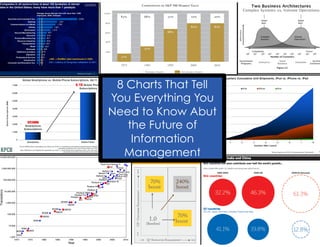
Extreme Information - 8 Charts That Tell You Everything You Need to Know
•
3 likes•2,193 views
This document summarizes the future of information management based on 8 charts. It discusses the transition from systems of record to systems of engagement, and the typical things managed in different eras from the 1960s to present. It notes how engagement and information will be differentiators, and how consumer technologies are collapsing the time between generations. It concludes that mobile strategy is now core, information management solutions are diverging, extreme information is normal, technology is driving world realignment, and the future looks very different than the past. It also lists the roles of various information professionals and notes that certification can help embrace T-shaped skills.
Report
Share
Report
Share
Download to read offline
Recommended
Information opportunities in social, mobile, and cloud technologies

My keynote presentation at the AIIM UK Roadshow.
Everything You Need to Know About Enterprise IT in Three Slides

Everything You Need to Know About...
...The History of Enterprise IT (1 slide)
...How Enterprise IT Buyers Are Changing (1 slide)
...How to Turn Information Chaos into Business Benefit (1 slide)
What is an information professional?

Focus is on understanding Information Professionals and how they connect with solution providers.
This was presented at the Document Management Solution Providers Executive Forum (http://www.aiim.org/dmspef).
Wake up, C-Suite -- #InfoChaos is Approaching

Information Governance usually puts the C-Suite to sleep. But unless they start treating it as a strategic priority, organizations run the risk of being overwhelmed by #InfoChaos. A summary of the latest research by AIIM, ARMA, and Cohasset Associates.
Presentation For IAC Federal Acquisition

This is the slideshow for the Federal Acquisition Presentation for IAC panel July 1, 2009. "Rockstars"
Big data and big content

Want to get involved in our big data/big content efforts? Direct Tweet me at jmancini77 -- I also did a blog post on this topic -- http://www.digitallandfill.org/2012/03/big-data-and-big-content-just-hype-or-a-real-opportunity.html
Reinstating Trust in the Digital Age

Talk given at PwC Digital Trust 2015 in Geneva, Switzerland.
http://www.pwc.ch/digitaltrust2015
Six Irrefutable Laws of Information Security

How can organizations balance business needs and growth with risk mitigation and security controls? These Six Irrefutable Laws of Information security can help you achieve balance.
Recommended
Information opportunities in social, mobile, and cloud technologies

My keynote presentation at the AIIM UK Roadshow.
Everything You Need to Know About Enterprise IT in Three Slides

Everything You Need to Know About...
...The History of Enterprise IT (1 slide)
...How Enterprise IT Buyers Are Changing (1 slide)
...How to Turn Information Chaos into Business Benefit (1 slide)
What is an information professional?

Focus is on understanding Information Professionals and how they connect with solution providers.
This was presented at the Document Management Solution Providers Executive Forum (http://www.aiim.org/dmspef).
Wake up, C-Suite -- #InfoChaos is Approaching

Information Governance usually puts the C-Suite to sleep. But unless they start treating it as a strategic priority, organizations run the risk of being overwhelmed by #InfoChaos. A summary of the latest research by AIIM, ARMA, and Cohasset Associates.
Presentation For IAC Federal Acquisition

This is the slideshow for the Federal Acquisition Presentation for IAC panel July 1, 2009. "Rockstars"
Big data and big content

Want to get involved in our big data/big content efforts? Direct Tweet me at jmancini77 -- I also did a blog post on this topic -- http://www.digitallandfill.org/2012/03/big-data-and-big-content-just-hype-or-a-real-opportunity.html
Reinstating Trust in the Digital Age

Talk given at PwC Digital Trust 2015 in Geneva, Switzerland.
http://www.pwc.ch/digitaltrust2015
Six Irrefutable Laws of Information Security

