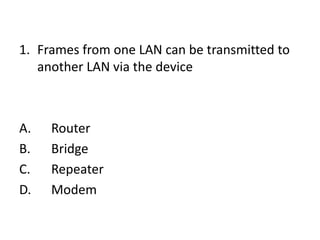
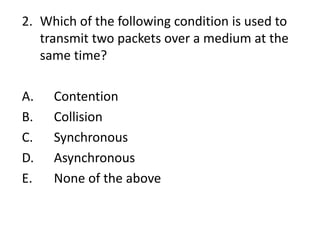
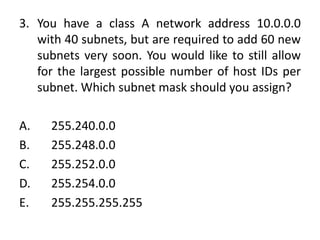
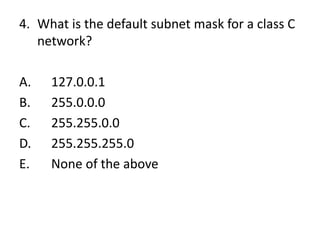
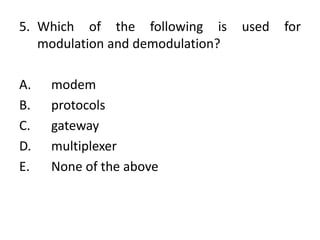
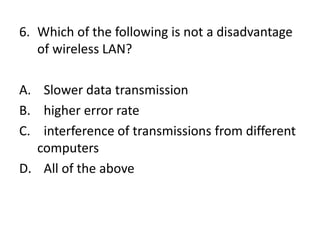
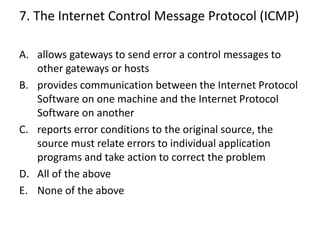
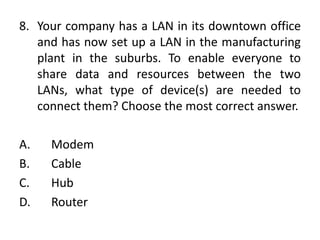
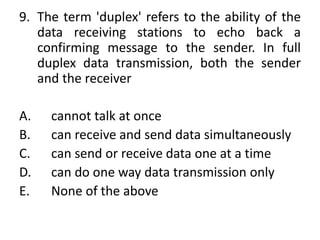
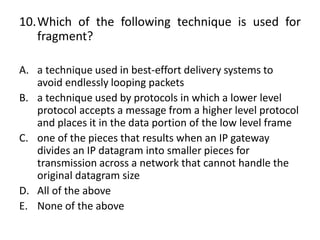
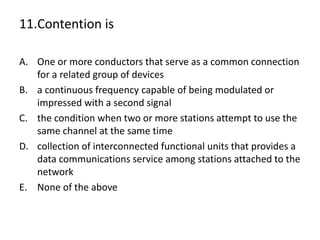
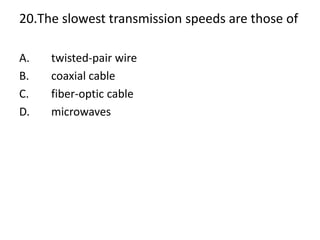
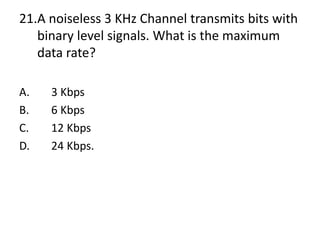
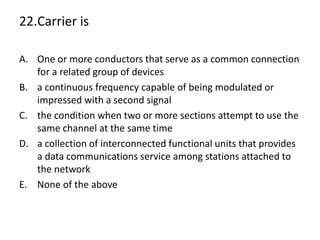
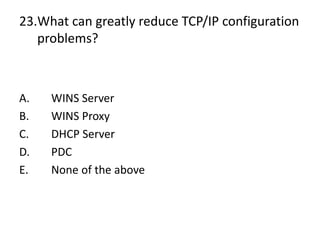
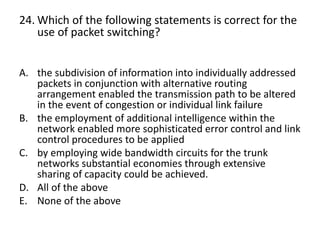
