Embed presentation
Download as PDF, PPTX



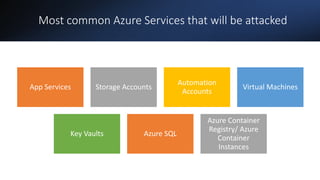
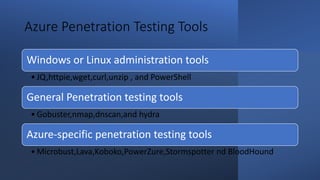
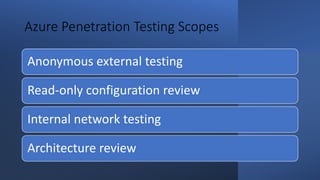
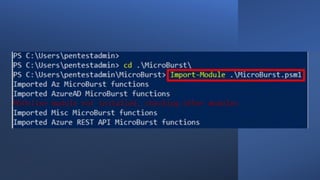


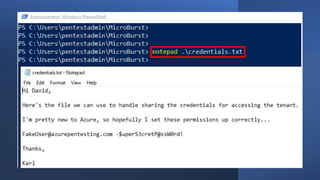
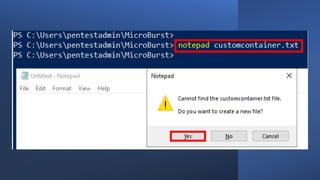
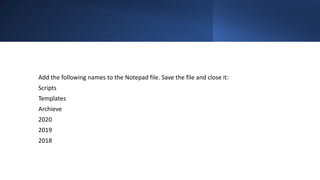
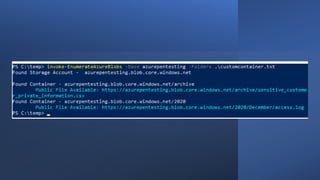


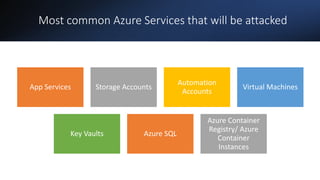
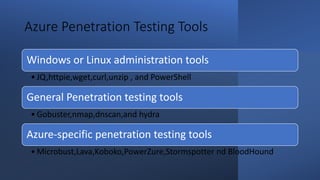
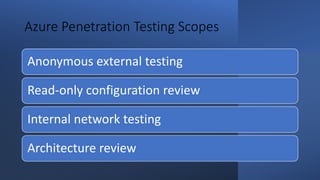
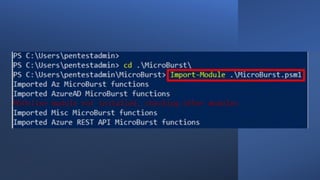
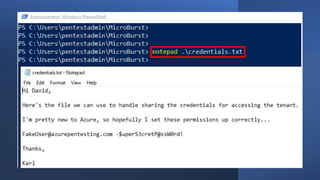
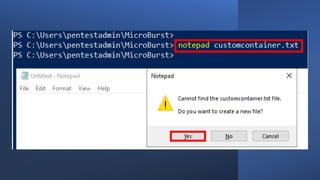
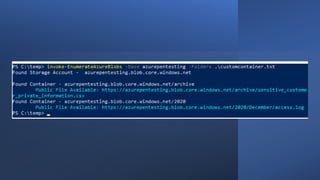
The document outlines an agenda for Azure penetration testing, covering an overview of Azure services, common attack targets, and various penetration testing tools. It includes guidelines for ethical hacking within Azure environments and emphasizes the importance of identifying vulnerabilities in public-facing services. The document also mentions specific tools for Azure penetration testing and offers a demo for practical skill development.