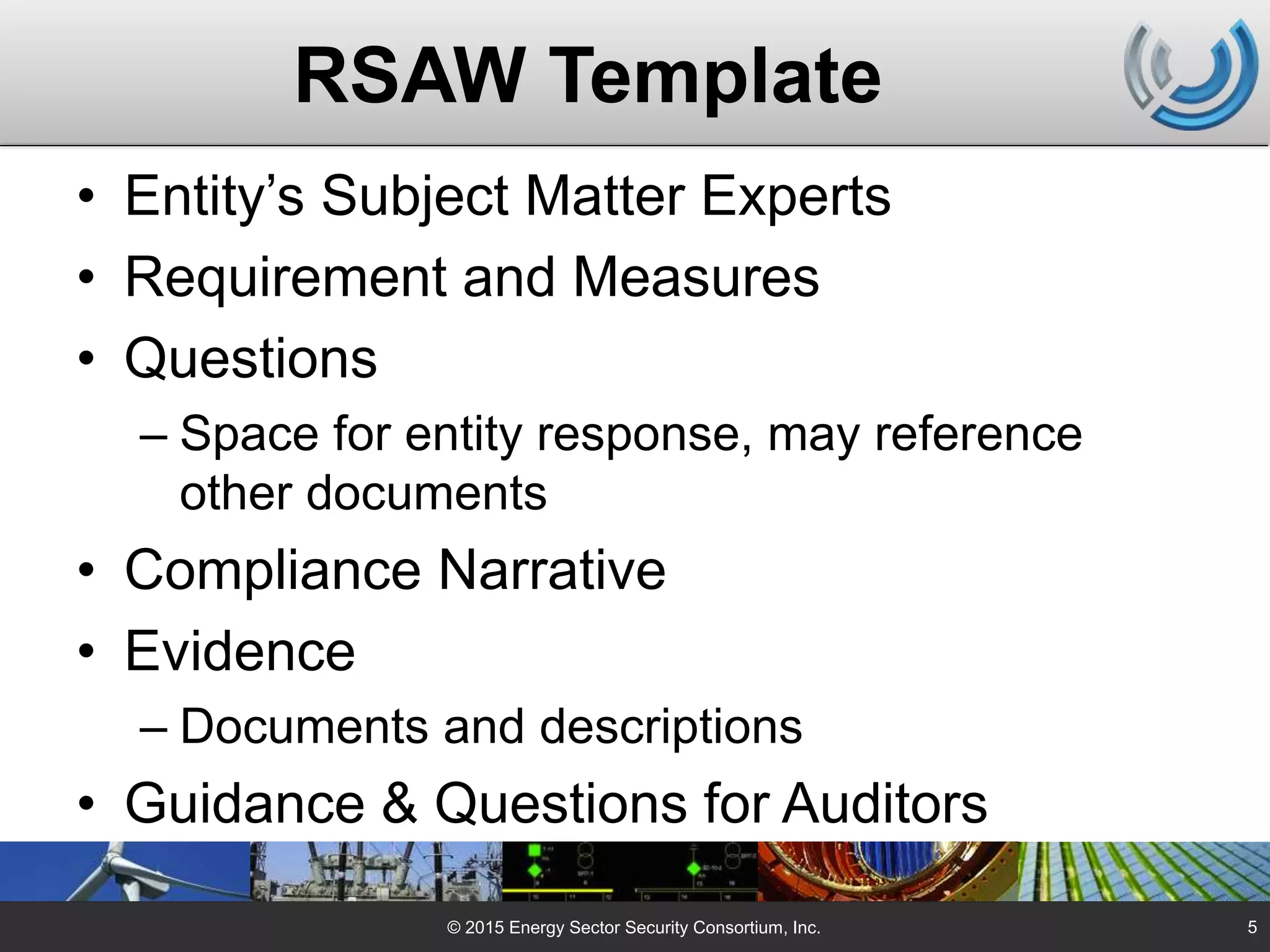
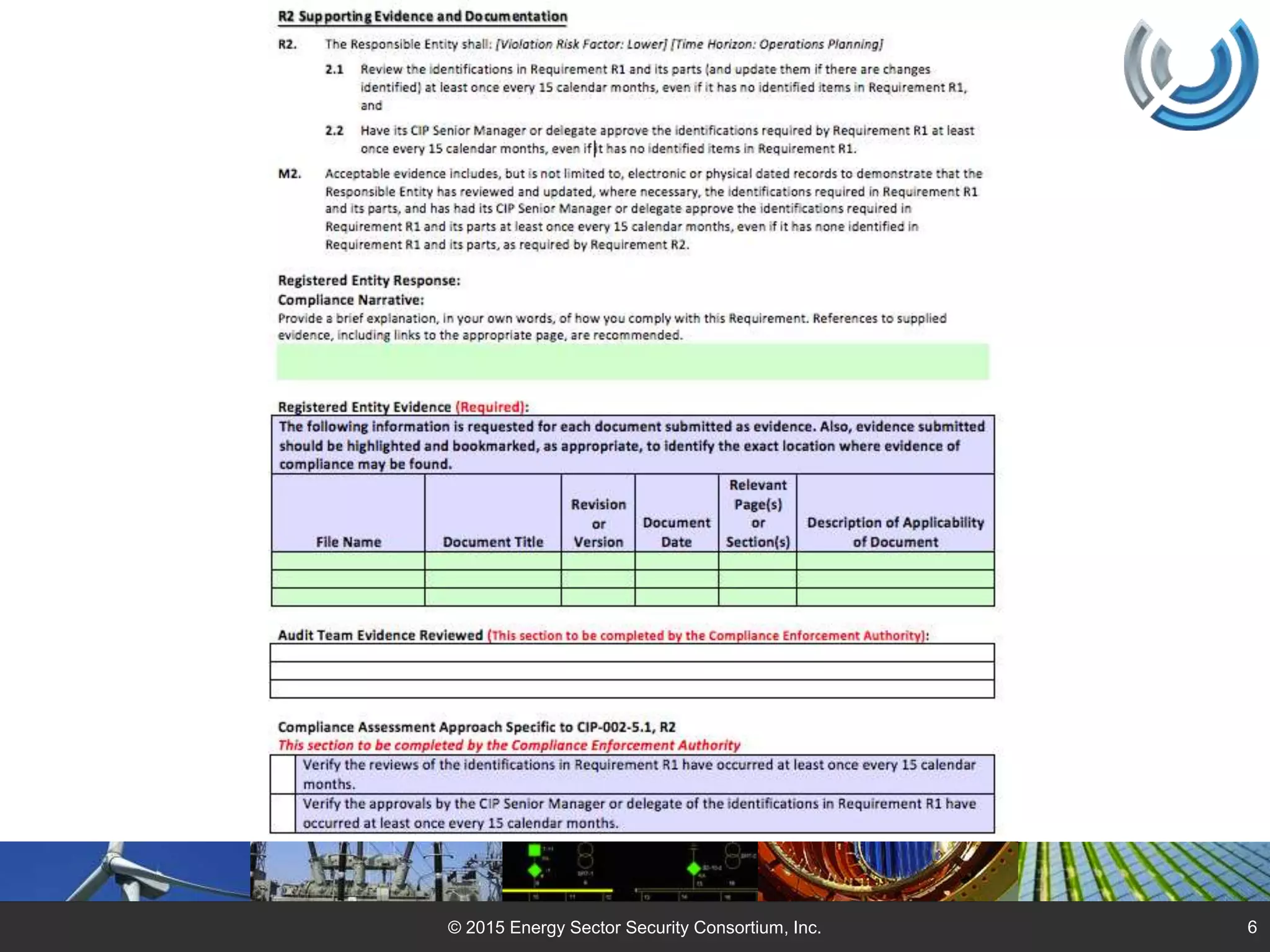
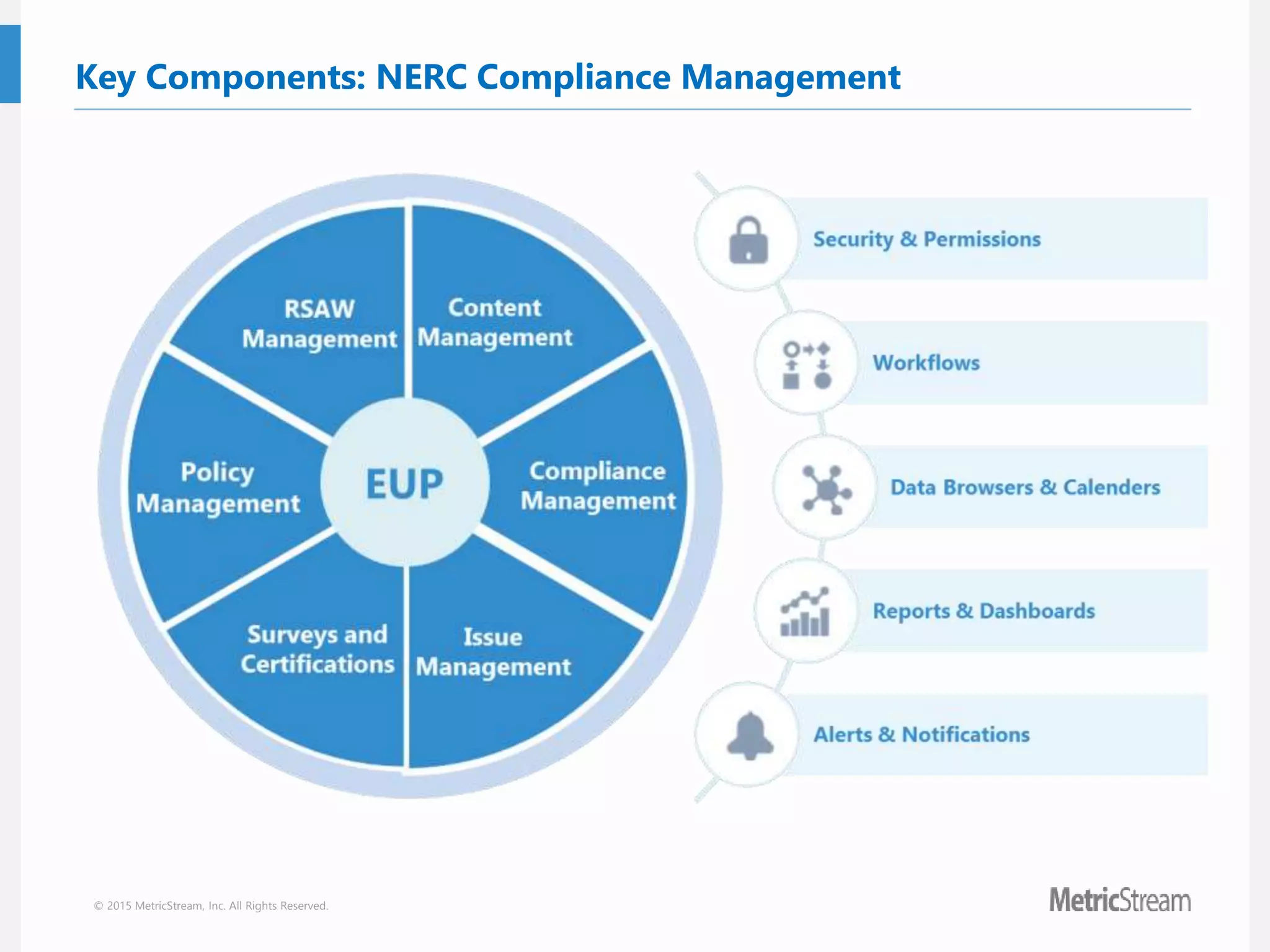
