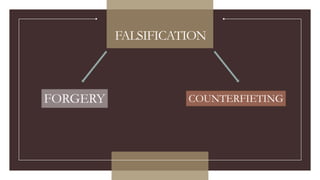
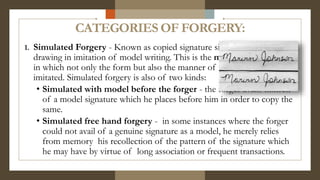
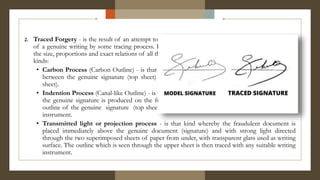
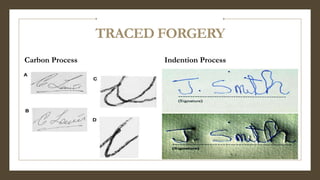
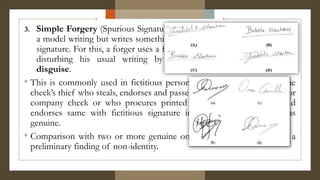
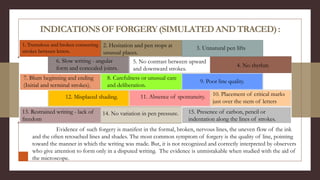
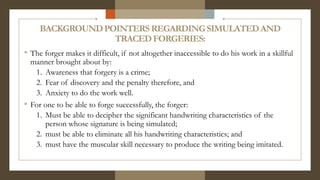
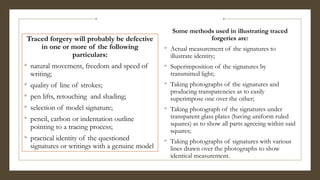
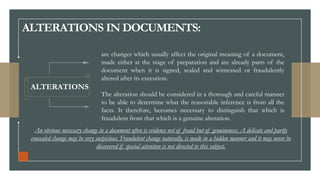
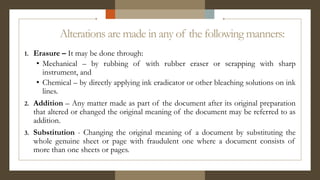
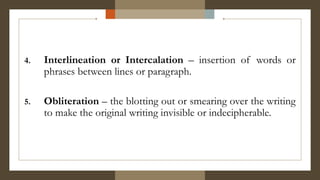
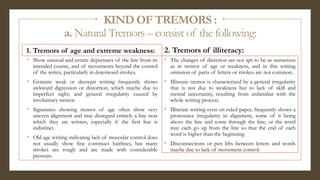
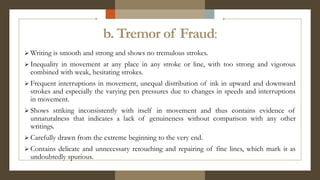
Forgery involves imitating signatures or documents. There are three main types of forgery: simulated forgery which copies signatures freehand, traced forgery which uses tracing methods to exactly replicate signatures, and simple forgery which uses fake names without copying a model. Traced forgeries often show defects like irregular line quality from hesitation and changes in pen pressure. Simulated forgeries may also contain indications of fraud like tremors, blunt letter forms, and lack of spontaneity. Document alterations like erasures, additions, or substitutions can also be used to change meanings fraudulently. Careful examination of writing characteristics is needed to determine the authenticity of signatures and documents.