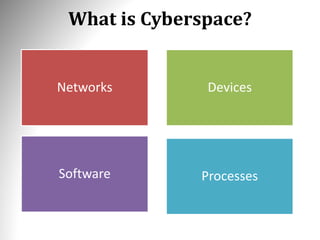
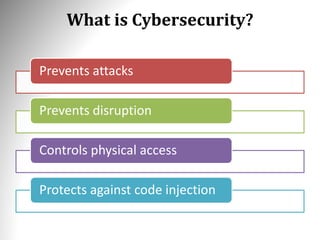
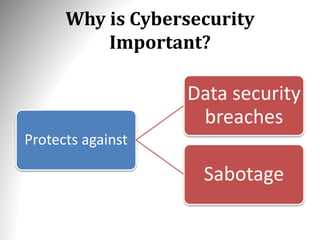
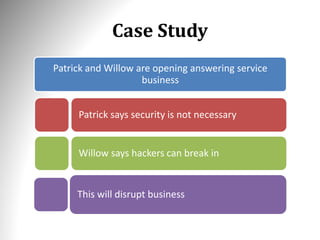
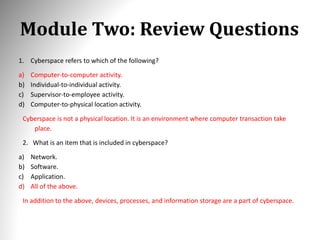
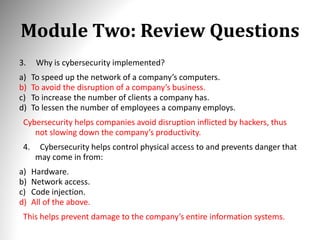
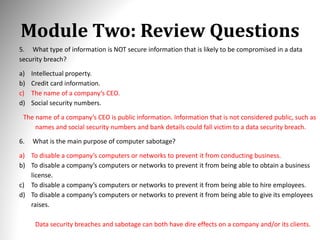
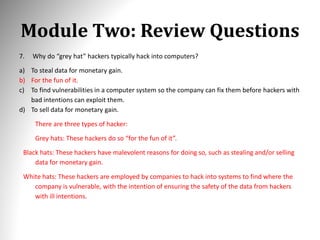
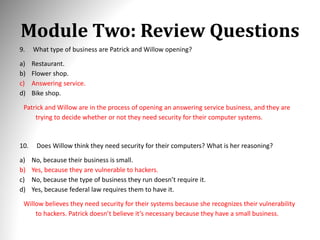
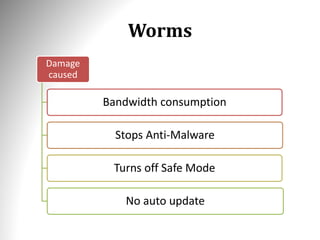
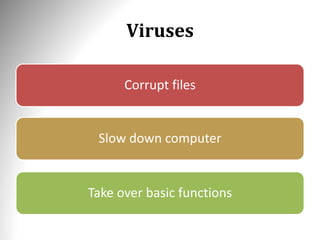
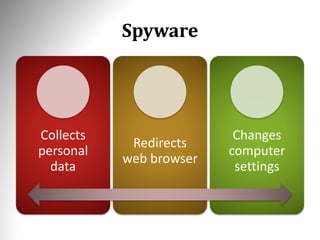
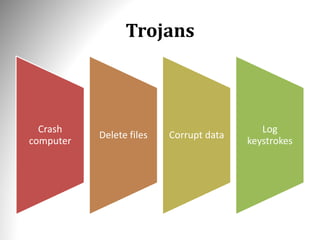
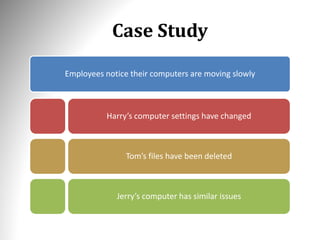
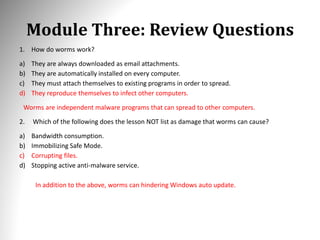
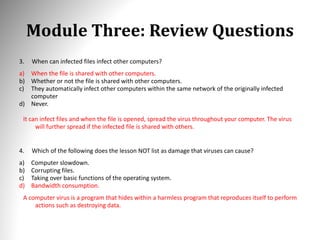
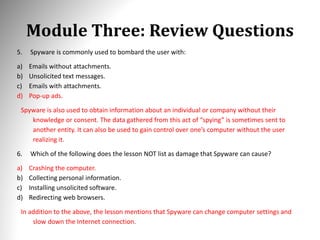