How can organizations balance business needs and growth with risk mitigation and security controls? These Six Irrefutable Laws of Information security can help you achieve balance.
Halvorsen on Risk Cyber Webinar

If you missed the webinar Marianne Halvorsen of http://Halvorsenonrisk.com gave on March 25th, 2013, please take a look at the slide presentation that accompanied the webinar. In it you will learn the different types of risks to your company, the costs when an event happens, and how you can protect yourself in the event of a cyber breach.
4 principles to get full benefit of the Internet of Things

The 4 "Essential Truths" your strategy needs to get the full benefits of the IoT
Protecting Intellectual Property in the Age of WikiLeaks

WikiLeaks stands as a warning for all of us responsible for protecting the digital assets and intellectual property (IP) of our organizations.
It is tempting to think that WikiLeaks, and the explosion of similar whistleblower and vigilante sites, as only interested in information from government, military, or political organizations. But a recent Forbes interview with WikiLeaks founder Julian Assange has a warning for us all.
The Myth of Zero-Risk Solutions; The Benefits of Privacy by Design

How can we enable the responsible use of data analytics while ensuring the strongest protection of personally identifiable data? By building it in as an essential design feature … enter Privacy by Design. By embedding privacy protective measures, such as strong deidentification
protocols, into the design of much-needed research and
data analytics, we will succeed in accomplishing multiple goals, thereby abandoning dated zero-sum paradigms!
Internet of Information and Services (IoIS): A Conceptual Integrative Archite...

Internet of Information and Services (IoIS): A Conceptual Integrative Archite...Antonio Marcos Alberti
Worldwide, hundreds of projects to redesign the Internet are in progress under the banner of the so-called Future Internet. Some argue that the most important thing is to the design to accommodate information exchanging, a.k.a. information-centrism. Others argue that the most important thing is to design to accommodate service-based applications. In this talk, we defend the idea that the most important thing is to design to integrate both aspects in a cohesive way. To do so, architectural blueprints should be able to solve indirections generally, to allow mobility and semantic rich search for services and contents, as well as location, hiring and dynamic invocation of services. We propose a single conceptual architecture capable of integrating the service- and information-centric approaches for the Future Internet. We call this approach as Internet of Information and Services (IoIS). ICT Trends WorldWide 

ICT Trends Worldwide, presented at the Tivit Foresight Seminar, December 2008, Finland
Chp 6 lect 6 - intellectual property rights and computer technology (shared...

discusses the foundations of intellectual property rights and how computer technology has influenced and changed the traditional issues of property rights, in particular intellectual property rights.
GTC West: The Business Case For Social Media

Presentation by Dustin Haisler and Magarita Quihuis for GTC West in Sacramento, California.
Big Data and the Future of Money 2014

This is an update of my previous presentation from 2012. I discuss several recent topics including the Witnesses Principle, the rise of Big Metadata, and the need for autonomy and possibly self-awareness for financial instruments designed to hold value for periods greater than a single human lifetime.
Io t malta_2013 Internet of Things IoT Webinar Dec 2013 #iot @Des

Webinar prepared for Diplo Foundation, December 2013
Introduction into the IoT
Inria - Cybersecurity: current challenges and Inria’s research directions

Inria white books look at major current challenges in informatics and mathematics and show actions conducted by our project-teams to these challenges. Their goal is to describe the state-of-the-art of a given topic, showing its complexity, and to present existing, as well as emerging, research directions and their expected societal impact. This white book has been edited by Steve Kremer, Ludovic Mé, Didier Rémy and Vincent Roca. They coordinated the contributions from researchers of Inria teams (the complete list of contributors is given at the end of the book). Many thanks to Janet Bertot for proof-reading this document, as well as to François Pottier, Gabriel Scherrer, and Benjamin Smith who read parts of it.
Publication date: January 2019
Towards Patient Controlled Privacy

