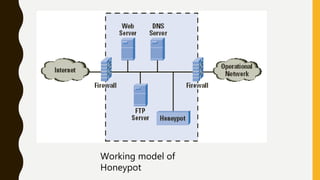
The document discusses honeypots, which are traps set up to gather information about hackers. It begins with an introduction to honeypots and their history. It then defines honeypots, explains why they should be used to learn about attacker tactics and identify vulnerabilities. It describes how honeypots work by simulating vulnerable systems. The document classifies honeypots and lists some popular honeypot tools. It concludes that honeypots provide valuable insights into how attackers operate.


![VIRTUAL HONEYPOT
• Thousands of honeypots on just one machine. They are inexpensive to
deploy and accessible to almost everyone
• Usually VMware [3] or User-Mode Linux (UML) are used to set up such
virtual honeypots
• Virtual honeypots are better than physical honeypots are scalability and
ease of maintenance](https://image.slidesharecdn.com/honeypotppt-190327162928/85/Honeypot-a-trap-to-hackers-13-320.jpg)