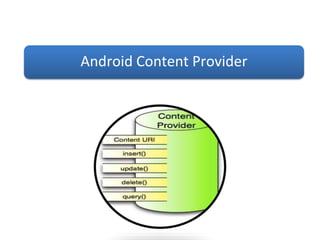
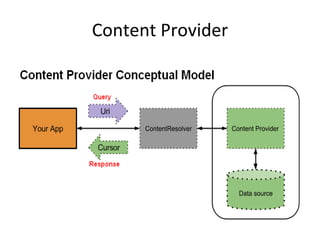
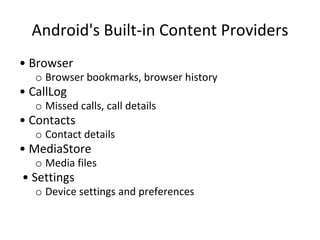
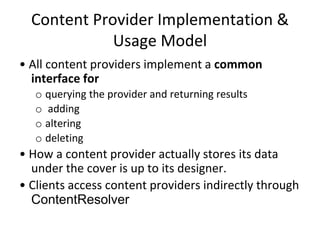
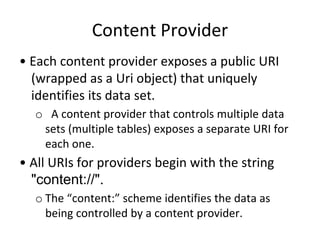
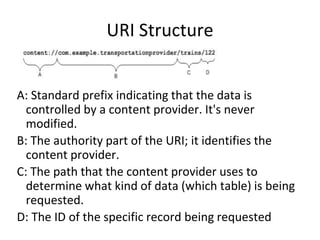
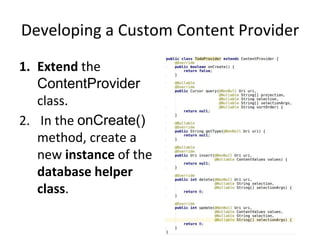
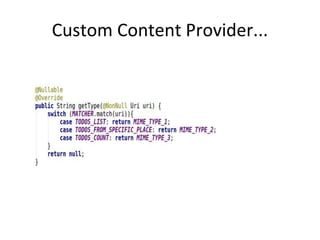
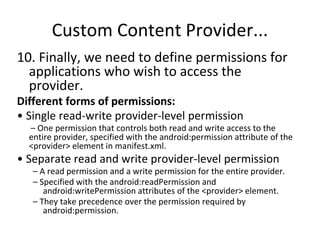
A content provider allows data to be shared across applications. It encapsulates the data and provides methods for querying and modifying the data. There are built-in Android content providers for common data types like contacts, audio, images. A custom content provider can be created by extending the ContentProvider class. It must implement methods like query(), insert(), update(), delete() and return a Uri or number of rows affected. The provider is declared in the manifest and permissions can control access at the provider or URI level.