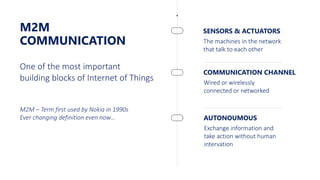
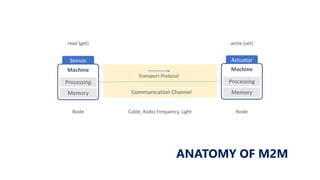
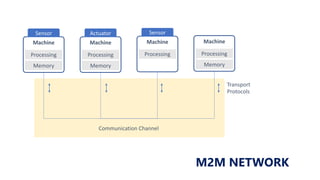
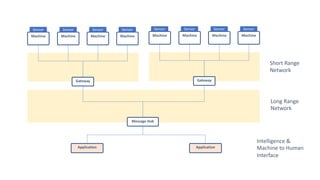
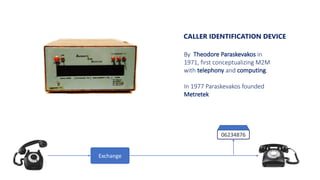
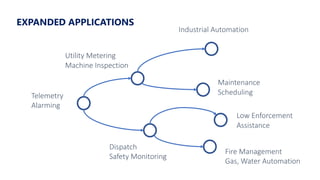
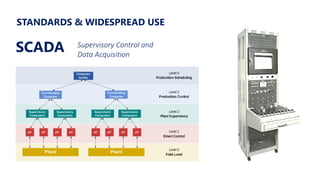
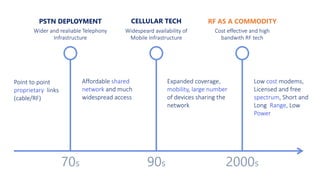
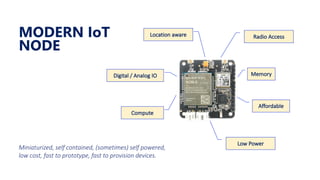
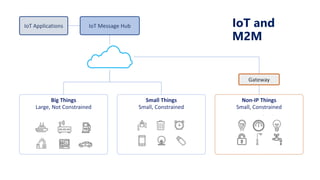
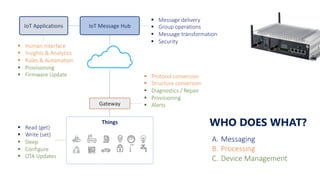
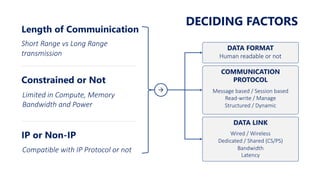
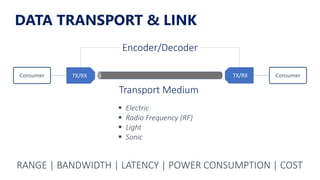
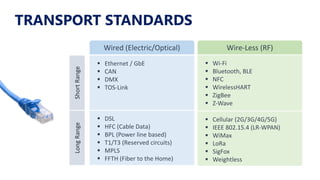
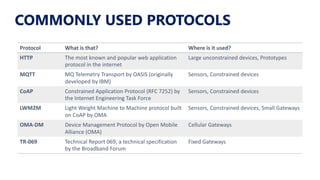
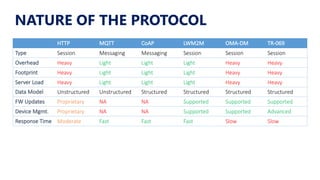
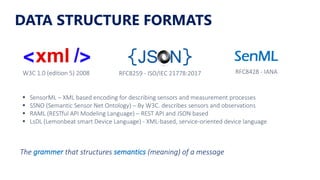
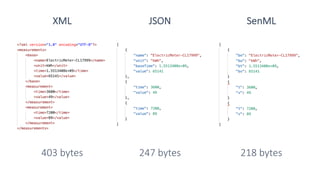
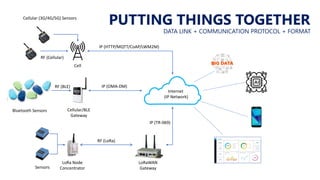
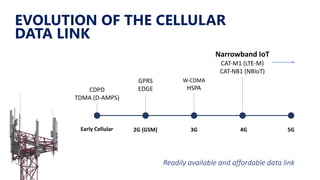
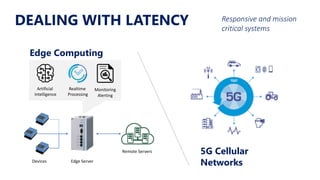
The document provides an overview of the evolution of machine-to-machine (M2M) communication, detailing its history, applications, and developments in the context of the Internet of Things (IoT). It discusses the technical components of M2M communication, including protocols and transport standards, as well as the relationship between M2M and IoT, highlighting recent advancements and opportunities in the field. The presentation emphasizes the ongoing transformation and expanded use of M2M technologies across various industries.