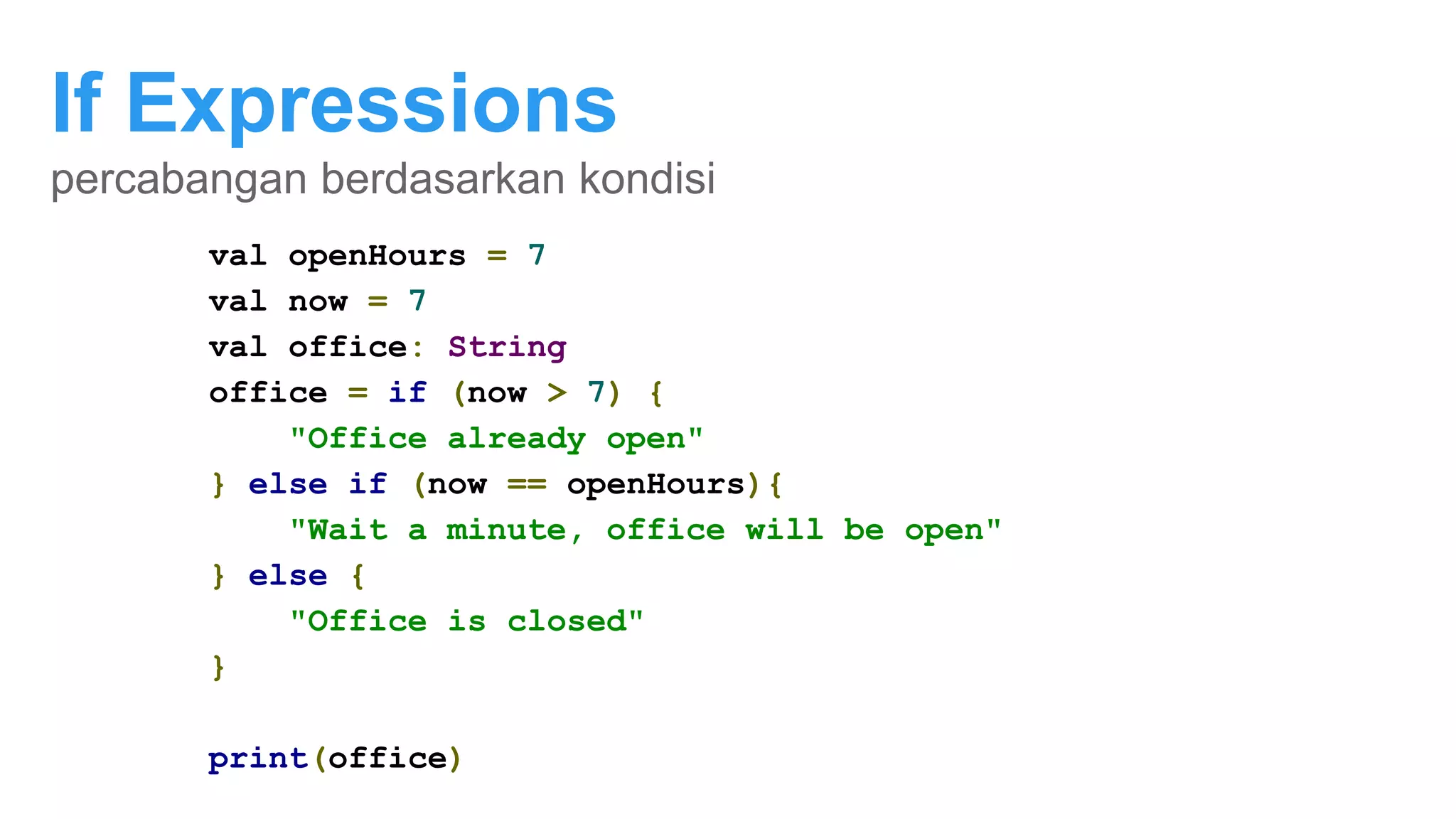
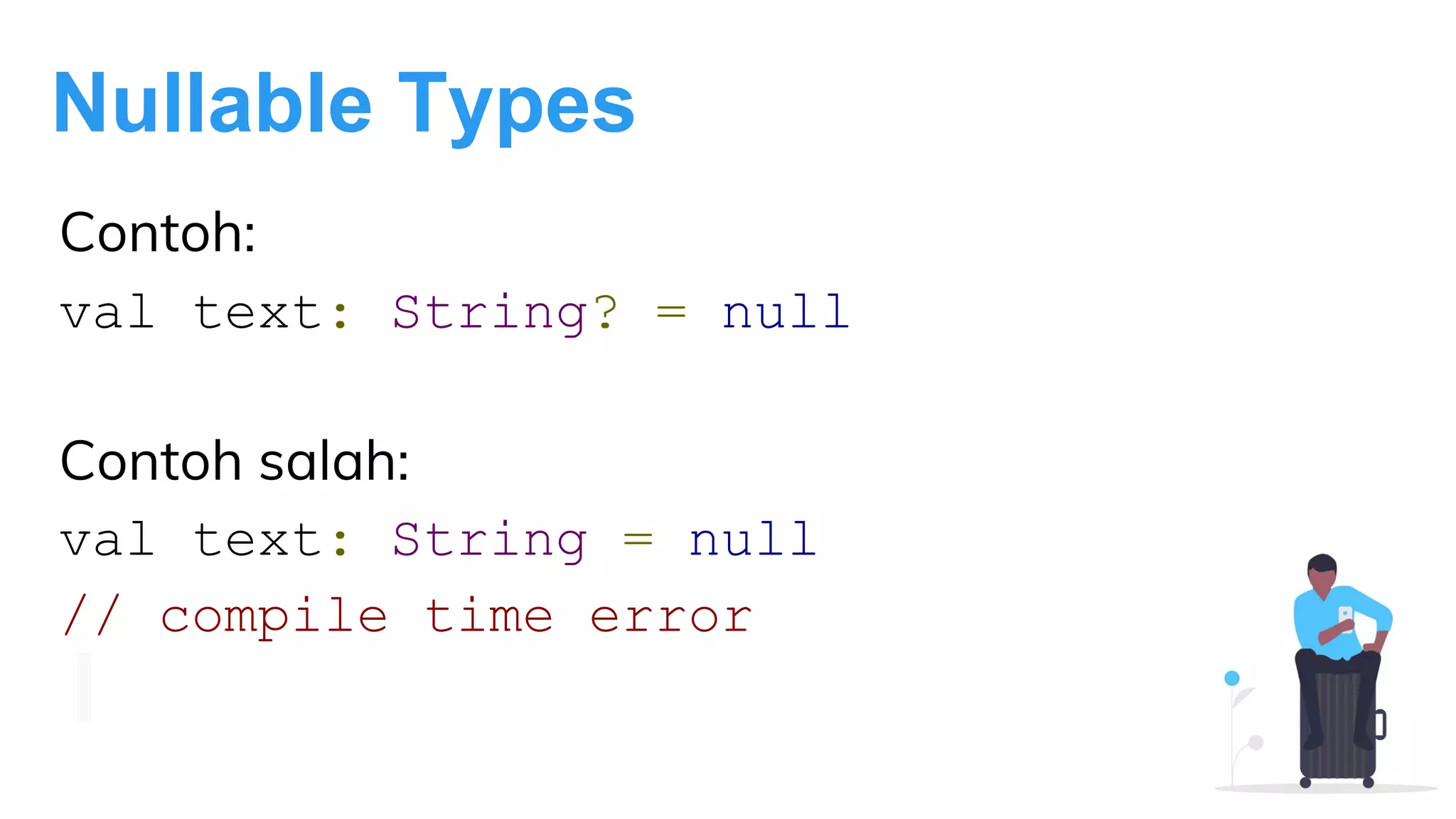
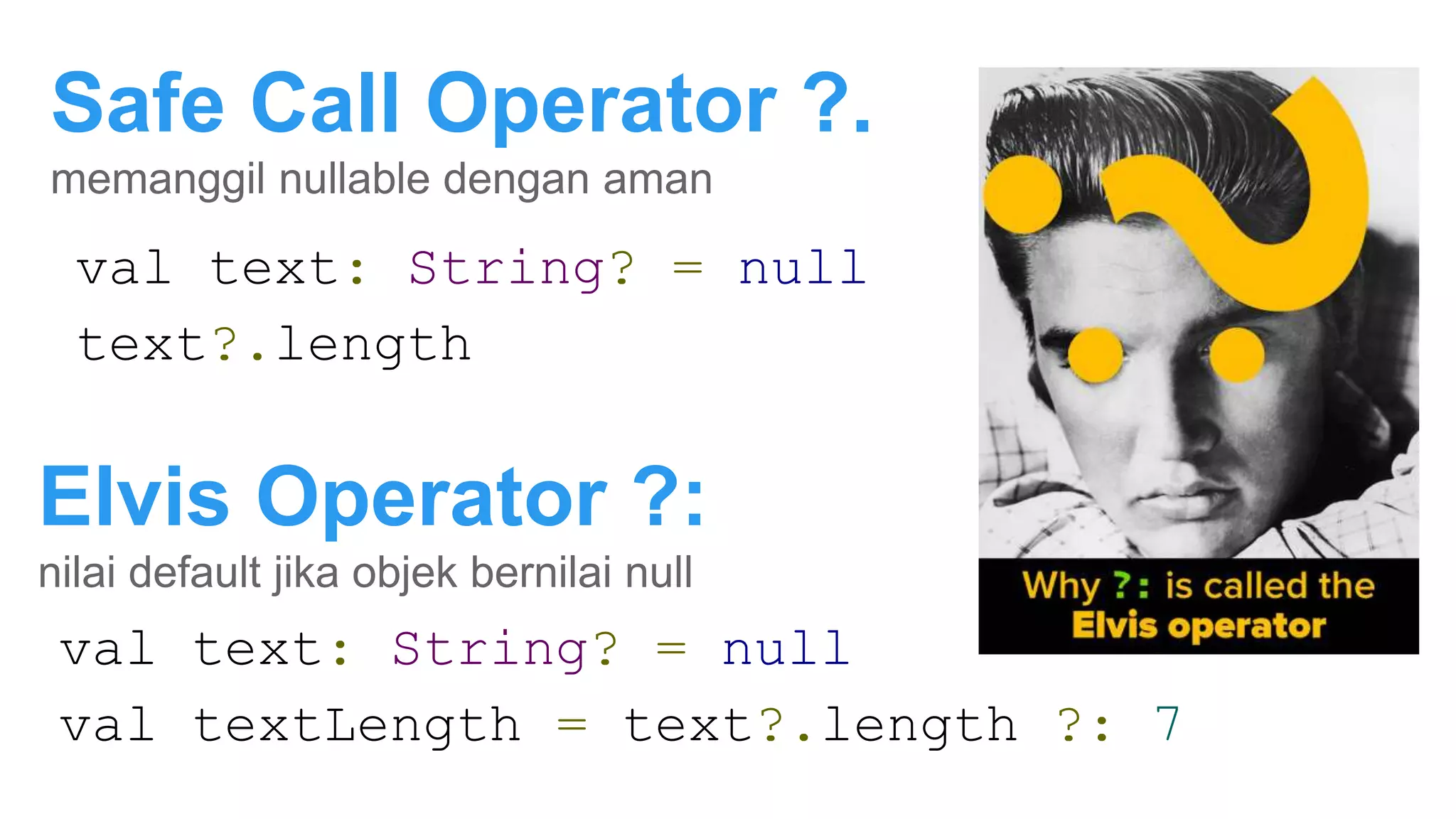
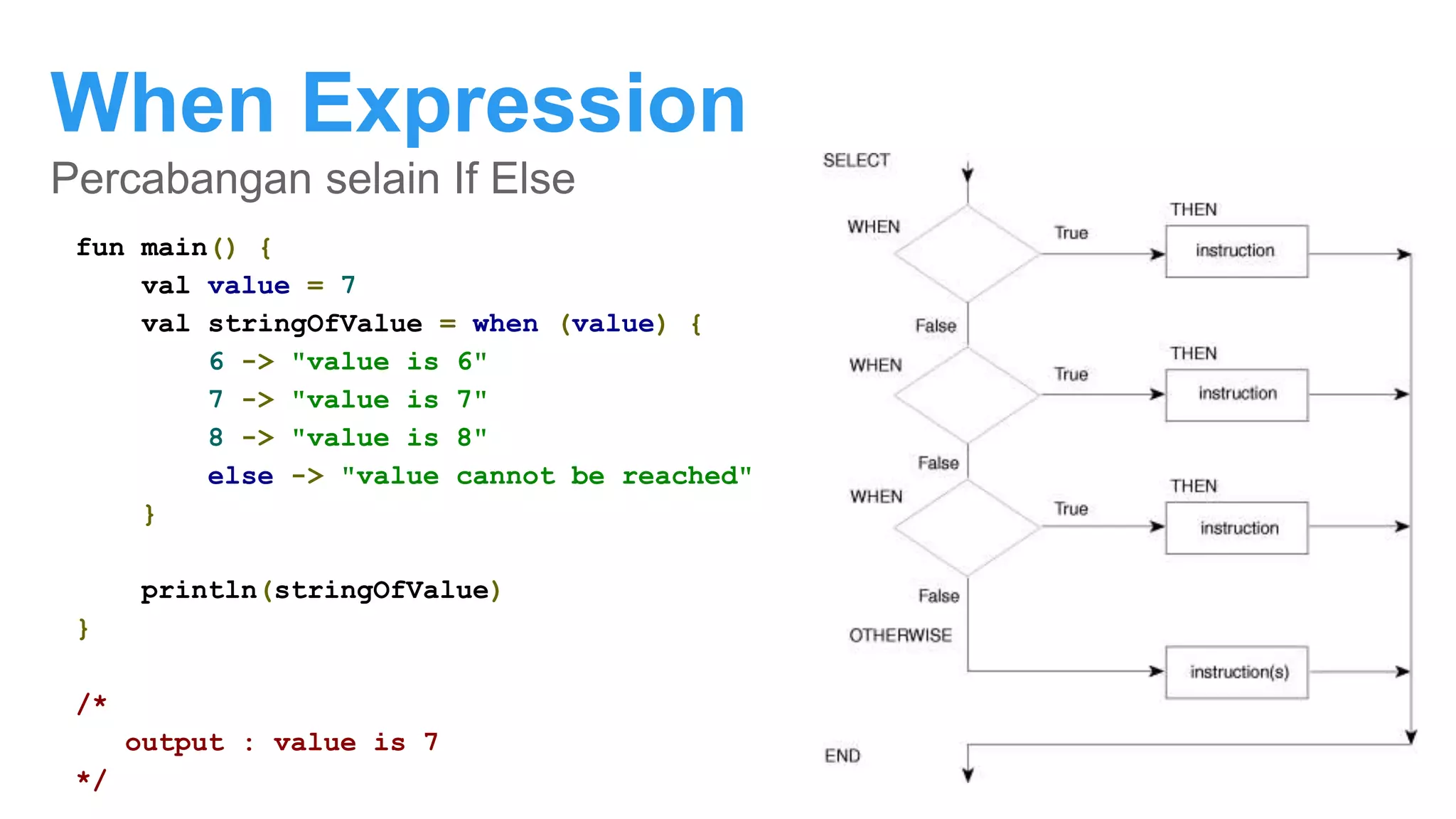
