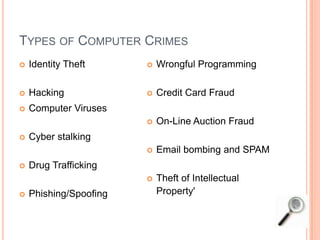
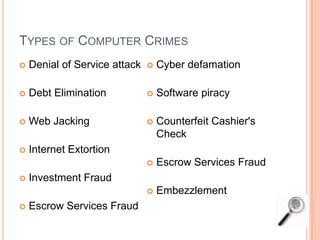
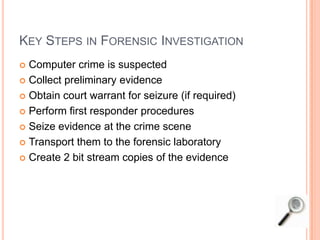
Cyber forensics involves applying scientific methods to digital evidence for legal purposes. It includes preserving, acquiring, analyzing, discovering, documenting, and presenting digital evidence. Common goals are to determine if unauthorized activity or crimes occurred using computer systems and networks. Cyber crimes are growing and can include hacking, cyber stalking, spamming, and intellectual property theft. Forensic investigations follow standard procedures including seizing evidence, making copies, and analyzing to find relevant information for legal cases.