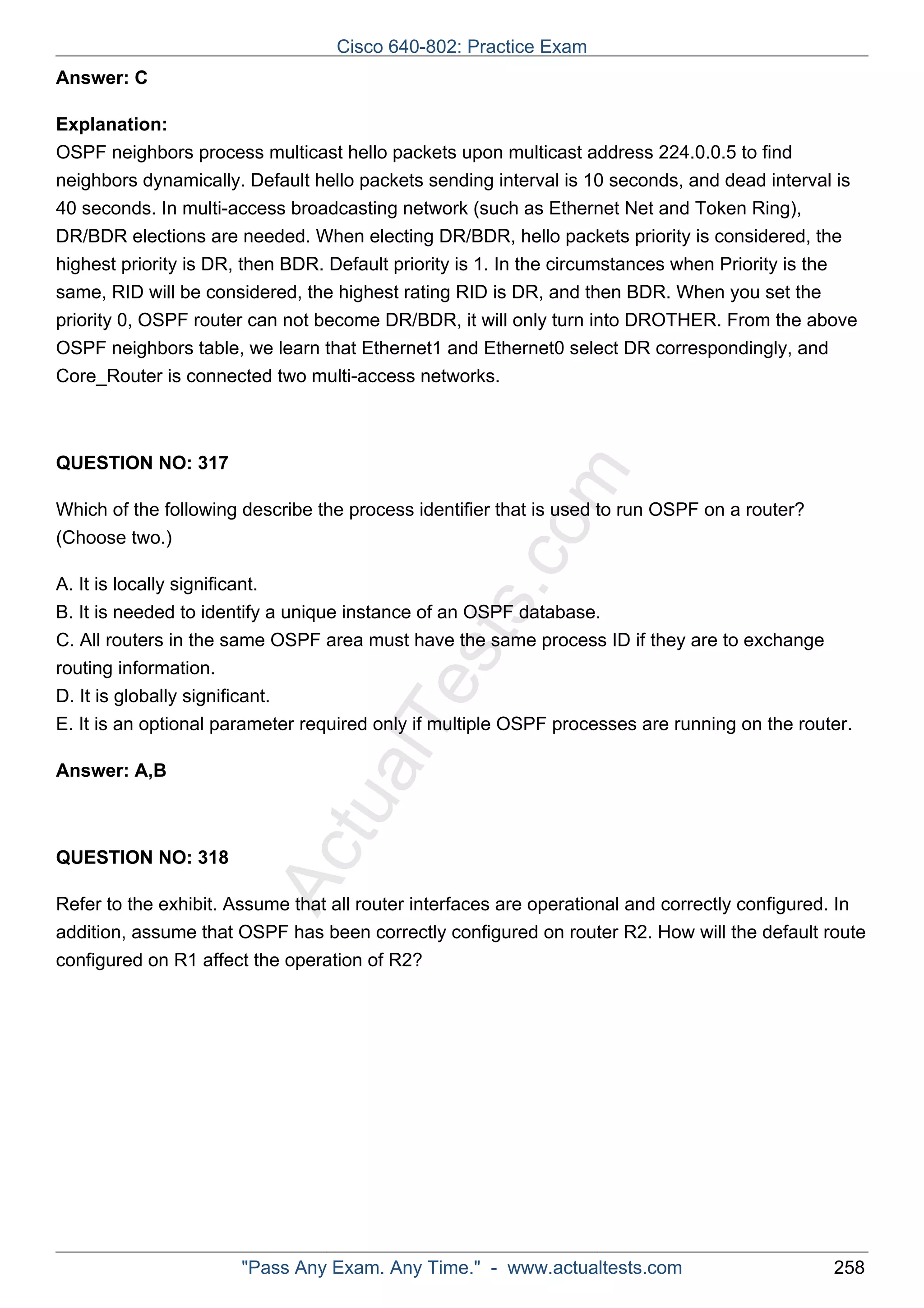
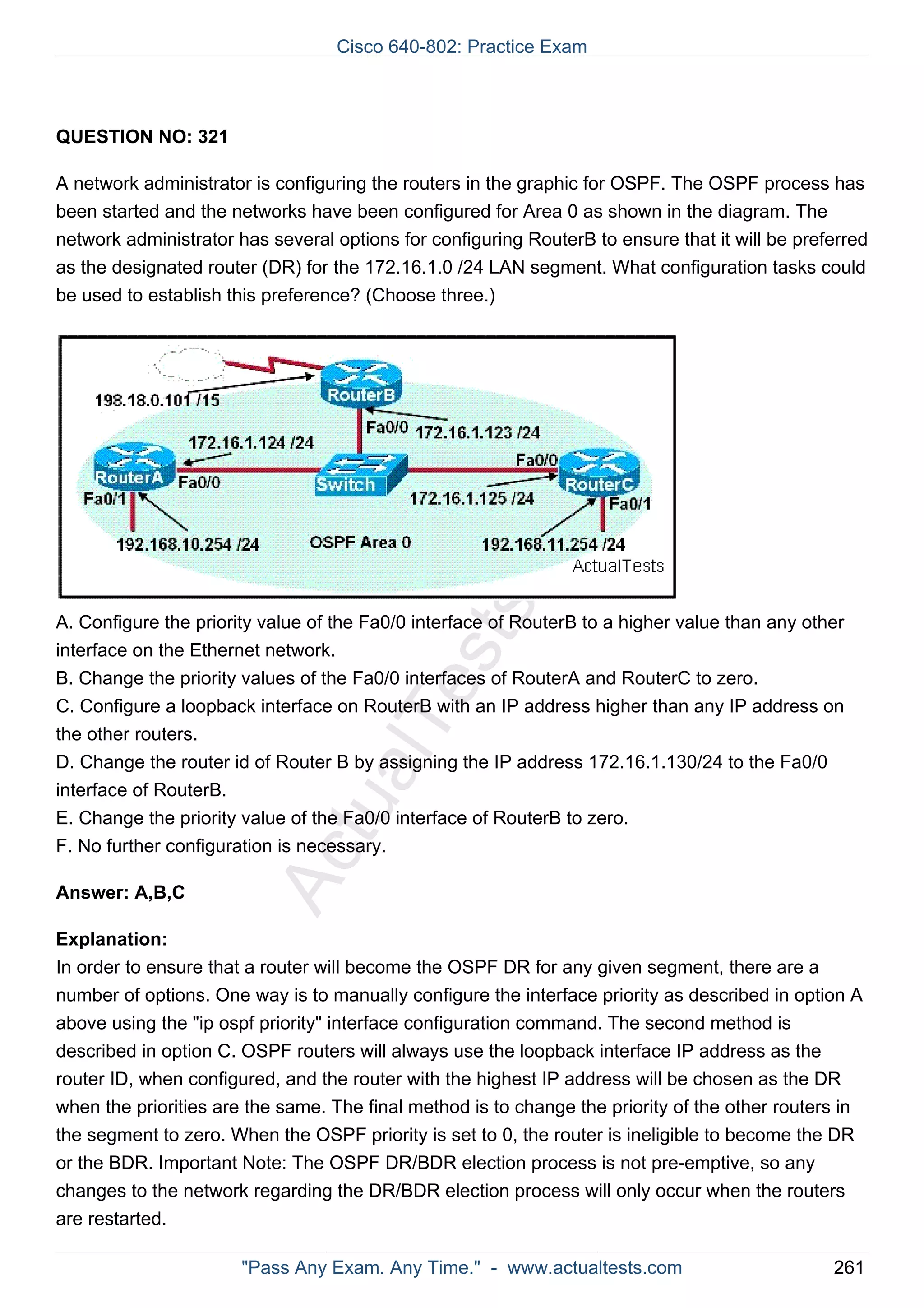
This document contains a practice exam for Cisco's 640-802 CCNA certification. It includes 10 multiple choice questions testing knowledge of networking concepts like the functions of routers, differences between switches and hubs, and network addressing. Correct answers are provided along with explanations of the concepts being tested.



































