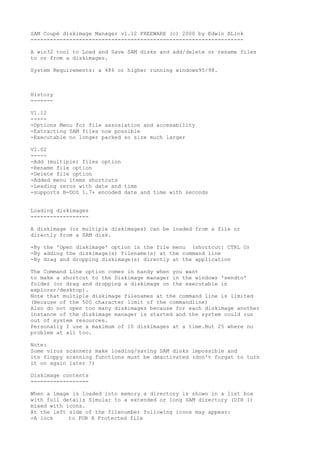
Diskmanager112
- 1. SAM Coupé diskimage Manager v1.12 FREEWARE (c) 2000 by Edwin BLink ------------------------------------------------------------------ A win32 tool to Load and Save SAM disks and add/delete or rename files to or from a diskimages. System Requirements: a 486 or higher running windows95/98. History ------- V1.12 ----- -Options Menu for file assosiation and accesability -Extracting SAM files now possible -Executable no longer packed so size much larger V1.02 ----- -Add (multiple) files option -Rename file option -Delete file option -Added menu items shortcuts -Leading zeros with date and time -supports B-DOS 1.7+ encoded date and time with seconds Loading diskimages ------------------ A diskimage (or multiple diskimages) can be loaded from a file or directly from a SAM disk. -By the 'Open diskimage' option in the file menu (shortcut: CTRL O) -By adding the diskimage(s) filename(s) at the command line -By drag and dropping diskimage(s) directly at the application The Command Line option comes in handy when you want to make a shortcut to the Diskimage manager in the windows 'sendto' folder (or drag and dropping a diskimage on the executable in explorer/desktop). Note that multiple diskimage filenames at the command line is limited (Because of the 500 character limit of the commandline) Also do not open too many diskimages because for each diskimage another instance of the diskimage manager is started and the system could run out of system resources. Personally I use a maximum of 10 diskimages at a time.But 25 where no problem at all too. Note: Some virus scanners make loading/saving SAM disks impossible and its floppy scanning functions must be deactivated (don't forgat to turn it on again later !) Diskimage contents ------------------ When a image is loaded into memory a directory is shown in a list box with full details Simular to a extended or long SAM directory (DIR 1) mixed with icons. At the left side of the filenumber following icons may appear: -A lock to FOR A Protected file
- 2. -Magnifying Glass with Question mark for a hidden file -Magnifying Glass with Questionmart and a lock for a hidden and protected file. -A Yellow warning sign for a corrupted file. -No icon for a normal file Each filetype has its own characteristic icon. However SAM Basic and sam code files do have more than one icon. All files including the ZX spectrum +D/Disciple files are supported At the Statusbar details about the samdisk will show. These are -The disk format which can be SAM DOS,MasterDOS and B-DOS, -The disklabel (MasterDOS,B-DOS only) -The total number of files on the disk -The number of corrupted files. A corrupted file is a file which causes a End of file, or track/sector error. -The number of unused K-bytes on the disk. New diskimage -------------- Selecting this option will create a emty diskimage in memory. You can choose if the diskimage should be 'formatted' like a SAMDOS disk, MasterDos or B-DOS disk. A diskname can be entered for masterDOS (10 characters) and B-DOS (16 characters) only. Change disk name ---------------- Use this option to rename the diskimages diskname. Note: SAMDOS disks do not have a diskname. When the change disk name option is used on a SAMDOS diskimage. The diskimage format will change into masterdos format. Saving diskimages ----------------- Use the save option to save the diskimage. To save a diskimage with another name use the save as .. option. Use the Save option under the SAM disk menu option to save directly to a FORMATTED SAM disk in the A drive. Note: -When the file extension is .dsk it will be saved in .dsk format. -When the file extension is .sad it will be saved in .sad format. So changing the file extension will also change the diskimages format. EXTRACTING FILES ---------------- A SAM file (or ZX File) can be extracted from a diskimage and saved to disk. Note that files are saved as-is and that no conversion is done.
- 3. FILE ASSOSIATION ---------------- The Options menu has options to assosiate DSK and SAD diskmages with the Diskimage Manager. You can also choose the icon of your choice for the assosiated filetype(s). When a assosiated Icon has been selected it will become active after the system has been restarted. Beside the assosiations you can make a lot of shortcuts to access the Diskimage Manager quickly. -Add to Desktop. -Add to Quick Launch bar. (for Win95 with IE4 or Win98) -Add to Start Menu -Add to SendTo folder (rightmouse click at explorer, 'SendTo>' option) -Create a SAM Coupé Program Group Just try them out. Once any option has been selected it can be easely undone by unchecking the option. Note by clicking OK all options will be (re)created or removed. So when the Diskimage Manager has moved to a different folder or drive Clicking OK will automaticaly update all settings. Unchecking all options and clicking OK removes all settings just like a Uninstall. Finally ------- This program comes without any warranty. So use it on your own risk. SAM Coupé Diskimage Manager was programmed using Delphi 5 Feel free to send me Comments or Ideas, etc. Enjoy Edwin Blink. blinky@thekeyboard.com
