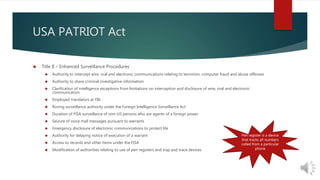
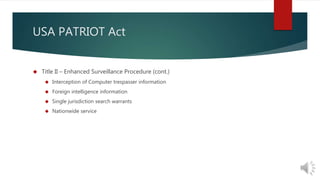
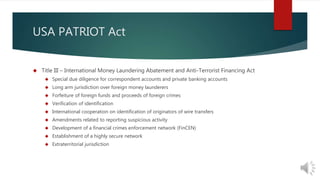
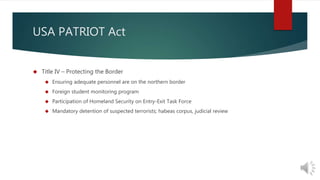
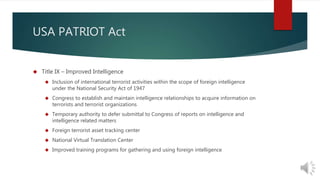
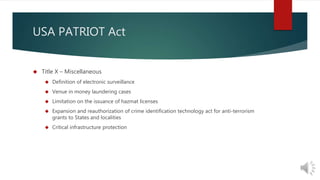
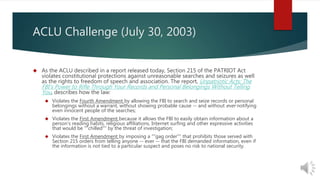
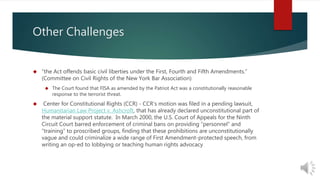
The USA PATRIOT Act was passed 45 days after 9/11 to enhance domestic security and increase surveillance powers. It impacted laws around intelligence gathering, immigration, and more. While proponents argued it granted needed powers to fight terrorism, critics said it infringed on civil liberties. There have been ongoing legal challenges around its scope and application. As time has passed, there are calls to reevaluate the act and ensure powers are not abused.