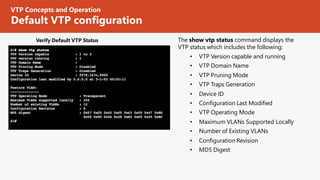
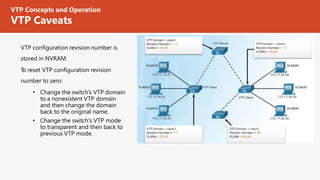
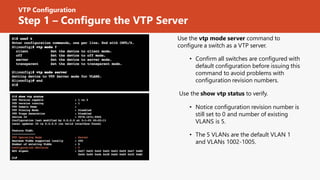
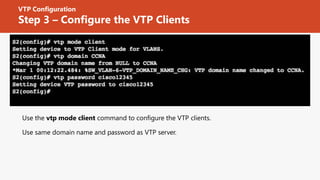
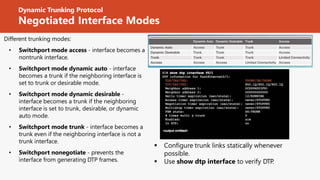
The document discusses strategies for scaling VLANs and troubleshooting inter-VLAN routing, including configuring VTP, DTP, extended VLANs, and Layer 3 switching. It provides instructions for configuring VTP servers and clients, creating and assigning VLANs, configuring trunks, and addresses common issues like misconfigured switch ports, IP addresses, and VTP/DTP settings. The objectives are to configure inter-switch connectivity technologies, troubleshoot inter-VLAN routing environments, and understand concepts like VTP advertisements, modes, and versions.