The US Department of Health and Human Services (HHS) began publishing Linked Data in 2011 as part of an ongoing effort to inform the public and stimulate new health care applications.
The Digital Enterprise Research Institute (DERI) is recognized as one of the leading international web science research institutes interlinking technologies, information and people to advance business and benefit society.
In the US, the President's Council of Advisors on Science and Technology (PCAST) published a report on Health IT that imagines new scenarios and recommends new capabilities for interacting with health data.
At DERI, innovative ontology and software implementations demonstrate how users can create and manage fine-grained privacy preferences that restrict or grant access to their Linked Data
This session will give an overview of the HHS/DERI collaboration to implement 'data element access services' towards the realization of patient controlled privacy.
• US Department of Health and Human Services
• PCAST Health Information Technology Report
• Digital Enterprise Research Institute
• Privacy Preference Ontology and Manager
• Puelia and Linked Data API
http://semtechbizsf2012.semanticweb.com/sessionPop.cfm?confid=65&proposalid=4539
Does the Privacy of Your Personal Information Worry You?

How much information are you willing to trade away for convenience? -- and at what cost?
#AIIM14 keynote -- Turning Information Chaos into Information Opportunity

My #AIIM14 keynote -- Mancini's Law --
Organizations are systems of information networks. They only operate effectively when there are clear and predictable information flows within and between these networks.
50% annual growth in the volume of digital information means that these networks – and especially the points of connection between them – will become increasingly unstable.
Without intervention, the resulting #infochaos will threaten the viability of the entire system.
e-book here -- http://www.aiim.org/infochaos
More Related Content
What's hot
Halvorsen on Risk Cyber Webinar

If you missed the webinar Marianne Halvorsen of http://Halvorsenonrisk.com gave on March 25th, 2013, please take a look at the slide presentation that accompanied the webinar. In it you will learn the different types of risks to your company, the costs when an event happens, and how you can protect yourself in the event of a cyber breach.
4 principles to get full benefit of the Internet of Things

The 4 "Essential Truths" your strategy needs to get the full benefits of the IoT
Protecting Intellectual Property in the Age of WikiLeaks

WikiLeaks stands as a warning for all of us responsible for protecting the digital assets and intellectual property (IP) of our organizations.
It is tempting to think that WikiLeaks, and the explosion of similar whistleblower and vigilante sites, as only interested in information from government, military, or political organizations. But a recent Forbes interview with WikiLeaks founder Julian Assange has a warning for us all.
The Myth of Zero-Risk Solutions; The Benefits of Privacy by Design

How can we enable the responsible use of data analytics while ensuring the strongest protection of personally identifiable data? By building it in as an essential design feature … enter Privacy by Design. By embedding privacy protective measures, such as strong deidentification
protocols, into the design of much-needed research and
data analytics, we will succeed in accomplishing multiple goals, thereby abandoning dated zero-sum paradigms!
Internet of Information and Services (IoIS): A Conceptual Integrative Archite...

Internet of Information and Services (IoIS): A Conceptual Integrative Archite...Antonio Marcos Alberti
Worldwide, hundreds of projects to redesign the Internet are in progress under the banner of the so-called Future Internet. Some argue that the most important thing is to the design to accommodate information exchanging, a.k.a. information-centrism. Others argue that the most important thing is to design to accommodate service-based applications. In this talk, we defend the idea that the most important thing is to design to integrate both aspects in a cohesive way. To do so, architectural blueprints should be able to solve indirections generally, to allow mobility and semantic rich search for services and contents, as well as location, hiring and dynamic invocation of services. We propose a single conceptual architecture capable of integrating the service- and information-centric approaches for the Future Internet. We call this approach as Internet of Information and Services (IoIS). ICT Trends WorldWide 

ICT Trends Worldwide, presented at the Tivit Foresight Seminar, December 2008, Finland
Chp 6 lect 6 - intellectual property rights and computer technology (shared...

