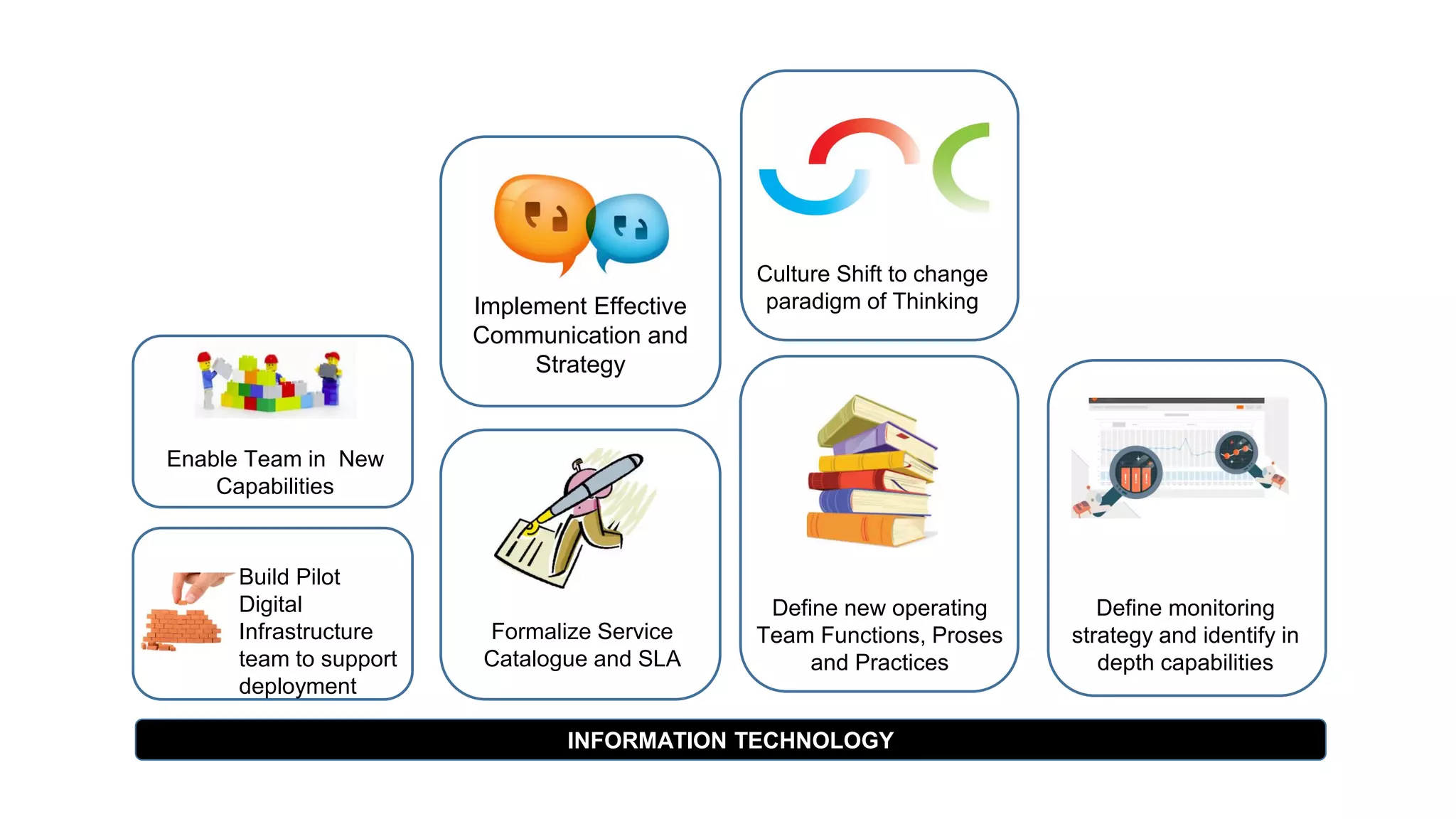
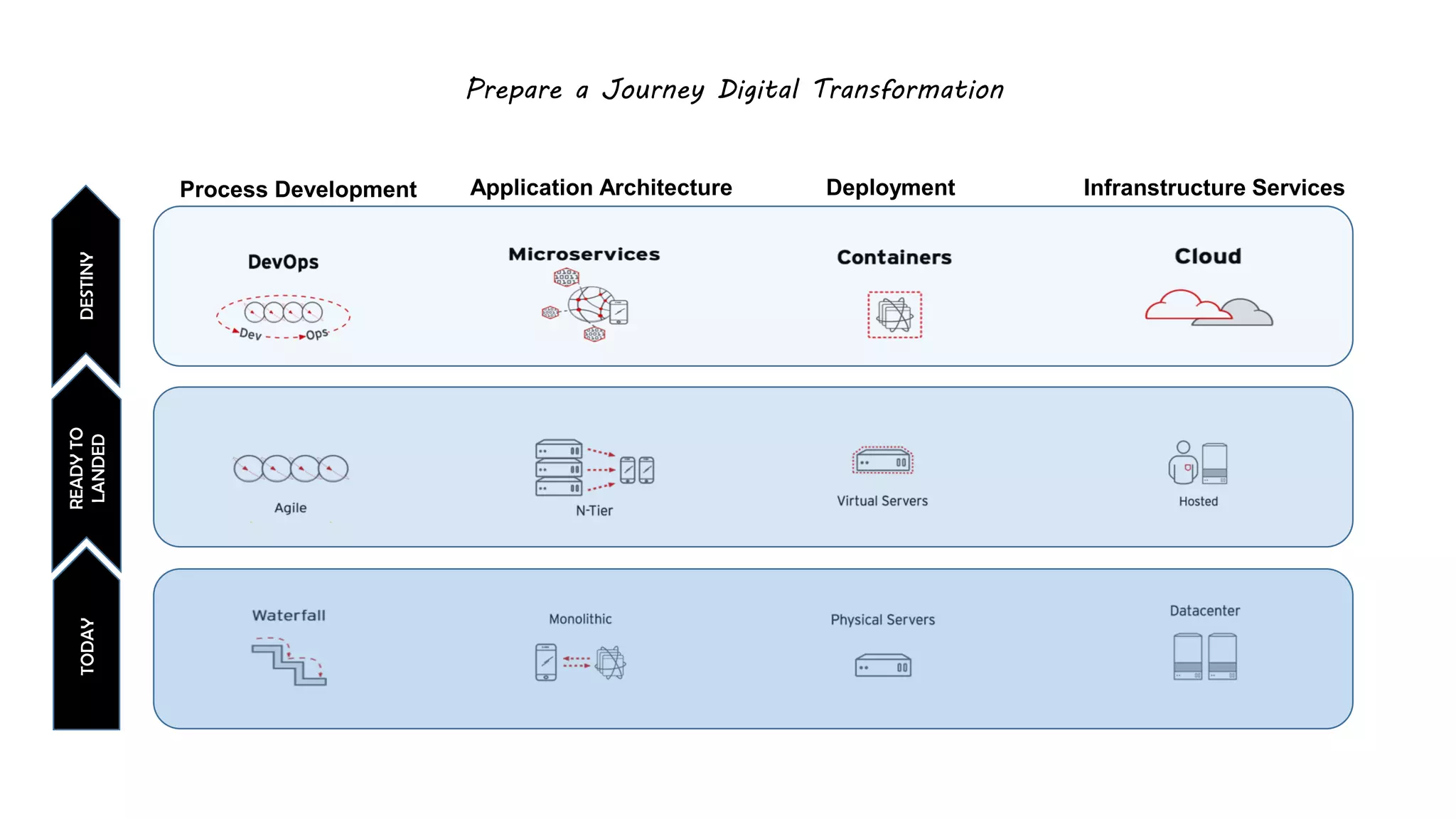
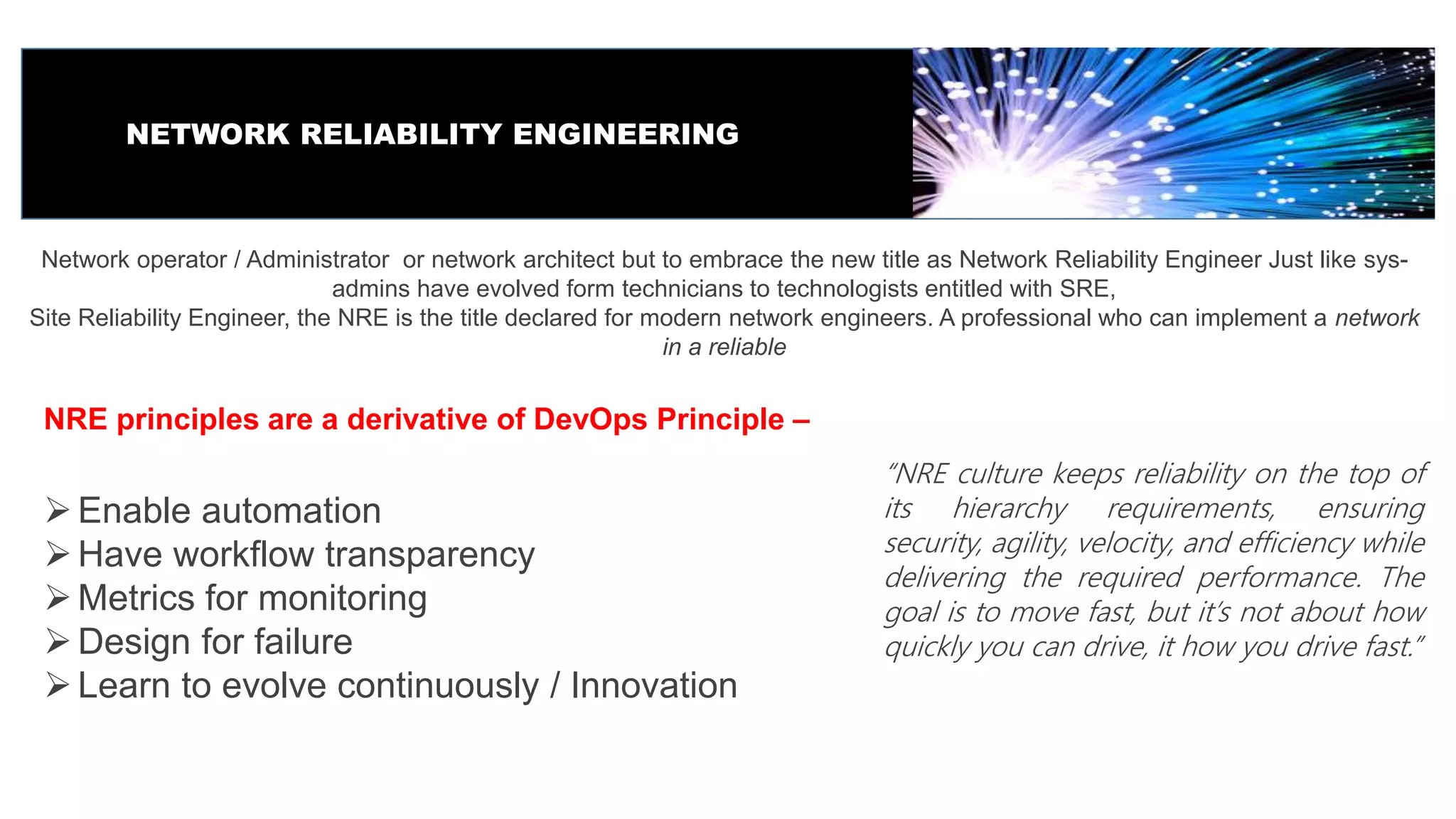
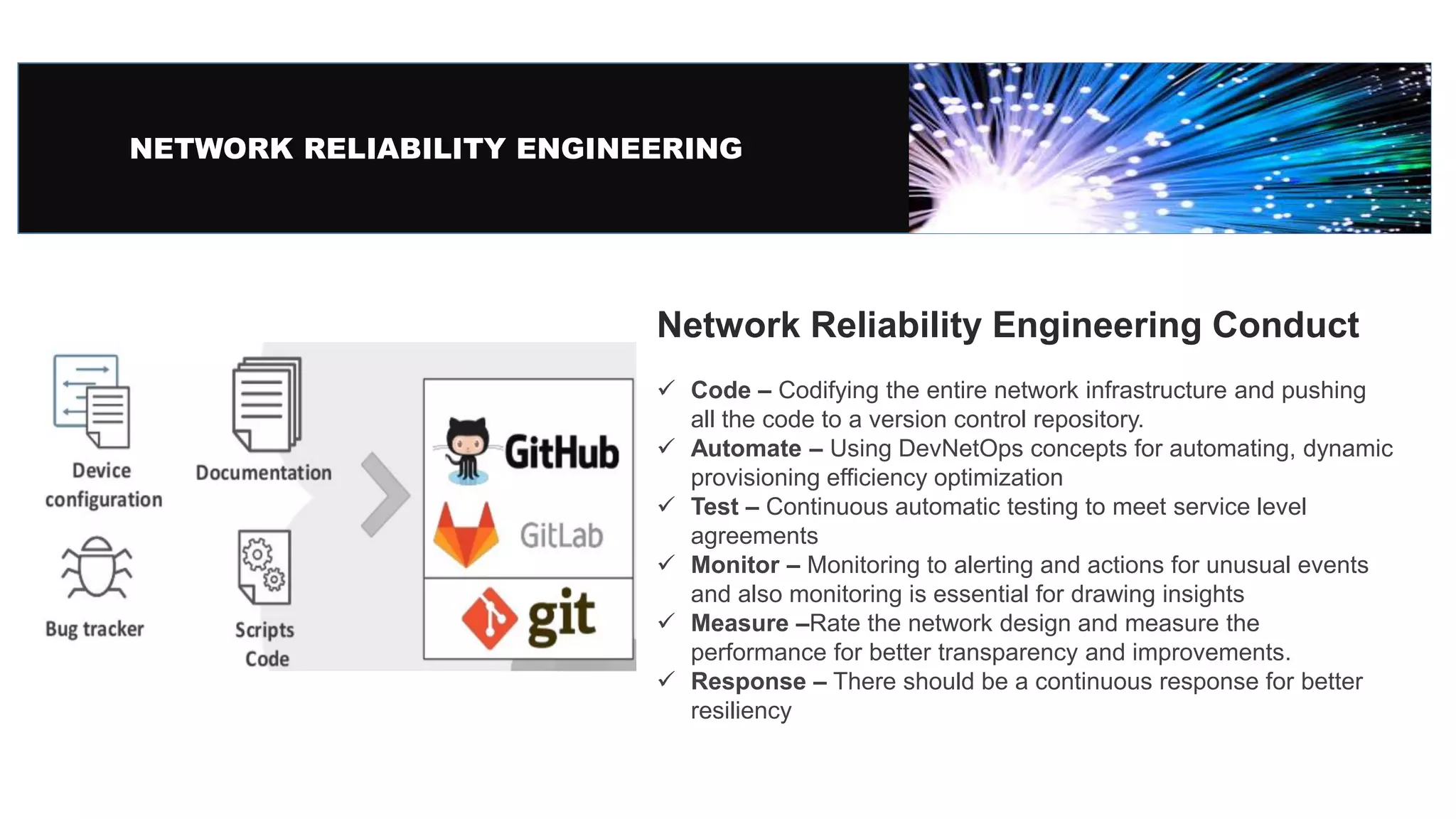
This document discusses digital transformation in infrastructure and the concept of Network Reliability Engineering. It recommends adopting the title of Network Reliability Engineer to modernize the role of network operators and administrators. The key principles of Network Reliability Engineering are derived from DevOps and include automation, workflow transparency, monitoring with metrics, designing for failure, and continuous learning and innovation. Conduct under Network Reliability Engineering includes coding infrastructure, automating with DevNetOps concepts, continuous testing, monitoring with alerting and actions, measuring performance, and having continuous response for resiliency.