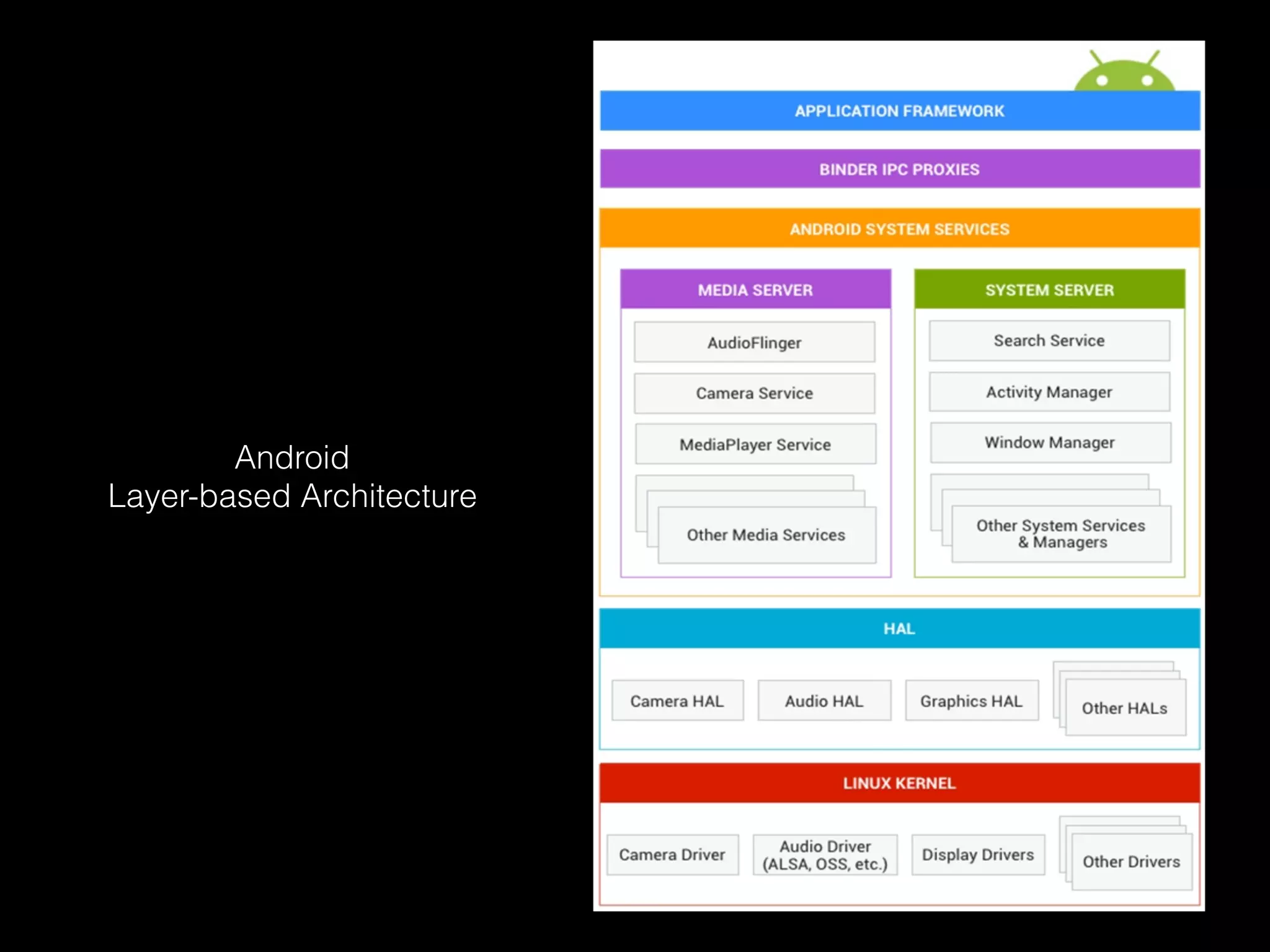
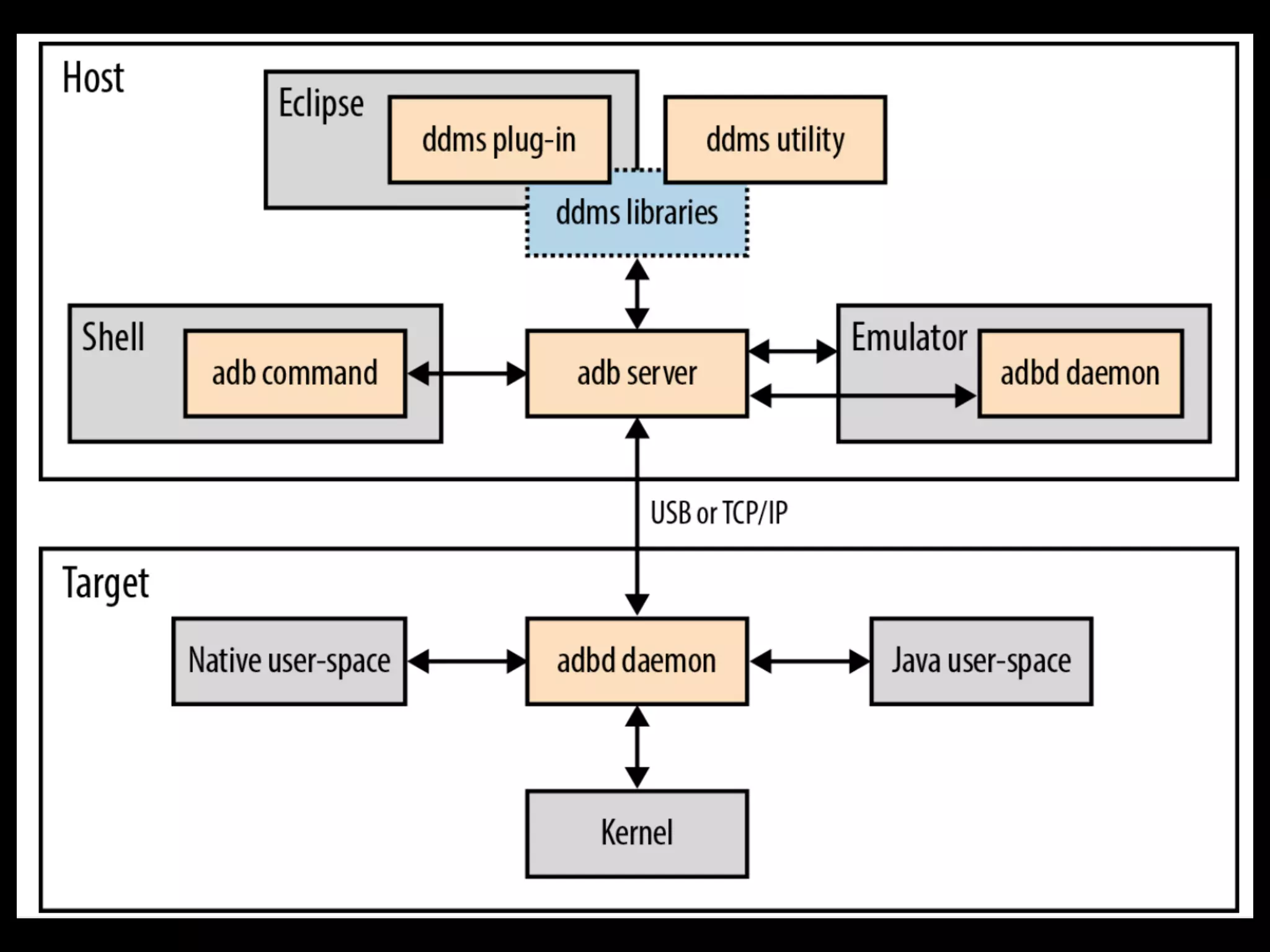
This document provides an overview of the Android embedded operating system, including its hardware, software ecosystem, and key characteristics and components. It discusses the Android Open Source Project, the layered architecture including the kernel, HAL, system services, and apps. It also covers the build system, filesystem structure, debugging and development tools like ADB and logcat.