discusses the foundations of intellectual property rights and how computer technology has influenced and changed the traditional issues of property rights, in particular intellectual property rights.
GTC West: The Business Case For Social Media

Presentation by Dustin Haisler and Magarita Quihuis for GTC West in Sacramento, California.
Big Data and the Future of Money 2014

This is an update of my previous presentation from 2012. I discuss several recent topics including the Witnesses Principle, the rise of Big Metadata, and the need for autonomy and possibly self-awareness for financial instruments designed to hold value for periods greater than a single human lifetime.
Io t malta_2013 Internet of Things IoT Webinar Dec 2013 #iot @Des

Webinar prepared for Diplo Foundation, December 2013
Introduction into the IoT
Inria - Cybersecurity: current challenges and Inria’s research directions

Inria white books look at major current challenges in informatics and mathematics and show actions conducted by our project-teams to these challenges. Their goal is to describe the state-of-the-art of a given topic, showing its complexity, and to present existing, as well as emerging, research directions and their expected societal impact. This white book has been edited by Steve Kremer, Ludovic Mé, Didier Rémy and Vincent Roca. They coordinated the contributions from researchers of Inria teams (the complete list of contributors is given at the end of the book). Many thanks to Janet Bertot for proof-reading this document, as well as to François Pottier, Gabriel Scherrer, and Benjamin Smith who read parts of it.
Publication date: January 2019
Towards Patient Controlled Privacy

The US Department of Health and Human Services (HHS) began publishing Linked Data in 2011 as part of an ongoing effort to inform the public and stimulate new health care applications.
The Digital Enterprise Research Institute (DERI) is recognized as one of the leading international web science research institutes interlinking technologies, information and people to advance business and benefit society.
In the US, the President's Council of Advisors on Science and Technology (PCAST) published a report on Health IT that imagines new scenarios and recommends new capabilities for interacting with health data.
At DERI, innovative ontology and software implementations demonstrate how users can create and manage fine-grained privacy preferences that restrict or grant access to their Linked Data
This session will give an overview of the HHS/DERI collaboration to implement 'data element access services' towards the realization of patient controlled privacy.
• US Department of Health and Human Services
• PCAST Health Information Technology Report
• Digital Enterprise Research Institute
• Privacy Preference Ontology and Manager
• Puelia and Linked Data API
http://semtechbizsf2012.semanticweb.com/sessionPop.cfm?confid=65&proposalid=4539
What's hot (20)
4 principles to get full benefit of the Internet of Things

4 principles to get full benefit of the Internet of Things
Protecting Intellectual Property in the Age of WikiLeaks

Protecting Intellectual Property in the Age of WikiLeaks
Power of Social Collaboration and Business Technology Adoption

Power of Social Collaboration and Business Technology Adoption
The Myth of Zero-Risk Solutions; The Benefits of Privacy by Design

The Myth of Zero-Risk Solutions; The Benefits of Privacy by Design
Future of technical innovation 3 trends that impact enterprise users

Future of technical innovation 3 trends that impact enterprise users
Internet of Information and Services (IoIS): A Conceptual Integrative Archite...

Internet of Information and Services (IoIS): A Conceptual Integrative Archite...
Chp 6 lect 6 - intellectual property rights and computer technology (shared...

Chp 6 lect 6 - intellectual property rights and computer technology (shared...
[Challenge:Future] Rallying Youth Against Cyber Crime![[Challenge:Future] Rallying Youth Against Cyber Crime](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Challenge:Future] Rallying Youth Against Cyber Crime](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Challenge:Future] Rallying Youth Against Cyber Crime
Io t malta_2013 Internet of Things IoT Webinar Dec 2013 #iot @Des

Io t malta_2013 Internet of Things IoT Webinar Dec 2013 #iot @Des
Inria - Cybersecurity: current challenges and Inria’s research directions

Inria - Cybersecurity: current challenges and Inria’s research directions
Viewers also liked
Does the Privacy of Your Personal Information Worry You?

