Embed presentation
Downloaded 51 times
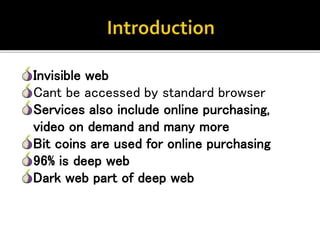
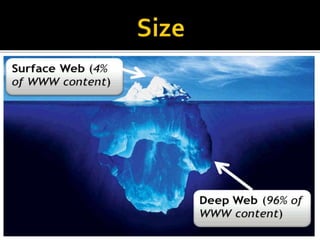
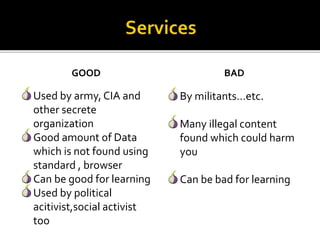
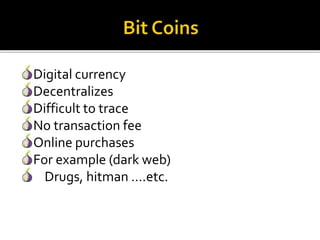
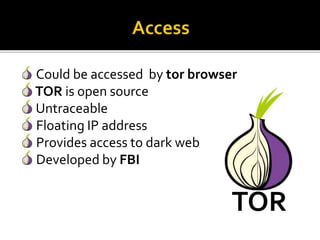
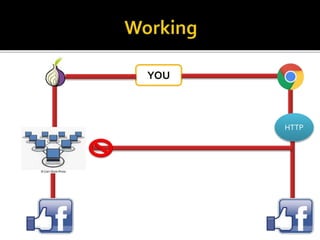
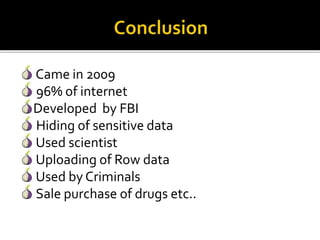
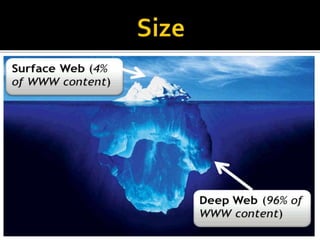
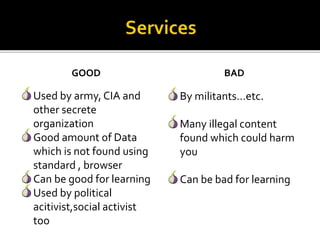
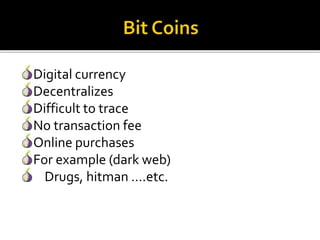
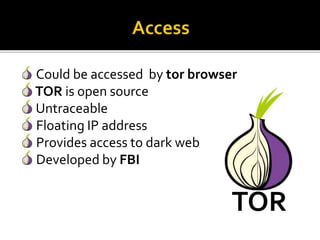
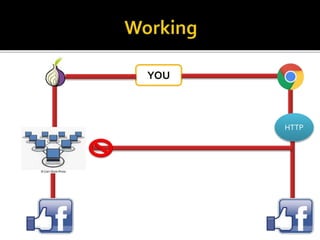
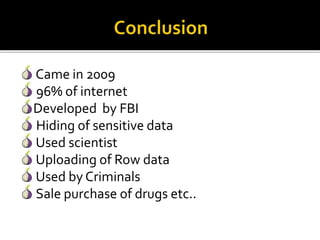
The document discusses the deep web and dark web, highlighting their vast size, the challenges of accessing their information, and their dual uses for both legitimate purposes (like research and political activism) and illegal activities (such as drug trafficking). It explains the importance of using specialized tools like the Tor browser for accessing these hidden parts of the internet while warning against potential dangers. Additionally, it emphasizes the role of digital currencies and the implications of anonymity in transactions.