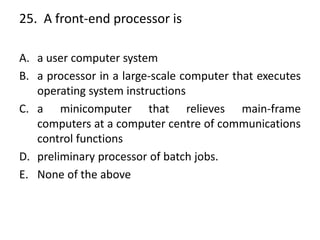
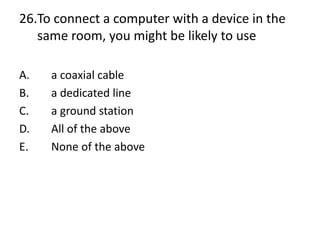
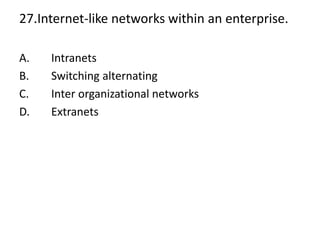
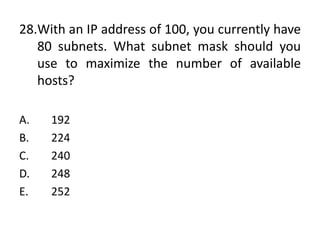
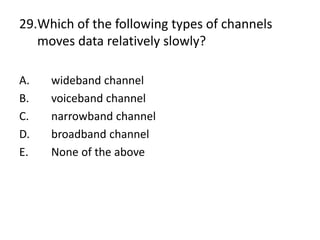
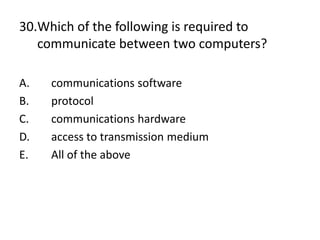
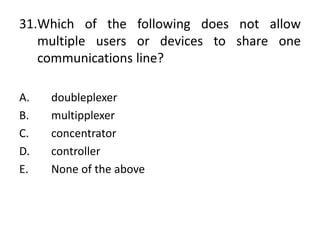
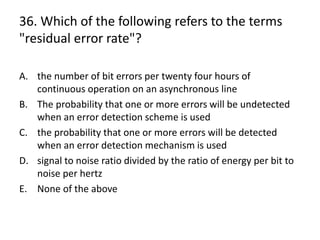
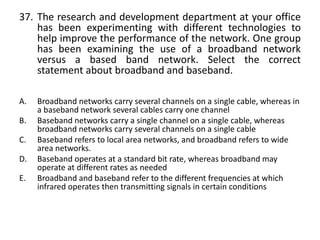
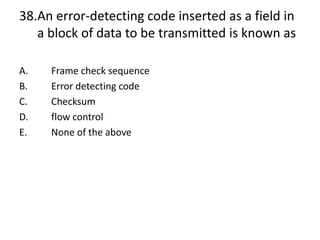
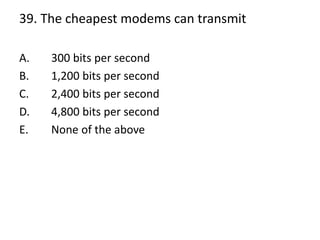
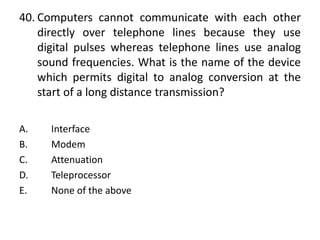
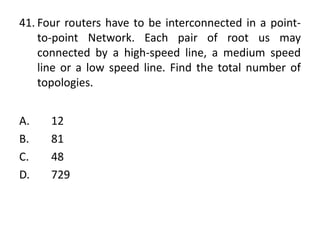
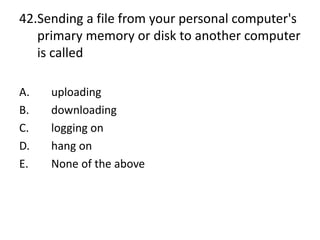
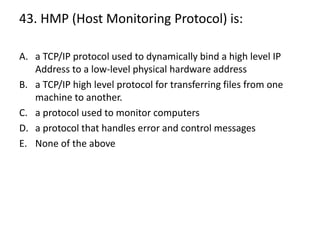
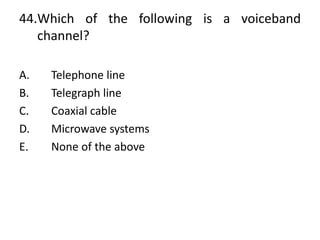
