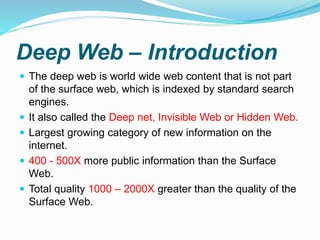
The document discusses the surface web and deep web, highlighting that the surface web is indexed by traditional search engines and constitutes only a small portion of online information, while the deep web contains significantly more content and includes hidden, dynamic, and non-html resources. It also describes the potential of the deep web, which can be a source of valuable information but is often associated with illegal activities accessed via specialized software like Tor, alongside the use of cryptocurrencies like bitcoin for anonymity in transactions. The future of the deep web may see a blending of content accessibility as more deep web information becomes available through search engines, while its complex nature continues to intrigue users.
![Surface Web
The surface web is that portion of the world wide web
that is index able by conventional search engines.
It is also known as the Clear net, the visible web or index
able web.
96% of web users use search engines to find needed
information, but nearly as high a percentage cite the
inability to find desired information as one of their biggest
frustration.
A traditional search engine sees only a small amount of
the information that’s available – a measly 0.03%
[source: OEDB]](https://image.slidesharecdn.com/darkwebpresentation-180111093630/85/Dark-web-presentation-2-320.jpg)