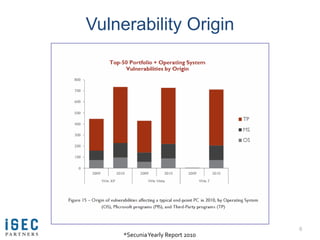
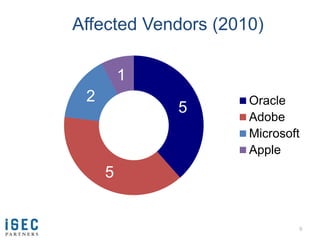
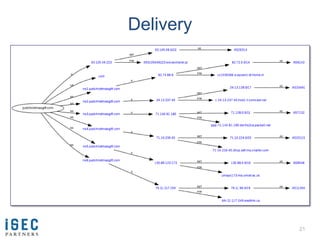
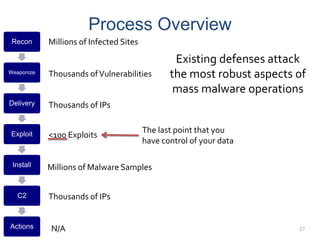
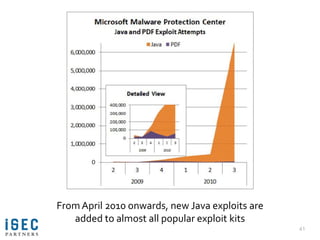
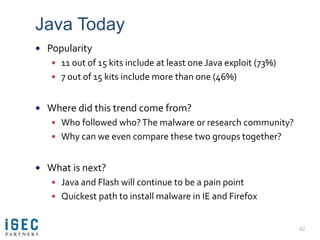
The document presents an analysis of attacker capabilities and methods in cybersecurity, emphasizing the effectiveness of intelligence-driven and threat-focused security strategies. It discusses trends and exploitation of vulnerabilities in software, particularly focusing on mass malware operations and the significance of timely responses to emerging threats. The presentation highlights the importance of aligning defense mechanisms with the processes attackers employ to improve security outcomes.






















































![Frequently Asked Question #4
Q: Future analysis?
A:
How [exactly] do researcher disclosures correlate with
massive exploitation?
Are the number of bugs exploited as zero-day
increasing? Why?
Do researchers follow zero-day disclosure trends or
vice-versa?
Exactly how much exploit code is modified from public
PoC’s before being integrated into a kit?
Expect new results some time in June
64](https://image.slidesharecdn.com/eip-final-110423210437-phpapp01/85/Dan-Guido-SOURCE-Boston-2011-64-320.jpg)