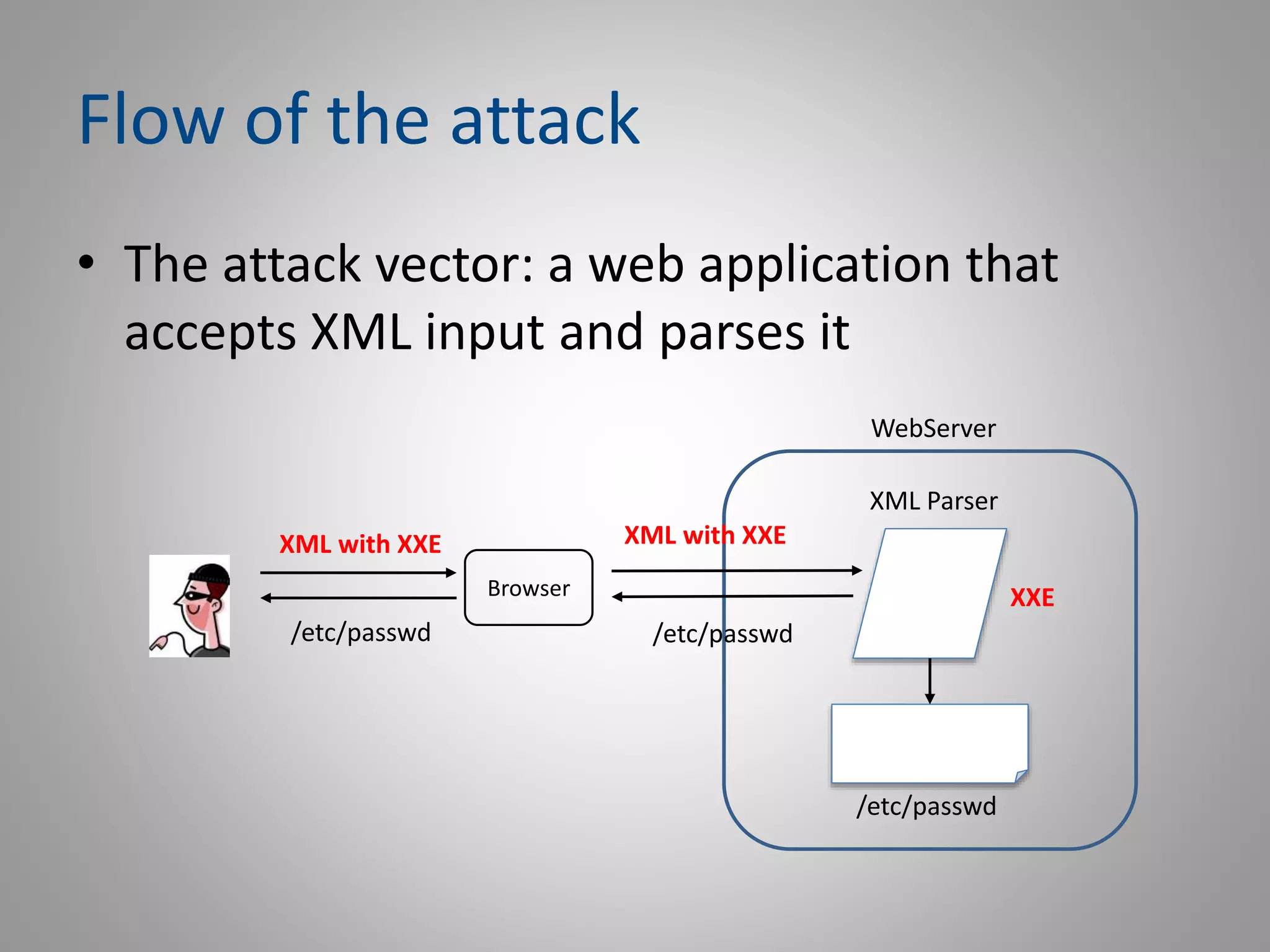
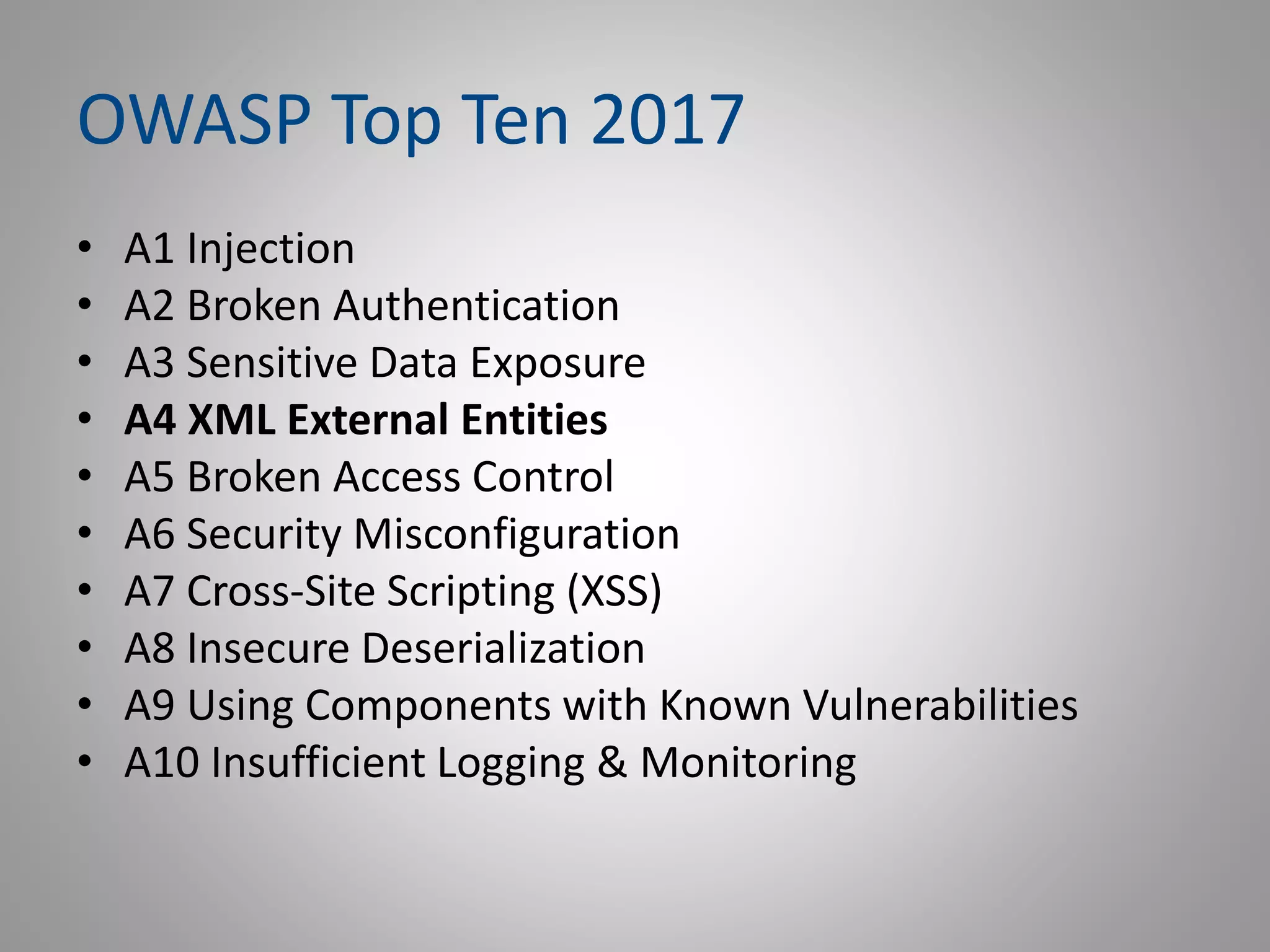
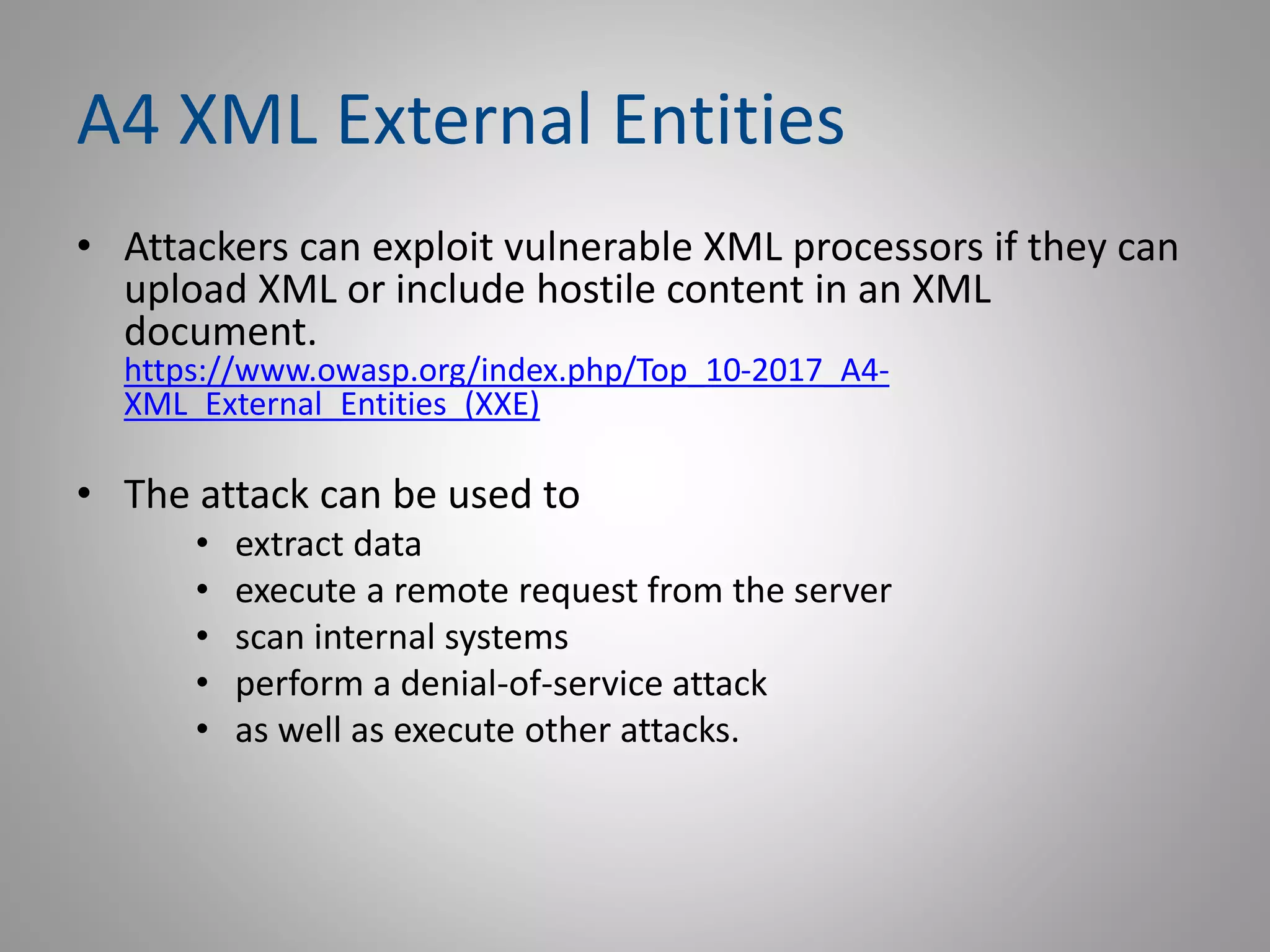
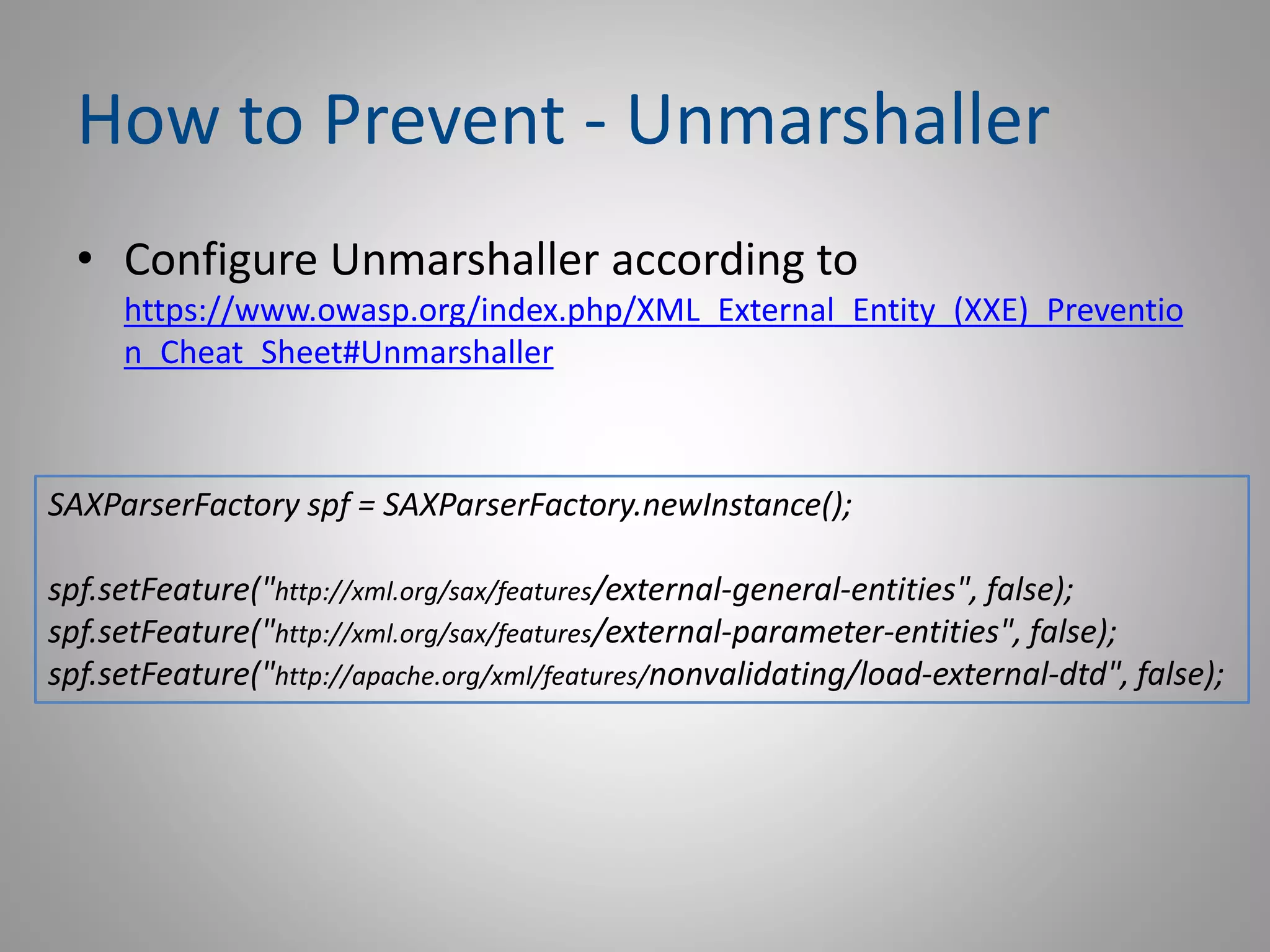
The document discusses XML External Entities (XXE) attacks, which can exploit vulnerable XML processors to extract data, execute remote requests, or perform denial-of-service attacks. It emphasizes the importance of disabling XML external entity processing in XML parsers to prevent such vulnerabilities and provides guidelines for securing XML processing. The speaker, Michael Furman, shares his background in software engineering and application security, along with resources for further information.

