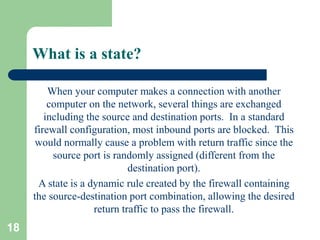
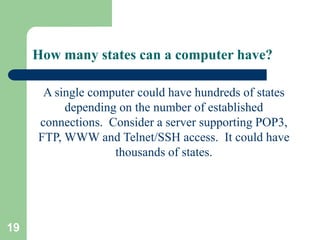
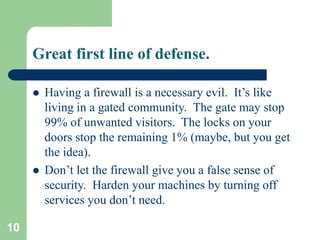
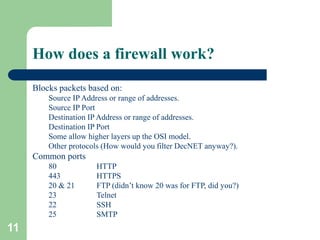
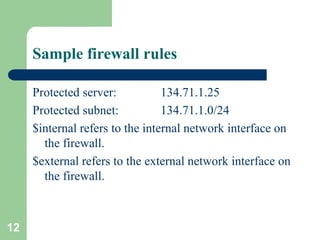
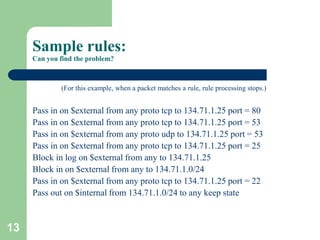
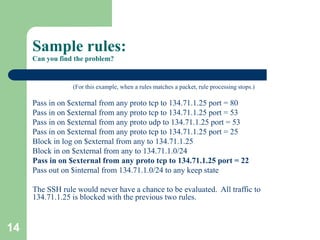
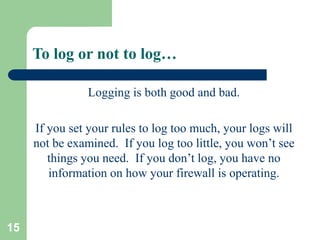
A firewall controls the flow of network traffic into and out of a network. It protects networks from attacks like probing, crashing services/computers, and unauthorized access. There are different types of firewalls including edge firewalls that protect individual devices, appliance firewalls that are dedicated firewall devices, and network firewalls that protect entire networks. Firewalls work by blocking or allowing packets based on criteria like source/destination IP addresses and ports. Firewall rules must be properly configured to allow desired traffic while blocking unwanted traffic. Logs record firewall activity and potential attacks but too much or too little logging has downsides.
![16
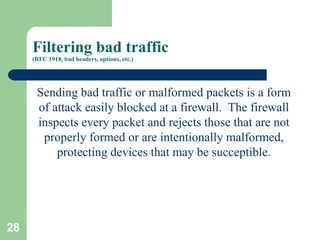
Sample log file
Jul 31 11:00:06 kd2 ipmon[14110]: 11:00:06.786765 xl0 @1:10 b 134.71.4.100,50258 -> 134.71.202.57,23 PR tcp len 20 48 -S IN
Jul 31 11:00:07 kd2 ipmon[14110]: 11:00:07.366515 xl0 @1:10 b 134.71.4.100,50258 -> 134.71.202.57,23 PR tcp len 20 48 -S IN
Jul 31 11:00:08 kd2 ipmon[14110]: 11:00:08.526751 xl0 @1:10 b 134.71.4.100,50258 -> 134.71.202.57,23 PR tcp len 20 48 -S IN
Jul 31 11:00:10 kd2 ipmon[14110]: 11:00:10.856705 xl0 @1:10 b 134.71.4.100,50258 -> 134.71.202.57,23 PR tcp len 20 48 -S IN
Jul 31 11:00:15 kd2 ipmon[14110]: 11:00:15.515785 xl0 @1:10 b 134.71.4.100,50258 -> 134.71.202.57,23 PR tcp len 20 48 -S IN
Jul 31 11:50:02 kd2 ipmon[14110]: 11:50:02.619311 xl0 @0:3 b 213.244.12.136,4588 -> 134.71.202.37,80 PR tcp len 20 44 -S IN
Jul 31 11:50:02 kd2 ipmon[14110]: 11:50:02.629271 xl0 @0:3 b 213.244.12.136,4597 -> 134.71.202.44,80 PR tcp len 20 44 -S IN
Jul 31 11:50:02 kd2 ipmon[14110]: 11:50:02.642610 xl0 @1:10 b 213.244.12.136,4610 -> 134.71.202.57,80 PR tcp len 20 44 -S IN
Jul 31 11:50:05 kd2 ipmon[14110]: 11:50:05.633338 xl0 @1:10 b 213.244.12.136,4610 -> 134.71.202.57,80 PR tcp len 20 44 -S IN
Jul 31 11:50:17 kd2 ipmon[14110]: 11:50:16.882433 xl0 @0:3 b 213.244.12.136,1406 -> 134.71.203.35,80 PR tcp len 20 44 -S IN