How much information are you willing to trade away for convenience? -- and at what cost?
#AIIM14 keynote -- Turning Information Chaos into Information Opportunity

My #AIIM14 keynote -- Mancini's Law --
Organizations are systems of information networks. They only operate effectively when there are clear and predictable information flows within and between these networks.
50% annual growth in the volume of digital information means that these networks – and especially the points of connection between them – will become increasingly unstable.
Without intervention, the resulting #infochaos will threaten the viability of the entire system.
e-book here -- http://www.aiim.org/infochaos
29 warning signs of digital disruption

Are you prepared for the coming Digital Disruption? 29 warning signs of Information Chaos...
Three Faces of Information Governance

Track keynote presentation at #otew2013, Open Text Enterprise World. Why our approach to information governance needs to change -- and focus on the BUSINESS.
I'm Mad as Hell -- The CEO and Technology Strategy

My comments at the #ASAE Technology Conference (#tech13) on the need for the C-Suite to increase their engagement on technology strategy.
How can I get rid of paper in my business processes?

Highlights of new AIIM research, Paper Wars, released to coincide with World Paper Free Day -- http://info.aiim.org/paper-wars
Updated! -- #AIIM16 keynote -- Why the H**** Should You Care About Informatio...

My keynote at #AIIM16 -- Digital Disruption and the critical need for information professionals.
How effective is your marketing program?

What is your marketing ROI? How do you know? Latest benchmark survey from AIIM
5 Tips for the Document Management Channel

Content and document management opportunities for resellers and integrators.
Information Management on Mobile Steroids

A discussion of how mobile will transform information management strategies in our organizations.
Social business and innovation

Originally delivered at Oracle Social Business Seminar - for more information on becoming a Certified Information Professional, go to http://www.aiim.org/certification.
How is Big Content Different From Big Data?

Moving the Mountain -- Evanta CIO Presentation on Big Data and Big Content -- central premise -- Big Data analysis without a strategy for the Content that usually fulfills the analytics is a waste of time.
NEW VERSION! -- Where is content management headed?

"ECM" as we know it is about to become something much different than it has been. Think Big.
Occupy IT Manifesto

A look at some of the forces reshaping enterprise IT -- and how the business looks at IT.
What's in your digital landfill?

As the volume of electronic information surrounding us grows exponentially, how will we deal with it? Do you know what is in your digital landfill?
[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...![[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Learn about the risks and challenges of typical imaging and 4 ways you can make sure your captured information is protected.
For more information on Scanning & Capture, visit our resource center: http://www.aiim.org/Resource-Centers/Scanning-and-Capture.
Information Management: An Oxymoron

some recent data and trends related to the (mis) management of electronic information
Viewers also liked (20)
Does the Privacy of Your Personal Information Worry You?

Does the Privacy of Your Personal Information Worry You?
#AIIM14 keynote -- Turning Information Chaos into Information Opportunity

#AIIM14 keynote -- Turning Information Chaos into Information Opportunity
I'm Mad as Hell -- The CEO and Technology Strategy

I'm Mad as Hell -- The CEO and Technology Strategy
How can I get rid of paper in my business processes?

How can I get rid of paper in my business processes?
Updated! -- #AIIM16 keynote -- Why the H**** Should You Care About Informatio...

Updated! -- #AIIM16 keynote -- Why the H**** Should You Care About Informatio...
NEW VERSION! -- Where is content management headed?

NEW VERSION! -- Where is content management headed?
[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...![[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar Slides] 4 Ways to Protect Your Captured Data from Theft and Complian...
Similar to Extreme Information - 8 Charts That Tell You Everything You Need to Know
Why Should Consultants and Systems Integrators Become Certified Information P...

