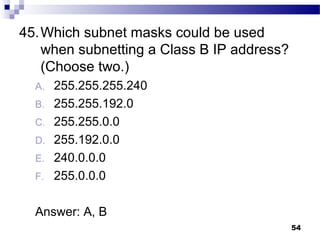
Here are the key steps to determine the subnet that this IP address belongs to:
1. The IP address is 172.16.192.166
2. A Class B address has a network portion of 172.16
3. Therefore, the network portion is 172.16
4. The remaining bits must be the host portion
5. Therefore, the subnet that this IP address belongs to is 172.16.0.0
The IP address 172.16.192.166 belongs to the 172.16.0.0 subnet.