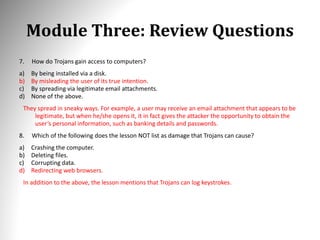
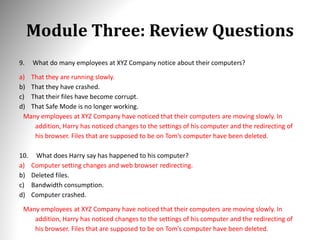
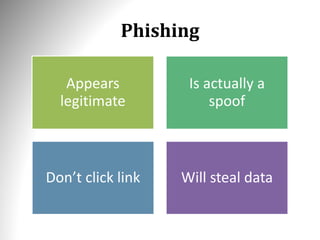
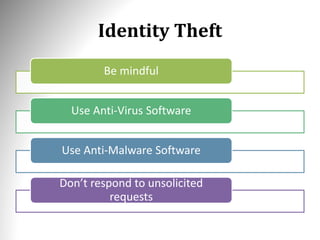
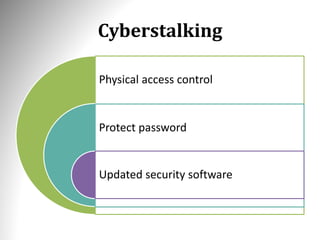
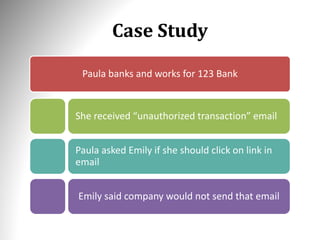
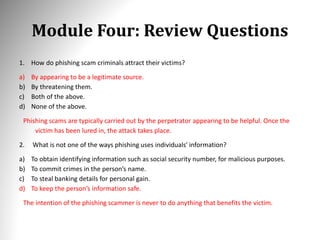
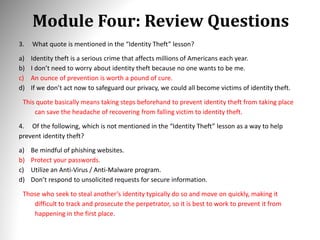
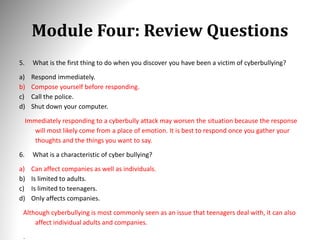
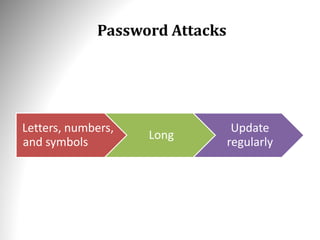
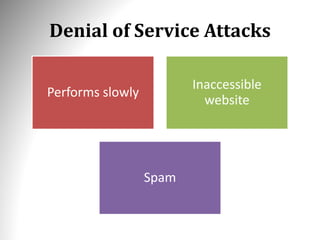
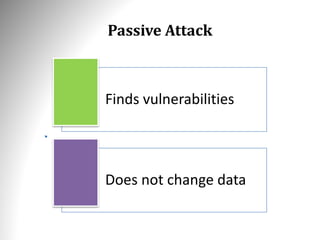
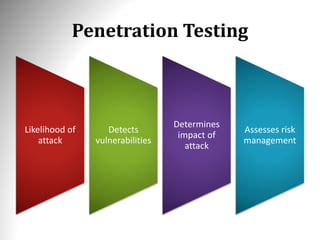
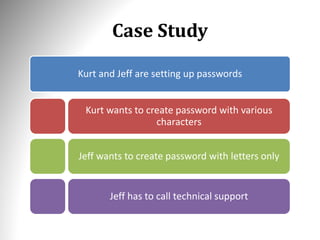
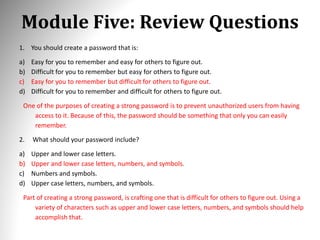
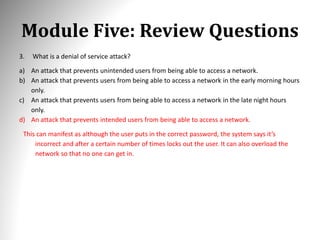
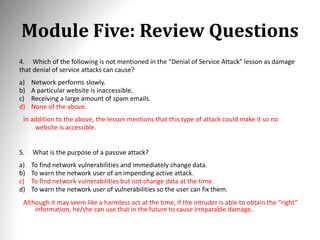
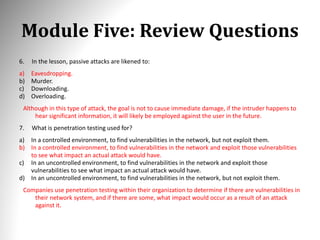