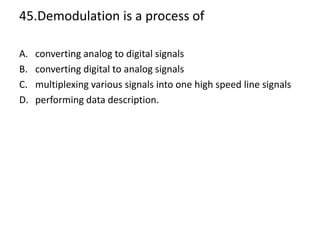
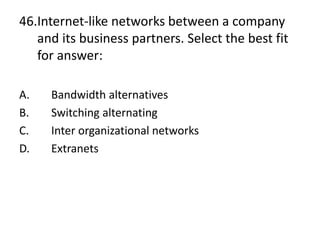
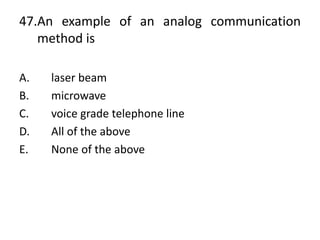
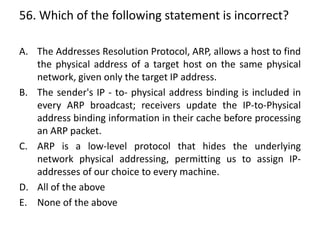
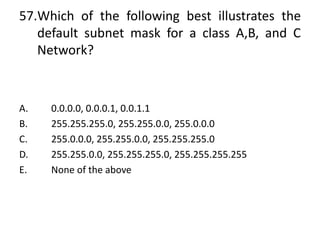
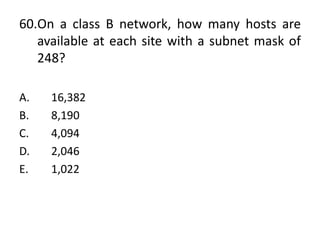
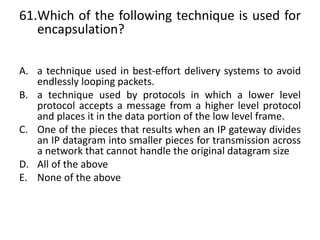
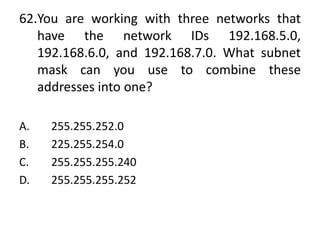
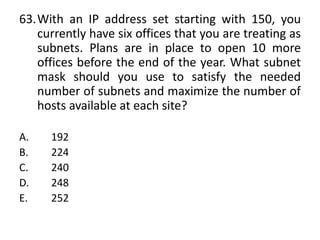
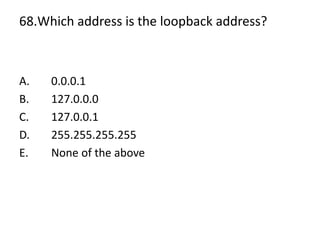
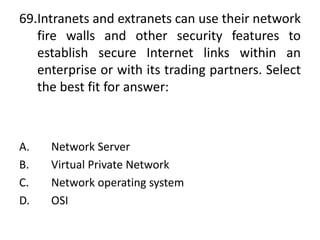
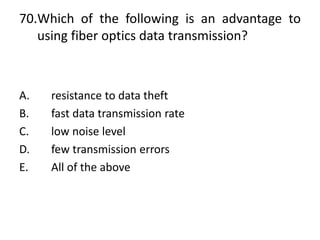
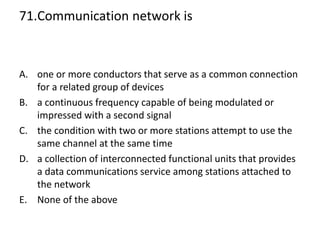
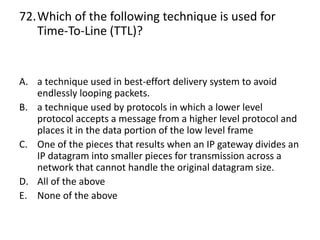
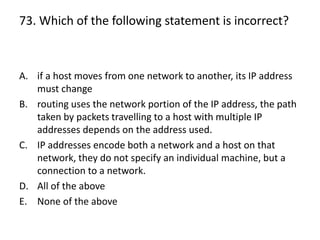
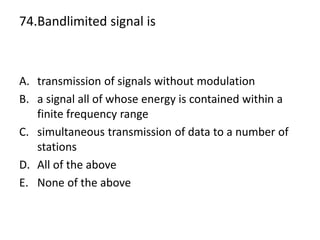
