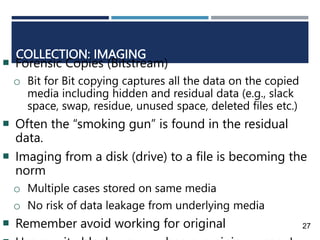
The document discusses the field of digital forensics, including defining digital forensic science, the communities involved, and outlining the process which includes identifying evidence, collecting it while maintaining a chain of custody, examining and analyzing the evidence, and presenting findings in a report. It also covers some challenges in the field like a lack of standards and certification as well as career opportunities in digital forensics.