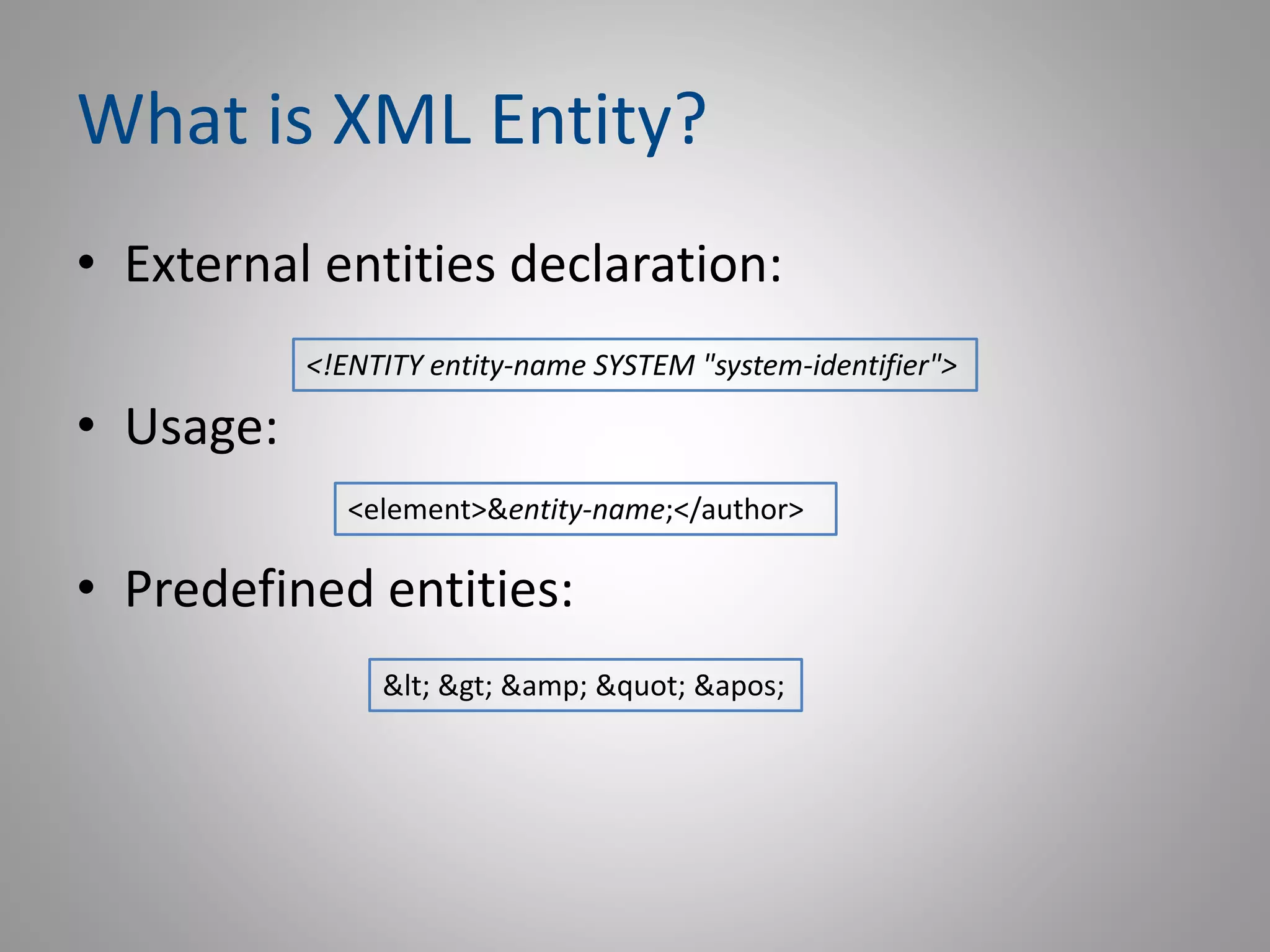
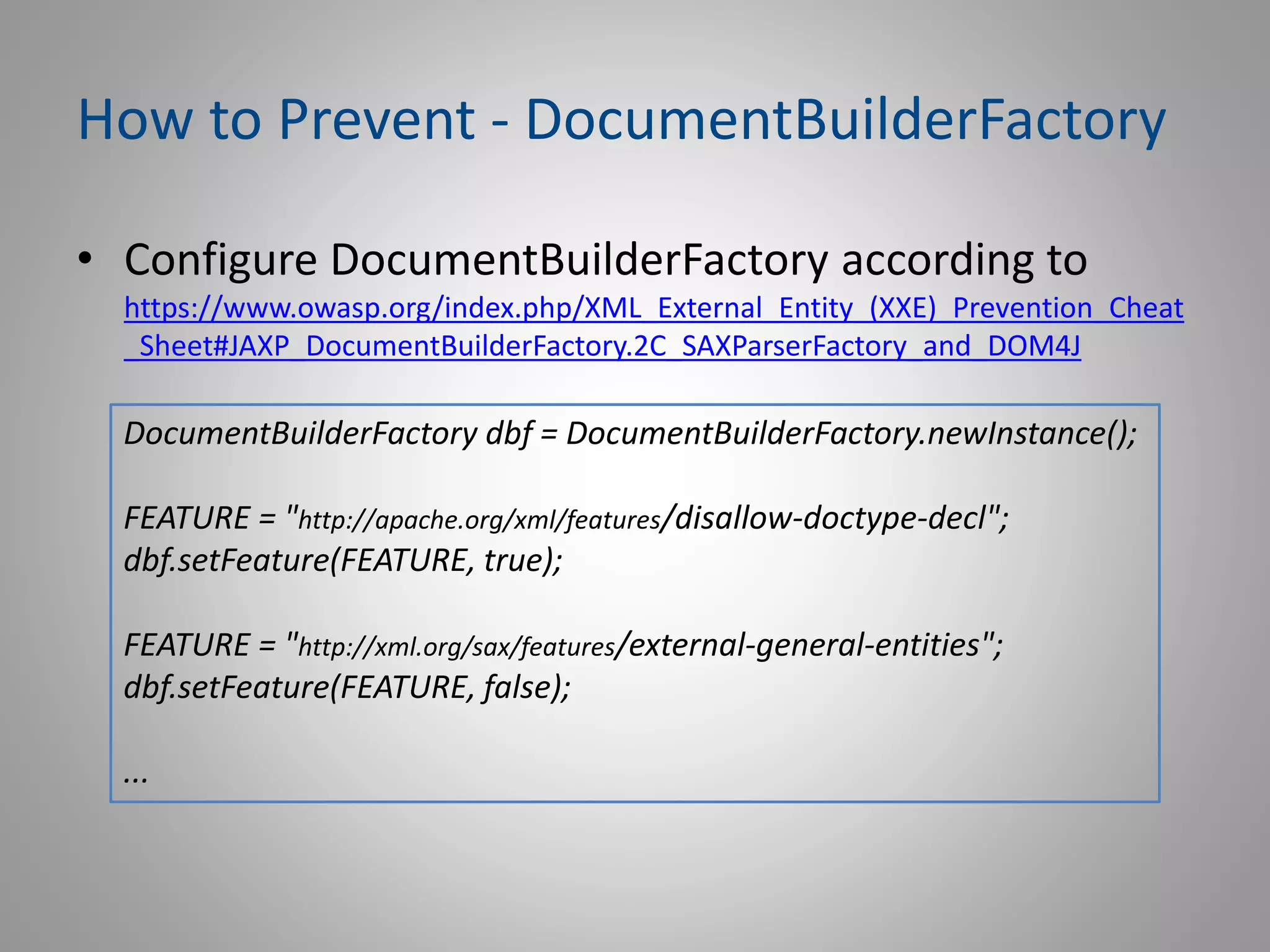
![Why XML Entity is Dangerous?
• What happens during the parsing of the file?
• The parser reads the local file.