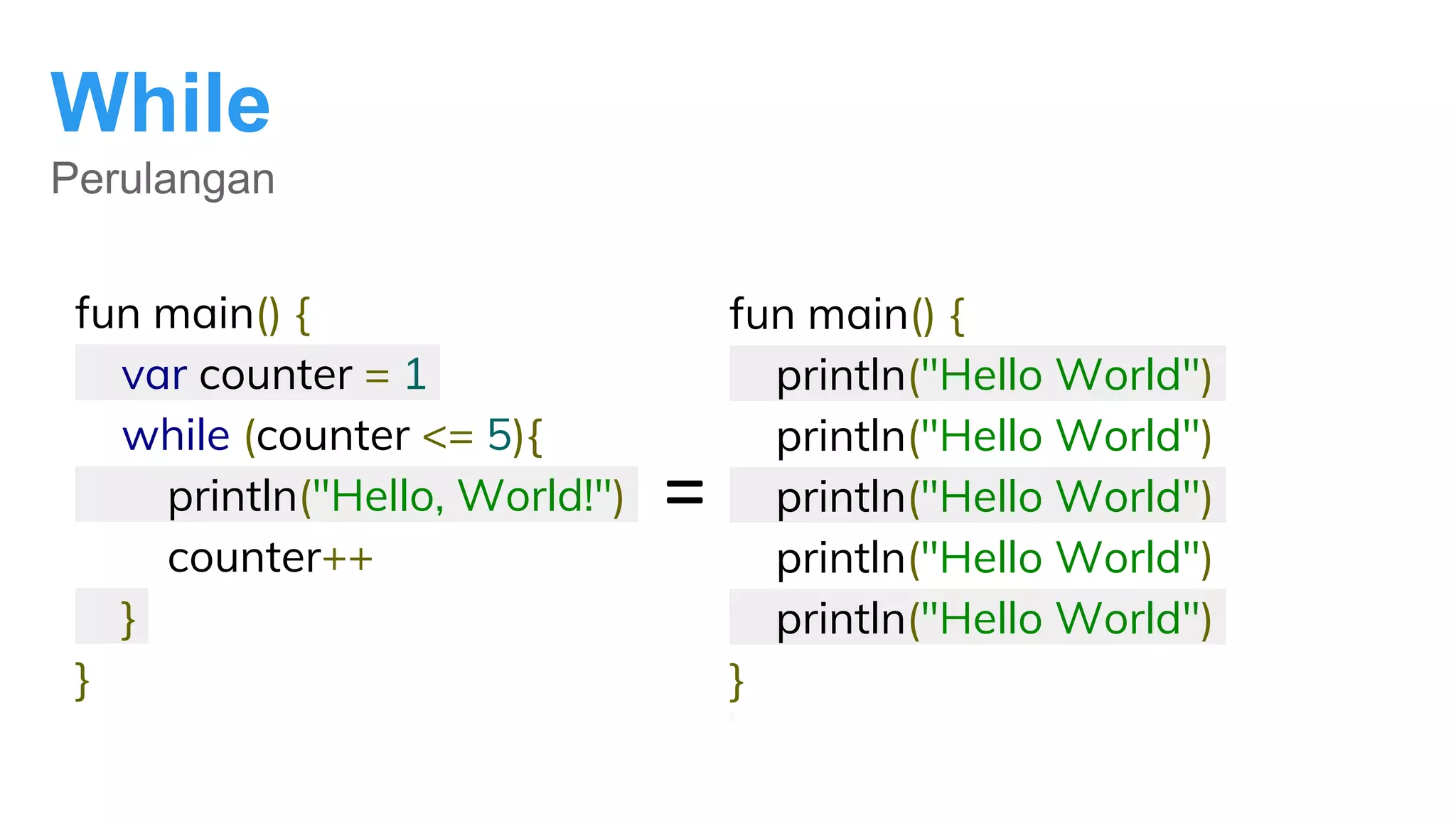
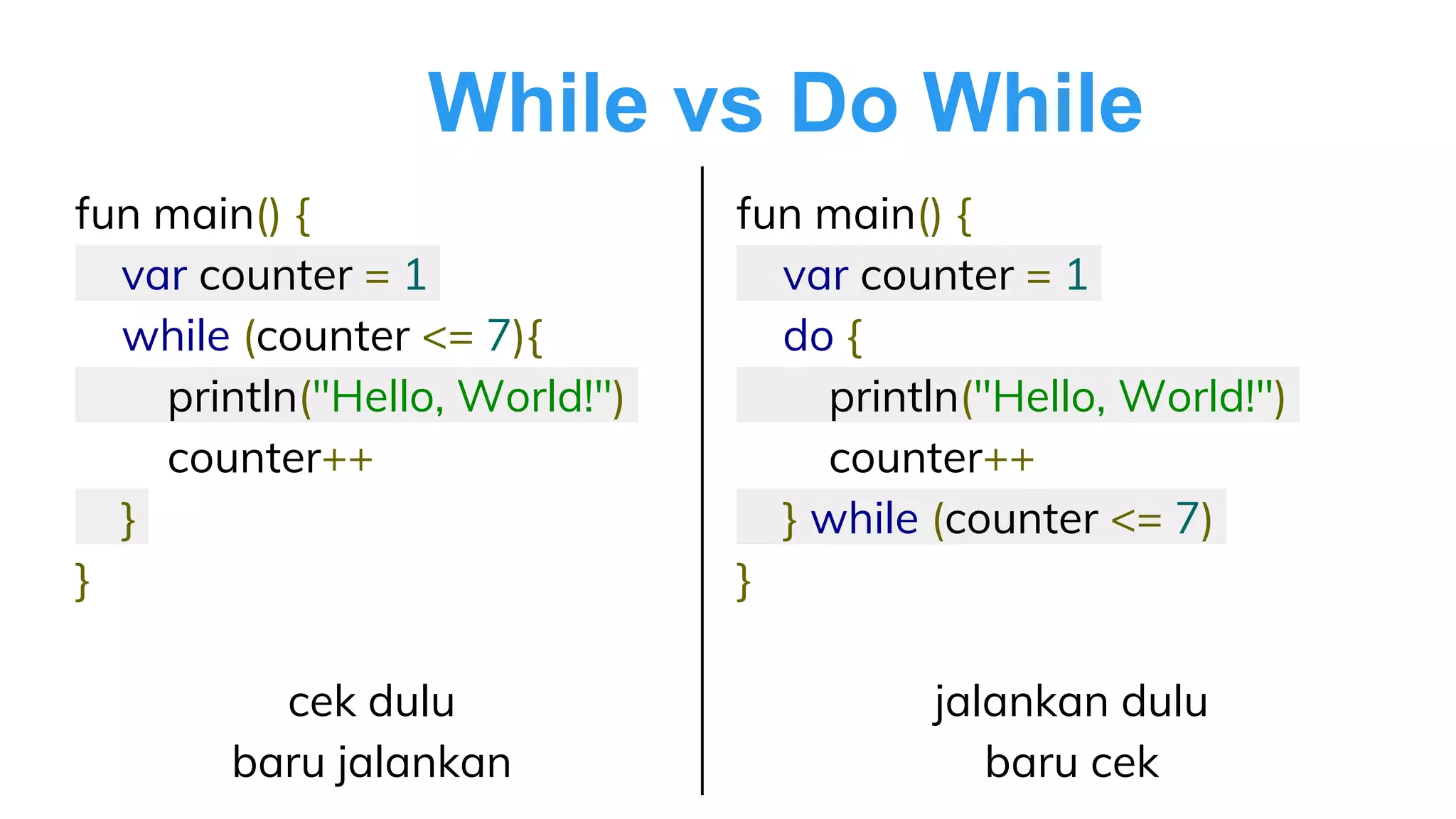
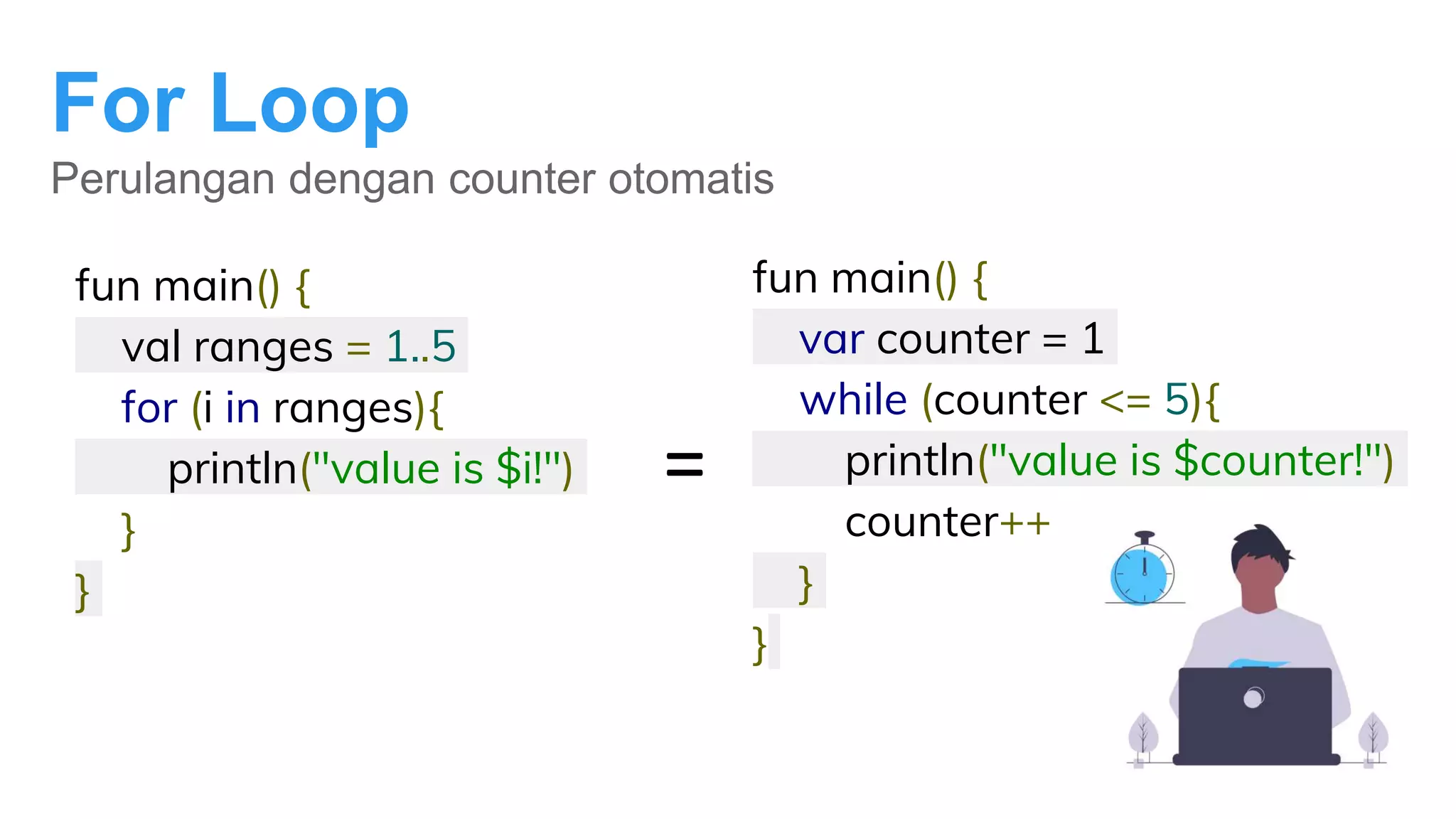
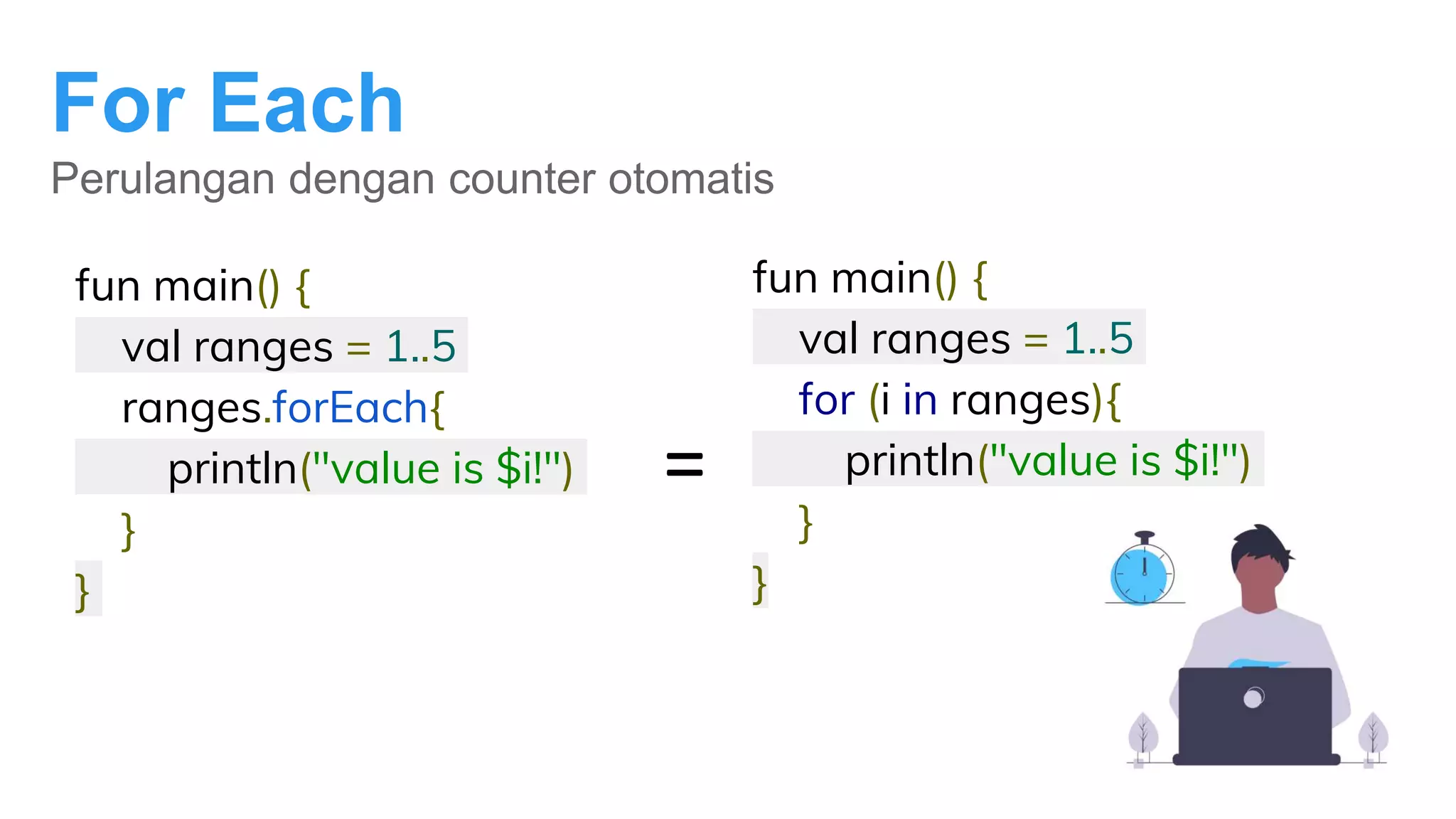
