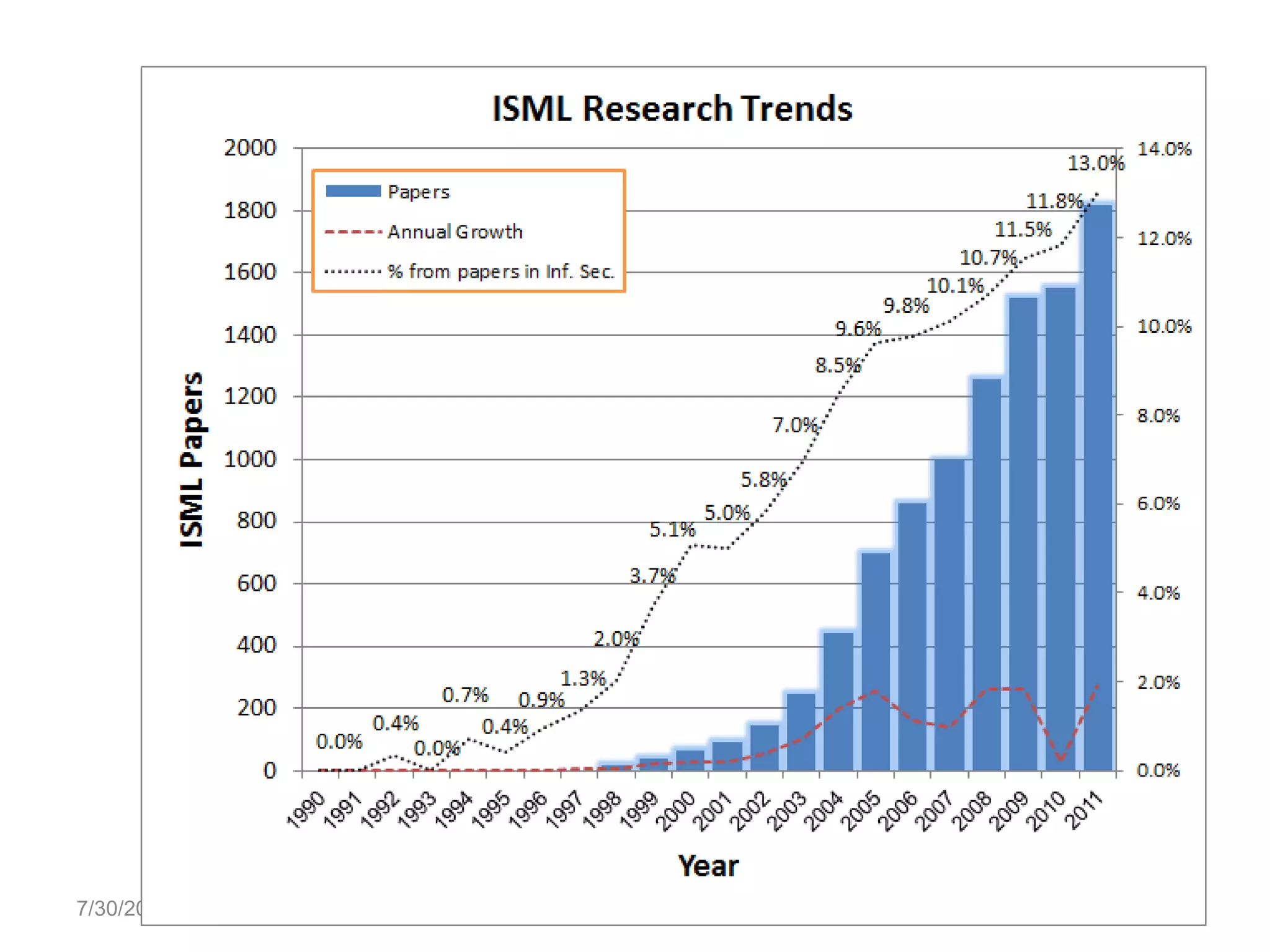
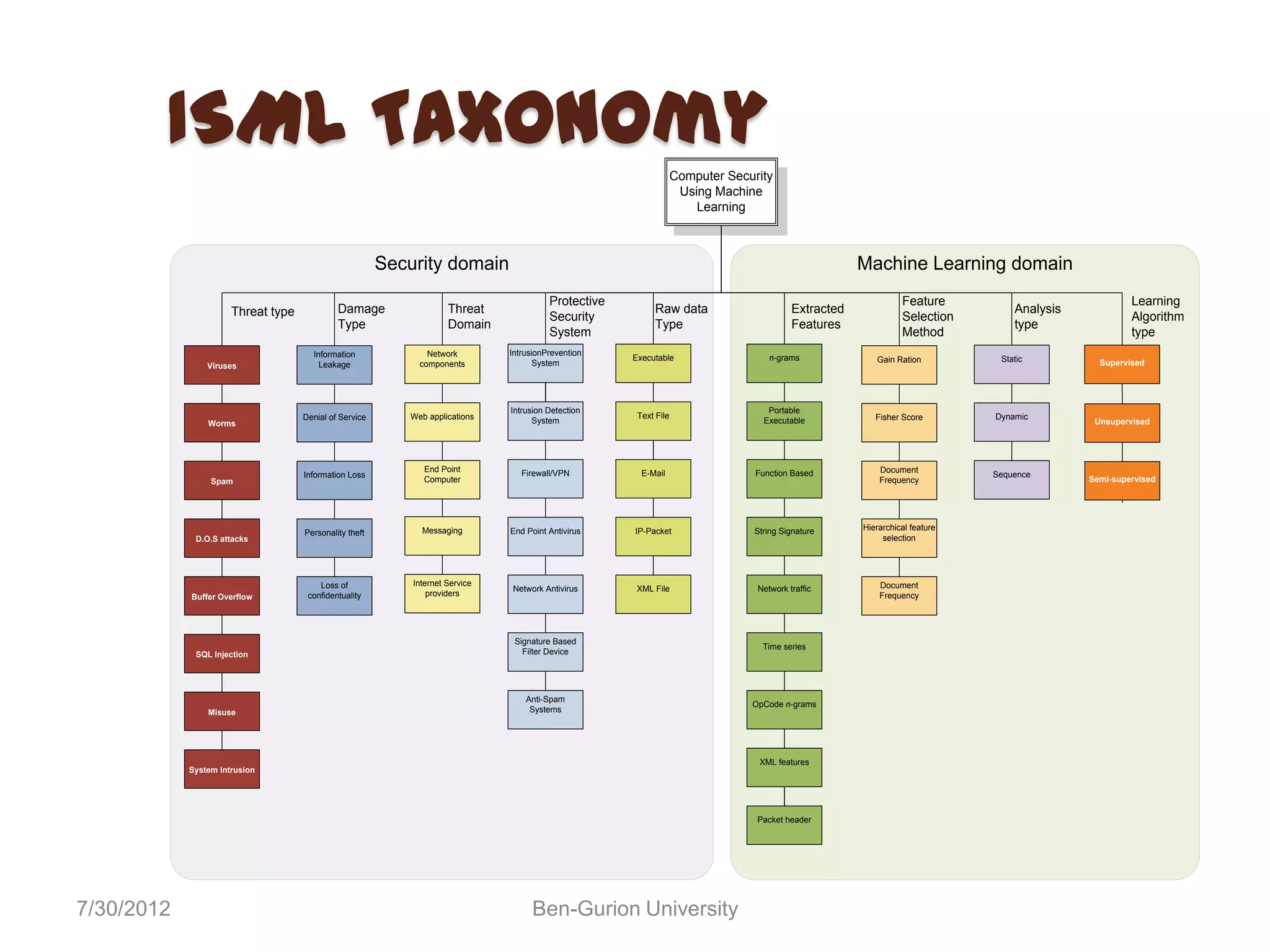
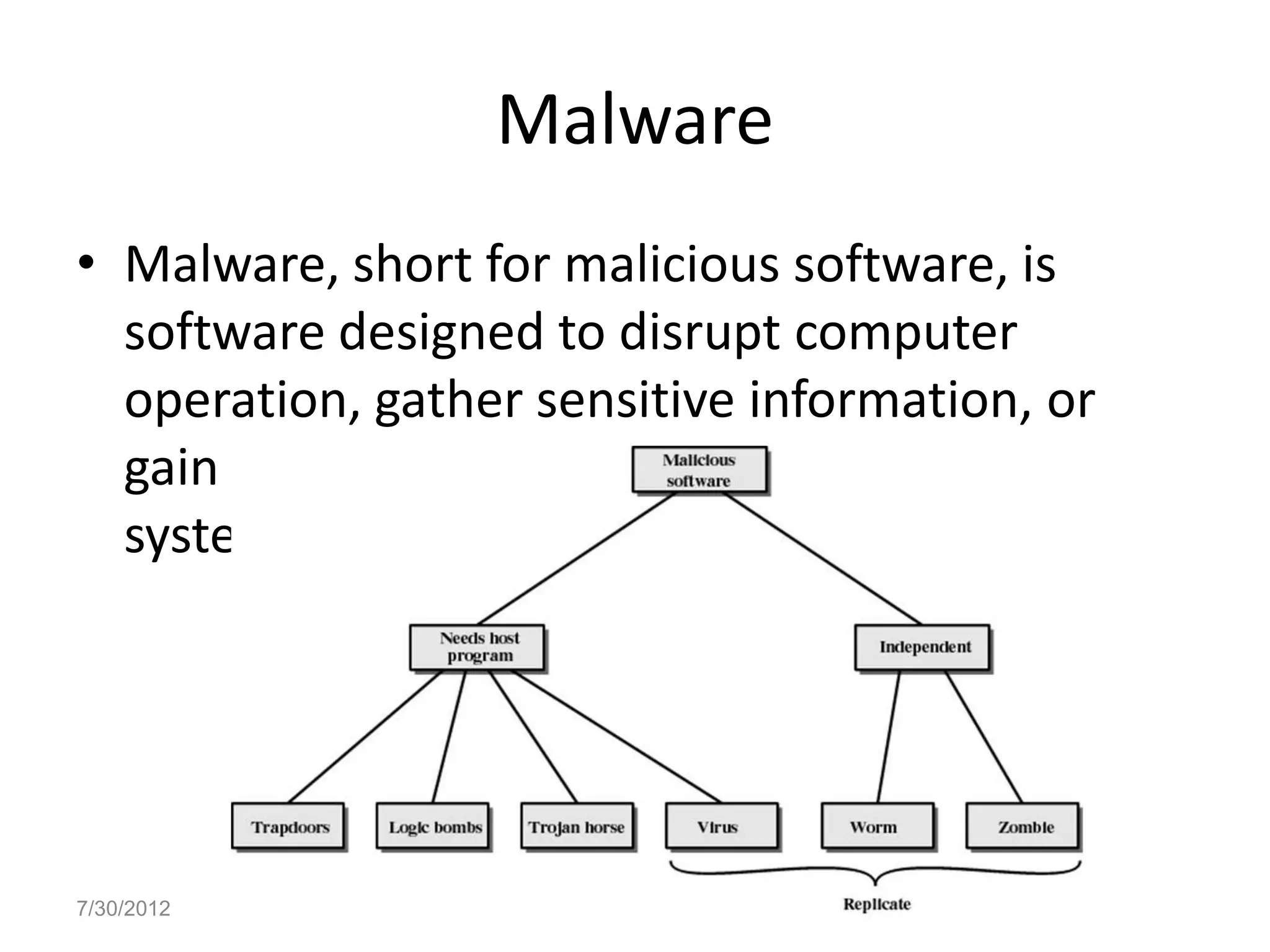
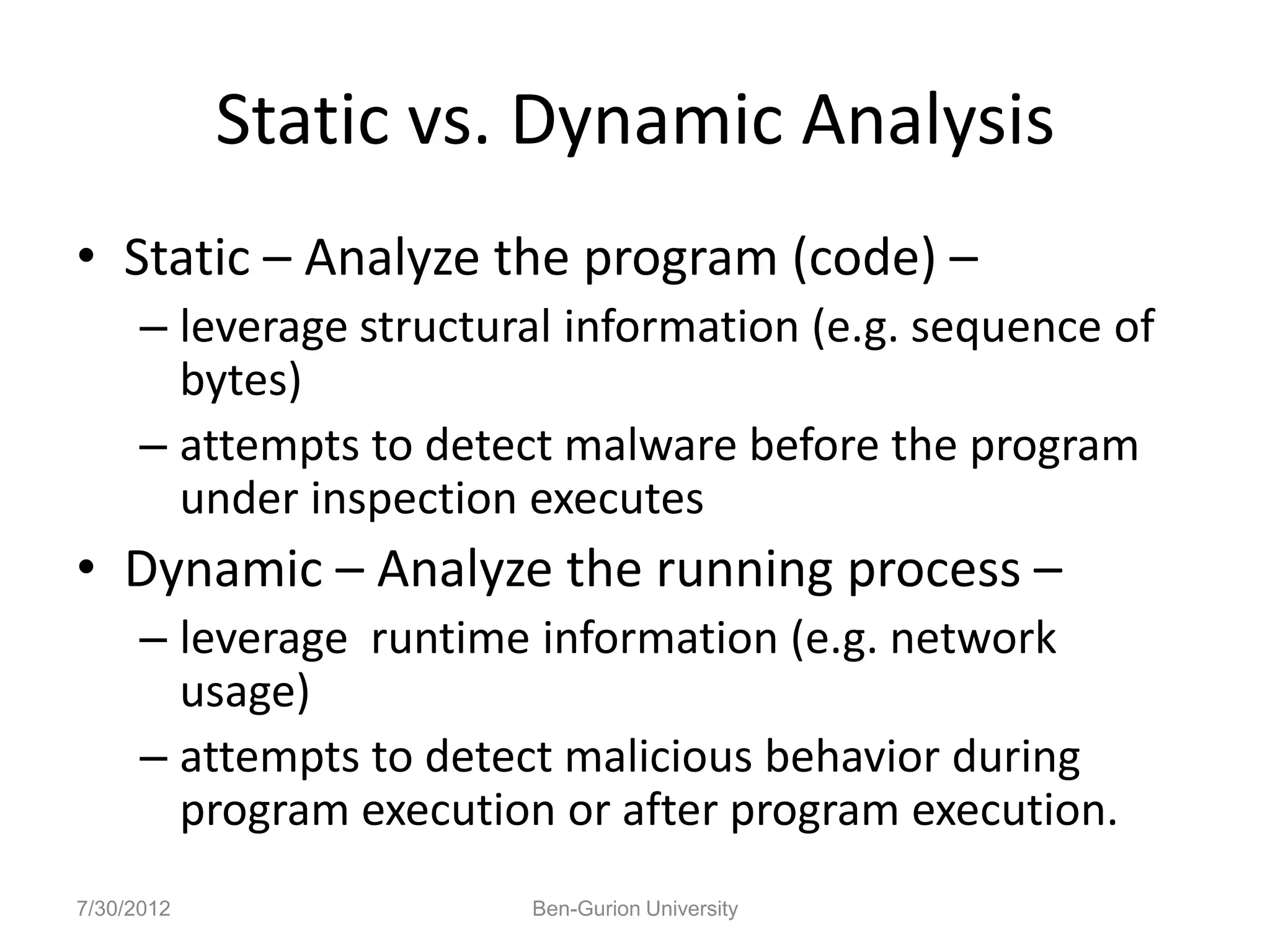
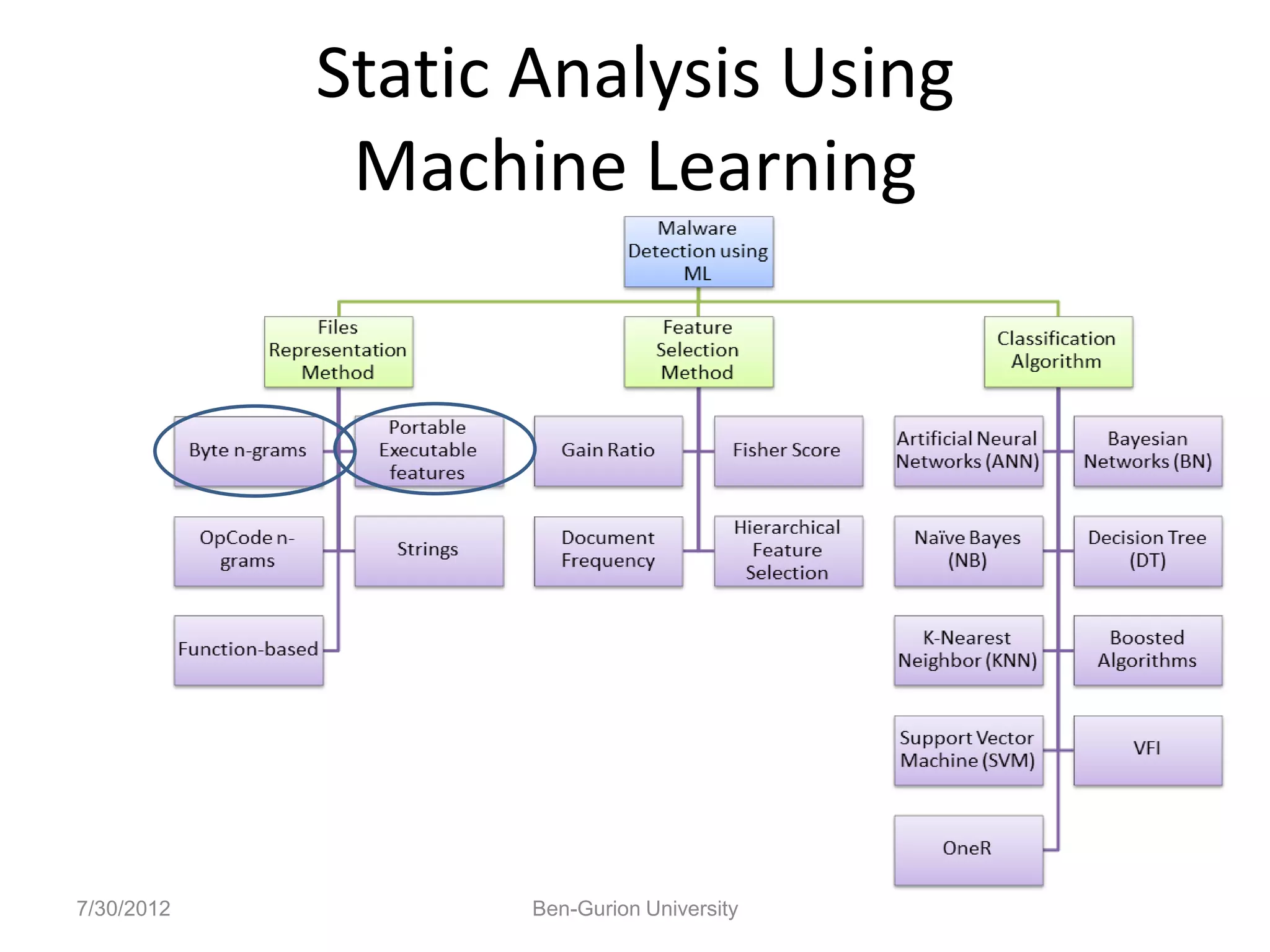
