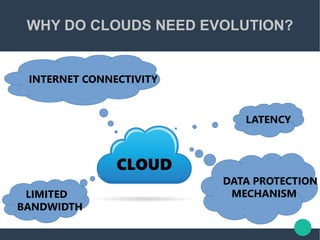
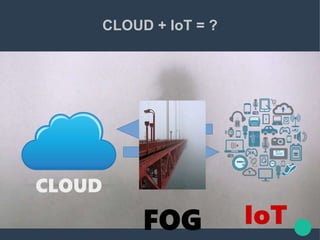
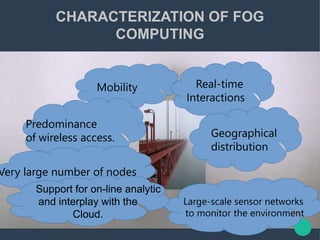
Fog computing provides compute, storage, and networking services between edge devices and cloud data centers. It helps address issues with cloud computing like latency, limited bandwidth, and data protection. Fog computing, located at the network edge, can process real-time, geographically distributed data from millions of IoT devices like vehicles, factories, and infrastructure. This localized processing allows analysis and action on IoT data within seconds, addressing needs that cloud alone cannot meet. Fog enhances cloud computing for IoT scenarios by extending cloud capabilities closer to the edge.