How can AIIM's Certified Information Professional program help make your organization more effective? How can you use it to differentiate your firm in a very crowded IT solutions marketplace?
How can social technologies be used to drive processes and innovation?

How can social technologies be used to drive processes and innovation? Delivered at Oracle/AIIM Social Business Seminar in NYC.
20111031 KMWorld 2011 Applying the Social Business Roadmap to Your Organization

This workshop delivered at KMWorld 2011 outlined the essential steps in the AIIM social business roadmap, presented a high-level assessment to conduct in order to develop an organization-specific roadmap, and outlined key strategies for the governance portion of the roadmap.
Information governance in the Facebook Era

For a version with voice, go to...
http://www.screencast.com/t/KcCvgnLW9Hrk
In the social, mobile and cloud era, what does it take to be an Information P...

Summary of massive changes underway in the enterprise IT marketplace being driven by social, mobile, and cloud, and the implications of these changes on what it means to be an information professional.
http://www.aiim.org/certification
20120208 ARMA Detroit Social Media Governance

This presentation at the ARMA Detroit Chapter focused on how to apply governance processes and principles to social media services and solutions.
Information Management in a Web 2.0 World May 2009

The current information management polices, standards, processes and systems are not fit for purpose for Web 2.0 working practices, and specifically for the emerging Cloud Computing models.
Understanding The Big Data Opportunity Final

A presentation given describing the opportunities for clients and agencies in the BIG Data space
Are You Ready for the Era of Big Data and Extreme Information Management?

This is the first part of a 5-part series on the Information Challenges facing organizations. A white paper describing these challenges can be found here - http://pages2.aiim.org/CIPWebPage_InfoProWP.html
Content Opportunities in Revolutionary Times

My Open Text ContentWorld keynote - The impact of SharePoint, Social, and Mobile on the Future of Information Management -- and the emerging role of information professionals
New Information Certification

Become a Certified Information Professional (CIP), AIIM's newly-launched certification. Earning this designation demonstrates your ability to solve an organization's existing information-related problems as well as plan for the future.
Collaboration & Social Media New Challenges For Records Management

Presentation was delivered as the keynote of the 27 Feb 2009, ARMA Northern VA chapter conference (http://www.armamar.org/nova/programs/ARMA%20NOVA%202009%20Seminar%20Brochure-c.pdf).
A future history of content management

An exploration of how Systems of Engagement connect with Systems of Record; Excerpts from an AIIM Task Force headed by noted author Geoffrey Moore.
Thinking about Technology, Risk, and Change Management Through a Social Lens

Keynote presentation originally given at the Newsgator Collective conference.
Digital Renaissance - Alfresco EMEA Partner Day

The Digital Renaissance is the convergence of the forces of Cloud, Mobile, Big Data and Social affecting the way that all industries do business. A virtuous cycle of customer engagement and business agility drive the redesign of business models and they way we all work together. New technologies and architectures are required to participate in the biggest changes to affect business since who knows when.
20111206 AIIM Cornhusker Social Media Governance

This webinar delivered to the AIIM Cornhusker chapter describes key considerations for social media governance in
Similar to Extreme Information - 8 Charts That Tell You Everything You Need to Know (20)
Why Should Consultants and Systems Integrators Become Certified Information P...

Why Should Consultants and Systems Integrators Become Certified Information P...
How can social technologies be used to drive processes and innovation?

How can social technologies be used to drive processes and innovation?
20111031 KMWorld 2011 Applying the Social Business Roadmap to Your Organization

20111031 KMWorld 2011 Applying the Social Business Roadmap to Your Organization
In the social, mobile and cloud era, what does it take to be an Information P...

In the social, mobile and cloud era, what does it take to be an Information P...
Information Management in a Web 2.0 World May 2009

Information Management in a Web 2.0 World May 2009
Are You Ready for the Era of Big Data and Extreme Information Management?

