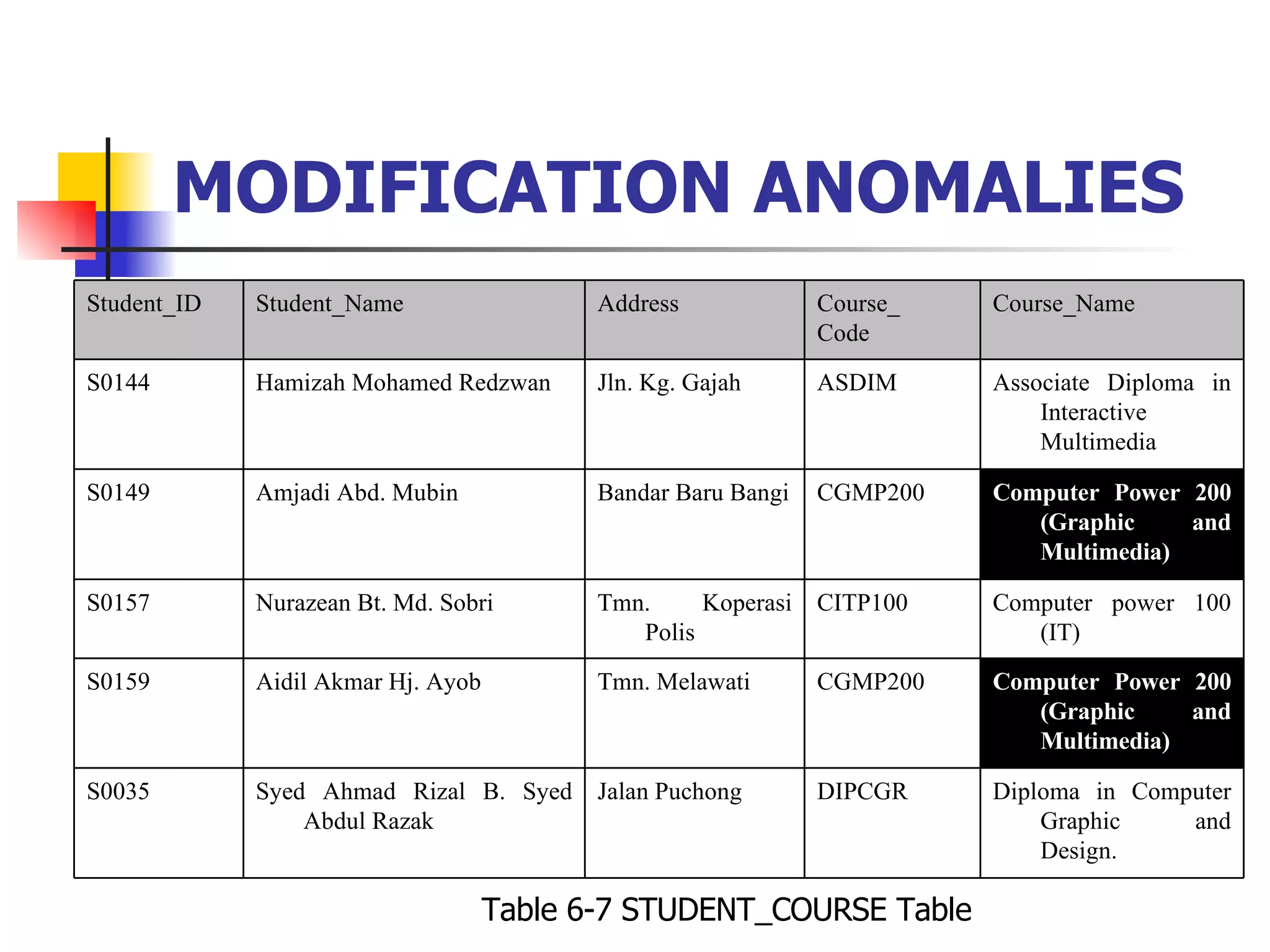
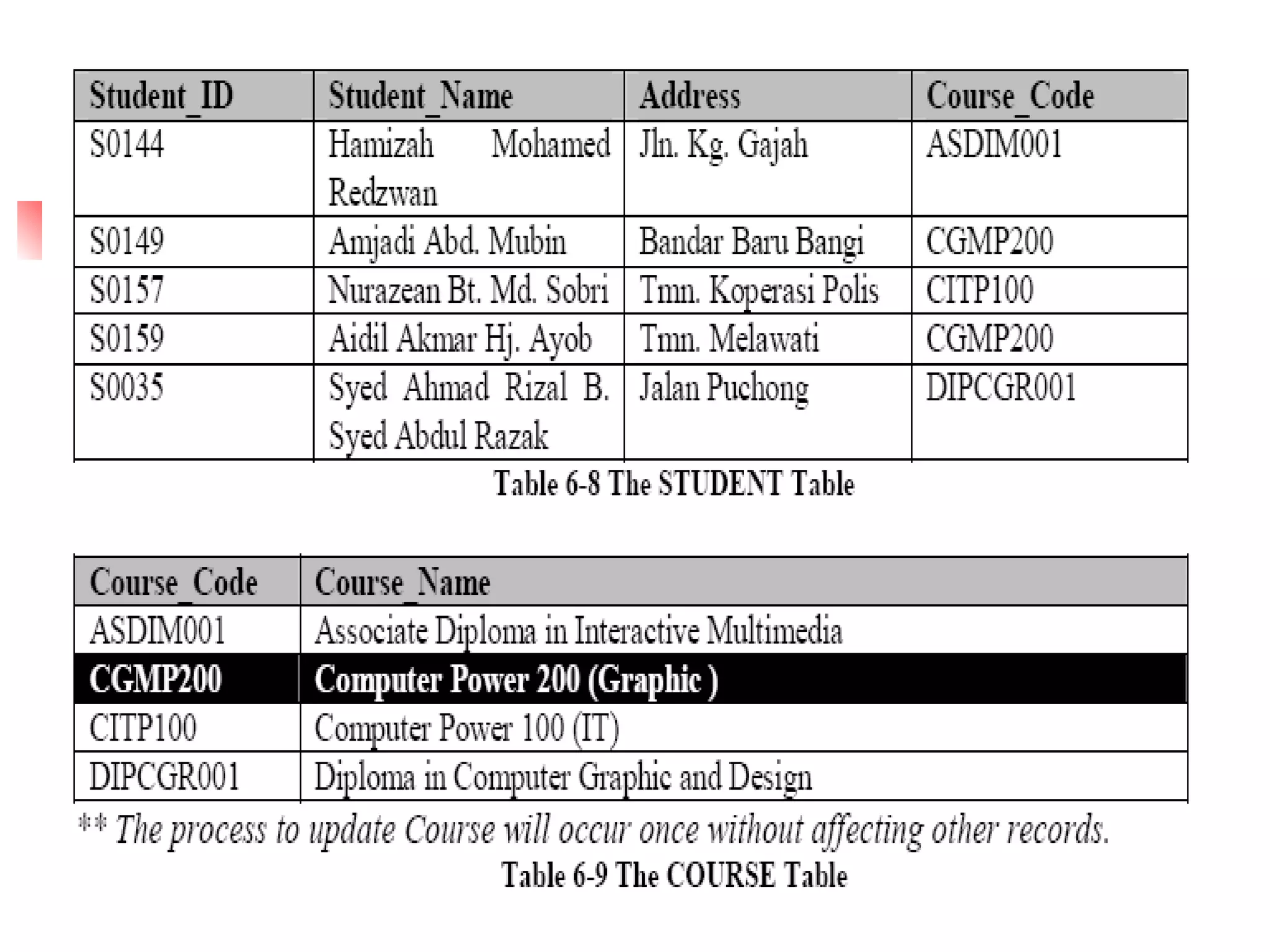
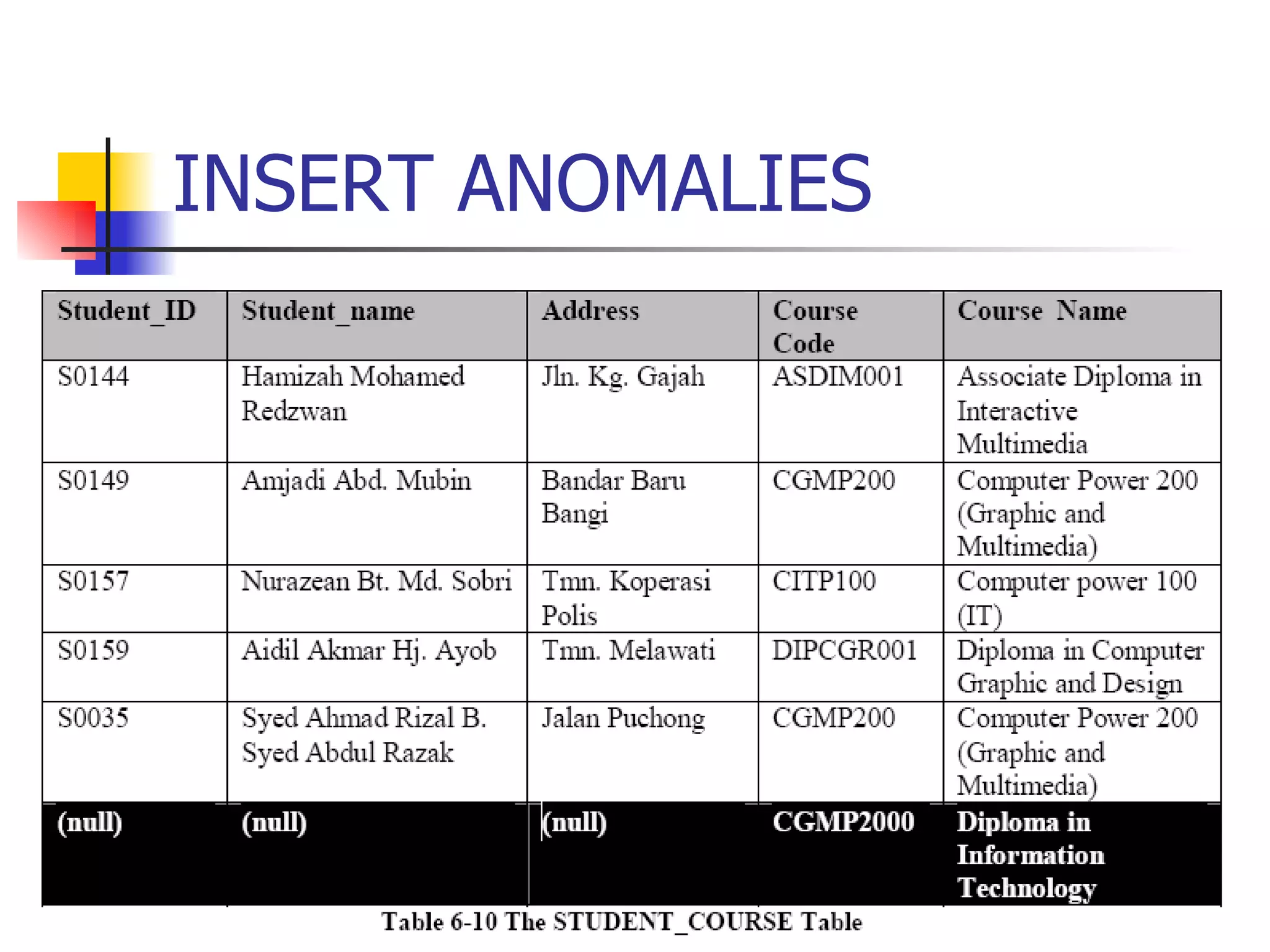
