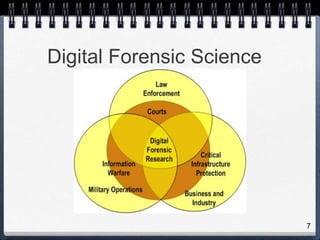
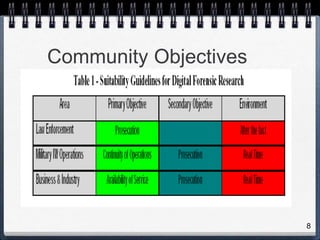
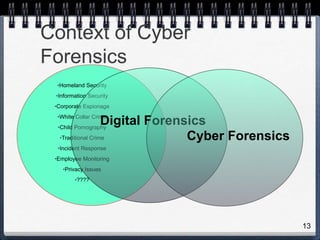
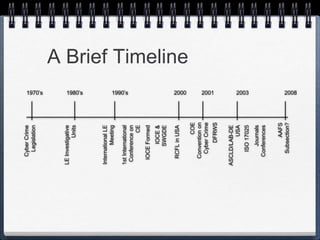
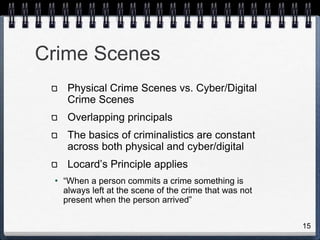
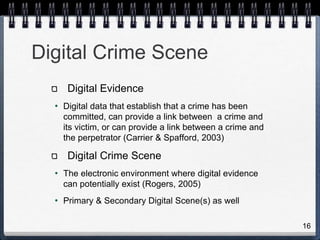
This document provides an introduction to cyber forensics. It discusses the field of digital forensics science and defines it as the use of scientific methods for preserving, collecting, analyzing and presenting digital evidence. It outlines the key communities in digital forensics including law enforcement, military and business/industry. The document also summarizes the basic methodology of cyber forensics which consists of acquiring evidence without altering it, authenticating the evidence and analyzing the data. Finally, it notes that cyber forensics is a maturing field with excellent career opportunities but that proper education and training are important.