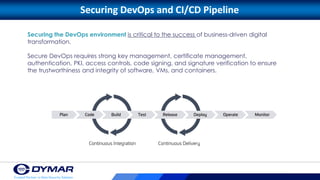
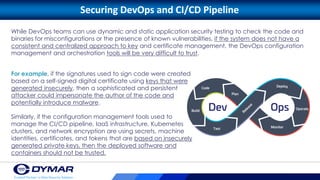
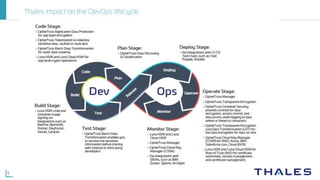
This document discusses securing the DevOps lifecycle with continuous trust. It provides an overview of DevOps and how security remains a challenge that impacts code and data integrity. It discusses how security and quality assurance teams must integrate with DevOps. The benefits of DevOps like speed, reliability, scalability and collaboration are described. It also discusses potential vulnerabilities in DevOps and how establishing a chain of trust across tools is needed. Hardware security modules and key management systems can help support security in DevOps tools that manage the CI/CD pipeline and infrastructure.