![Logging
log [-p <prioritychar>] [-t <tag>] <message>
prioritychar should be one of:
v,d,i,w,e
log -p i -t ACME Initiating bird tracking sequence
# logcat
...
I/ACME ( 336): Initiating bird tracking sequence
shell scripts中使⽤用](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-56-2048.jpg)
![ioctl
read()/write()
# cat /dev/birdlocator0
# echo "Fire" > /dev/birdlaser0
ioctl [-l <length>] [-a <argsize>] [-rdh] <device> <ioctlnr>
-l <length> Length of io buffer
-a <argsize> Size of each argument (1-8)
-r Open device in read only mode
-d Direct argument (no iobuffer)
-h Print help](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-57-2048.jpg)

![logwrapper
Usage: logwrapper [-a] [-d] [-k] BINARY [ARGS ...]
Forks and executes BINARY ARGS, redirecting stdout and stderr to
the Android logging system. Tag is set to BINARY, priority is
always LOG_INFO.
-a: Causes logwrapper to do abbreviated logging.
This logs up to the first 4K and last 4K of the command
being run, and logs the output when the command exits
-d: Causes logwrapper to SIGSEGV when BINARY terminates
fault address is set to the status of wait()
-k: Causes logwrapper to log to the kernel log instead of
the Android system log](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-59-2048.jpg)
![run-as
run-as: Usage:
run-as <package-name> [--user <uid>] <command> [<args>]](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-60-2048.jpg)
![service
Usage: service [-h|-?]
service list
service check SERVICE
service call SERVICE CODE [i32 N | i64 N | f N | d N | s16 STR ] ...
Options:
i32: Write the 32-bit integer N into the send parcel.
i64: Write the 64-bit integer N into the send parcel.
f: Write the 32-bit single-precision number N into the send parcel.
d: Write the 64-bit double-precision number N into the send parcel.
s16: Write the UTF-16 string STR into the send parcel.](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-61-2048.jpg)
![dumpsys
usage: dumpsys
To dump all services.
or:
dumpsys [-t TIMEOUT] [--help | -l | --skip SERVICES | SERVICE [ARGS]]
--help: shows this help
-l: only list services, do not dump them
-t TIMEOUT: TIMEOUT to use in seconds instead of default 10 seconds
--skip SERVICES: dumps all services but SERVICES (comma-separated list)
SERVICE [ARGS]: dumps only service SERVICE, optionally passing ARGS to it
现场查看状态(Android服务)](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-62-2048.jpg)
![dumpstate 事后分析-系统快照
usage: dumpstate [-h] [-b soundfile] [-e soundfile] [-o file [-d] [-p] [-z]] [-s] [-S] [-q] [-B] [-P] [-R] [-V version]
-h: display this help message
-b: play sound file instead of vibrate, at beginning of job
-e: play sound file instead of vibrate, at end of job
-o: write to file (instead of stdout)
-d: append date to filename (requires -o)
-p: capture screenshot to filename.png (requires -o)
-z: generate zipped file (requires -o)
-s: write output to control socket (for init)
-S: write file location to control socket (for init; requires -o and -z) -q: disable vibrate
-B: send broadcast when finished (requires -o)
-P: send broadcast when started and update system properties on progress (requires -o and -B)
-R: take bugreport in remote mode (requires -o, -z, -d and -B, shouldn't be used with -P)
-V: sets the bugreport format version (valid values: 1.0)](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-63-2048.jpg)
![rawbu
Usage: rawbu COMMAND [options] [backup-file-path]
commands are:
help Show this help text.
backup Perform a backup of /data.
restore Perform a restore of /data.
options include:
-h Show this help text.
-a Backup all files.
backup-file-path Defaults to /sdcard/backup.dat .
On devices that emulate the sdcard, you will need to
explicitly specify the directory it is mapped to,
to avoid recursive backup or deletion of the backup file
during restore.