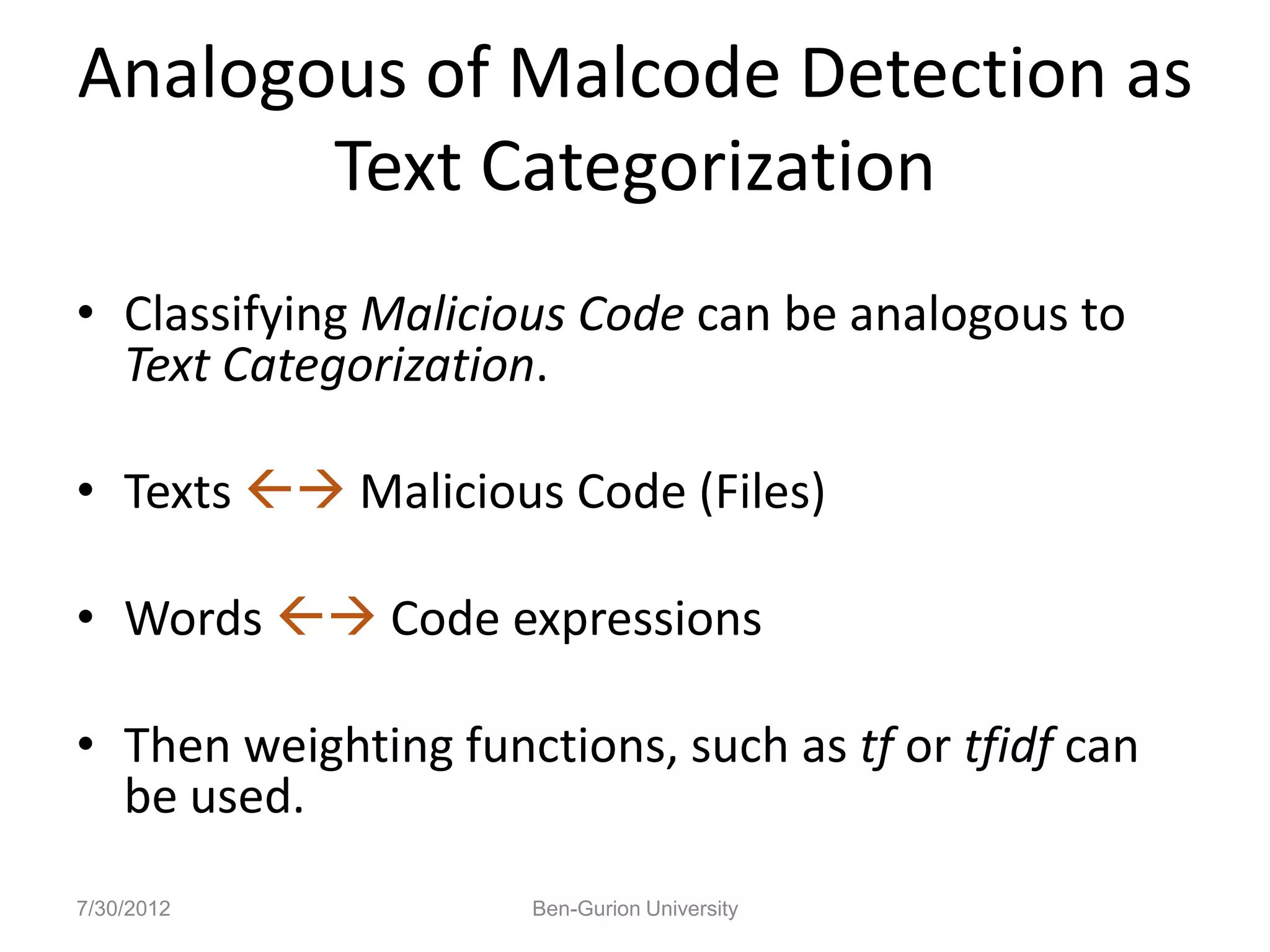
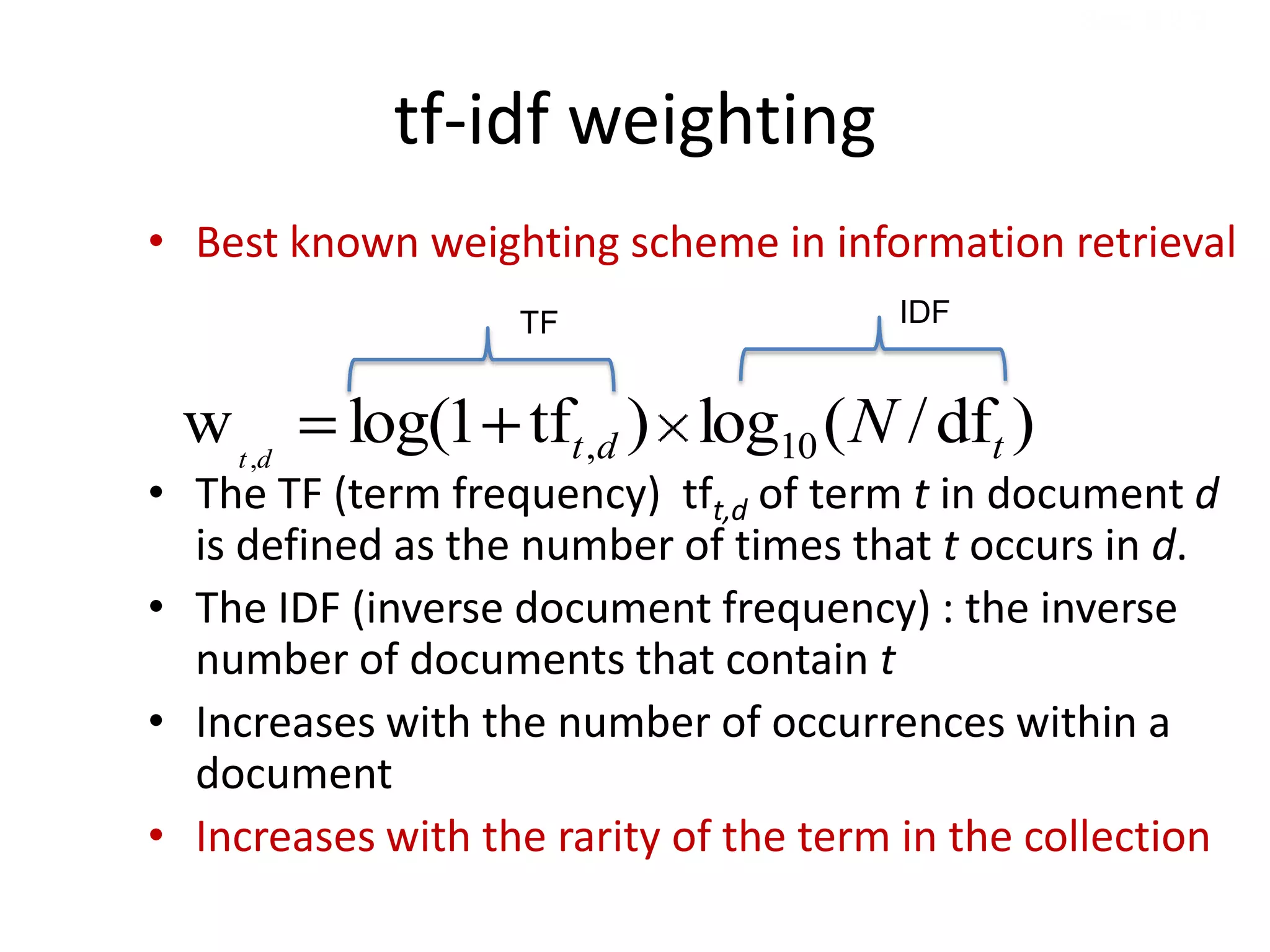
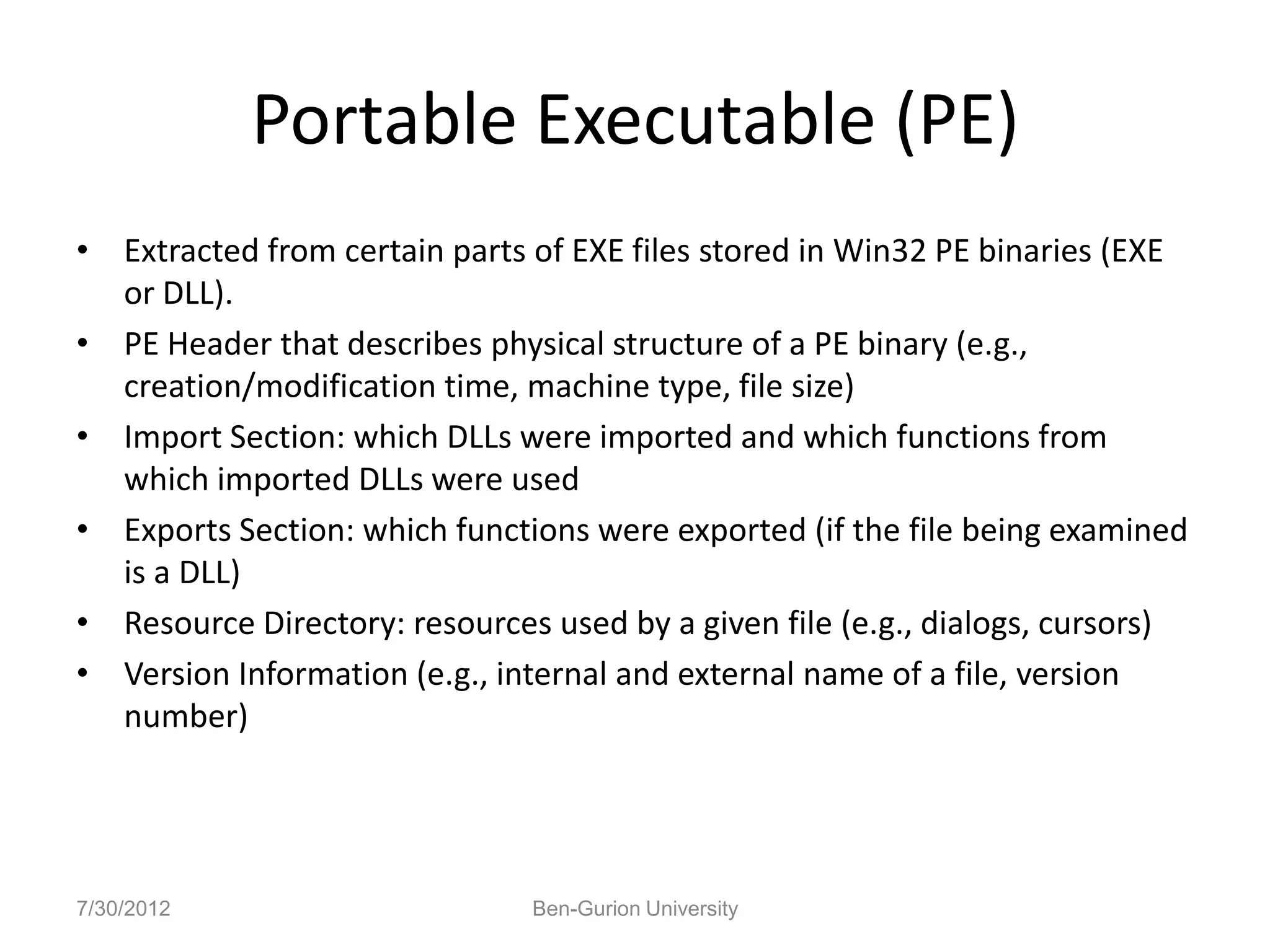
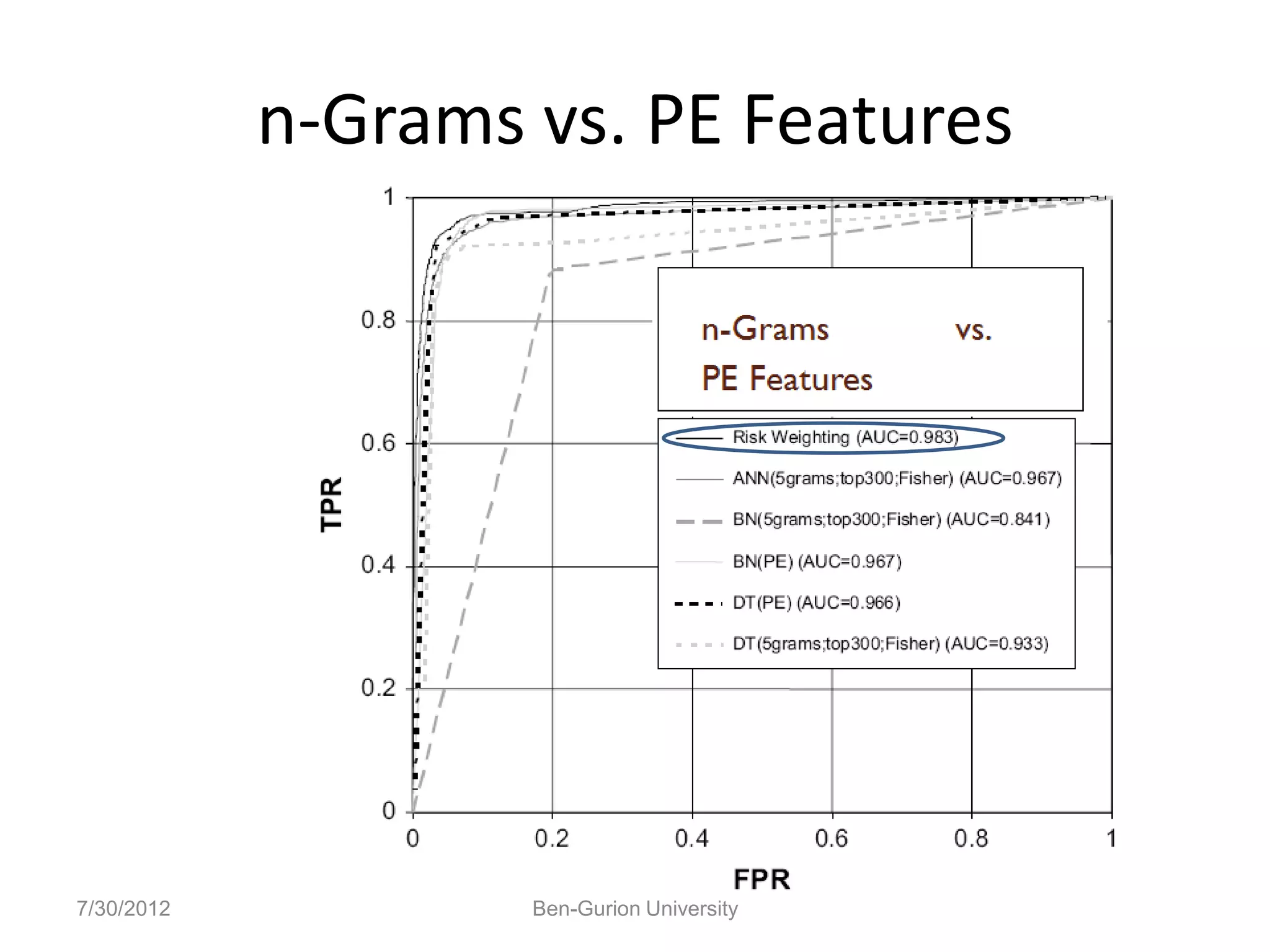
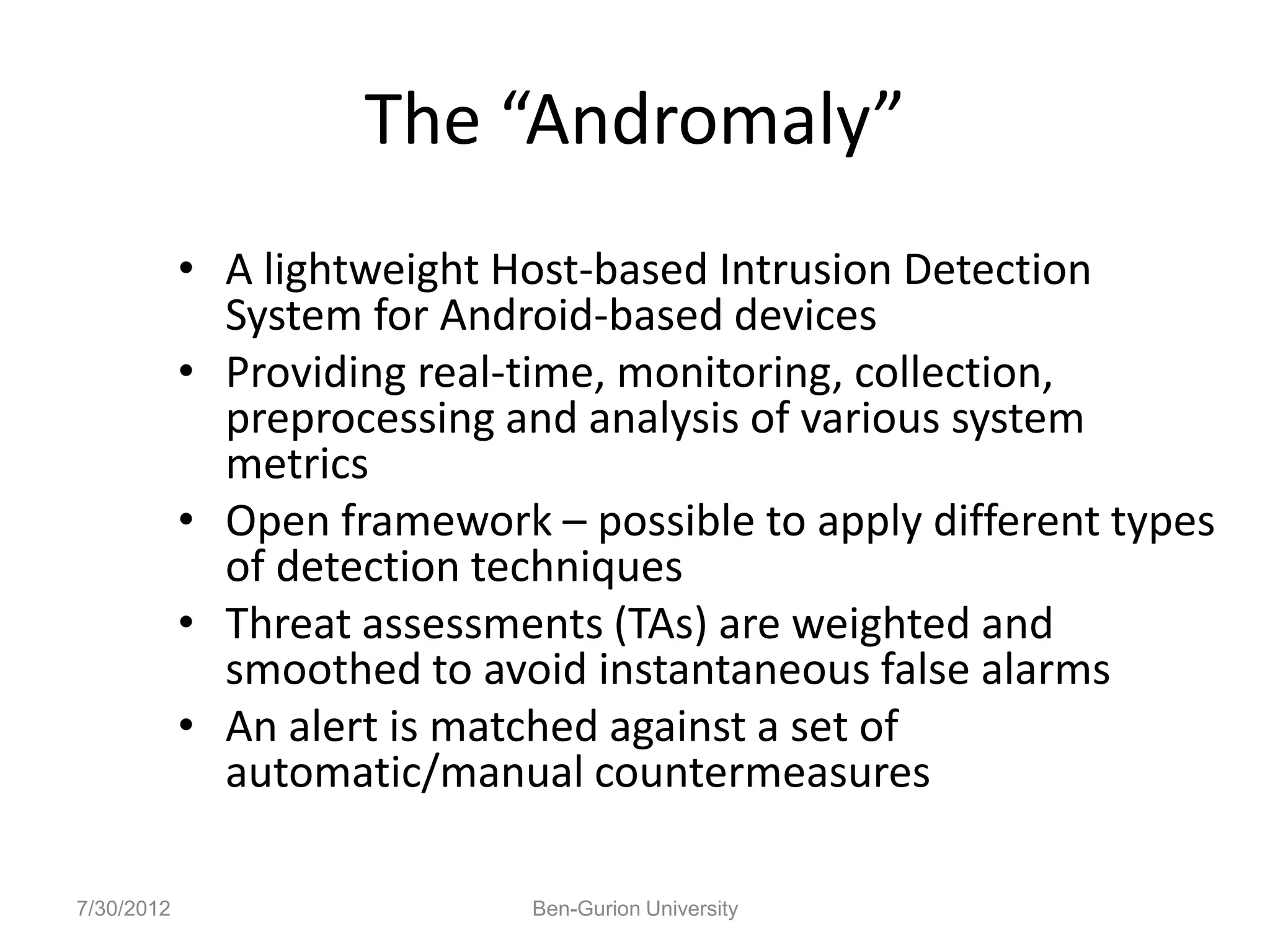