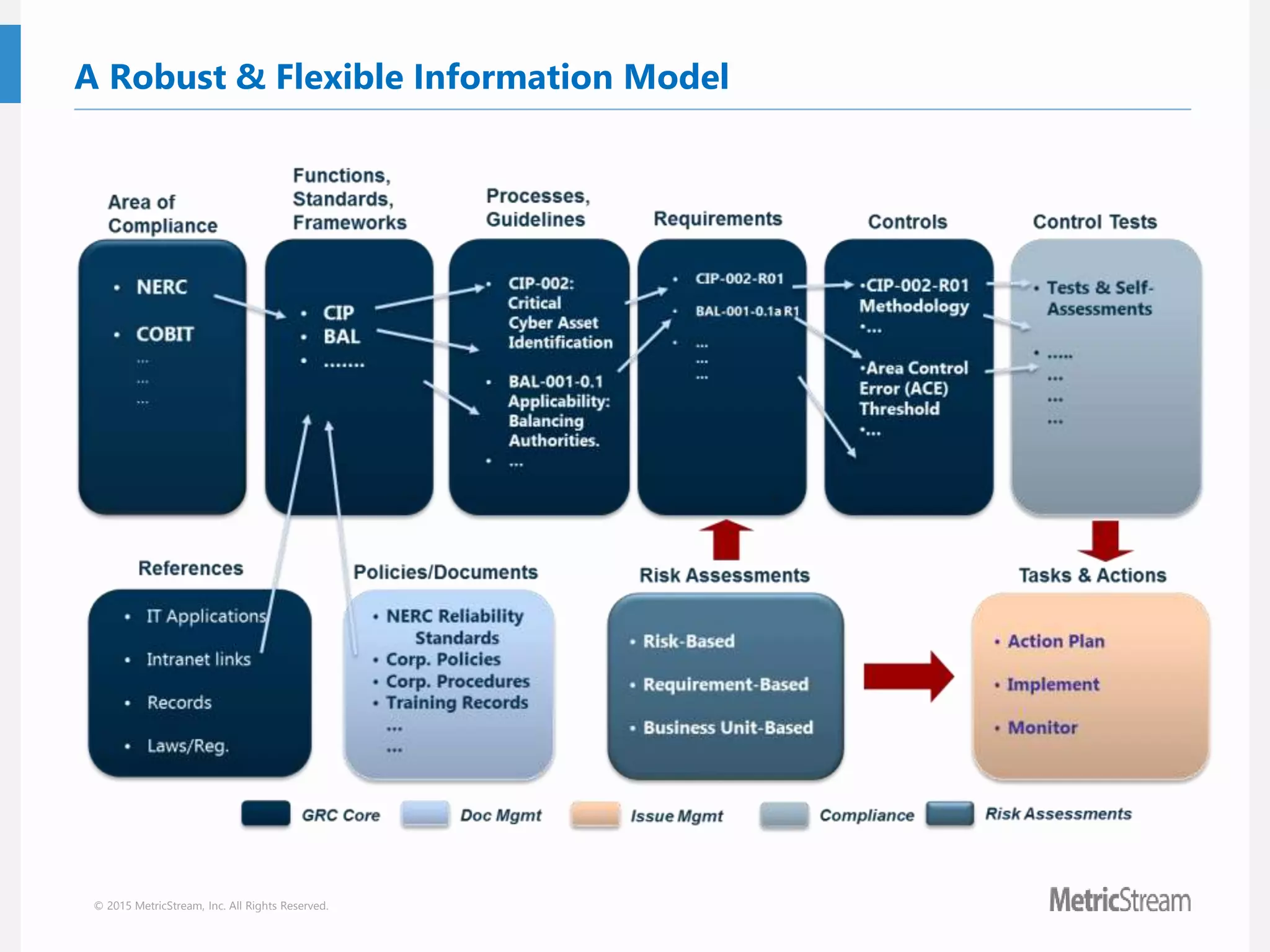
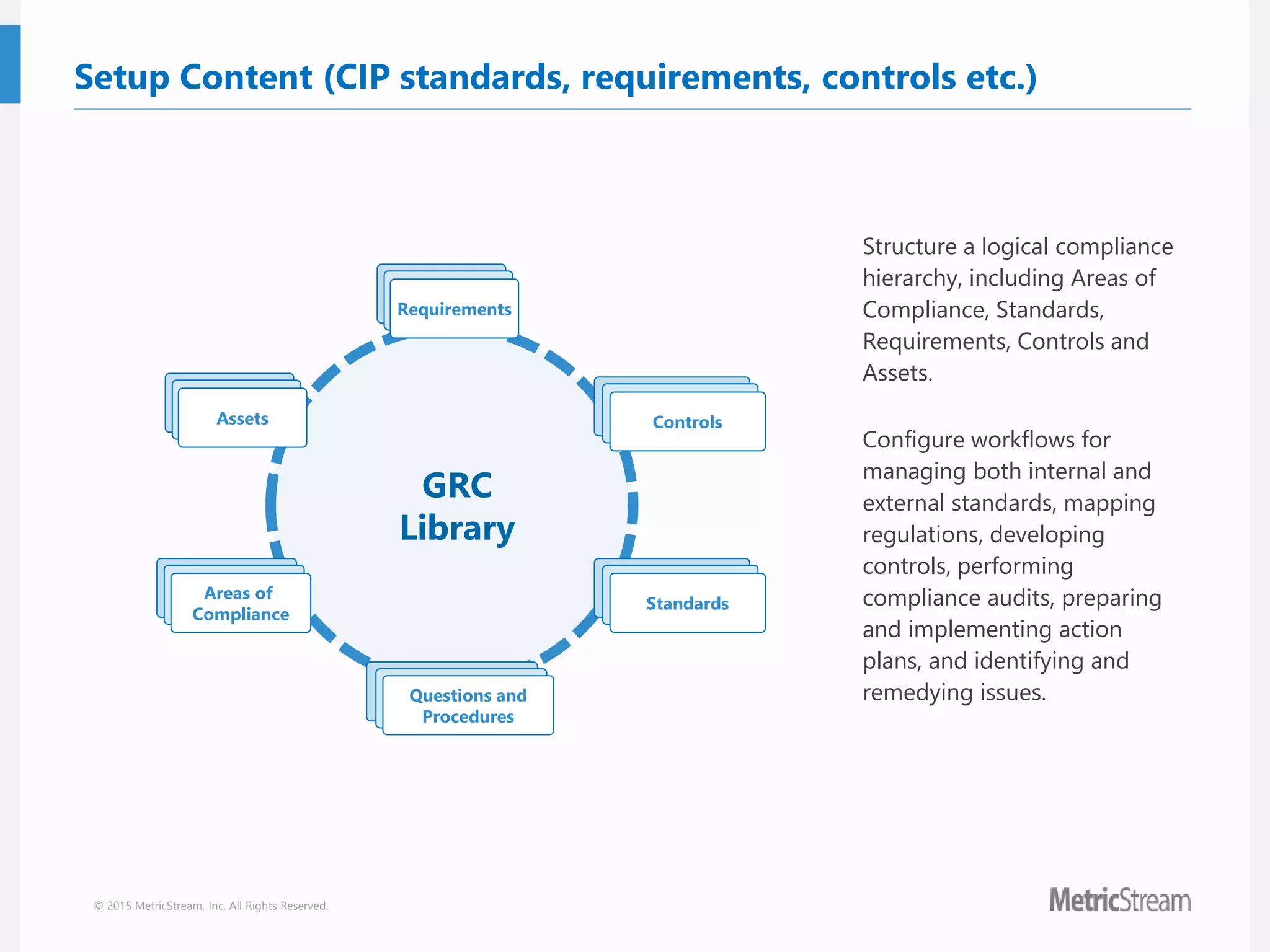
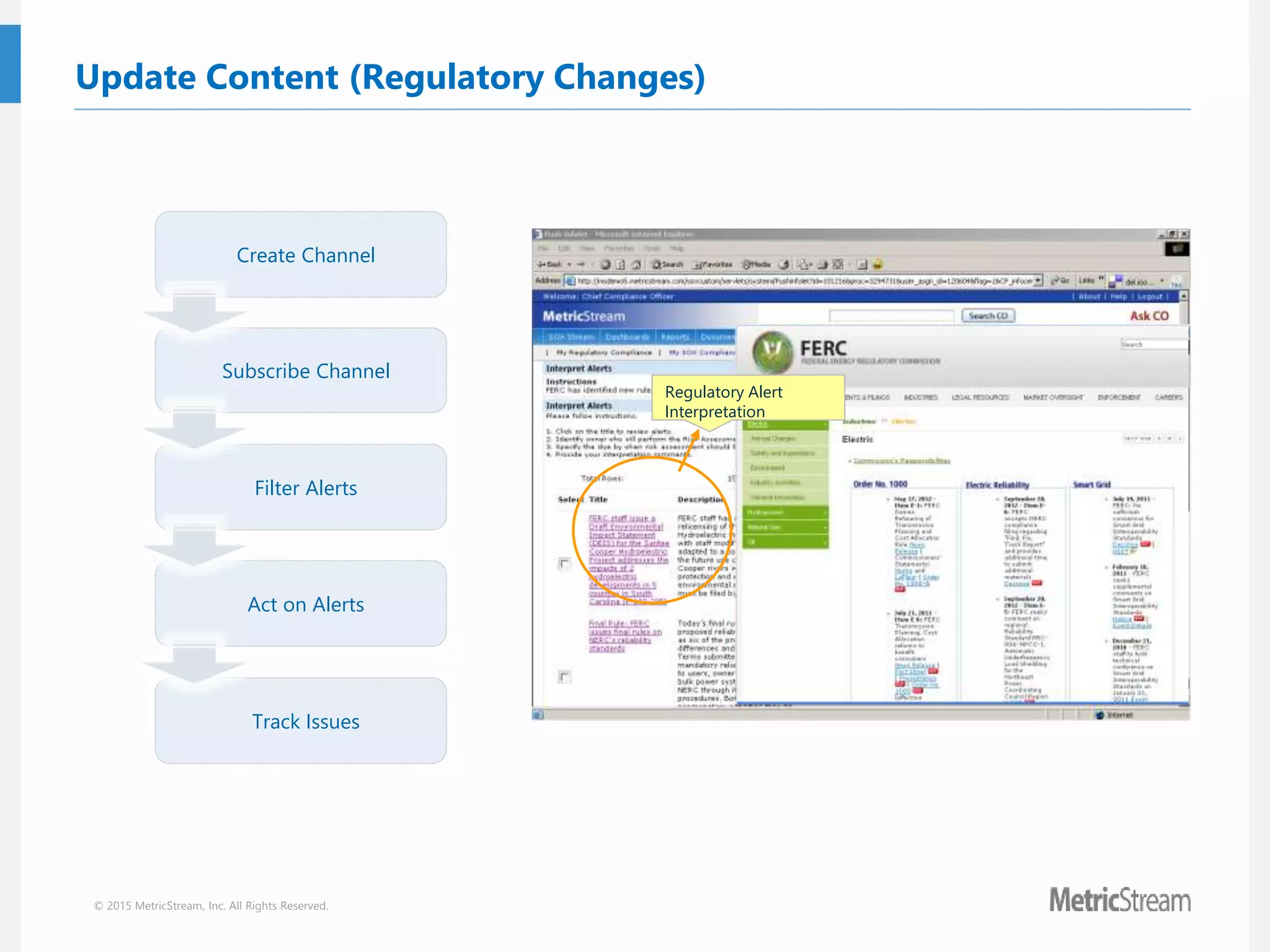
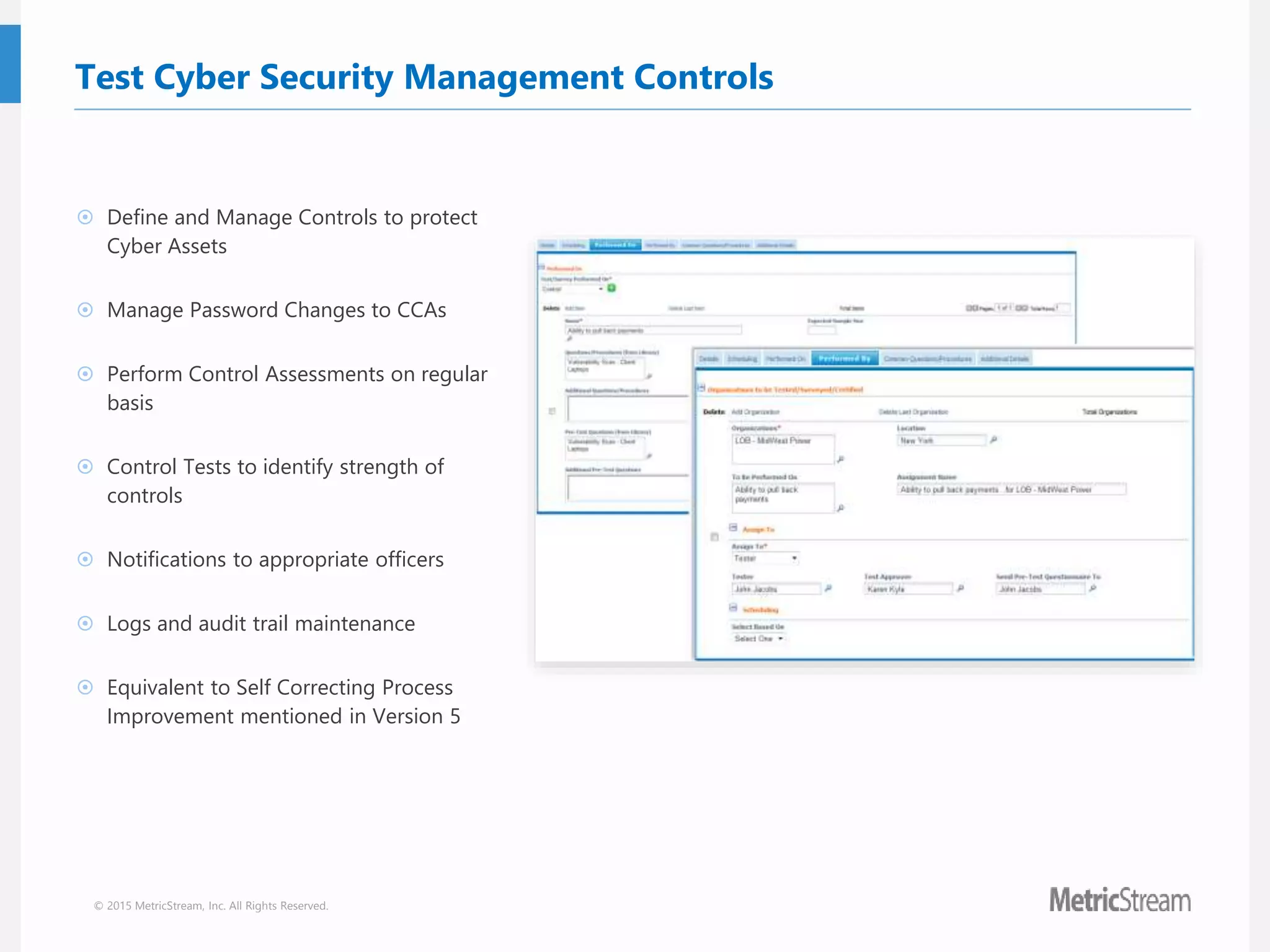