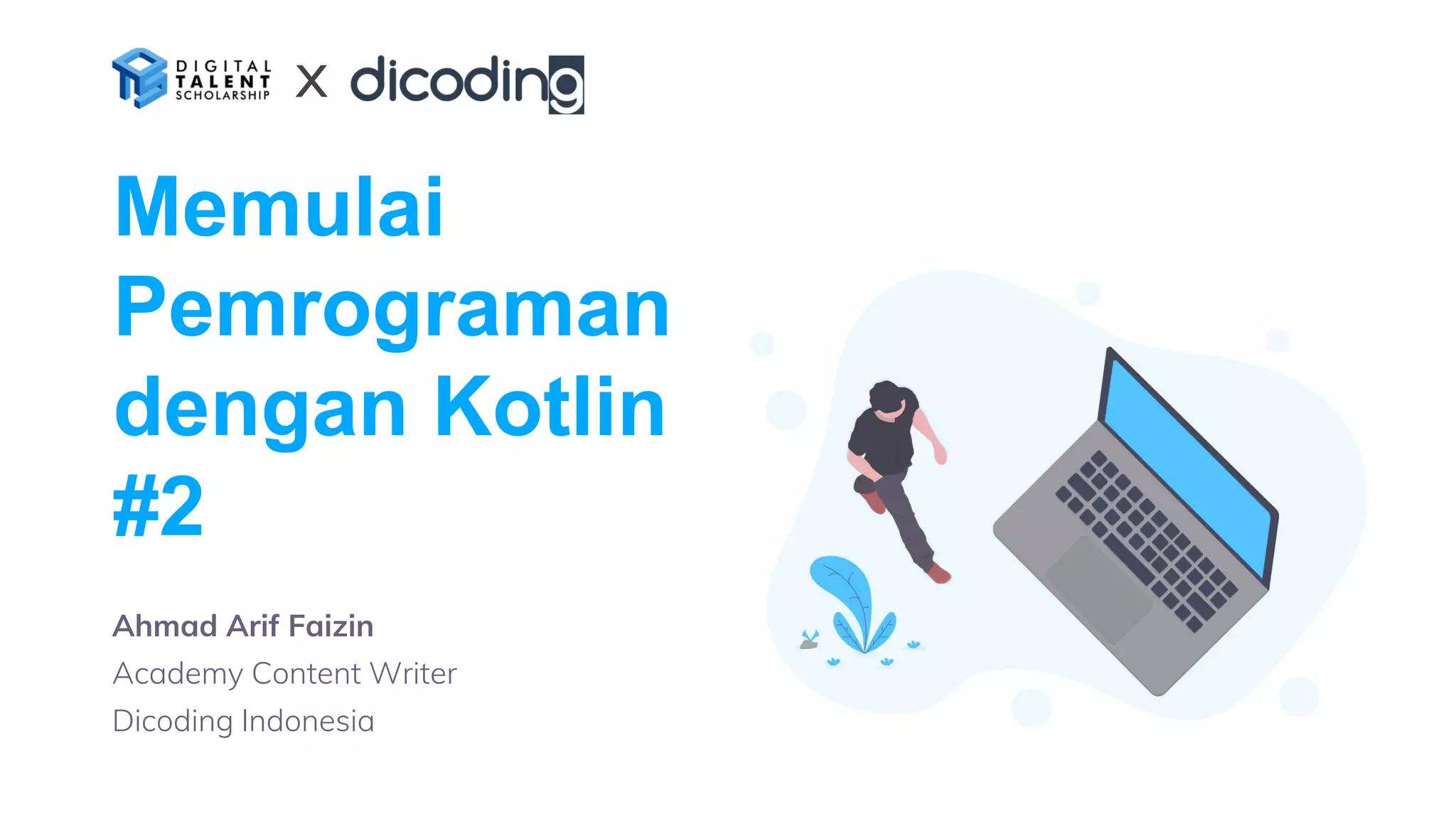
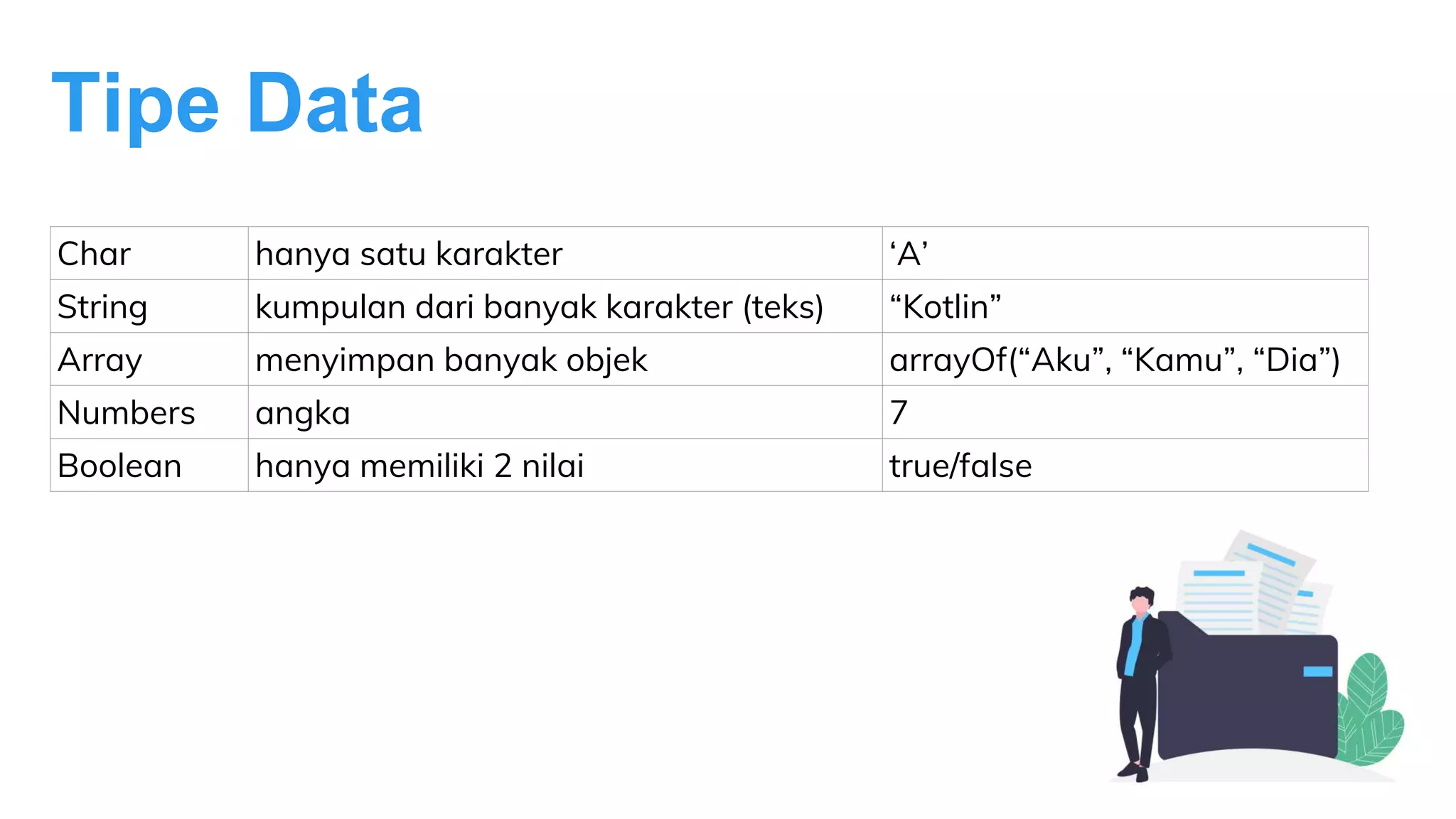
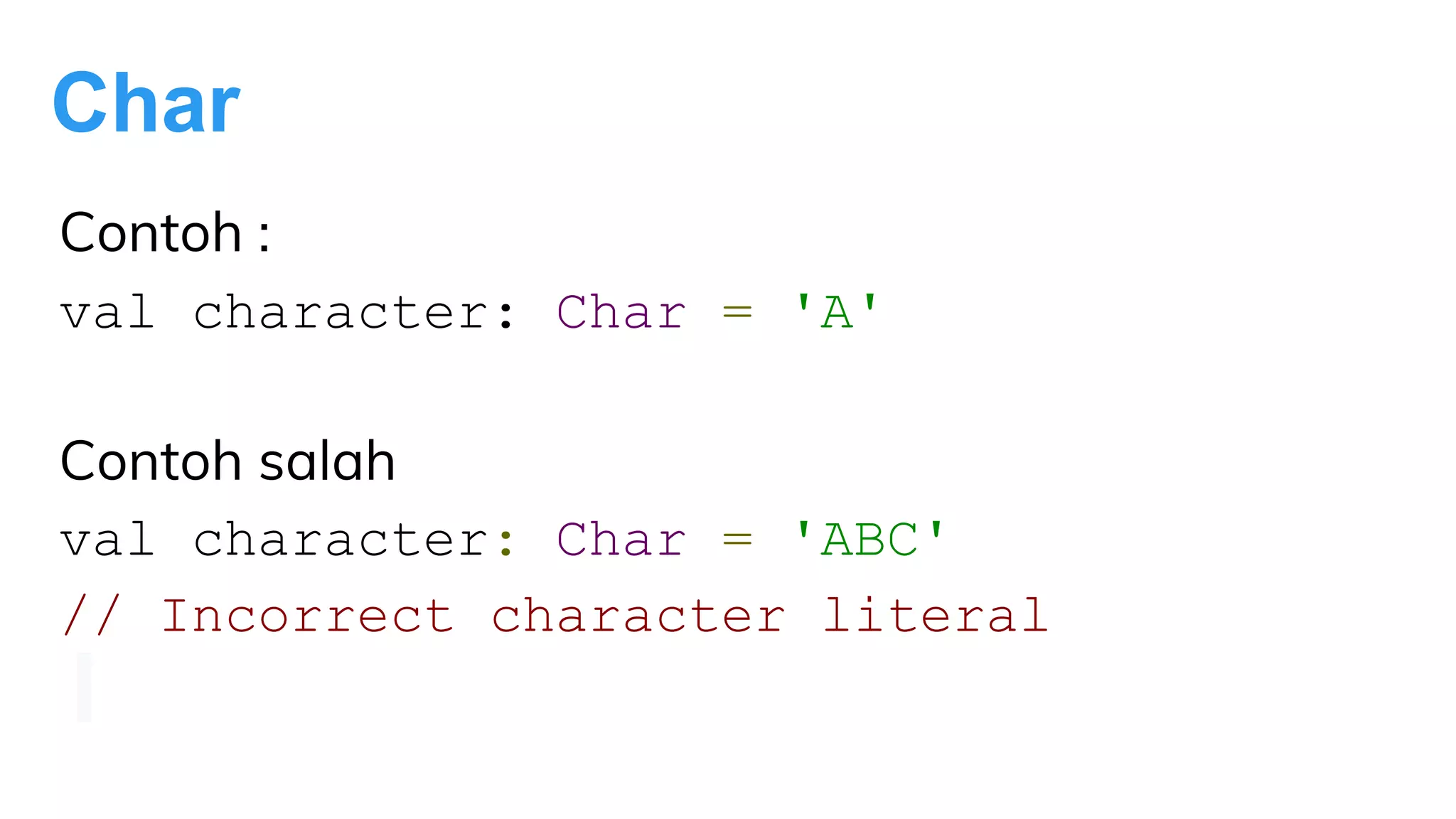
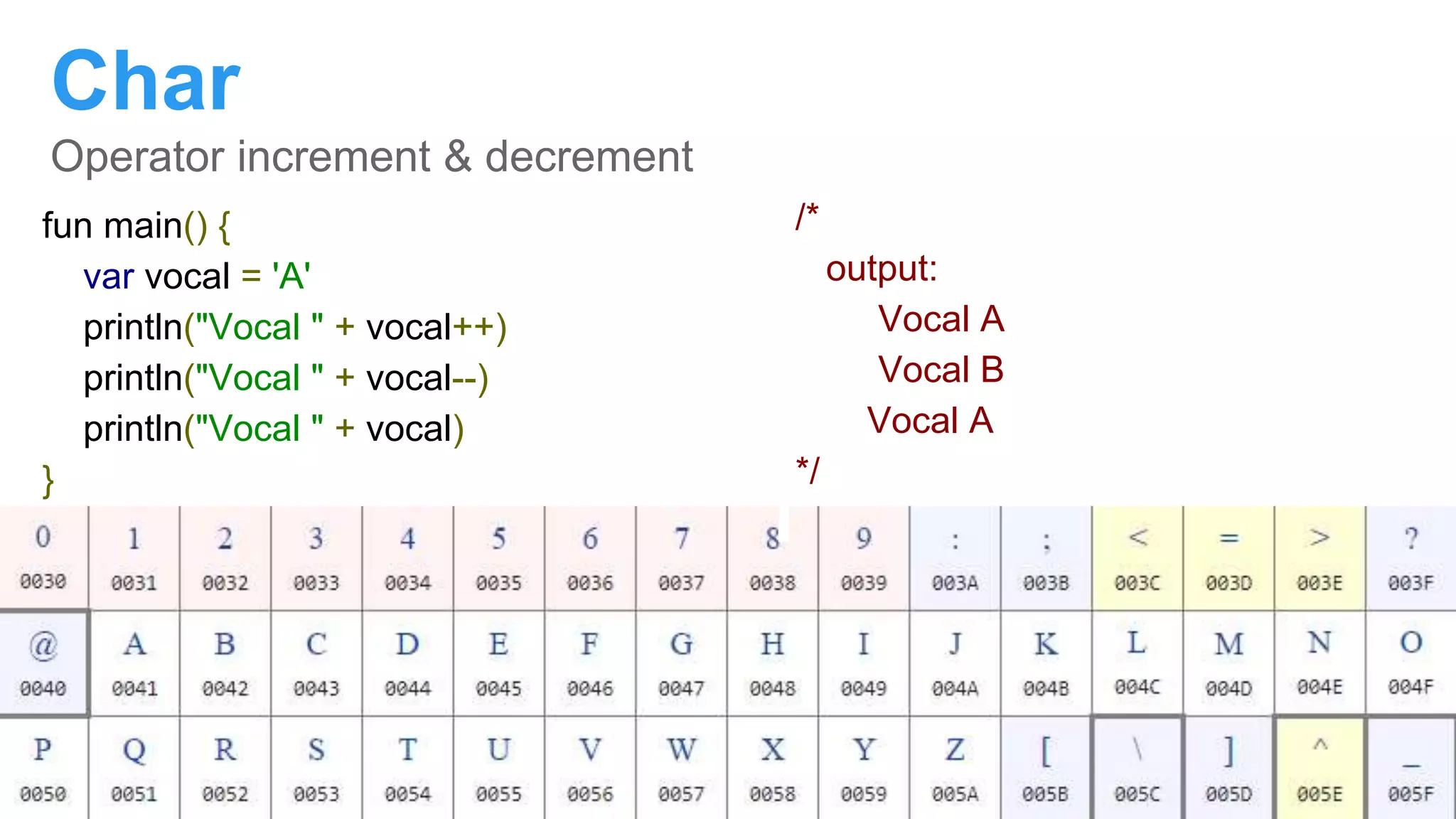
