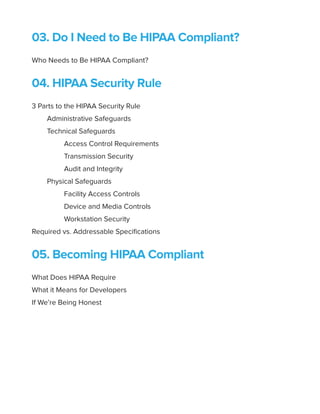
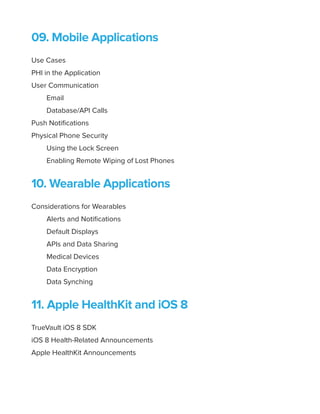
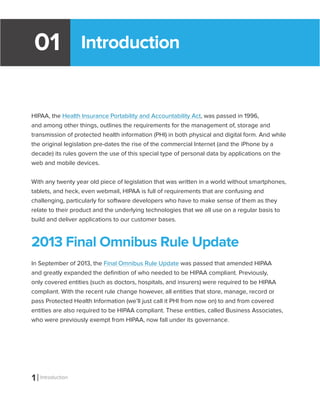
The document is a comprehensive guide on HIPAA compliance tailored for developers working with applications involving protected health information (PHI). It outlines the legal framework of HIPAA, the responsibilities of covered entities and business associates, and key rules such as the security, privacy, and breach notification rules. Additionally, the guide provides practical advice for achieving compliance and understanding the implications of HIPAA regulations on software development for mobile, web, and wearable applications.














![23 Developer Considerations
“[Building our own HIPAA compliant infrastructure] took upwards of 1,000
person-hours to figure out HIPAA-compliance issues. This will continue to
be an ongoing cost for us, because HIPAA is an ongoing law and it changes
sometimes. It takes substantial auditing time and money.”
— jph
Looking at it as a 1,000 hour project is one way to evaluate the true cost of rolling your
own compliance infrastructure, not to mention the ongoing audit and maintenance costs
associated with your in-house solution.
Unintended use cases
As we’ve mentioned before, HIPAA isn’t like the DMCA, there is no safe harbor clause for
unintended transmission, storage or disclosure of PHI. Regardless of how you planned it,
scoped it, envisioned it or dissuaded users from including it—if PHI is in your app or on your
servers you could face HIPAA fines if you’re not in compliance.
It’s not as big of an edge case as you might think. Here’s a few examples of how easily PHI
can enter into your application.
Your app to get doctor’s advice based on anonymous symptoms could easily have PHI as
soon as the patient shares an email address, lab report, or last doctor visit.
Your diabetes management app which tracks your blood sugar and prescription information
has a note added by the user of their doctor’s dosing instructions and pharmacy Rx number.
You get the idea. Regardless of how you intend for the user to use your application, there is
a pretty decent chance that if the application is related to personal health in any way, PHI will
ultimately end up in the system.
HIPAA Hosting and compliance
HIPAA hosting refers to website, application or data storage and hosting services that comply](https://image.slidesharecdn.com/developersguidetohipaacompliance1-140713192444-phpapp01/85/Application-Developers-Guide-to-HIPAA-Compliance-29-320.jpg)