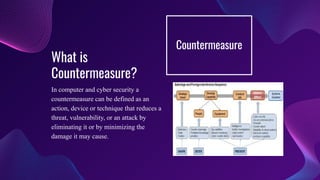
Implications of Misuse & Cyber Security discusses various forms of computer misuse including using stolen credit cards, financial fraud, and vulnerabilities in computer systems. It covers topics like cybersecurity, computer system vulnerabilities, threats like spyware, hackers and viruses. It also discusses countermeasures to prevent threats like strong passwords, firewalls, anti-virus software and keeping software updated. Distributed denial of service (DDoS) attacks are explained as attempts to overwhelm networks through large traffic volumes. Internal vulnerabilities include access control issues, malware, and vulnerability scanning. Computer misuse related to cyberbullying can psychologically impact individuals and negatively affect organizations.