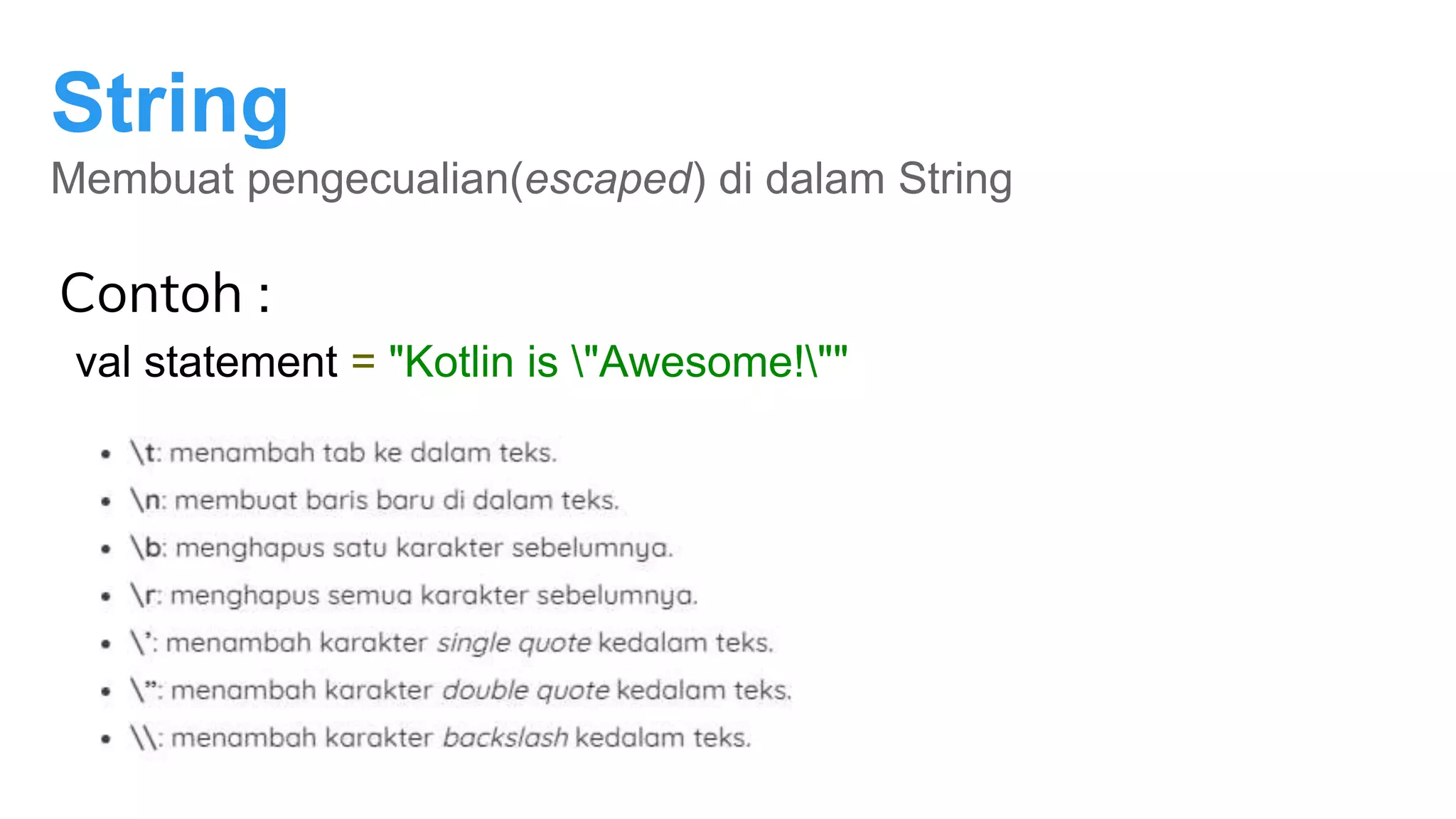
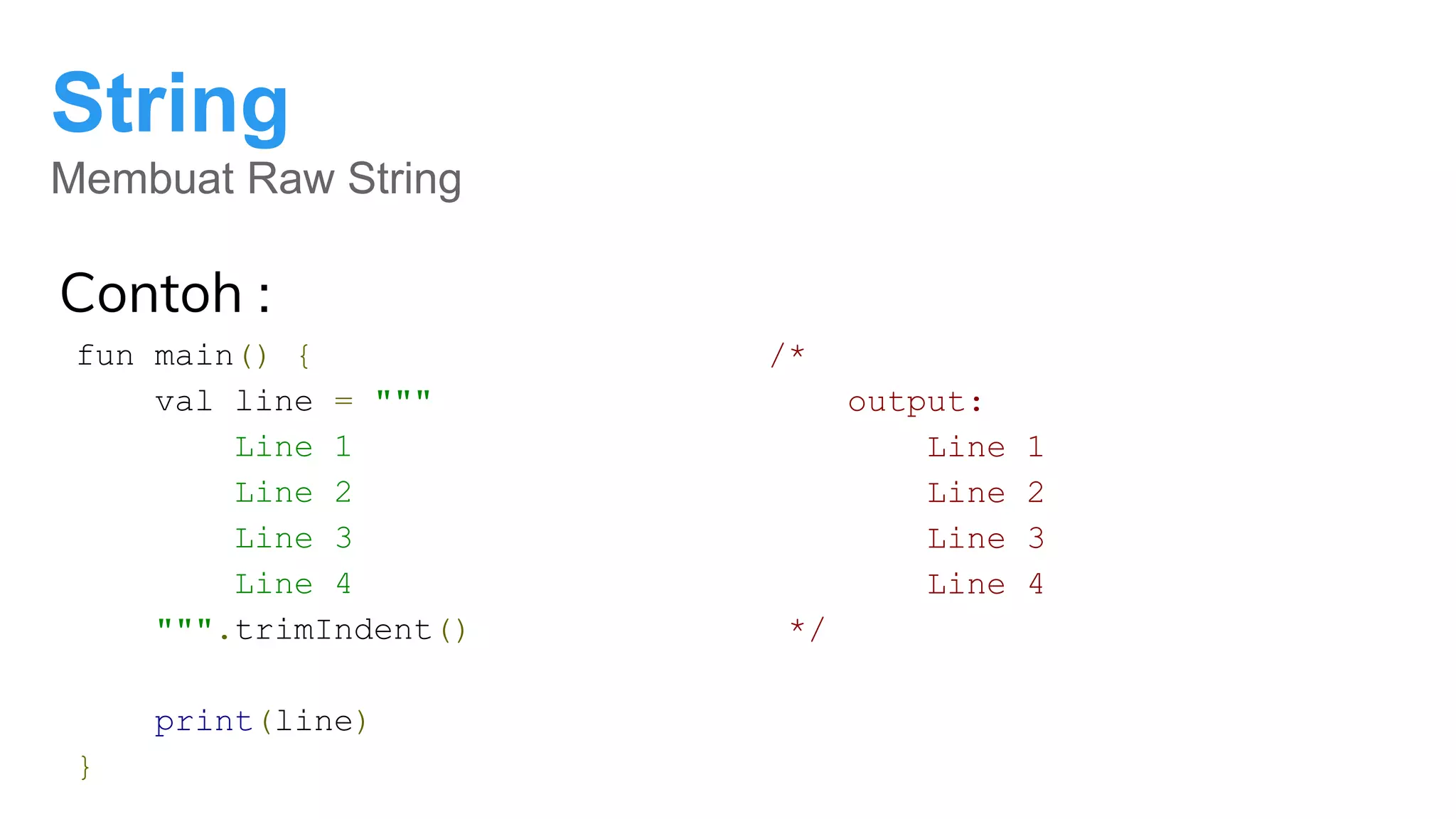
This document provides tips and tricks for installing Kotlin programming tools and covers fundamental Kotlin concepts like data types, variables, functions, control flow structures, and loops. It discusses installing Kotlin and resolving common errors. It introduces basic Kotlin syntax for strings, numbers, Booleans, arrays, and more. It also covers if/else expressions, when expressions, enums, loops like while, for, and for-each, and break/continue functionality. The document encourages practicing exercises to continue learning Kotlin.