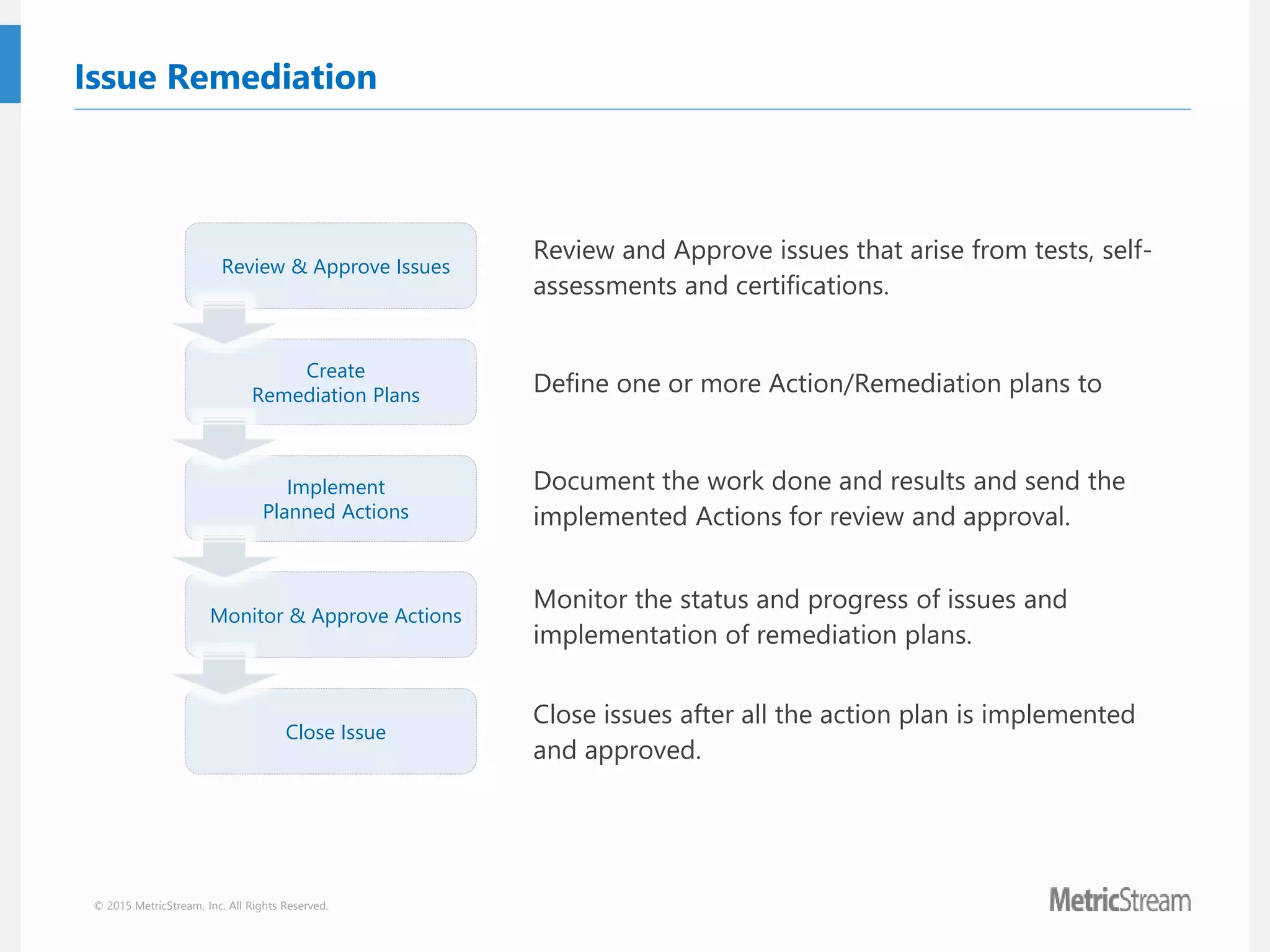
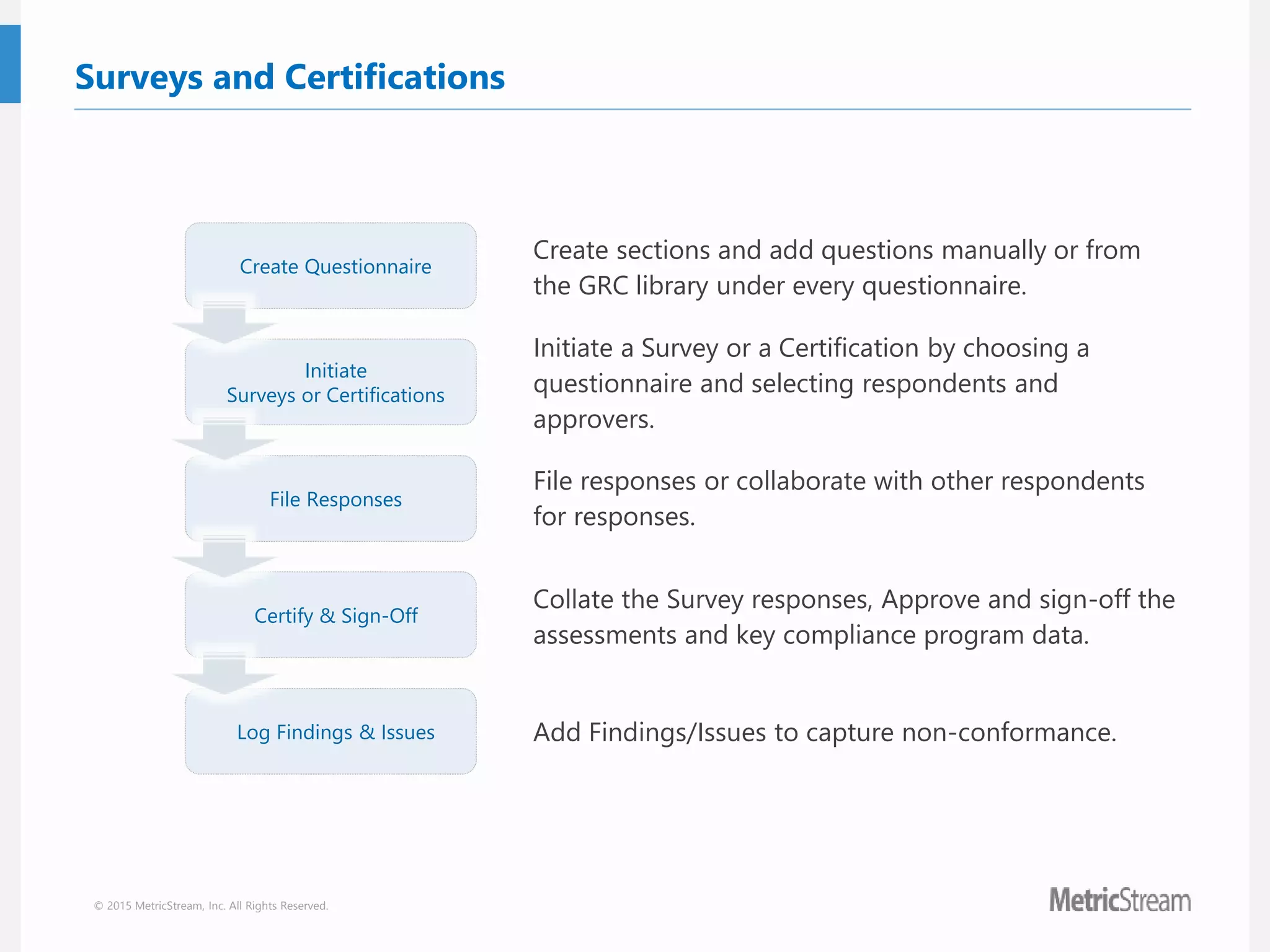
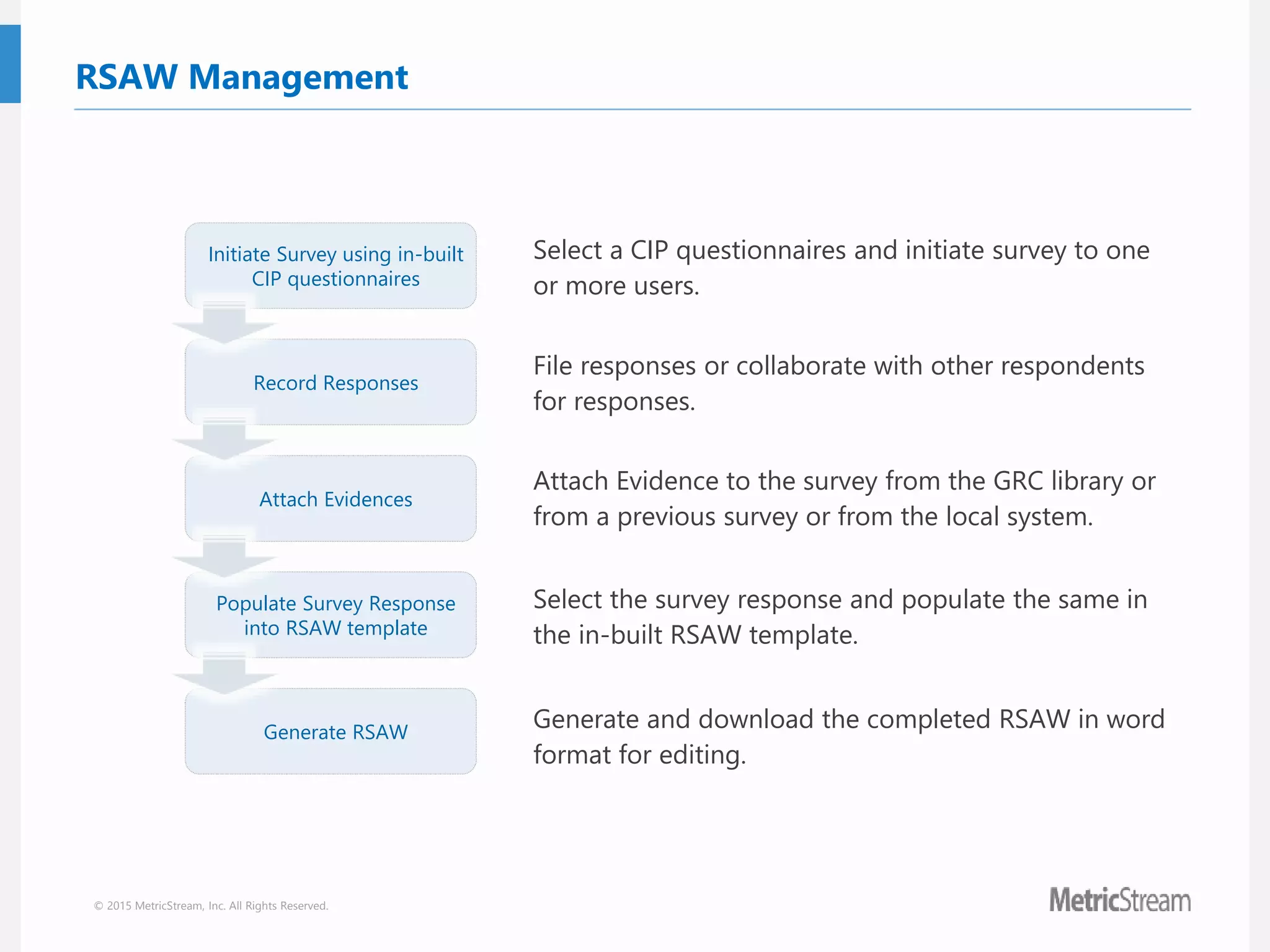
