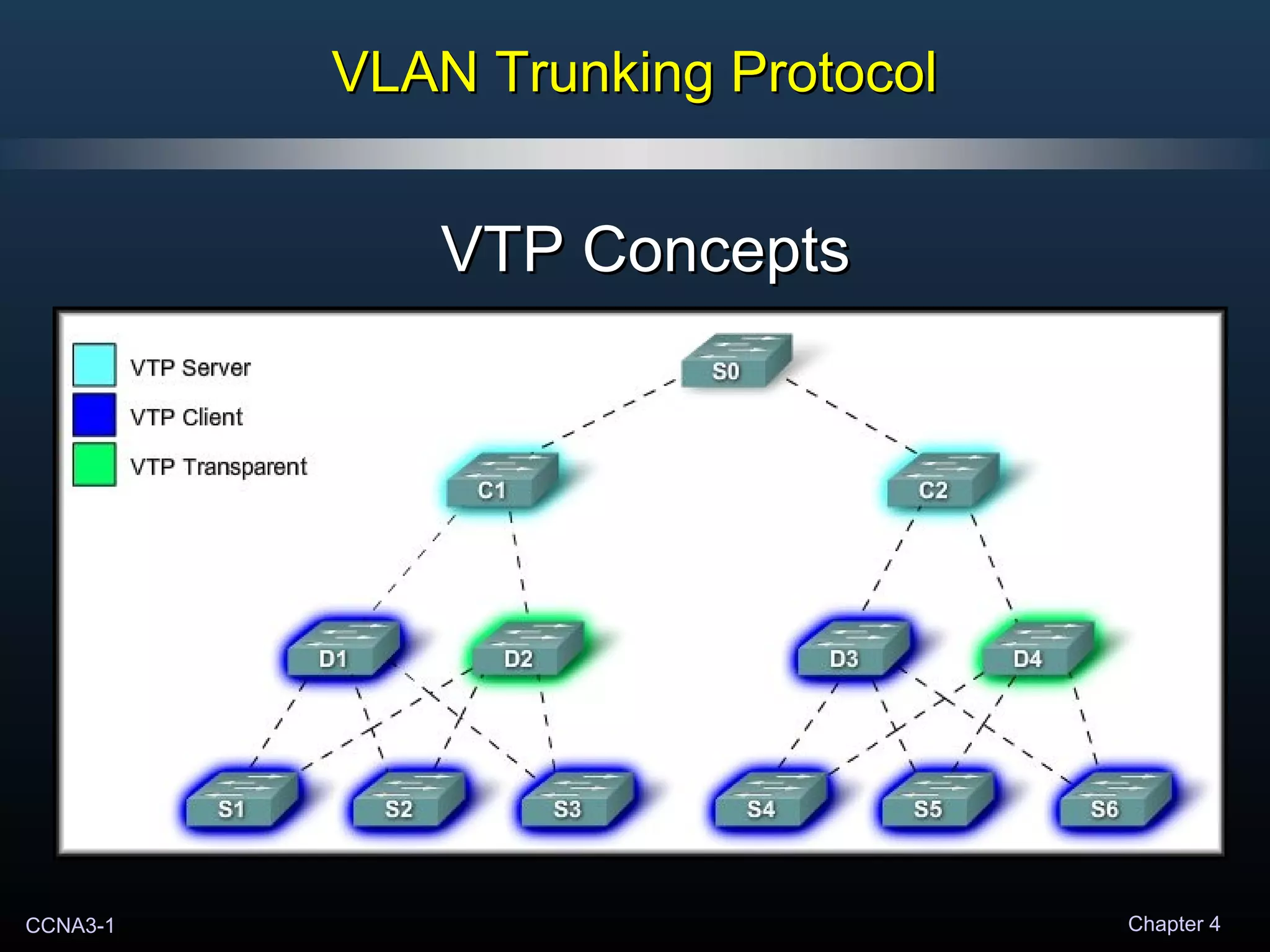
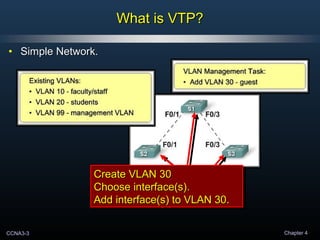
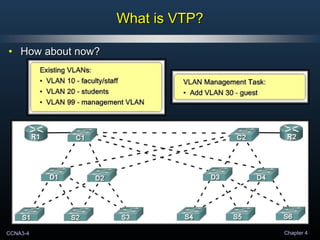
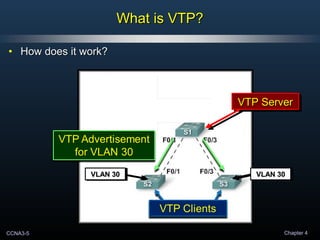
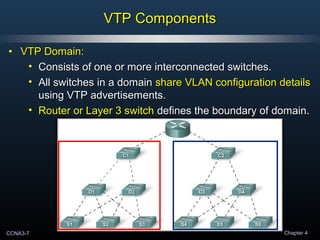
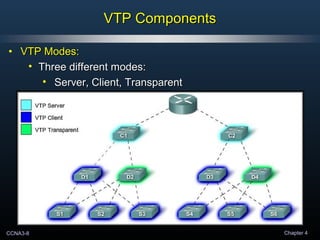
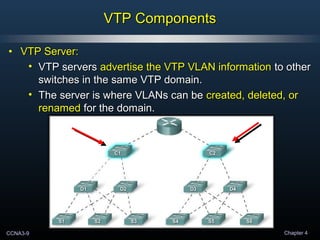
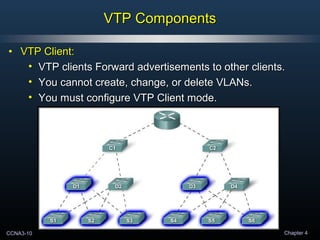
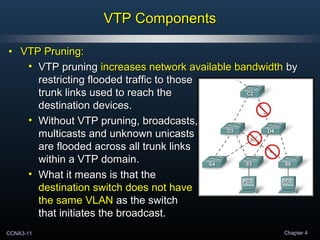
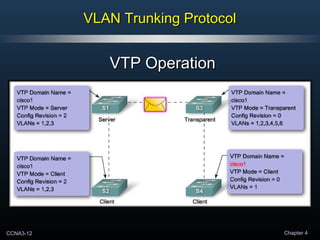
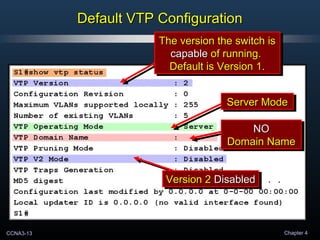
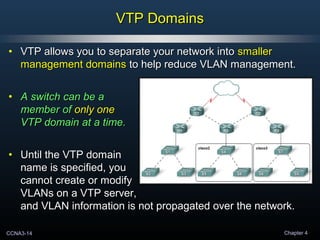
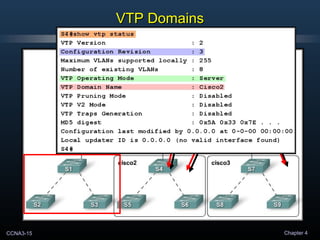
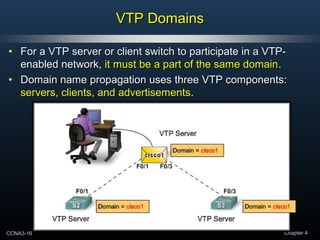
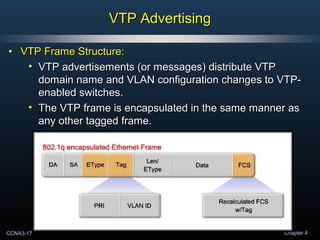