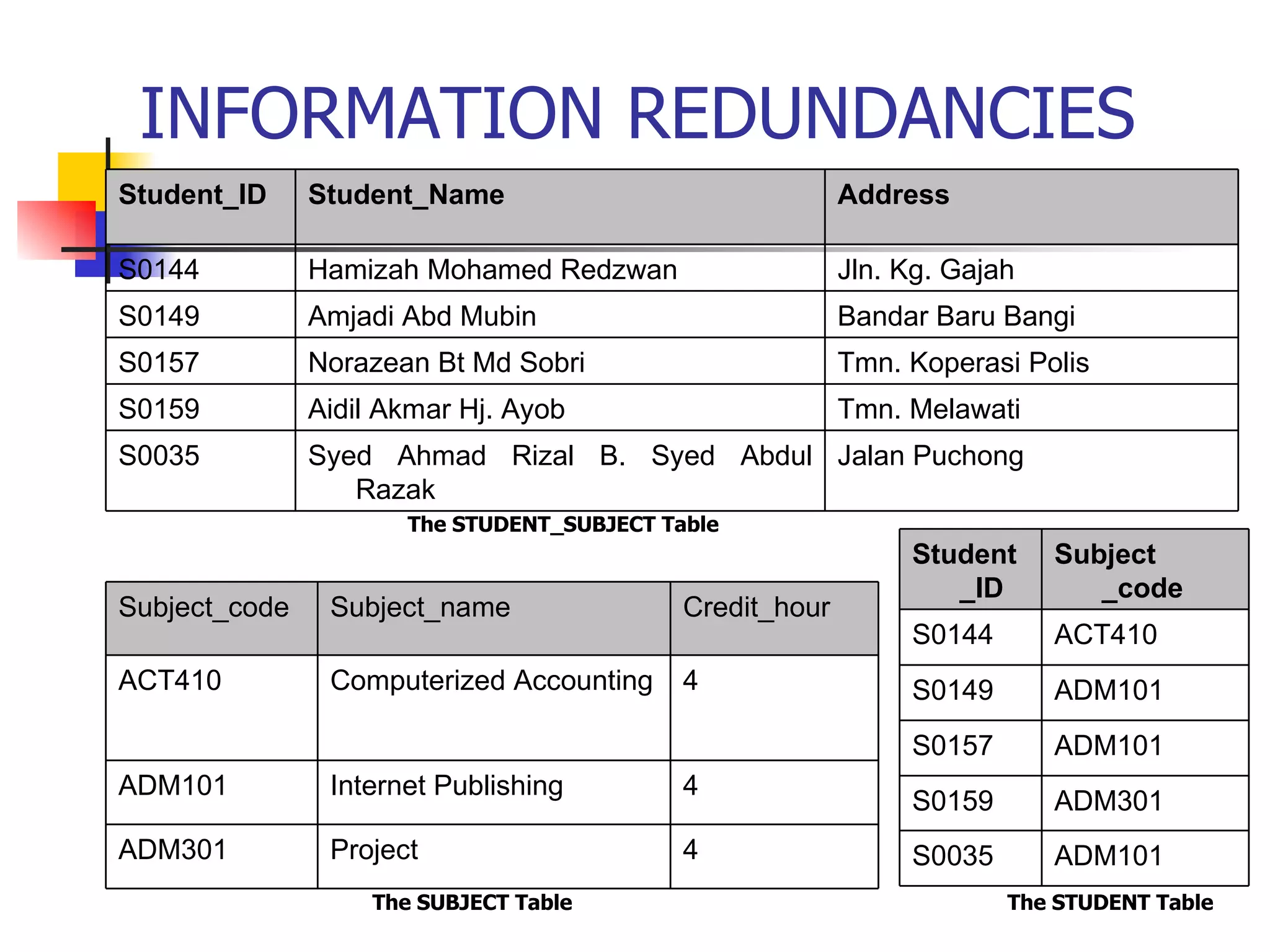
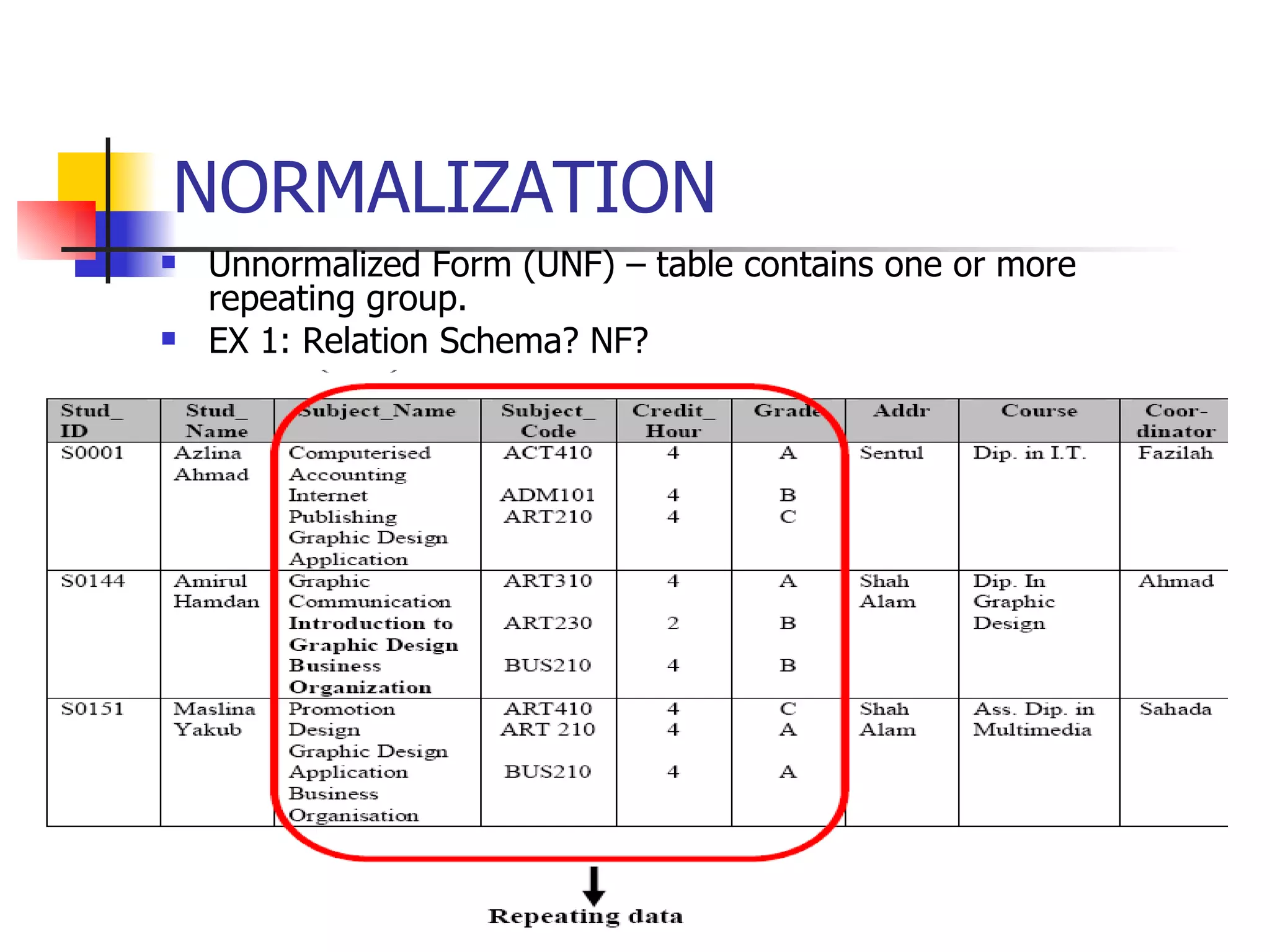
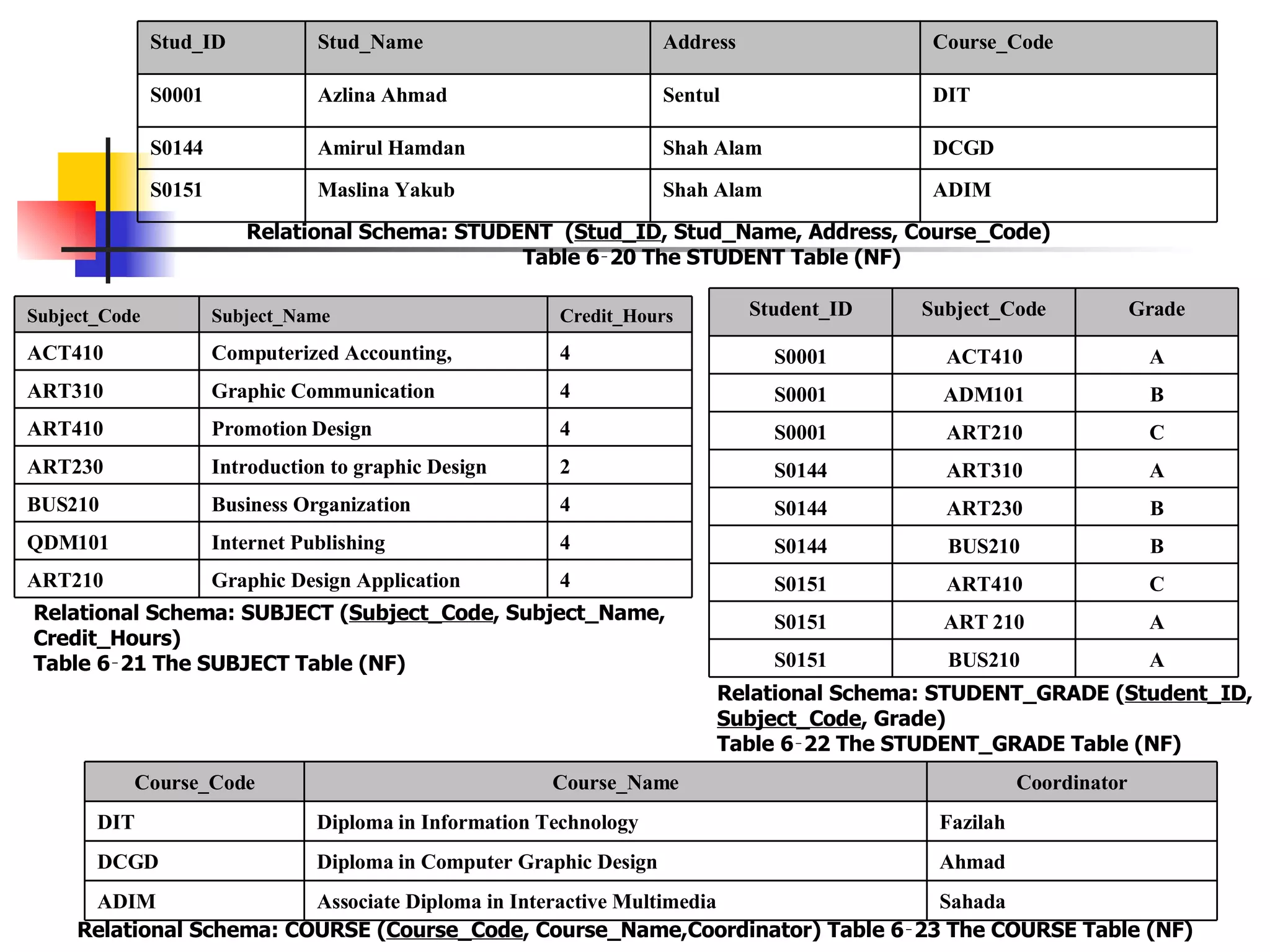