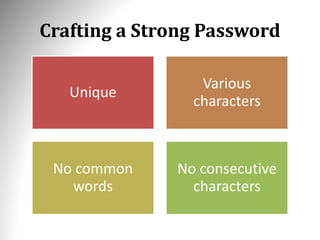
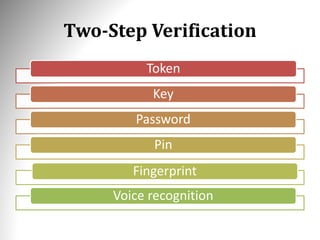
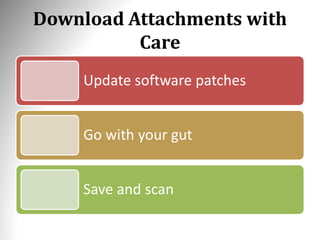
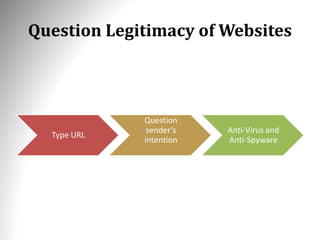
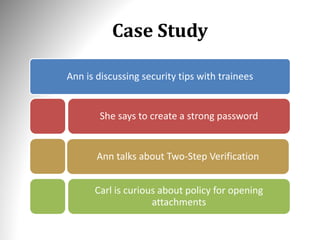
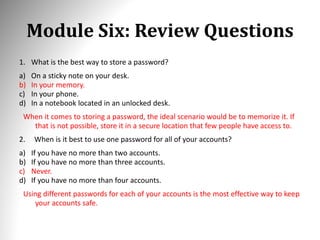
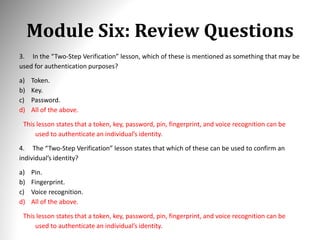
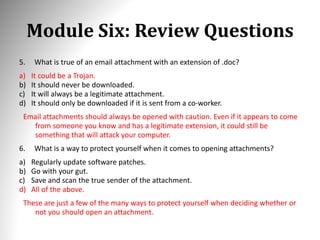
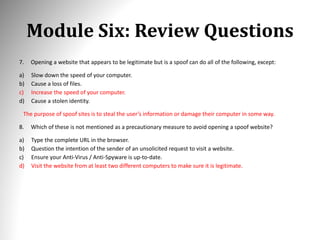
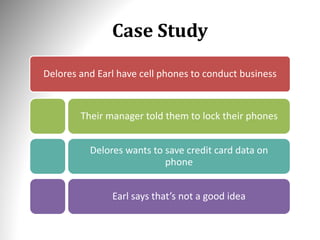
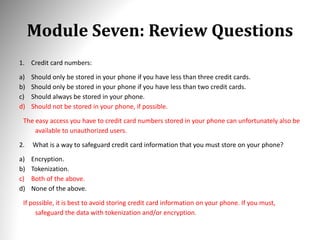
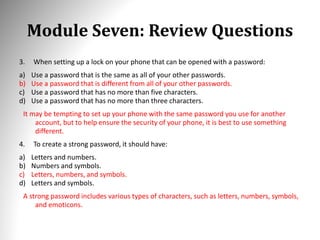
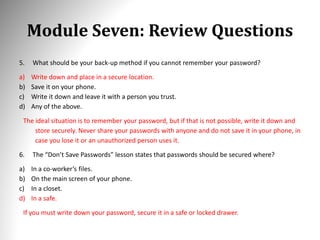
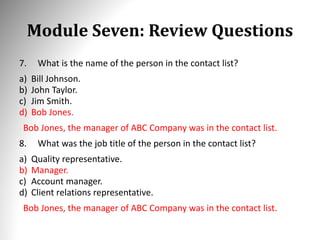
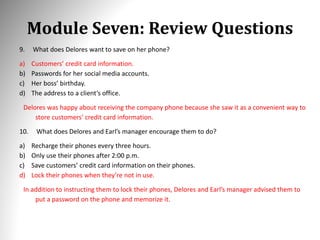
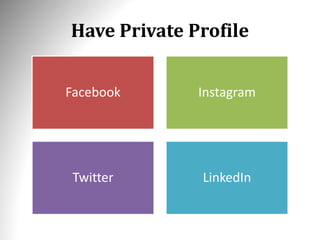
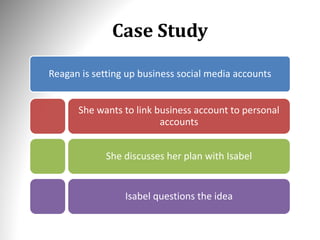