Eg. /data/media/0/backup.dat
The rawbu command allows you to perform low-level
backup and restore of the /data partition. This is
where all user data is kept, allowing for a fairly
complete restore of a device's state. Note that
because this is low-level, it will only work across
builds of the same (or very similar) device software.
⽤用户数据备份、还原 ⽅方便便测试,bug复现](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-64-2048.jpg)
![am
usage: am [subcommand] [options]
usage: am start [-D] [-N] [-W] [-P <FILE>] [--start-profiler <FILE>]
[--sampling INTERVAL] [-R COUNT] [-S]
[--track-allocation] [--user <USER_ID> | current] <INTENT>
am startservice [--user <USER_ID> | current] <INTENT>
am stopservice [--user <USER_ID> | current] <INTENT>
am force-stop [--user <USER_ID> | all | current] <PACKAGE>
am kill [--user <USER_ID> | all | current] <PACKAGE>
am kill-all
am broadcast [--user <USER_ID> | all | current] <INTENT>
am instrument [-r] [-e <NAME> <VALUE>] [-p <FILE>] [-w]
[--user <USER_ID> | current]
[--no-window-animation] [--abi <ABI>] <COMPONENT>
am profile start [--user <USER_ID> current] [--sampling INTERVAL] <PROCESS> <FILE>
am profile stop [--user <USER_ID> current] [<PROCESS>]
am dumpheap [--user <USER_ID> current] [-n] <PROCESS> <FILE>
am set-debug-app [-w] [--persistent] <PACKAGE>
am clear-debug-app
am set-watch-heap <PROCESS> <MEM-LIMIT>
am clear-watch-heap
am bug-report [--progress]
am monitor [--gdb <port>]
am hang [--allow-restart]
am restart
am idle-maintenance
am screen-compat [on|off] <PACKAGE>
am package-importance <PACKAGE>
am to-uri [INTENT]
am to-intent-uri [INTENT]
am to-app-uri [INTENT]
am switch-user <USER_ID>
am start-user <USER_ID>
am unlock-user <USER_ID> [TOKEN_HEX]
am stop-user [-w] [-f] <USER_ID>
am stack start <DISPLAY_ID> <INTENT>
am stack movetask <TASK_ID> <STACK_ID> [true|false]
am stack resize <STACK_ID> <LEFT,TOP,RIGHT,BOTTOM>
am stack resize-animated <STACK_ID> <LEFT,TOP,RIGHT,BOTTOM>
am stack resize-docked-stack <LEFT,TOP,RIGHT,BOTTOM> [<TASK_LEFT,TASK_TOP,TASK_RIGHT,TASK_BOTTOM>]
am stack size-docked-stack-test: <STEP_SIZE> <l|t|r|b> [DELAY_MS]
am stack move-top-activity-to-pinned-stack: <STACK_ID> <LEFT,TOP,RIGHT,BOTTOM>
am stack positiontask <TASK_ID> <STACK_ID> <POSITION>
am stack list
am stack info <STACK_ID>
am stack remove <STACK_ID>
am task lock <TASK_ID>
am task lock stop
am task resizeable <TASK_ID> [0 (unresizeable) | 1 (crop_windows) | 2 (resizeable) | 3 (resizeable_and_pipable)]
am task resize <TASK_ID> <LEFT,TOP,RIGHT,BOTTOM>
am task drag-task-test <TASK_ID> <STEP_SIZE> [DELAY_MS]
am task size-task-test <TASK_ID> <STEP_SIZE> [DELAY_MS]
am get-config
am suppress-resize-config-changes <true|false>
am set-inactive [--user <USER_ID>] <PACKAGE> true|false
am get-inactive [--user <USER_ID>] <PACKAGE>
am send-trim-memory [--user <USER_ID>] <PROCESS>
[HIDDEN|RUNNING_MODERATE|BACKGROUND|RUNNING_LOW|MODERATE|RUNNING_CRITICAL|COMPLETE]
am get-current-user
Activity Manager](https://image.slidesharecdn.com/android-180713044308/75/Embedded-Android-65-2048.jpg)