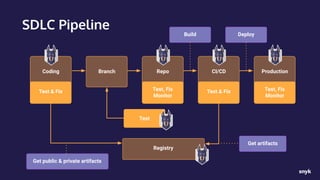
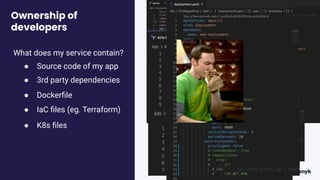
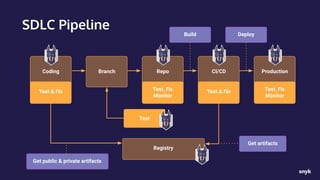
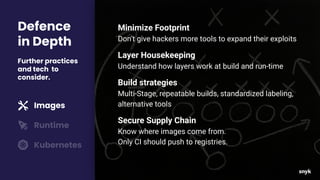
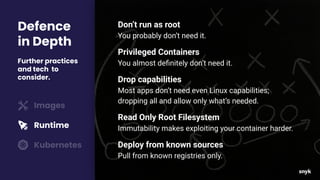
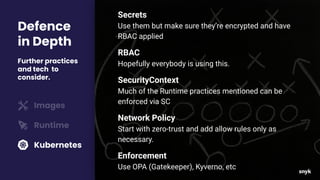
The document discusses why container security is important for developers. It notes that containers add security concerns at the operating system level that were previously handled by other teams. This increases developers' scope of responsibility while they are also expected to maintain pipeline velocity. It demonstrates how to integrate security checks into the development workflow without slowing down developers. It advocates for implementing known secure practices for building and running containers to mitigate vulnerabilities and adopting a defense-in-depth approach.