Are You Ready for the Era of Big Data and Extreme Information Management?
Collaboration & Social Media New Challenges For Records Management

Collaboration & Social Media New Challenges For Records Management
The nature of social software and how it changes the business - Cecil Dijoux

The nature of social software and how it changes the business - Cecil Dijoux
Nature of Social Software and how it transforms the business

Nature of Social Software and how it transforms the business
Thinking about Technology, Risk, and Change Management Through a Social Lens

Thinking about Technology, Risk, and Change Management Through a Social Lens
More from John Mancini
5 things you didn't know about automating governance and compliance

Prospectus and presentation for upcoming multi-client research project by AIIM on the intersection between artificial intelligence & machine learning and information governance.
OpenText keynote -- Enterprise World 2018

My keynote at the content session at Enterprise World, Toronto Canada, July 10, 2018
Digital Disruption and the Challenge of Keeping Members Engaged

Some thoughts about how disruptive technologies impact the value proposition for how associations engage their members. From my keynote at the Aptify User Conference last year.
Keynote - AIIM17 -- Forces of Change in Content Management

How is content management changing? How should "ECM" evolve? Here are my thoughts during my AIIM17 keynote.
4 Reasons Finance Execs Should be Transformation Ninjas

Digital Transformation and Digital Disruption are on every C-level wish list. The CFO is a untapped resource in this fight -- and should help lead it.
5 Strategies to Avoid the Digital Riptide

Keynote presentation at the ABBYY Partner Conference in Tokyo -- How can you turn digital DISRUPTION into digital TRANSFORMATION? I did a broader accompanying blog post on some of these themes here -- http://info.aiim.org/digital-landfill/3-lessons-from-japanese-trains-information-management-and-the-internet-of-things
#AIIM16 wrap up -- what did it all mean?

Summary of 20 great presentations at #AIIM16 in 20 slides. Check them out!
From Microfilm to Big Data - How Can One Brain Handle This Much Change Withou...

How is Digital Disruption changing the role of Information in our organizations? How do we shift the focus from the "T"(technology) in IT to the "I" (information)?
Information Governance -- Necessary Evil or a Bridge to the Future?

How the world is changing -- Old paradigms are being stretched to the breaking point
How we usually think about governance -- It’s not just about what you keep
How should we respond? -- Building an action plan for the next 2-3 years
Intelligent information: New Rules for Managing the Customer Experience

Presentation initially delivered at Kodak Global Directions conference, 9-24-13
Is IT Really the Villain? - Future of Technology in the Enterprise

Is IT the Villain? - The Future of Technology in the Enterprise -- A summary of my keynote presentation at the CITE Conference and Expo in San Francisco. How do organizations deal with the advantages of social, mobile, and consumer technologies without losing control?
Extreme Buyers + Extreme Governance + Extreme Engagement

My keynote presentation at #AIIM13 -- Extreme Buyers + Extreme Governance + Extreme Engagement = Information Lagniappe
Are you prepared for the impact of consumerization?

A discussion of the impact of consumer technology on enterprise IT systems and the need for a change in how IT and CIOs approach this question.
Don Draper's 3 Rules of Content Marketing

A focus on how marketing has changed -- but also on how some elements have stayed the same -- using Don's perspectives as a frame. The presentation describes how the role of content has changed, and the increasing challenges facing organizations to deliver content that is targeted at the role, buying stage, and preferred delivery of prospects and leads.
More from John Mancini (14)
5 things you didn't know about automating governance and compliance

5 things you didn't know about automating governance and compliance
Digital Disruption and the Challenge of Keeping Members Engaged

Digital Disruption and the Challenge of Keeping Members Engaged
Keynote - AIIM17 -- Forces of Change in Content Management

Keynote - AIIM17 -- Forces of Change in Content Management
4 Reasons Finance Execs Should be Transformation Ninjas

4 Reasons Finance Execs Should be Transformation Ninjas
From Microfilm to Big Data - How Can One Brain Handle This Much Change Withou...