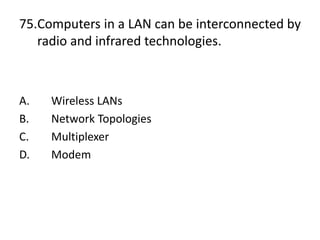
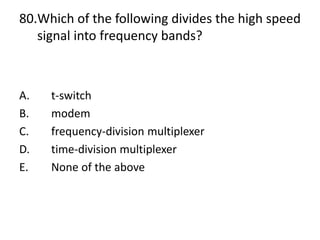
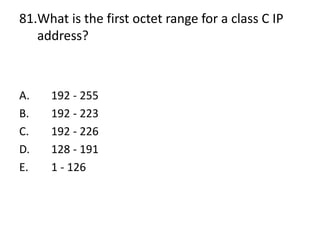
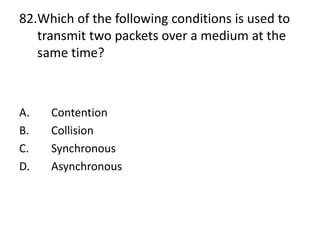
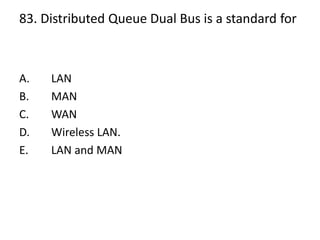
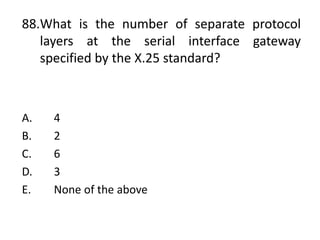
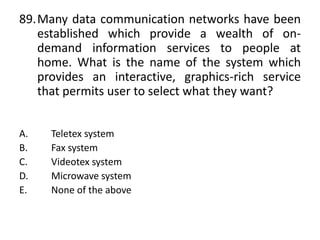
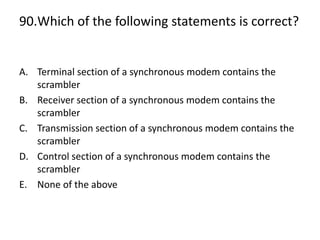
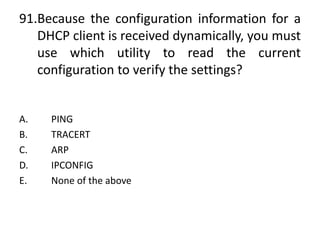
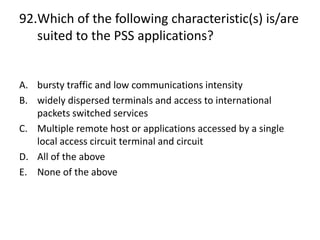
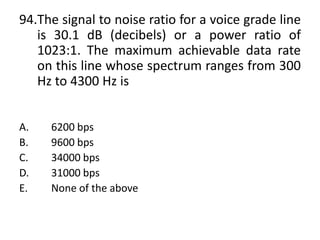
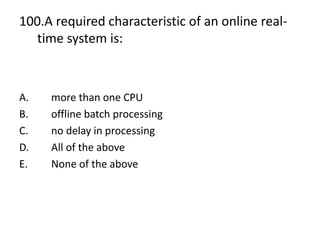
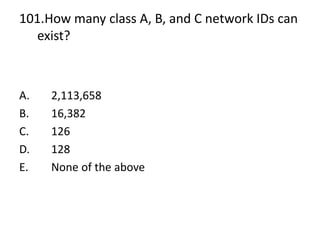
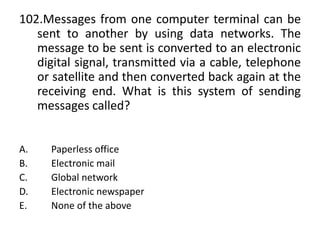
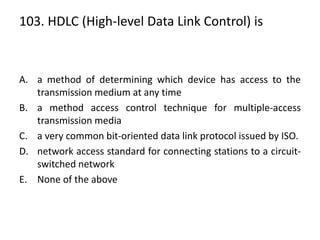
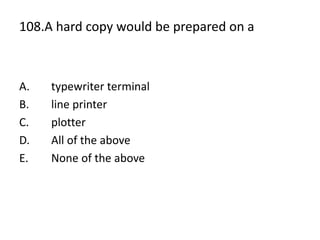
