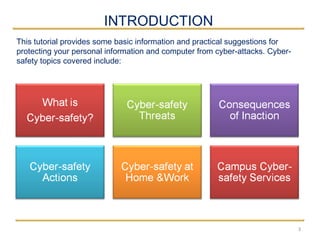
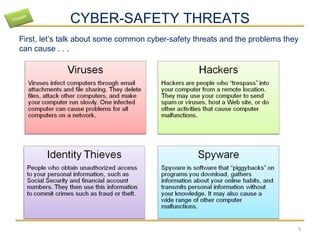
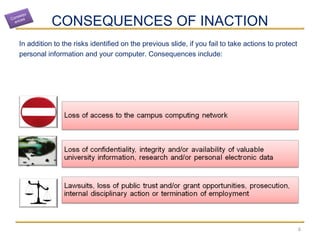
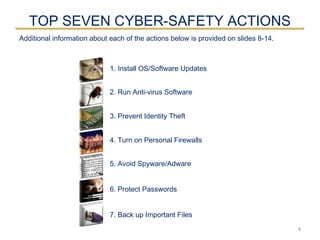
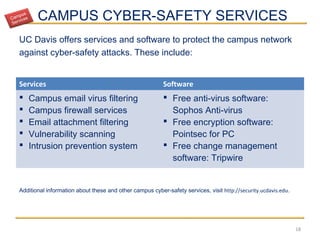
This document provides an overview of basic cyber safety practices. It discusses seven key actions for protecting personal information and computers: 1) installing operating system and software updates, 2) running anti-virus software, 3) preventing identity theft, 4) turning on personal firewalls, 5) avoiding spyware and adware, 6) protecting passwords, and 7) backing up important files. Implementing all seven of these security measures will protect against many common cyber threats with only a few minutes of effort for each one. The document also outlines some cyber safety risks and consequences of inaction, as well as cyber safety best practices for home, work, and on campus.