From Microfilm to Big Data - How Can One Brain Handle This Much Change Withou...
Information Governance -- Necessary Evil or a Bridge to the Future?

Information Governance -- Necessary Evil or a Bridge to the Future?
Intelligent information: New Rules for Managing the Customer Experience

Intelligent information: New Rules for Managing the Customer Experience
Is IT Really the Villain? - Future of Technology in the Enterprise

Is IT Really the Villain? - Future of Technology in the Enterprise
Extreme Buyers + Extreme Governance + Extreme Engagement

Extreme Buyers + Extreme Governance + Extreme Engagement
Are you prepared for the impact of consumerization?

Are you prepared for the impact of consumerization?
Recently uploaded
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Recently uploaded (20)
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Extreme Information - 8 Charts That Tell You Everything You Need to Know
- 1. 8 Charts That Tell You Everything You Need to Know Abut the Future of Information Management
- 2. We are in uncharted waters.
- 4. Systems of Engagement Social and Era Internet Cloud Systems of Record Years 1960-1975 1975-1992 1992-2001 2001-2009 2010-2015 Typical A batch A dept A A web An thing trans process document page interaction managed Best known Digital IBM Microsoft Google Facebook company Equipment Content Social Image Document Content mgmt Microfilm Business Mgmt Mgmt Mgmt focus Systems
- 5. Consideration Systems of Record Systems of Engagement Focus Transactions Interactions Governance Command & Control Collaboration Core Elements Facts & Commitments Ideas & Nuances Value Single Source of Truth Discovery & Dialog Standard Accurate & Complete Immediate & Accessible Content Authored Communal Primary Record Type Documents Conversations Searchability Easy Hard Usability User is trained User “knows” Accessibility Regulated & Contained Ad Hoc & Open Retention Permanent Transient Policy Focus Security (Protect Assets) Privacy (Protect Users)
- 6. Source: Gallup, Customer Engagement | What’s Your Engagement Ratio?
- 7. Conclusion #1: ENGAGEMENT will differentiate who survives – and who doesn’t.
- 9. Conclusion #2: INFORMATION is to our age what OIL was to the last.
- 10. Source: Mary Meeker, Internet Trends, D10 Conference
- 11. Conclusion #3: Consumer technologies are collapsing the “breathing room” we have between generations of technology.
- 12. Source: Mary Meeker, Internet Trends, D10 Conference
- 13. Conclusion #4: If you don’t have a mobile strategy, you don’t have a strategy.
- 14. Source: Geoffrey Moore, Escape Velocity
- 15. Conclusion #5: The ECM industry is diverging into two kinds of solutions – with different sets of winners.
- 16. Source: McKinsey & Company
- 17. Conclusion #6: EXTREME INFORMATION is the new normal.
- 18. Source: BRICs: The changing faces of global power, By Alan Beattie, Financial Times, January 17 2010
- 19. Conclusion #7: Technology is driving a massive realignment of the world itself.
- 20. Source: http://letshavetheconversation.blogspot.com/2011/11/moores-law-economics-of-abundance.html
- 21. Conclusion #8: We are approaching the second half of the chessboard and it doesn’t look like anywhere we’ve been before.
- 22. Who are all these people? IT Legal professional Risk/Liability Records Manager Focus Digital Archivist Business Process Owners Professionals Information Value Focus Business Analyst Knowledge Manager Information/Data Scientist Ent Information Manager Governance Focus Info/Data Stewards Ent Information Architect Social Focus Information Curators Community Managers Most roles from Deb Logan and Regina Casonata, Gartner
- 23. Blind Men and the Elephant, John Godfrey Saxe 23
- 24. Get certified today. $265 at Prometrics All the preparatory content is free. Embrace T-shaped skills. AIIM.org/certification
- 25. Thank you. John F. Mancini President, AIIM @jmancini77 DigitalLandfill.org