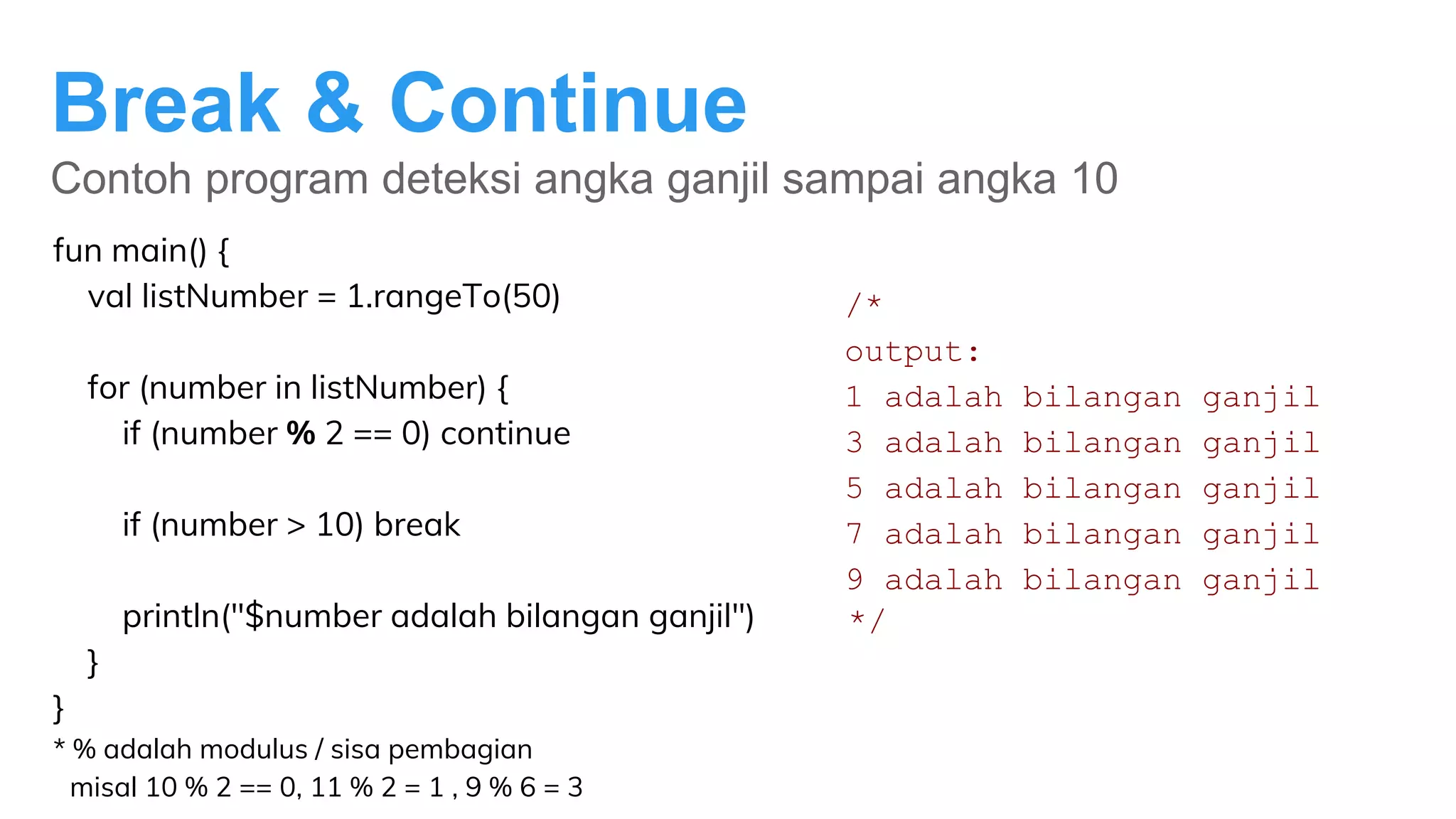
![String
Memasukkan variabel ke dalam String
Contoh :
fun main() {
val text = "Kotlin"
val firstChar = text[0]
print("First character of" + text + " is " + firstChar)
}
print("First character of $text is $firstChar") string template](https://image.slidesharecdn.com/dtsxdicoding2memulaipemrogramankotlin-200709043908/75/Dts-x-dicoding-2-memulai-pemrograman-kotlin-13-2048.jpg)
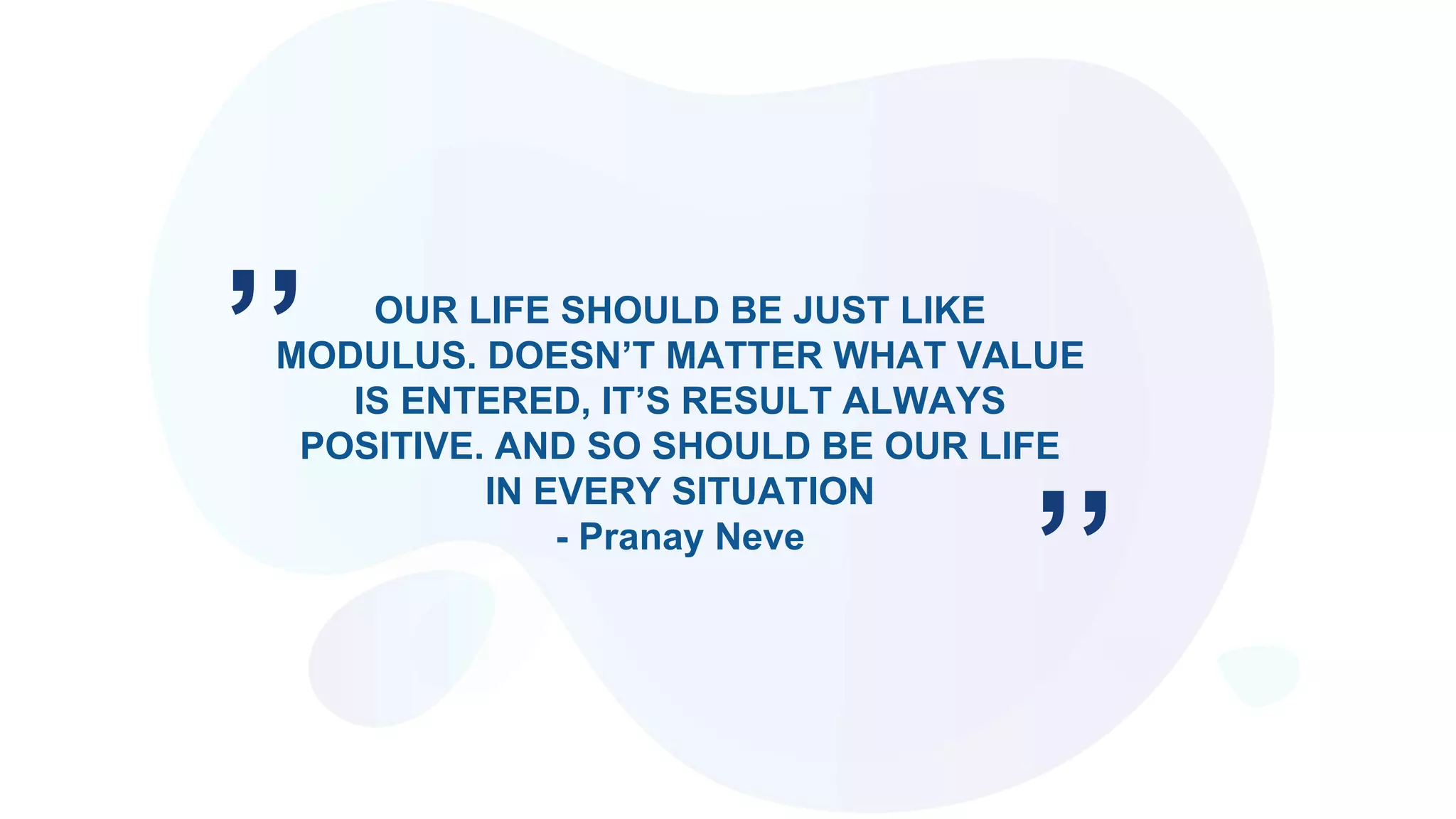
![Array
indeks dimulai dari 0
fun main() {
val intArray = intArrayOf(1, 3, 5, 7) // [1, 3, 5, 7]
intArray[2] = 11 // [1, 3, 11, 7]
print(intArray[2])
}
/*
Output: 11
*/
1 3 5 7
ke-0 ke-1 ke-2 ke-3](https://image.slidesharecdn.com/dtsxdicoding2memulaipemrogramankotlin-200709043908/75/Dts-x-dicoding-2-memulai-pemrograman-kotlin-16-2048.jpg)