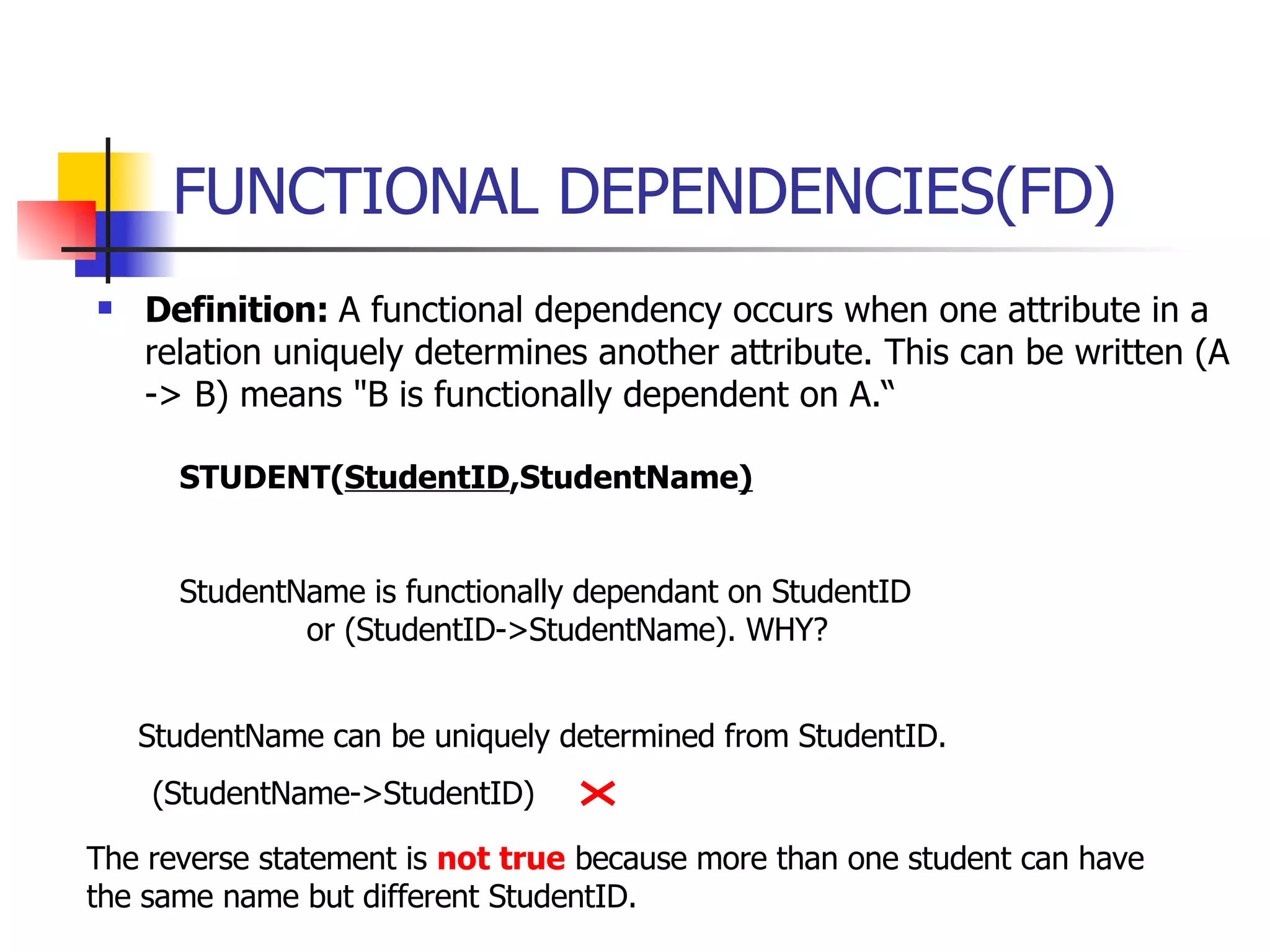
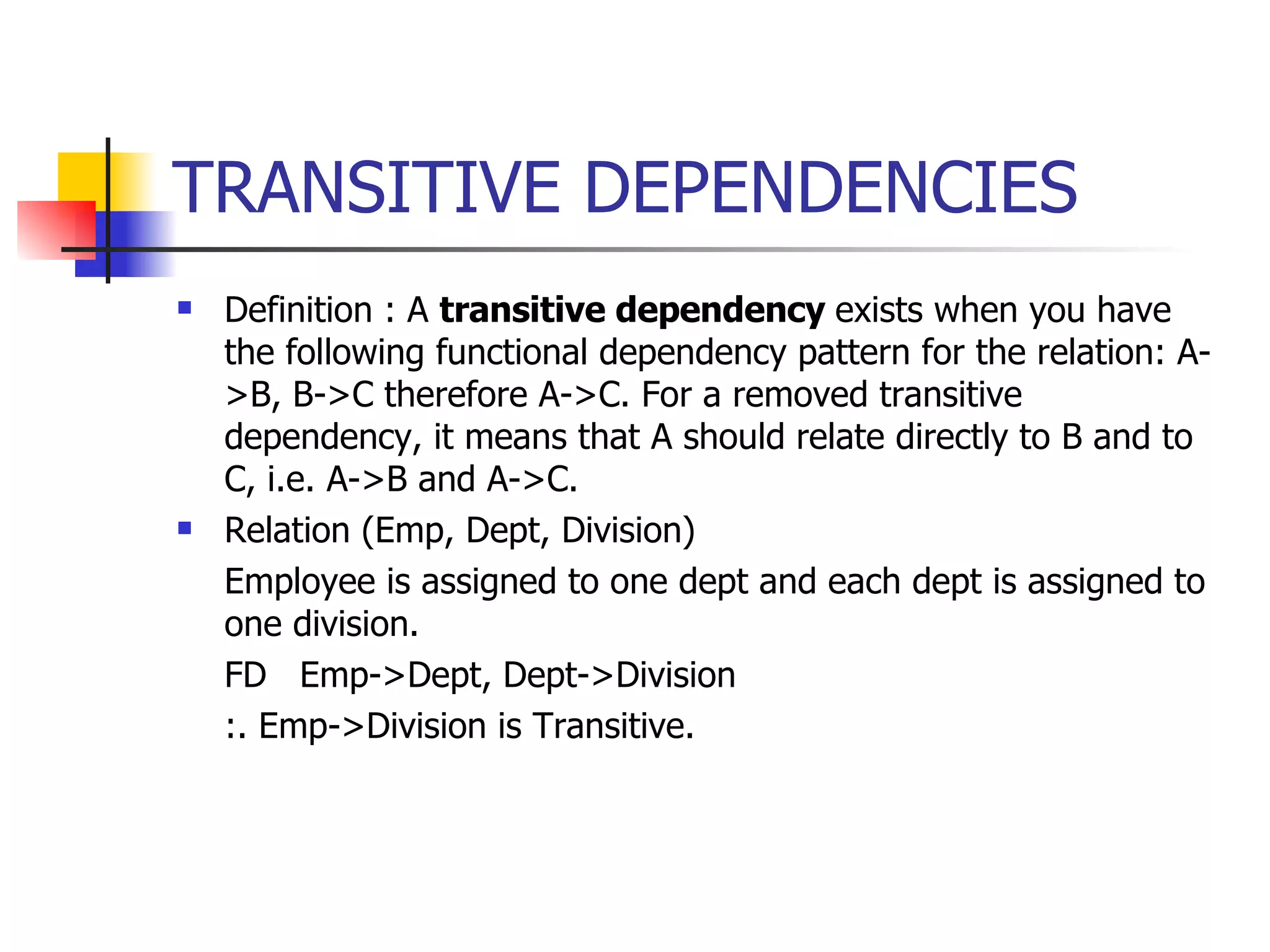