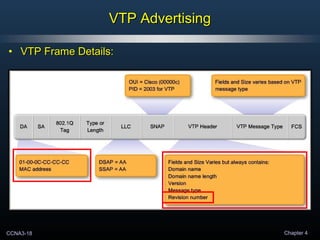
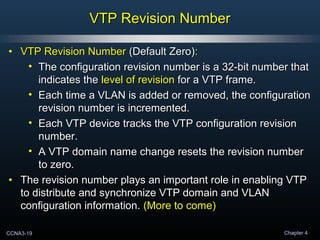
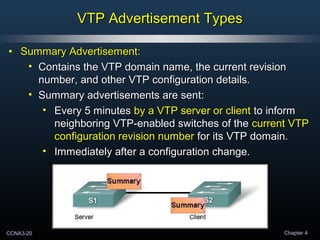
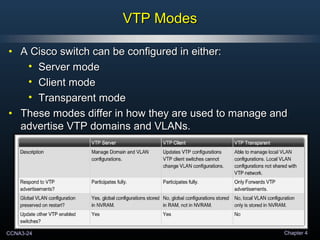
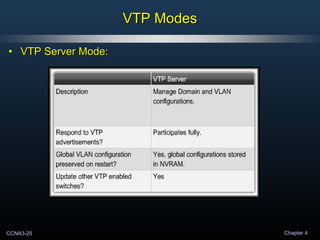
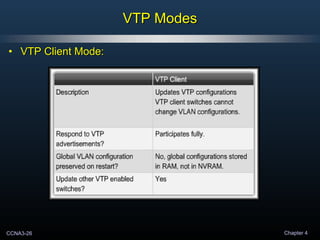
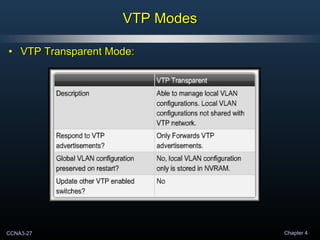
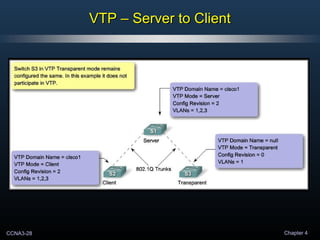
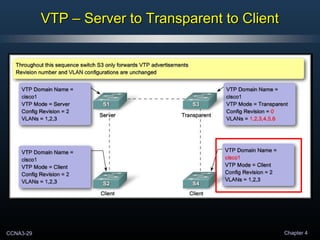
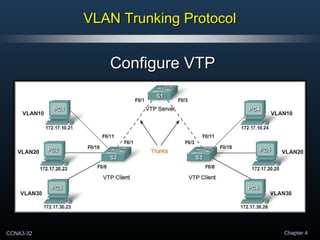
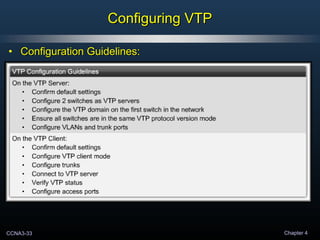
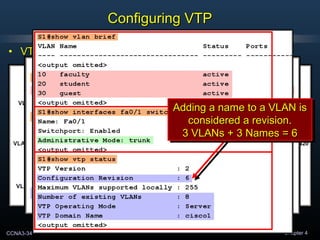
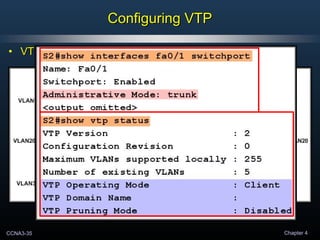
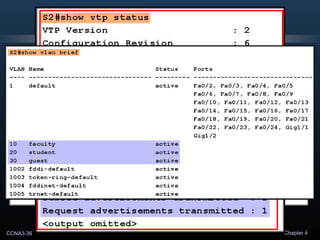
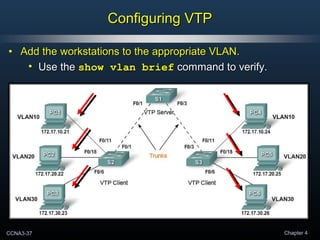
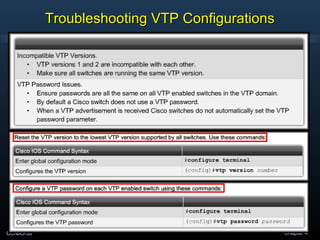
