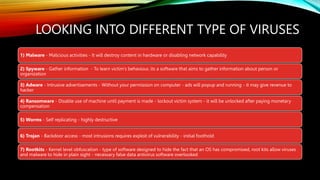
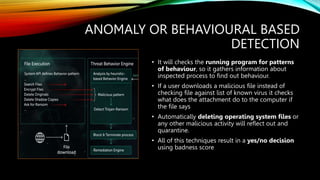
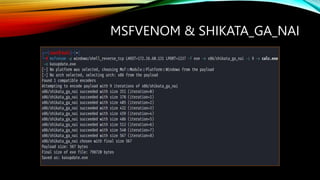
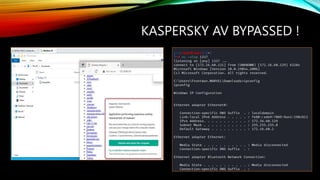
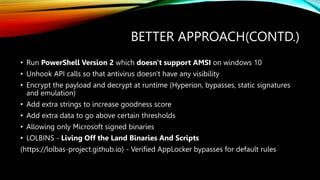
The document outlines various types of malware, including viruses, spyware, adware, ransomware, worms, trojans, and rootkits. It discusses common antivirus detection mechanisms such as signature-based and anomaly-based detection, as well as how the Antimalware Scan Interface (AMSI) functions. Additionally, it provides techniques for bypassing popular antivirus software and suggests alternative approaches for malicious activities.