Jul 31 11:50:20 kd2 ipmon[14110]: 11:50:20.401561 xl0 @0:3 b 213.244.12.136,1688 -> 134.71.203.47,80 PR tcp len 20 44 -S IN
Jul 31 11:50:20 kd2 ipmon[14110]: 11:50:20.414682 xl0 @0:3 b 213.244.12.136,1701 -> 134.71.203.60,80 PR tcp len 20 44 -S IN
Jul 31 11:50:24 kd2 ipmon[14110]: 11:50:24.127364 xl0 @0:3 b 213.244.12.136,1944 -> 134.71.203.103,80 PR tcp len 20 44 -S IN
Jul 31 11:50:24 kd2 ipmon[14110]: 11:50:24.144581 xl0 @0:3 b 213.244.12.136,1957 -> 134.71.203.108,80 PR tcp len 20 44 -S IN
Jul 31 11:50:27 kd2 ipmon[14110]: 11:50:27.761458 xl0 @0:3 b 213.244.12.136,2243 -> 134.71.203.168,80 PR tcp len 20 44 -S IN
Jul 31 11:50:27 kd2 ipmon[14110]: 11:50:27.778617 xl0 @0:3 b 213.244.12.136,2260 -> 134.71.203.185,80 PR tcp len 20 44 -S IN
Jul 31 11:50:30 kd2 ipmon[14110]: 11:50:30.771581 xl0 @0:3 b 213.244.12.136,2243 -> 134.71.203.168,80 PR tcp len 20 44 -S IN
Jul 31 11:50:30 kd2 ipmon[14110]: 11:50:30.772833 xl0 @0:3 b 213.244.12.136,2260 -> 134.71.203.185,80 PR tcp len 20 44 -S IN
Jul 31 11:52:48 kd2 ipmon[14110]: 11:52:47.511993 xl0 @1:10 b 207.45.69.69,1610 -> 134.71.202.57,113 PR tcp len 20 44 -S IN
Jul 31 11:52:51 kd2 ipmon[14110]: 11:52:50.501969 xl0 @1:10 b 207.45.69.69,1610 -> 134.71.202.57,113 PR tcp len 20 44 -S IN
Jul 31 11:52:54 kd2 ipmon[14110]: 11:52:53.501498 xl0 @1:10 b 207.45.69.69,1610 -> 134.71.202.57,113 PR tcp len 20 44 -S IN
Jul 31 11:52:56 kd2 ipmon[14110]: 11:52:55.703527 xl0 @1:10 b 142.163.9.225,6346 -> 134.71.202.57,3343 PR tcp len 20 40 -A IN
Jul 31 11:52:57 kd2 ipmon[14110]: 11:52:56.500682 xl0 @1:10 b 207.45.69.69,1610 -> 134.71.202.57,113 PR tcp len 20 44 -S IN
Jul 31 11:53:00 kd2 ipmon[14110]: 11:52:59.500694 xl0 @1:10 b 207.45.69.69,1610 -> 134.71.202.57,113 PR tcp len 20 44 -S IN
Jul 31 12:00:24 kd2 ipmon[14110]: 12:00:24.220209 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:00:26 kd2 ipmon[14110]: 12:00:26.040009 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:00:28 kd2 ipmon[14110]: 12:00:28.794944 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:00:34 kd2 ipmon[14110]: 12:00:34.302899 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:00:46 kd2 ipmon[14110]: 12:00:45.284181 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN](https://image.slidesharecdn.com/firewallbasics-ron-190921093703/85/Firewall-basics-ron-16-320.jpg)
![17
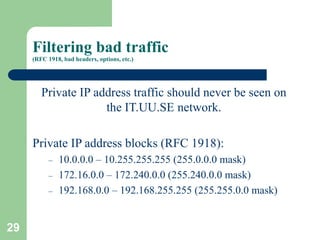
Had enough yet?