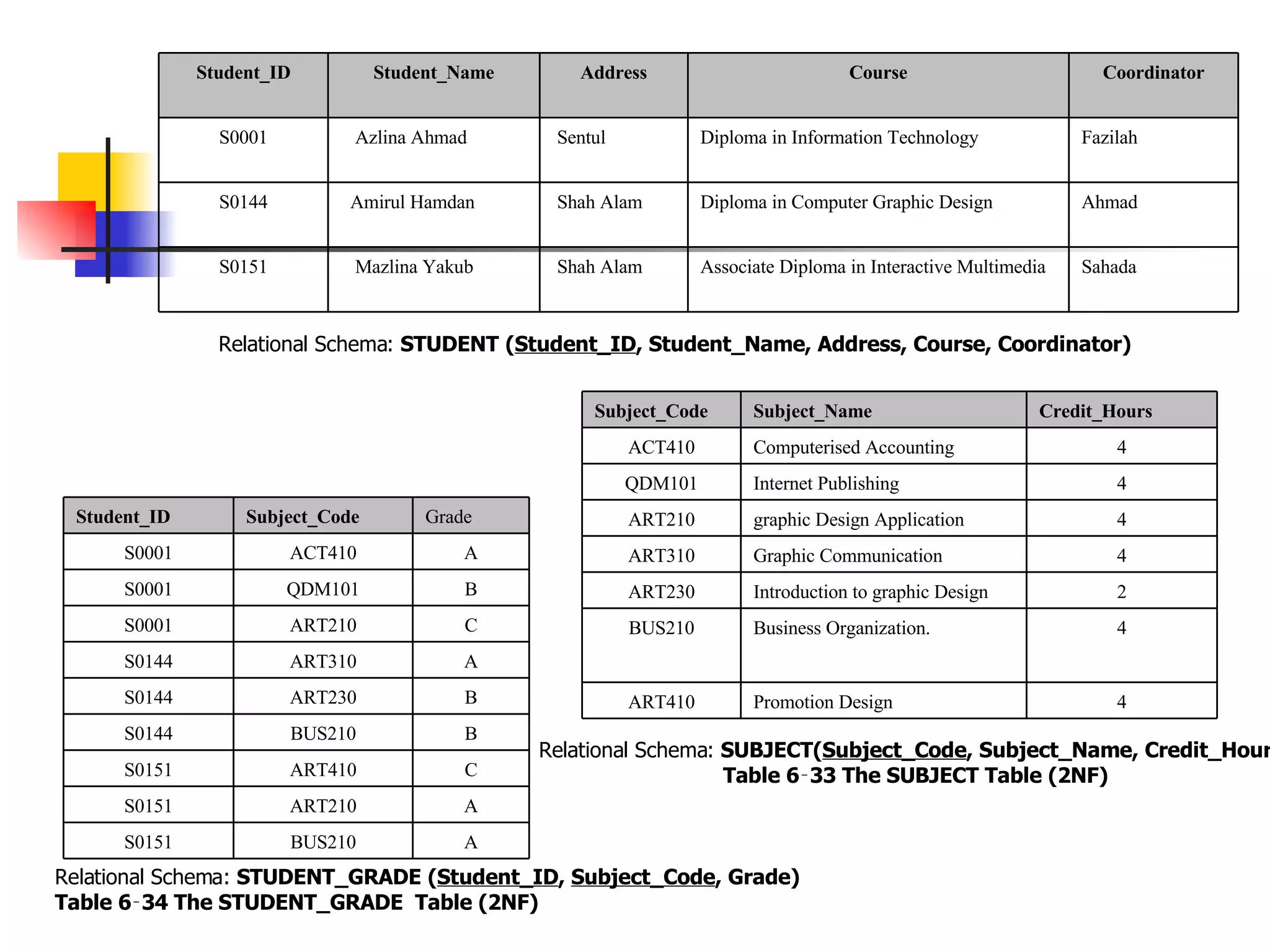
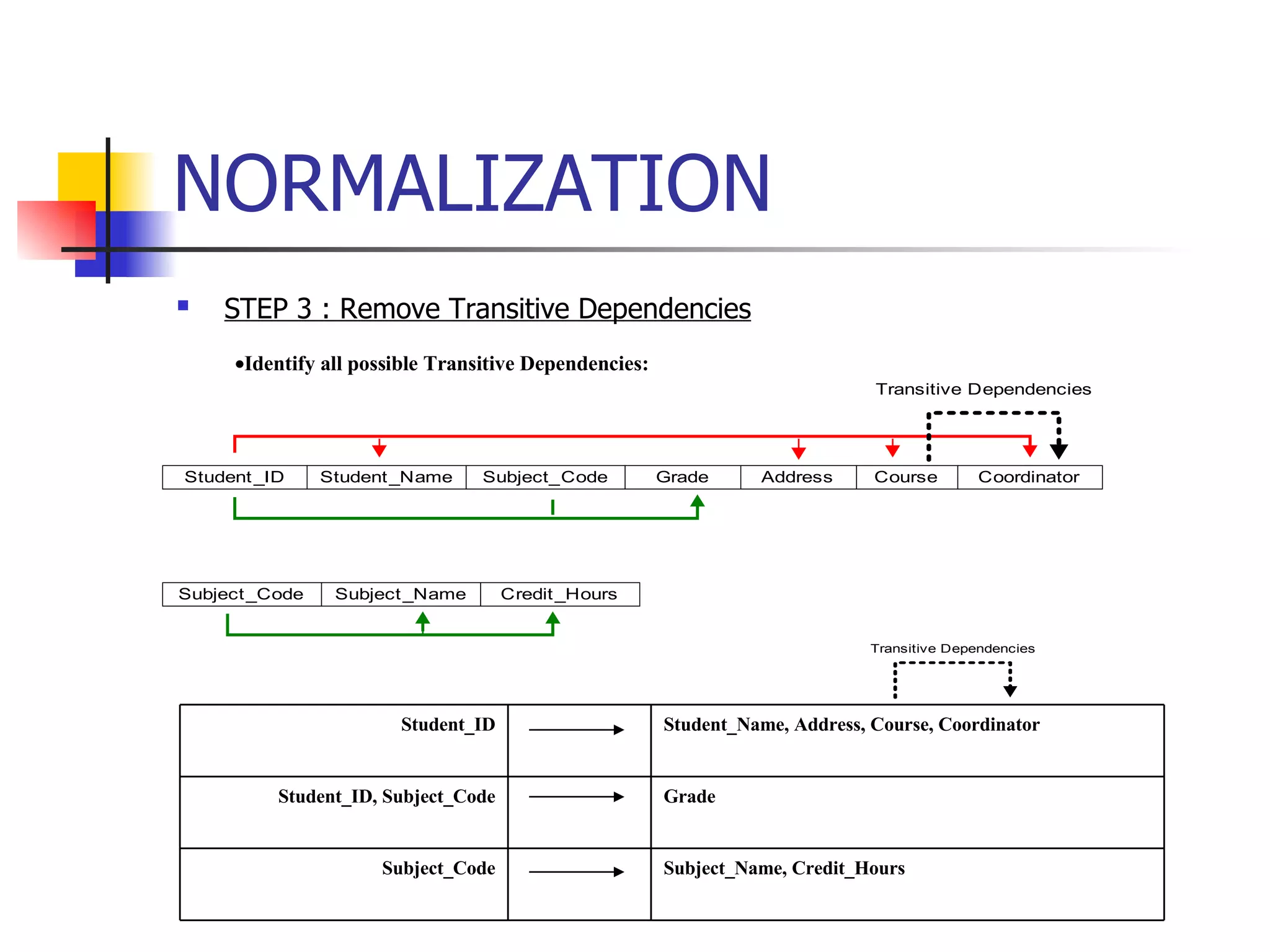
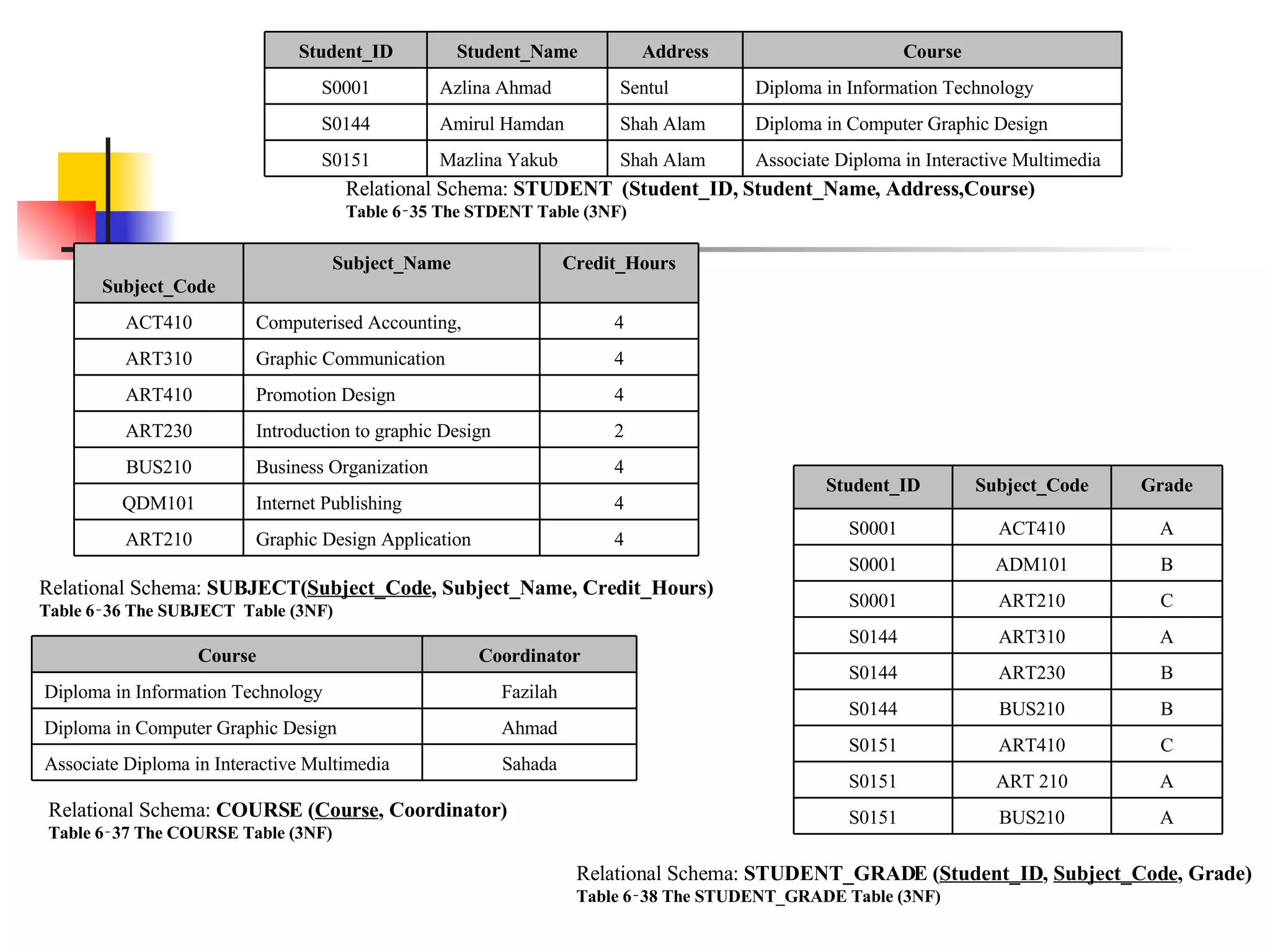
The document defines normalization and its purpose in reducing data redundancy and anomalies. It discusses normalization forms from 1NF to 3NF and the steps to normalize a data model, including identifying functional and transitive dependencies. The steps are to remove repeating groups, handle partial dependencies, and eliminate transitive dependencies to create tables in 3NF. Examples show functional dependencies determine a unique relationship between attributes.