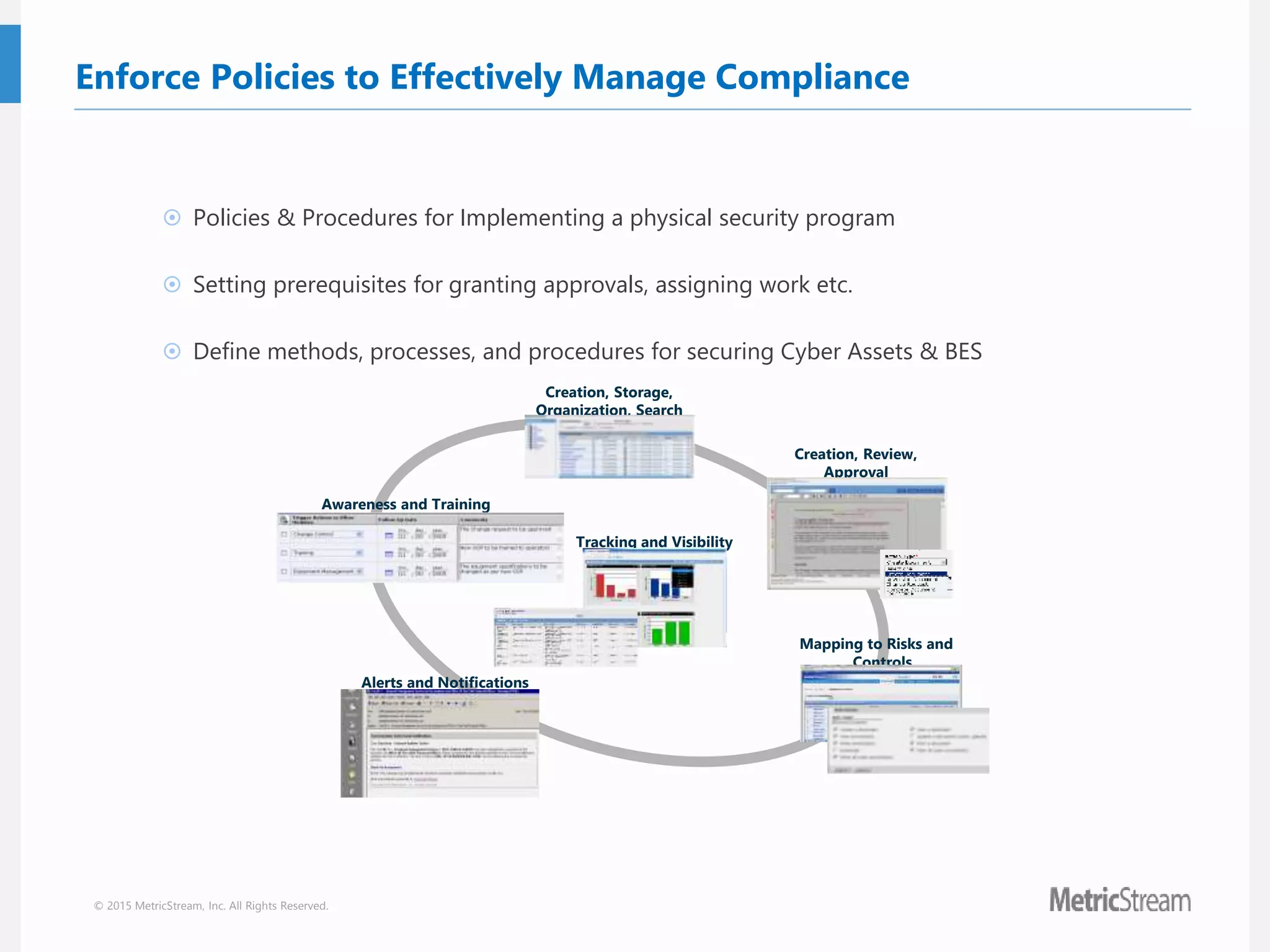
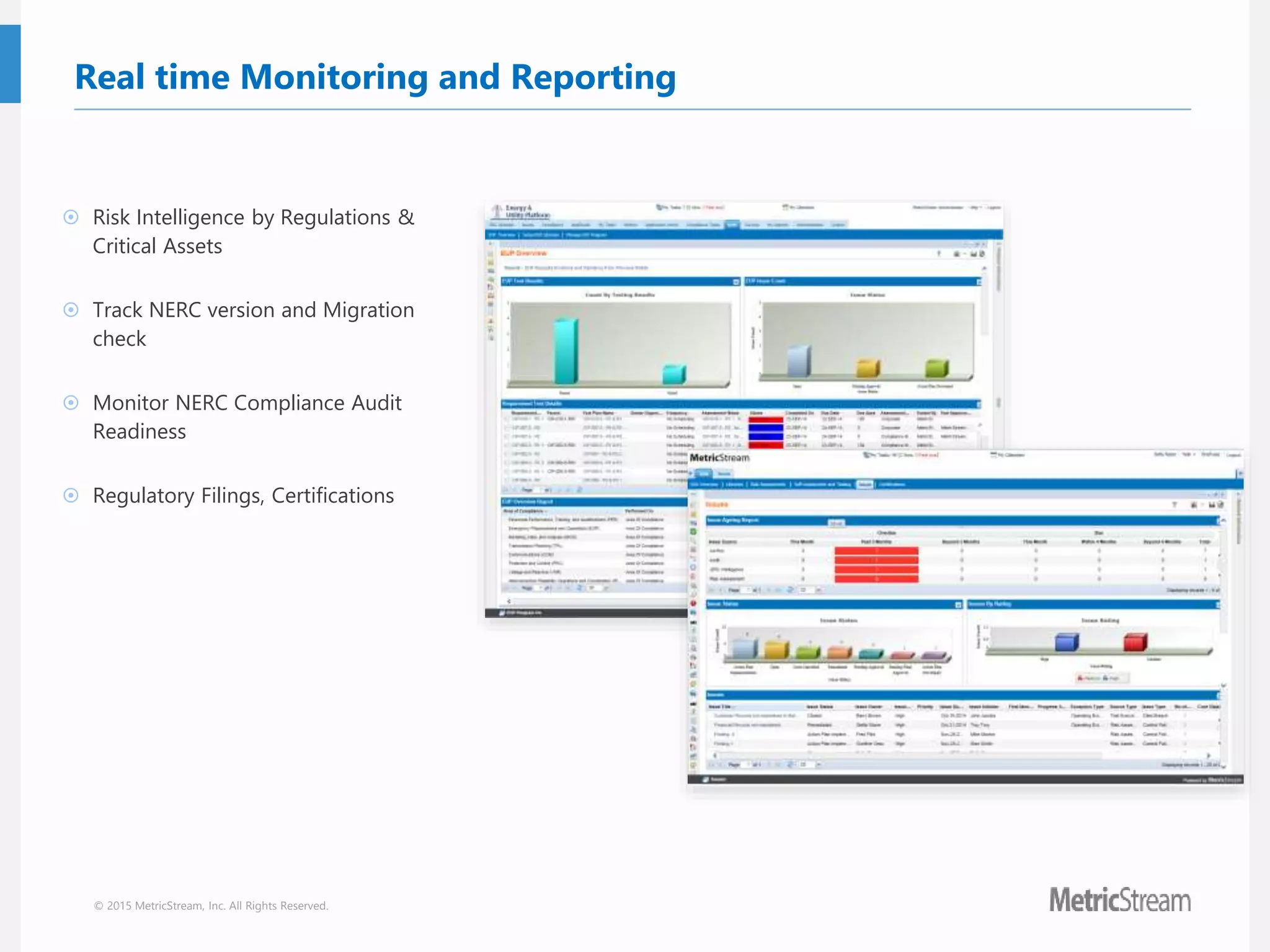
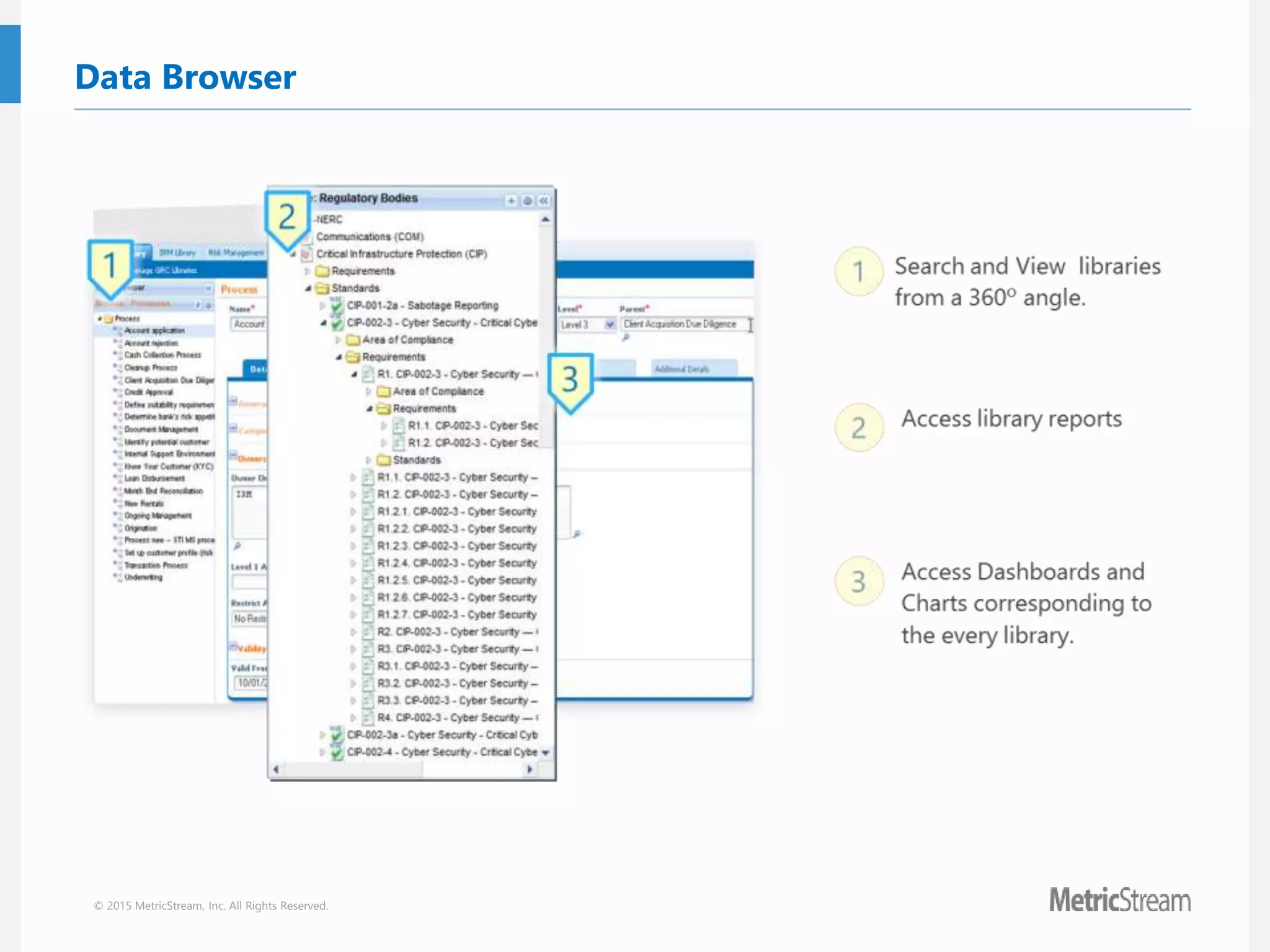
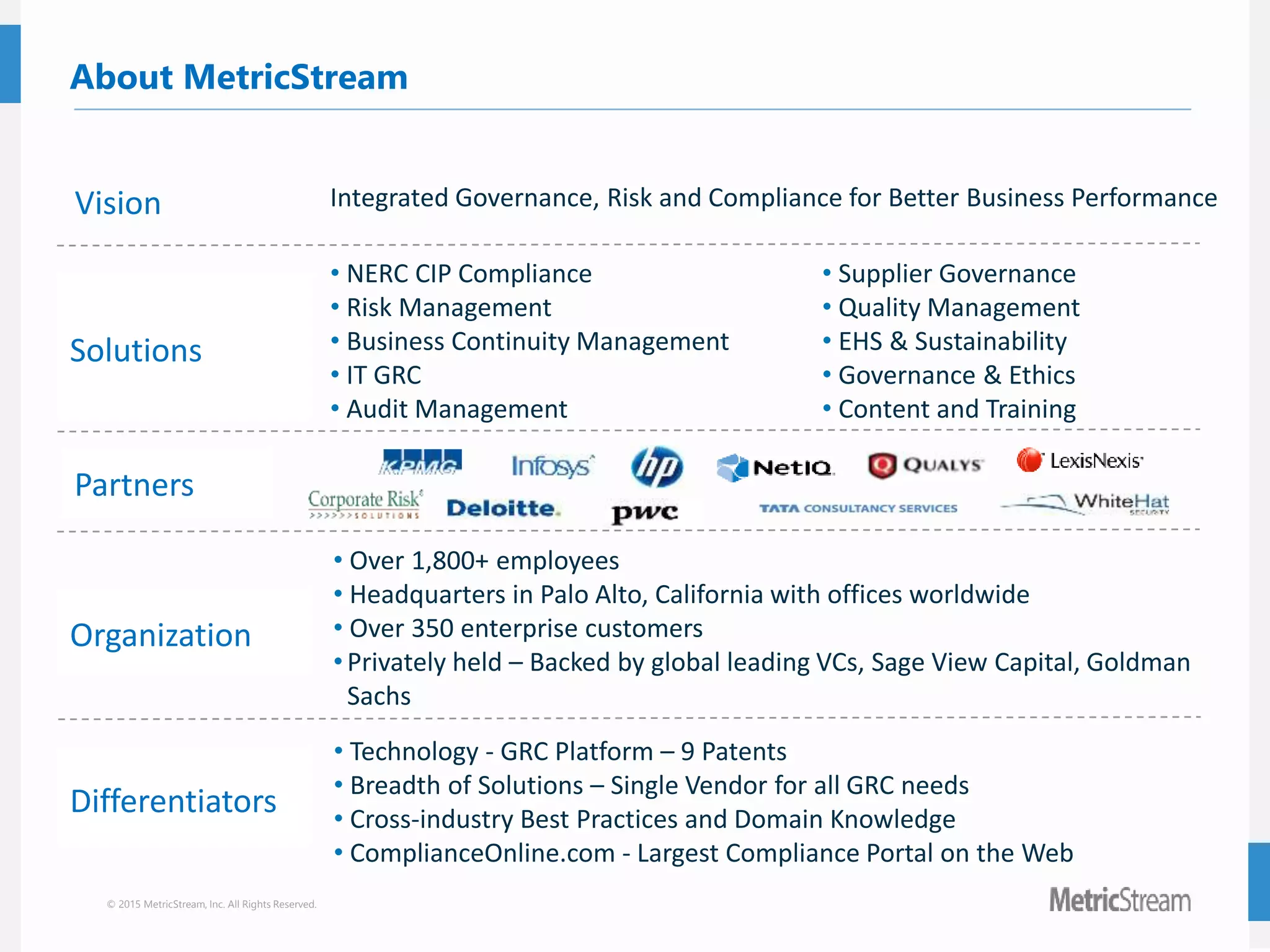
The document discusses the implicit requirements of the NERC CIP RSAs and outlines the RSaw template and its key components, including identifying information, compliance narratives, and auditor questions. It emphasizes the need for documenting processes related to cyber asset management, including the classification of assets, shared compliance responsibilities, and maintaining compliance with policies. The presentation also details the benefits of leveraging technology for RSaw management and MetricStream's NERC CIP compliance solutions.