Embed presentation
Download as PDF, PPTX
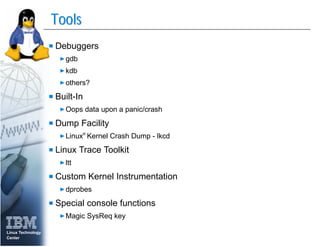

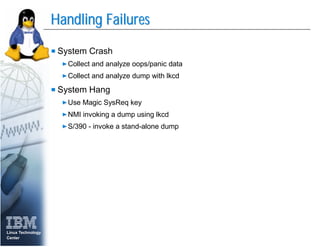
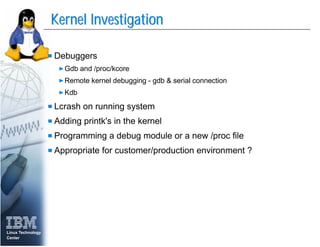
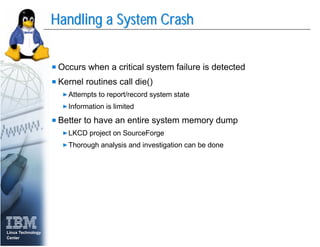
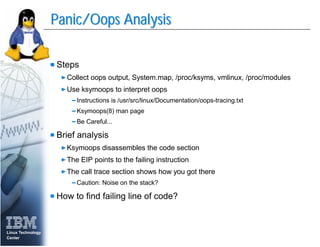
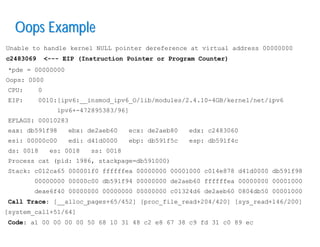
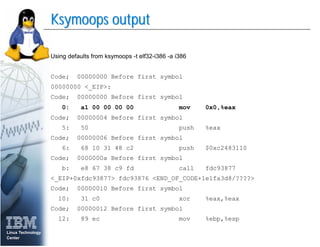
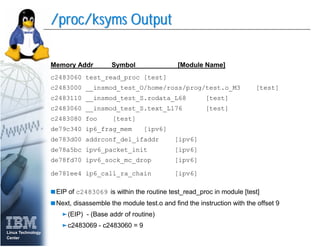
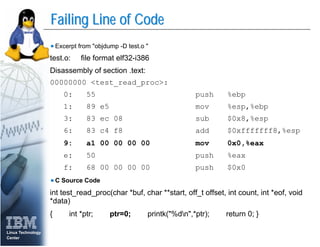
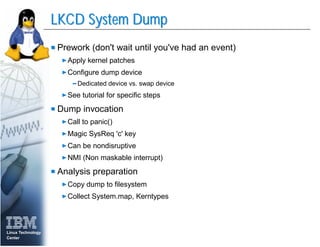
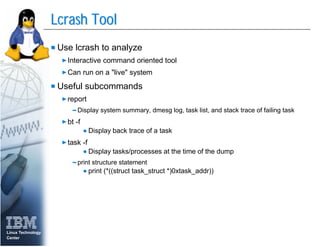
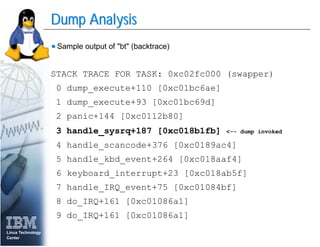

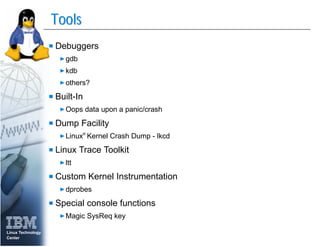
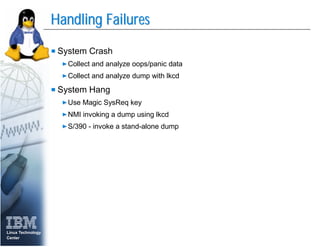
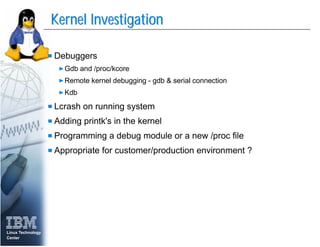
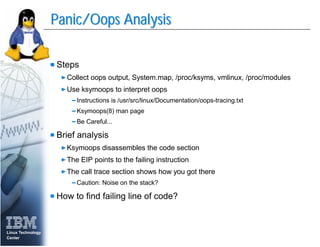
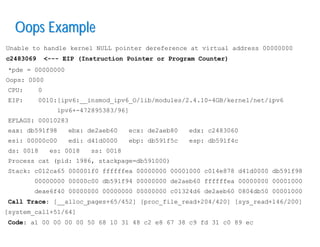
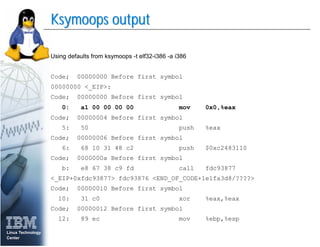
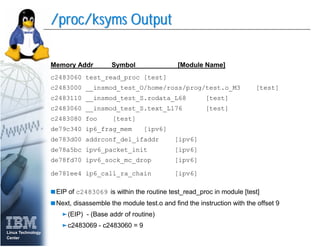
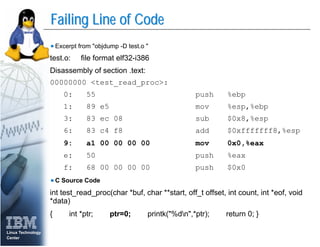
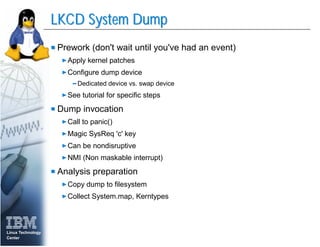
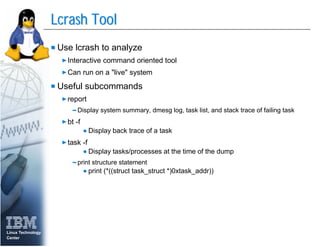
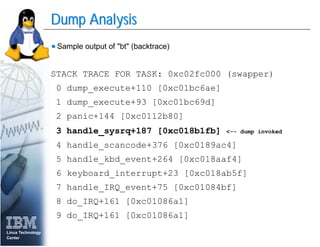
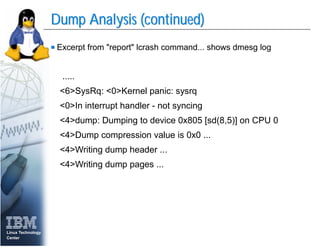
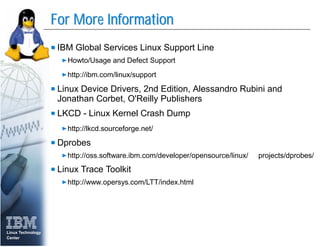
This document discusses tools and techniques for debugging the Linux kernel, including debuggers like gdb, built-in debugging facilities, system logs, and crash dump analysis tools like LKCD. It outlines common issues like kernel crashes and hangs, and provides an example of analyzing an "oops" crash dump to identify the failing line of code through tools like ksymoops. It also covers generating a full system memory dump using LKCD for thorough crash investigation.