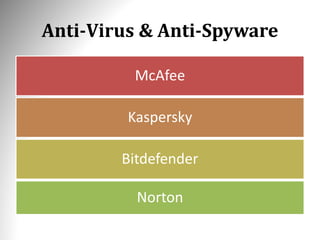
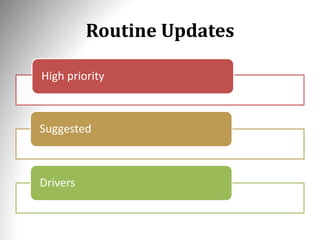
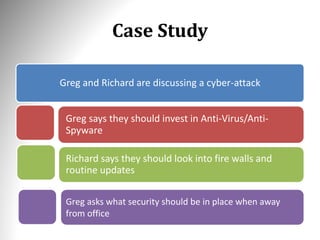
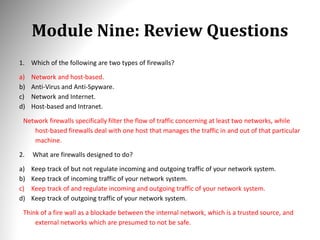
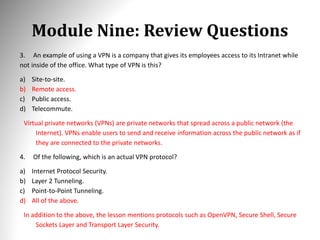
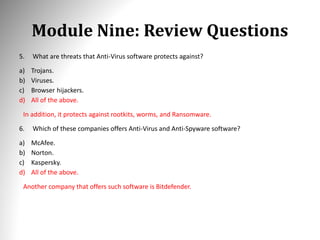
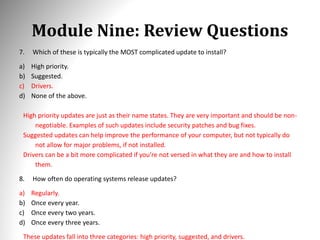
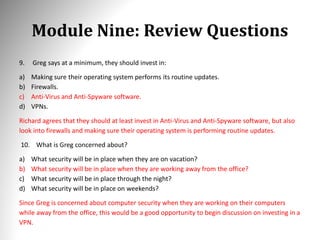
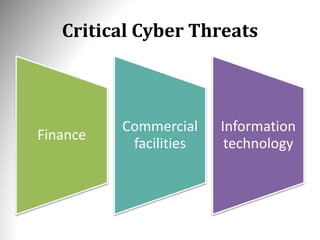
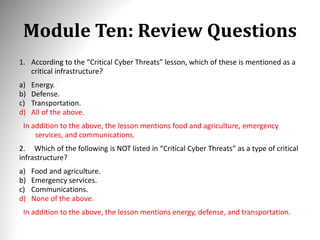
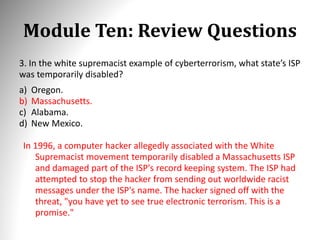
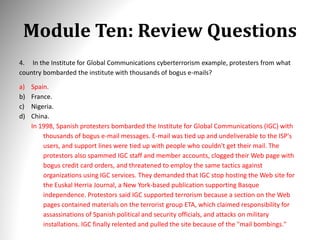
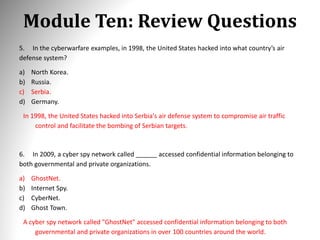
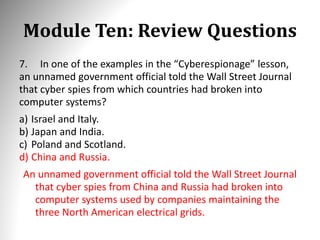
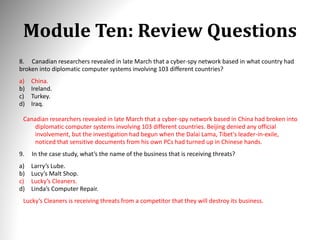
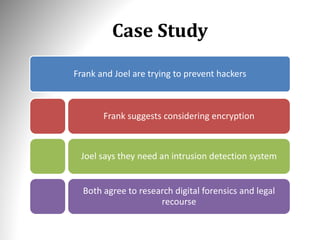
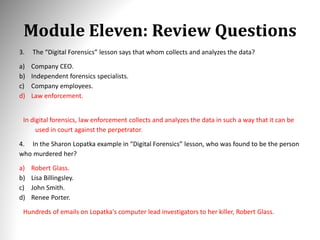
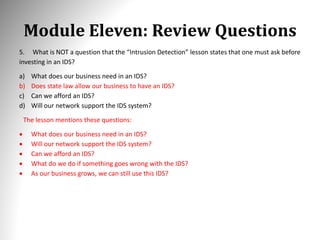
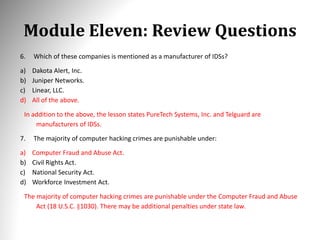
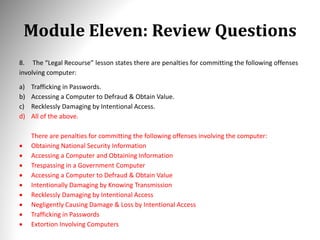
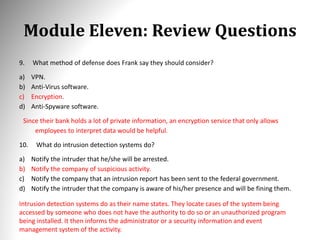
The document outlines the fundamentals of cybersecurity, emphasizing the importance of protecting information systems from cyber threats, including malware and various types of hackers. It covers key concepts such as the nature of cyberspace, types of malware (e.g., viruses, spyware, trojans), and the necessity for organizations to implement security measures to prevent breaches and ensure data integrity. Additionally, it discusses real-life case studies and the impact of cyberattacks on businesses, stressing the need for strong passwords and awareness of phishing scams.