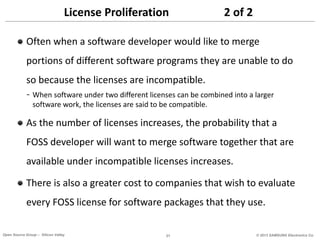
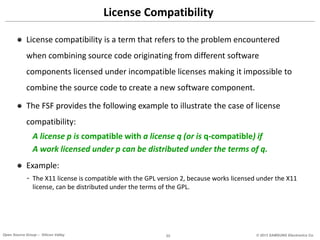
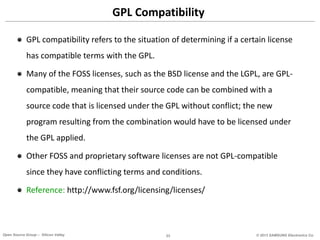
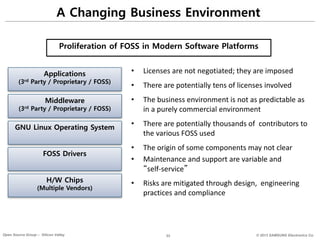
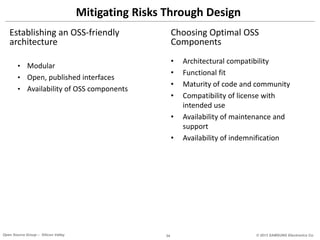
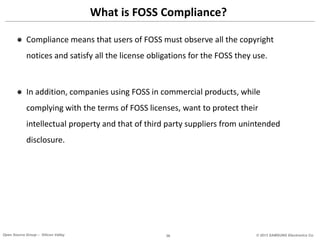
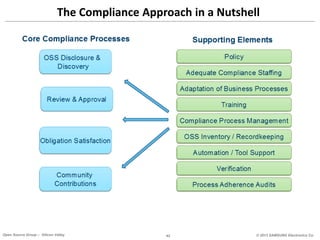
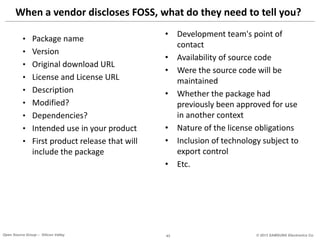
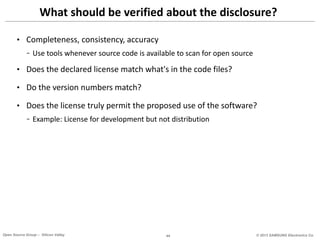
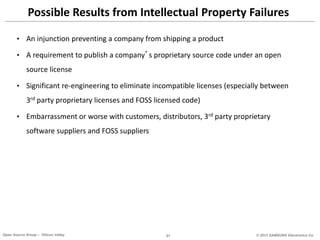
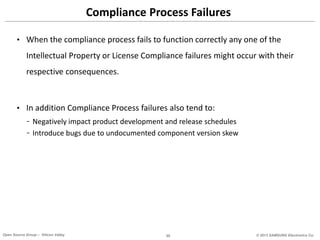
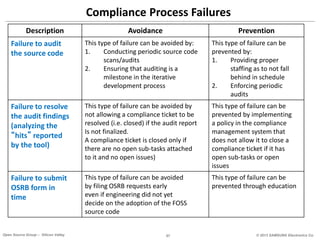
The document provides an overview of open source software (OSS) licenses, their terms, obligations, and the impact they can have on software development and distribution. It emphasizes the importance of compliance with OSS licenses, includes the consequences of non-compliance, and outlines the necessary measures for maintaining compliance within organizations. Various types of licenses, including proprietary, permissive, freeware, and shareware, are discussed, alongside their implications for intellectual property rights and development processes.


![LGPL v2 – Lesser General Public License
• LGPL v2.1 is typically used for libraries
• Similar to GPL v2 but dynamic linkage to GPL v2 incompatible components
(including proprietary) is allowed.
• License obligations summary:
- Must include a copy of the license in documentation available to the end-user
- Must inform user of how to obtain the source code and that it is covered by LGPL v2.1
- Must give prominent notice that the library is used in the work
- Must redistribute source code for the library [including modifications, if any]
- When redistributing source code, must include a copy of the license
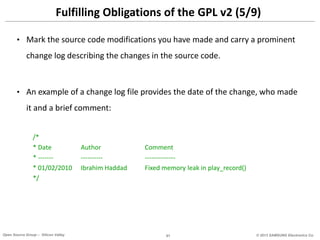
- Source code modifications must be clearly marked as such and carry a prominent change log
- Modifications become LGPL v2.1
- End-user must be able to replace the library
Samsung Open Source Group 86](https://image.slidesharecdn.com/compliancecompletedeck-141110155516-conversion-gate02/85/Guide-to-Open-Source-Compliance-86-320.jpg)
![Architecture Review – Example
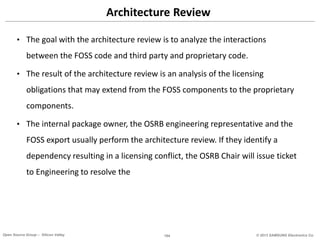
Legend
Proprietary
3rd Party Commercial
GPL
LGPL
FOSS Permissive
Function call
Socket interface
(fc)
(si)
System call
(sc)
Shared headers
(sh)
Samsung Open Source Group 105
User Space
Kernel Space
Hardware
[Insert Components]
[Insert interaction method]
[Insert Components]
[Insert interaction method]
[Insert Components]](https://image.slidesharecdn.com/compliancecompletedeck-141110155516-conversion-gate02/85/Guide-to-Open-Source-Compliance-105-320.jpg)