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:////etc/passwd" >]>
<xmlroot><xmlEntry>&xxe;3</xmlEntry></xmlroot>](https://image.slidesharecdn.com/meetupowaspa4xxe-181102064232/75/OWASP-A4-XML-External-Entities-XXE-9-2048.jpg)
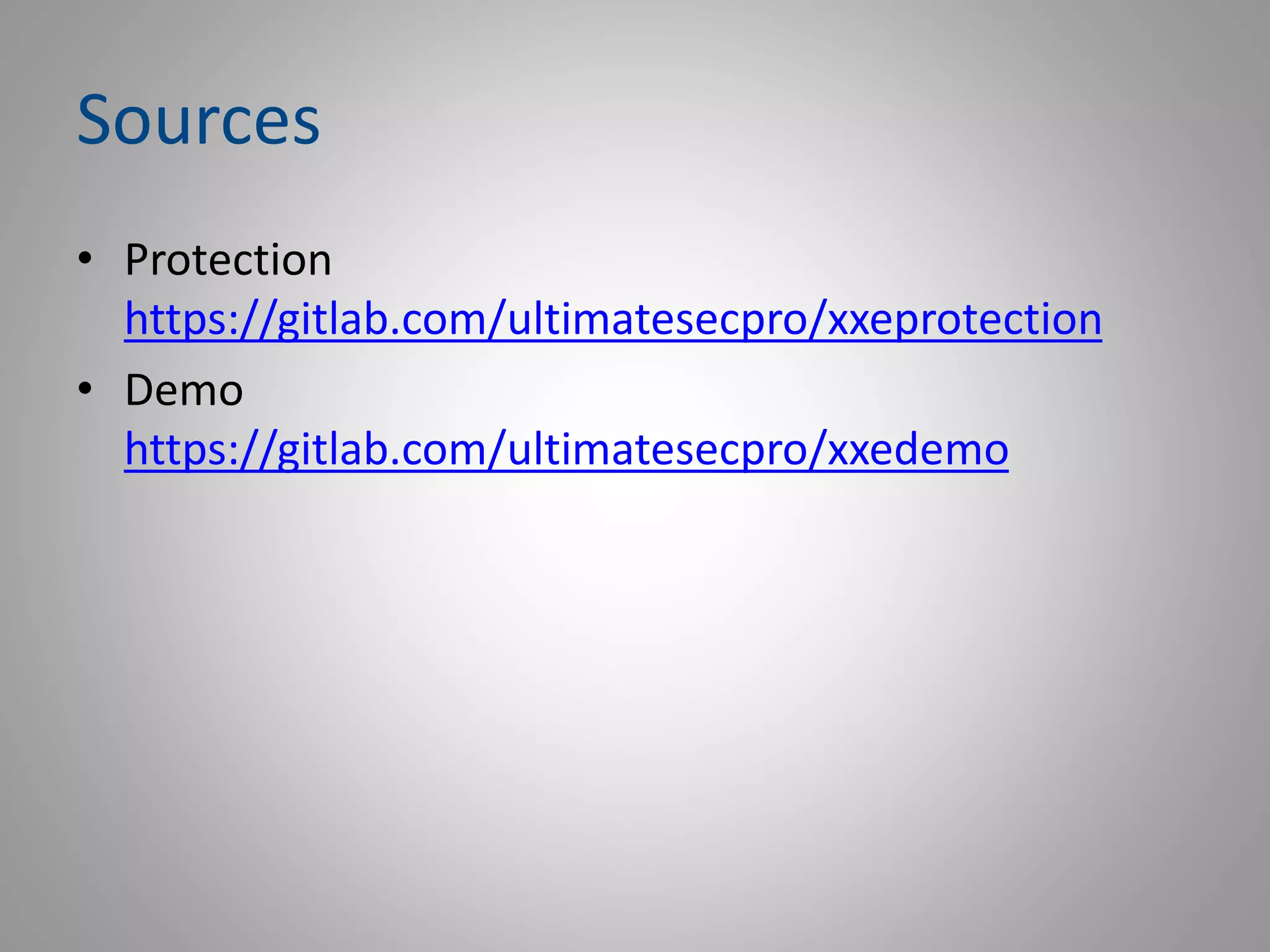
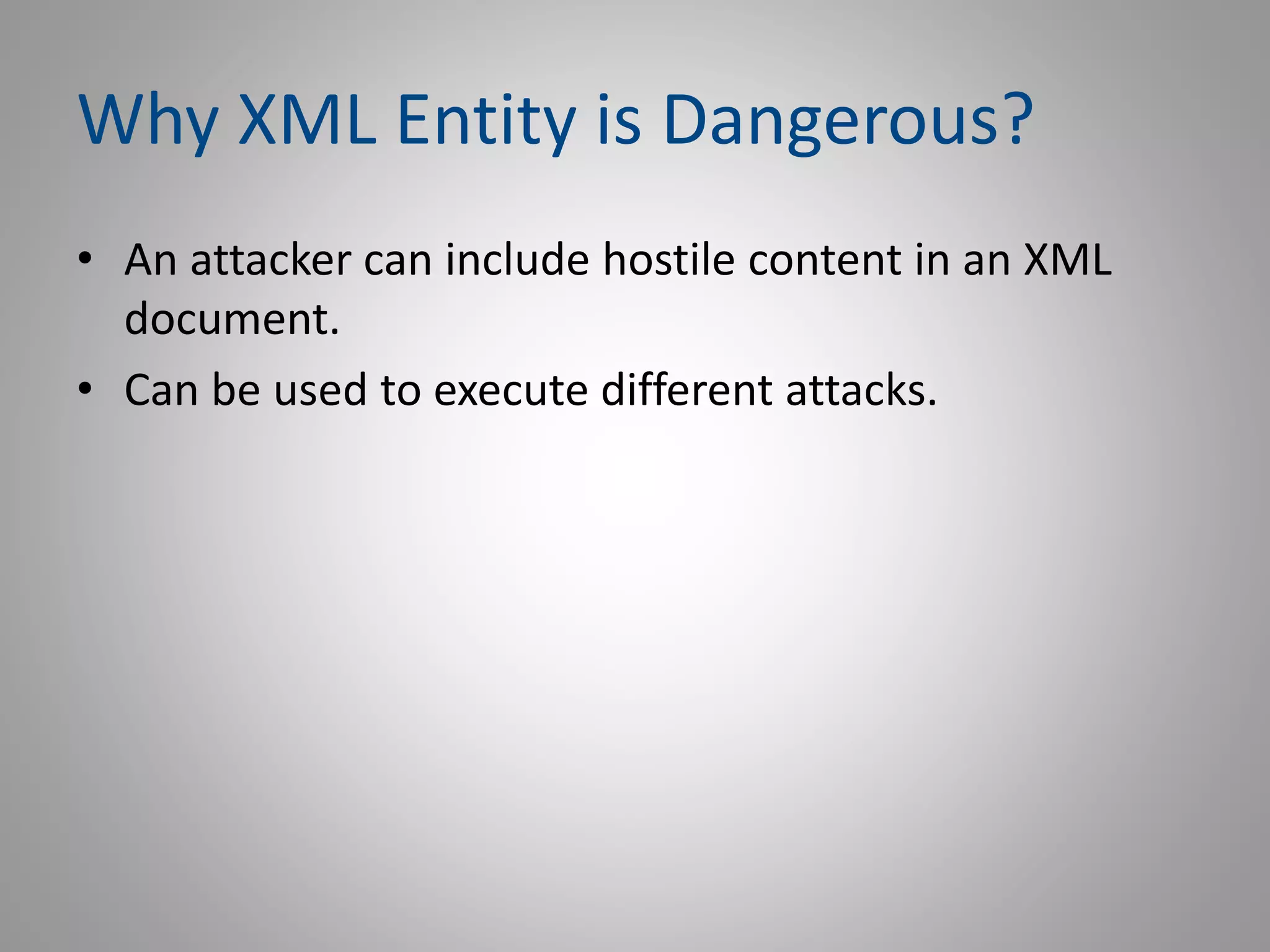
![Why XML Entity is Dangerous?
• What happens during the parsing of the file?
• The parser executes the remote HTTP call
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "http://api.geonames.org/timezoneJSON" >]>
<xmlroot><xmlEntry>&xxe;3</xmlEntry></xmlroot>](https://image.slidesharecdn.com/meetupowaspa4xxe-181102064232/75/OWASP-A4-XML-External-Entities-XXE-10-2048.jpg)