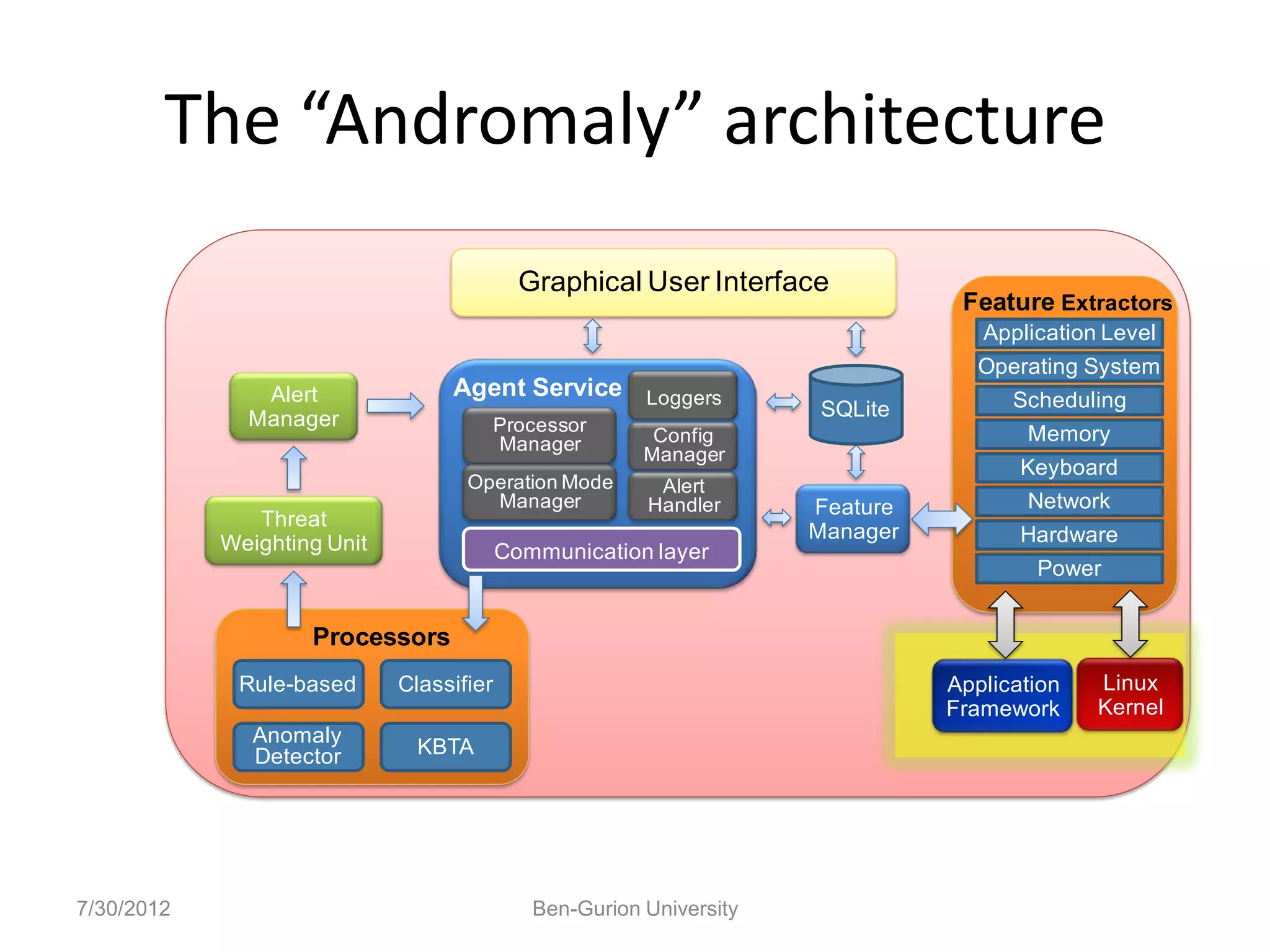
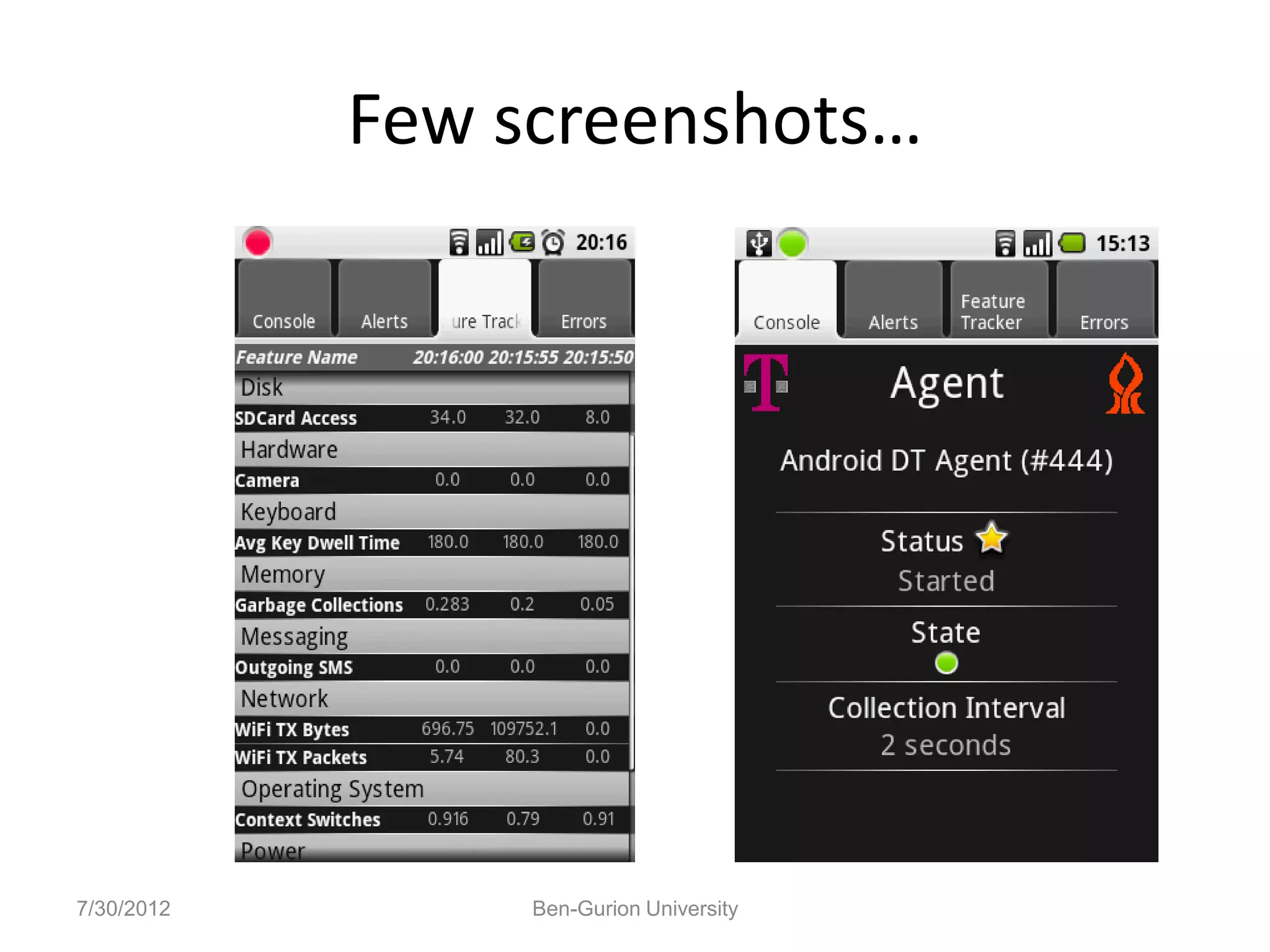
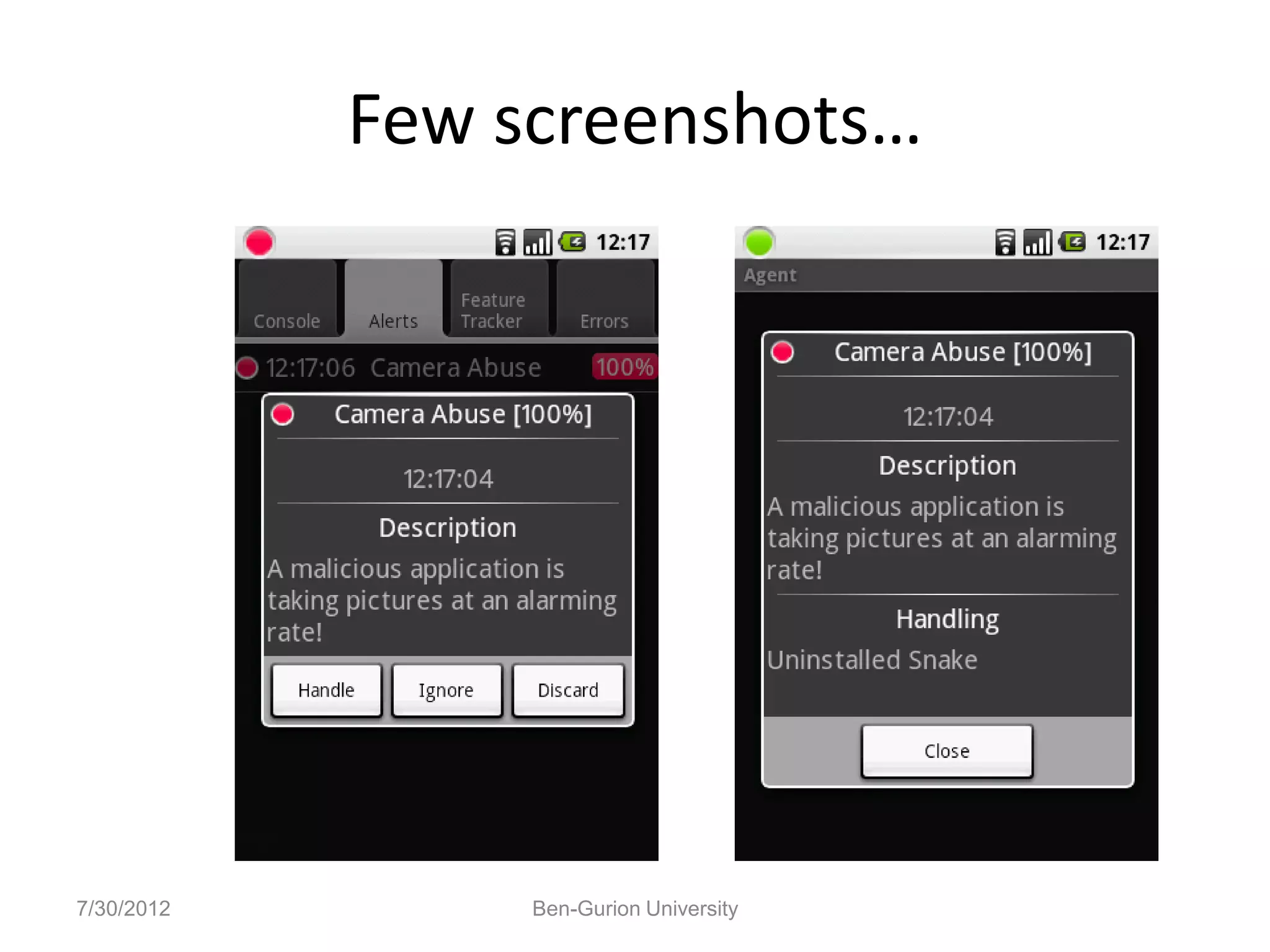
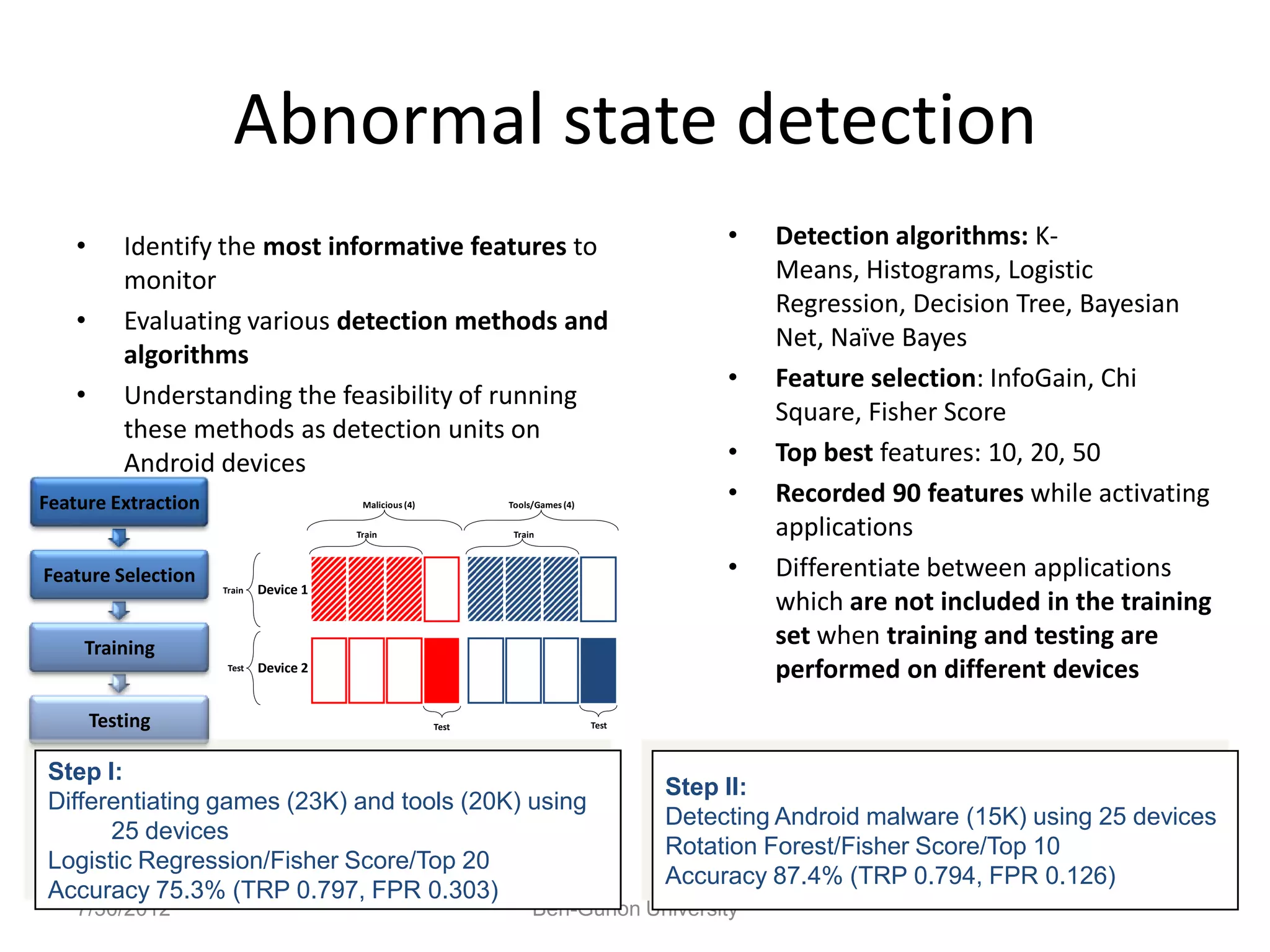
This document discusses machine learning approaches