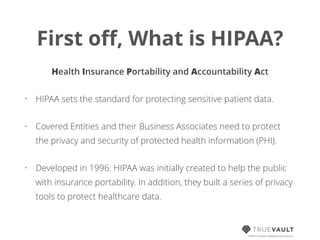
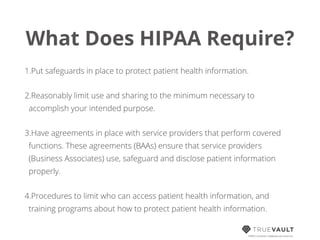
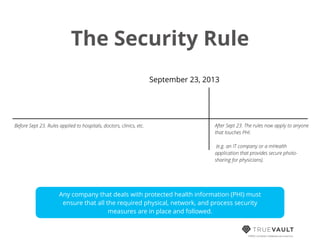
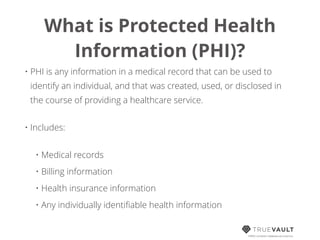
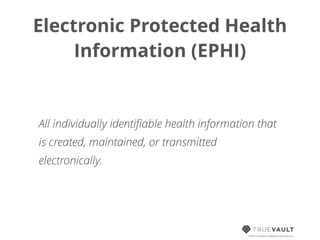
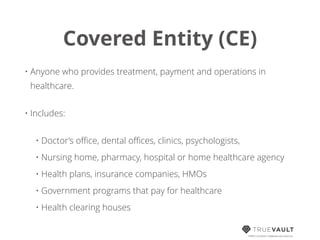
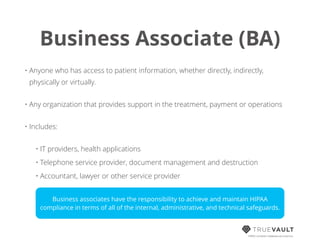
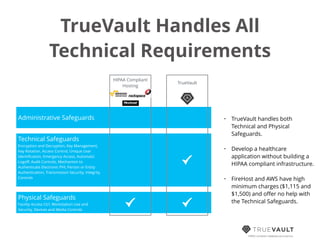
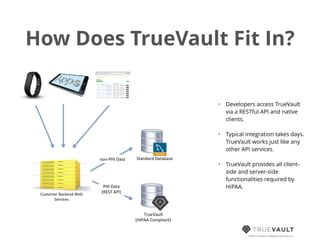
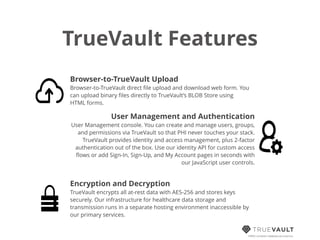
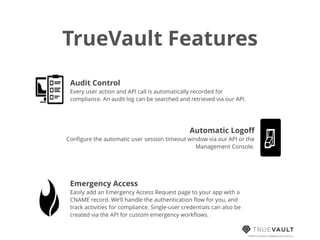
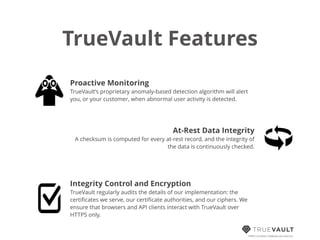
This document discusses HIPAA compliance for developers creating digital health applications, emphasizing the requirements and complexities of safeguarding protected health information (PHI). It details the rules associated with HIPAA, the importance of compliance for those handling PHI, and introduces TrueVault as a solution for simplifying compliance through its HIPAA-compliant database-as-a-service. The document also outlines the key safeguards that must be established, including administrative, technical, and physical protections.

![HIPAA Compliance is a
Brutal Time Suck!
!
“[Building our own HIPAA compliant infrastructure] took upwards of
1,000 person-hours to figure out HIPAA-compliance issues. This will
continue to be an ongoing cost for us, because HIPAA is an ongoing law
and it changes sometimes. It takes substantial auditing time and money.
TrueVault would save us all that.”
Posted on Hacker News by jph
(Unsolicited comment. Not a customer.)
HIPAA compliant database-as-a-service](https://image.slidesharecdn.com/hipaacompliancefordevelopers-140514235826-phpapp01/85/HIPAA-Compliance-for-Developers-2-320.jpg)