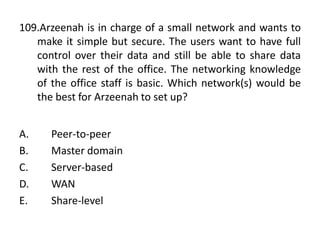
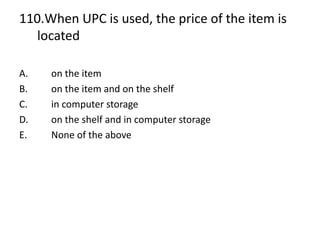
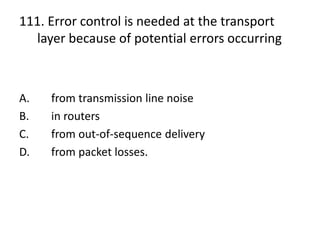
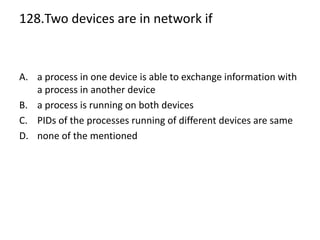
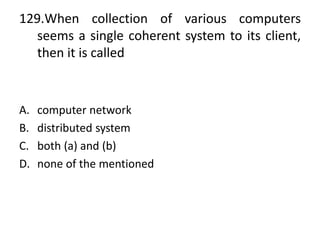
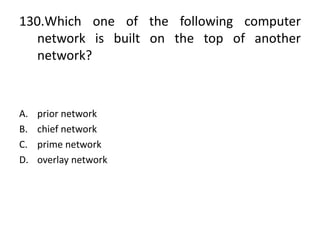
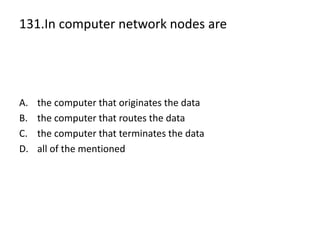
The document presents a series of multiple-choice questions related to computer networking topics, including LANs, subnetting, TCP/IP protocols, and modulation techniques. It covers concepts such as network devices, data communication methods, and various network protocols. The questions are designed to assess understanding and knowledge in computer networking principles and practices.