Jul 31 12:00:58 kd2 ipmon[14110]: 12:00:58.200613 xl0 @1:10 b 24.27.2.83,3363 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:01 kd2 ipmon[14110]: 12:01:00.236672 xl0 @1:10 b 61.98.116.133,4510 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:01 kd2 ipmon[14110]: 12:01:01.192960 xl0 @1:10 b 24.27.2.83,3363 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:03 kd2 ipmon[14110]: 12:01:02.868846 xl0 @1:10 b 12.251.174.163,2403 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:03 kd2 ipmon[14110]: 12:01:03.161480 xl0 @1:10 b 61.98.116.133,4510 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:05 kd2 ipmon[14110]: 12:01:05.010881 xl0 @1:10 b 24.166.24.65,3816 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:05 kd2 ipmon[14110]: 12:01:05.282234 xl0 @1:10 b 24.159.69.143,1834 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:06 kd2 ipmon[14110]: 12:01:05.796431 xl0 @1:10 b 12.251.174.163,2403 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:07 kd2 ipmon[14110]: 12:01:07.240923 xl0 @1:10 b 24.27.2.83,3363 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:07 kd2 ipmon[14110]: 12:01:07.251735 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:08 kd2 ipmon[14110]: 12:01:07.963357 xl0 @1:10 b 24.166.24.65,3816 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:08 kd2 ipmon[14110]: 12:01:08.229151 xl0 @1:10 b 24.159.69.143,1834 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:09 kd2 ipmon[14110]: 12:01:09.209297 xl0 @1:10 b 65.31.146.125,55989 -> 134.71.202.57,10336 PR tcp len 20 65 -R IN
Jul 31 12:01:09 kd2 ipmon[14110]: 12:01:09.212097 xl0 @1:10 b 61.98.116.133,4510 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:12 kd2 ipmon[14110]: 12:01:11.704343 xl0 @1:10 b 12.251.174.163,2403 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:14 kd2 ipmon[14110]: 12:01:13.969454 xl0 @1:10 b 24.166.24.65,3816 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:14 kd2 ipmon[14110]: 12:01:14.230632 xl0 @1:10 b 24.159.69.143,1834 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:28 kd2 ipmon[14110]: 12:01:28.256761 xl0 @1:10 b 166.102.153.16,4886 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:29 kd2 ipmon[14110]: 12:01:29.105610 xl0 @1:10 b 166.102.153.16,4886 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:36 kd2 ipmon[14110]: 12:01:36.257674 xl0 @1:10 b 166.102.153.16,4886 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:01:39 kd2 ipmon[14110]: 12:01:39.338642 xl0 @1:10 b 134.71.204.115,3792 -> 134.71.202.57,1065 PR udp len 20 36 IN
Jul 31 12:02:02 kd2 ipmon[14110]: 12:02:02.588716 xl0 @1:10 b 66.25.162.252,2868 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:02:05 kd2 ipmon[14110]: 12:02:05.555511 xl0 @1:10 b 66.25.162.252,2868 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:02:10 kd2 ipmon[14110]: 12:02:10.610751 xl0 @1:10 b 68.69.142.167,2613 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:02:11 kd2 ipmon[14110]: 12:02:11.565107 xl0 @1:10 b 66.25.162.252,2868 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:02:13 kd2 ipmon[14110]: 12:02:13.530261 xl0 @1:10 b 68.69.142.167,2613 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:02:14 kd2 ipmon[14110]: 12:02:14.729242 2x xl0 @0:3 b 134.71.203.92,138 -> 134.71.203.255,138 PR udp len 20 269 IN
Jul 31 12:02:20 kd2 ipmon[14110]: 12:02:19.529568 xl0 @1:10 b 68.69.142.167,2613 -> 134.71.202.57,10336 PR tcp len 20 48 -S IN
Jul 31 12:07:59 kd2 ipmon[14110]: 12:07:58.606378 xl0 @1:10 b 65.80.163.98,60325 -> 134.71.202.57,9074 PR tcp len 20 48 -S IN
Jul 31 12:33:33 kd2 ipmon[14110]: 12:33:32.920644 xl0 @0:3 b 80.145.78.83,4286 -> 134.71.202.47,80 PR tcp len 20 48 -S IN](https://image.slidesharecdn.com/firewallbasics-ron-190921093703/85/Firewall-basics-ron-17-320.jpg)