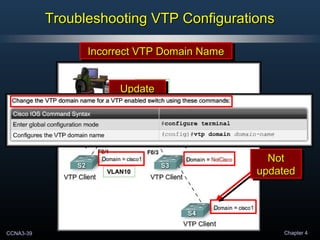
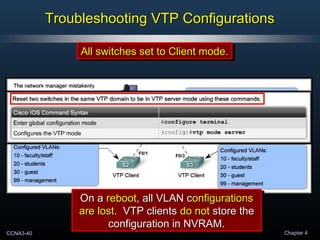
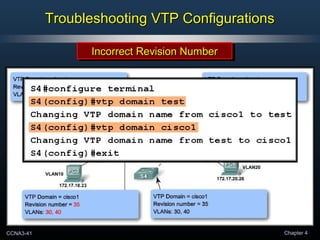
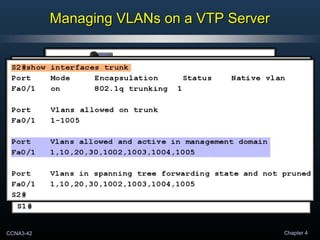
VTP allows VLAN configurations to be synchronized across multiple switches, simplifying network management. It operates by electing a switch as the VTP server, where VLANs can be created and modified. This information is then propagated through VTP advertisements to other switches operating as clients or in transparent mode. Troubleshooting may involve checking the VTP domain name, revision number, and that at least one switch is operating as a server.