for cyber security, specifically malware detection. It begins with an introduction to cyber security and machine learning. It then discusses using machine learning for malware detection, including analyzing files through static and dynamic analysis. The document outlines extracting features from files and using text categorization approaches. It evaluates various machine learning classifiers and features for malware detection. Finally, it discusses applying these techniques on Android devices for abnormal state detection.


![HoneyGen
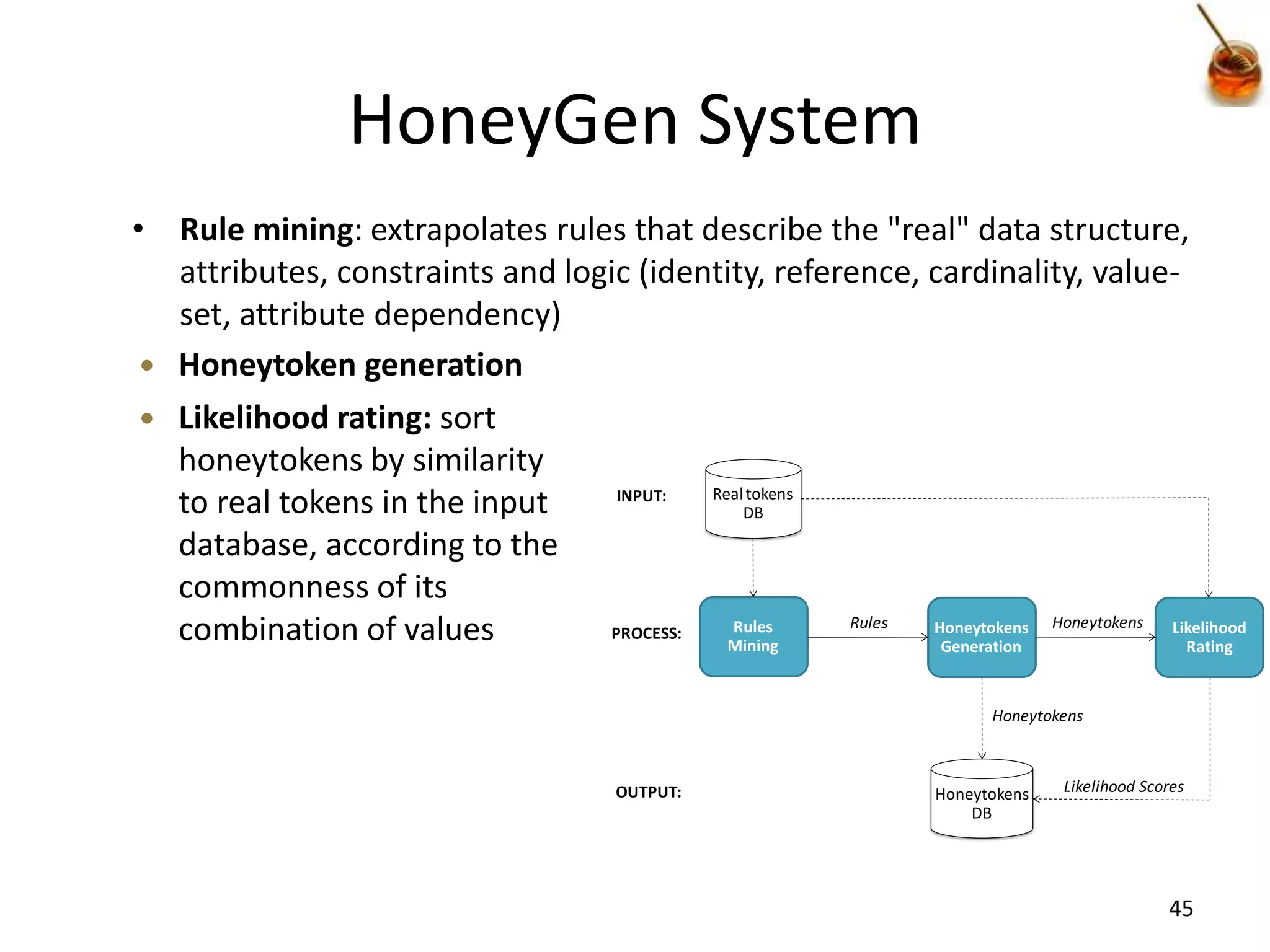
• Challenge: A good honeytoken is an artificial
data item that is hard to distinguish between
real tokens and the honeytoken
• HoneyGen: an Automated Honeytokens
Generator [Berkovitch, 2011]
– Proposed a generic method for honeytokens
generation that given any database will be able to
generate high quality honeytokens
44](https://image.slidesharecdn.com/cybersecurityshort-120730214759-phpapp02/75/When-Cyber-Security-Meets-Machine-Learning-44-2048.jpg)