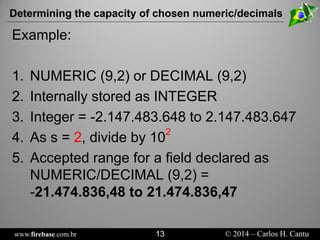
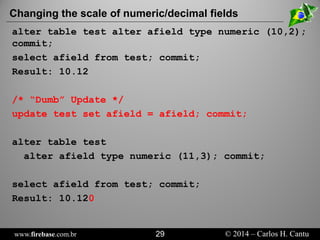
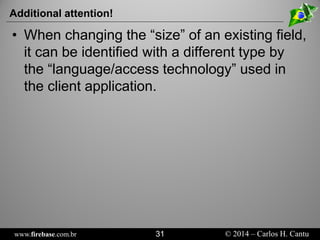
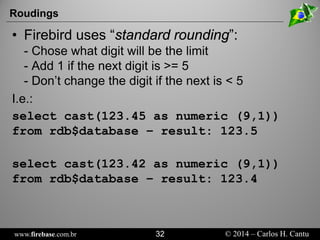
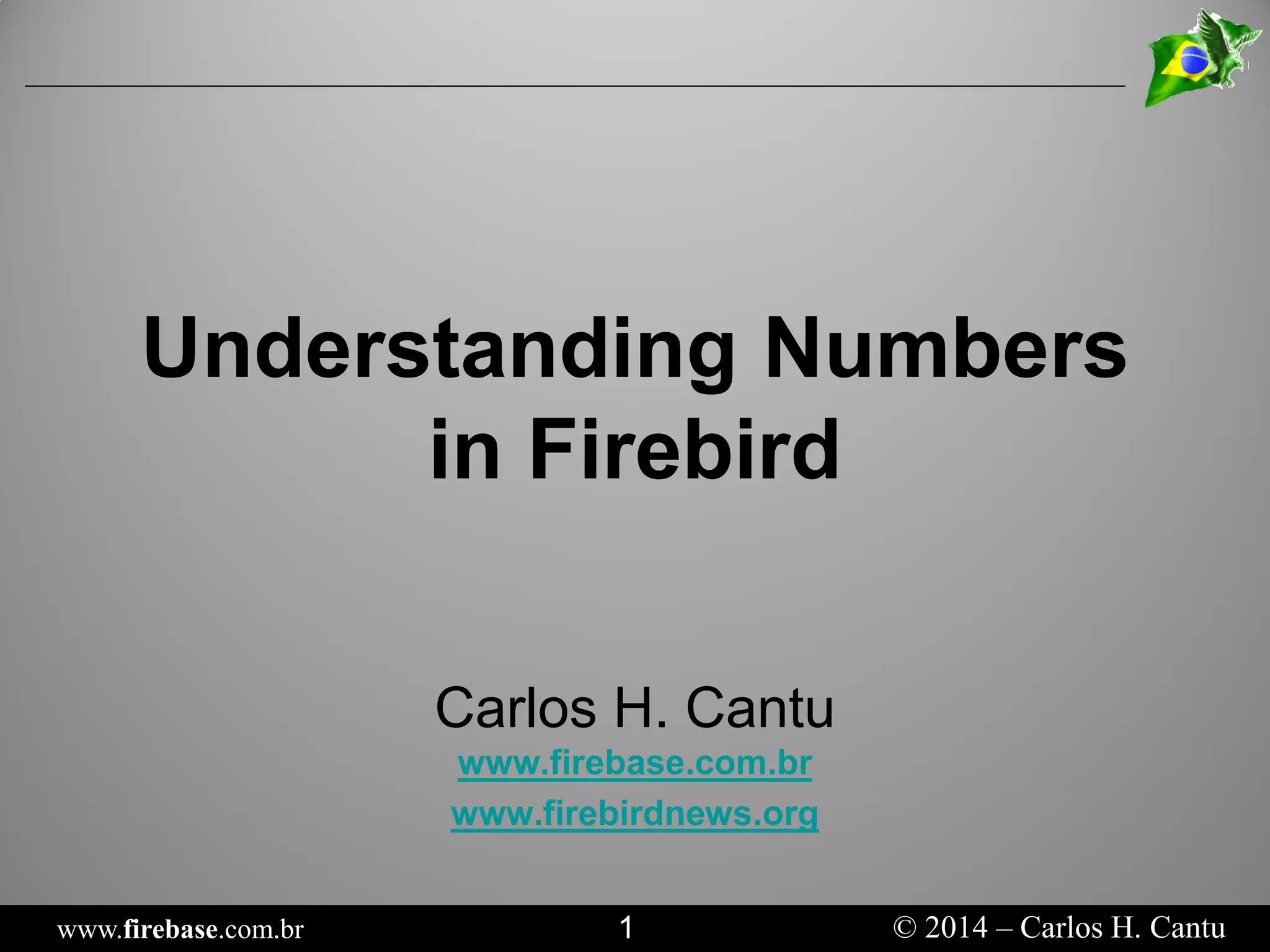
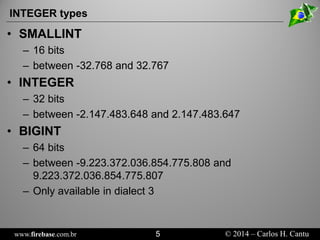
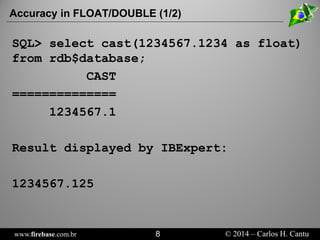
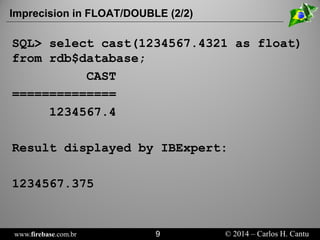
This document provides information about numbers and data types in Firebird databases. It discusses integer, floating point, numeric, and decimal data types, including their storage sizes and value ranges. It also covers data type considerations when migrating between Firebird dialects and potential issues with calculations and changing numeric scales. The document is intended to help understand internal numeric storage and proper data type usage in Firebird.




![www.firebase.com.br 10 © 2014 – Carlos H. Cantu
Fixed point
•
NUMERIC (p,s) / DECIMAL (p,s)
•
Is stored occupying either 16, 32 or 64 bits
•
p= precision (total digits) [1 <= p <= 18] s= scale (number of digits after the “comma”)
•
smust be always lower or equal to p
•
If pand sis not informed, the internal type will be INTEGER
•
In FB, palways determinates the minimum number of stored digits (not follow the standard)
•
The retrieved value is always exactly equal to the original value!](https://image.slidesharecdn.com/cantu-numericdatatypes-141105045401-conversion-gate01/85/Understanding-Numbers-in-Firebird-SQL-10-320.jpg)