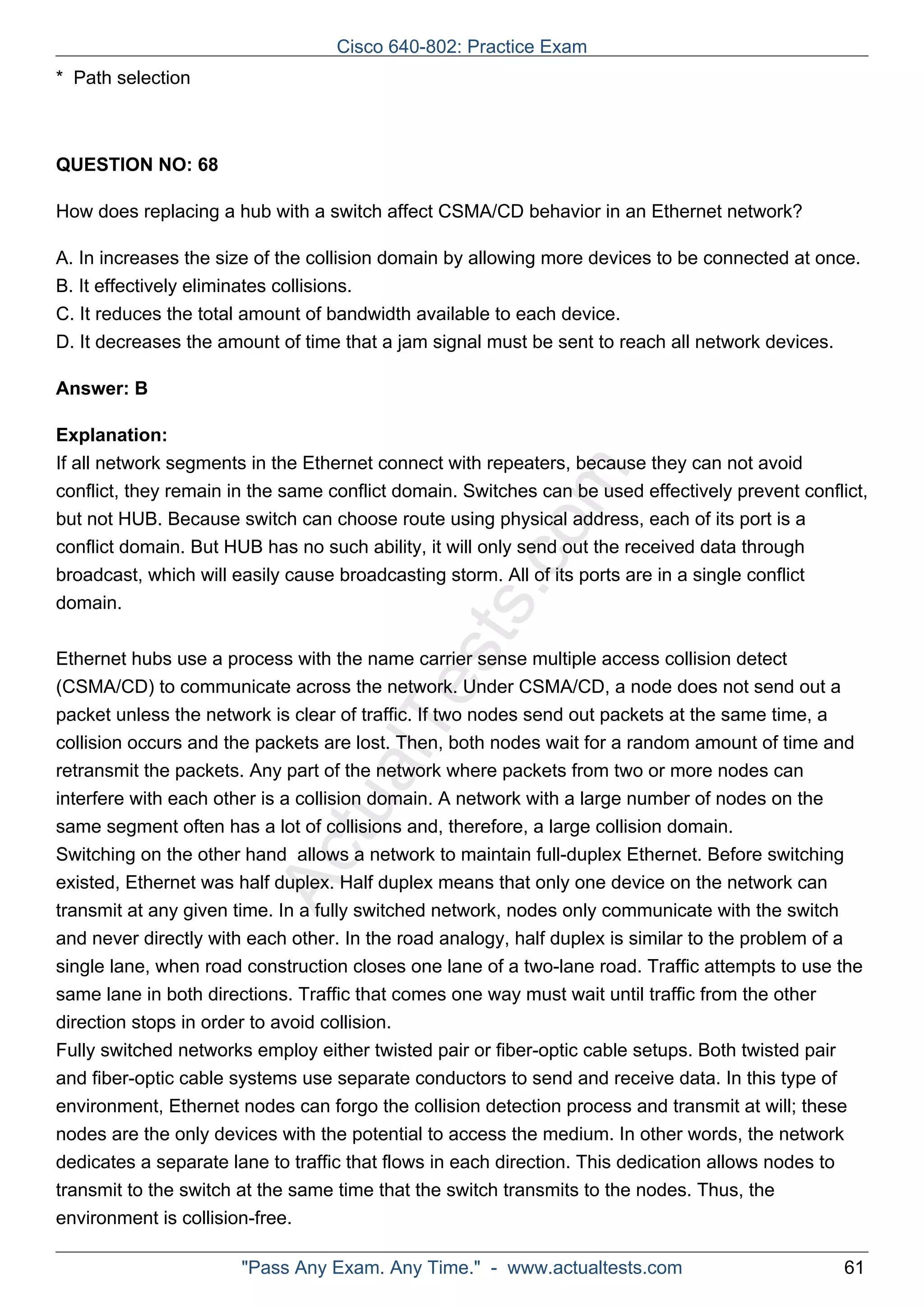






![4. Configure vlan, interface vlan 1 may be used to configure details in vlan
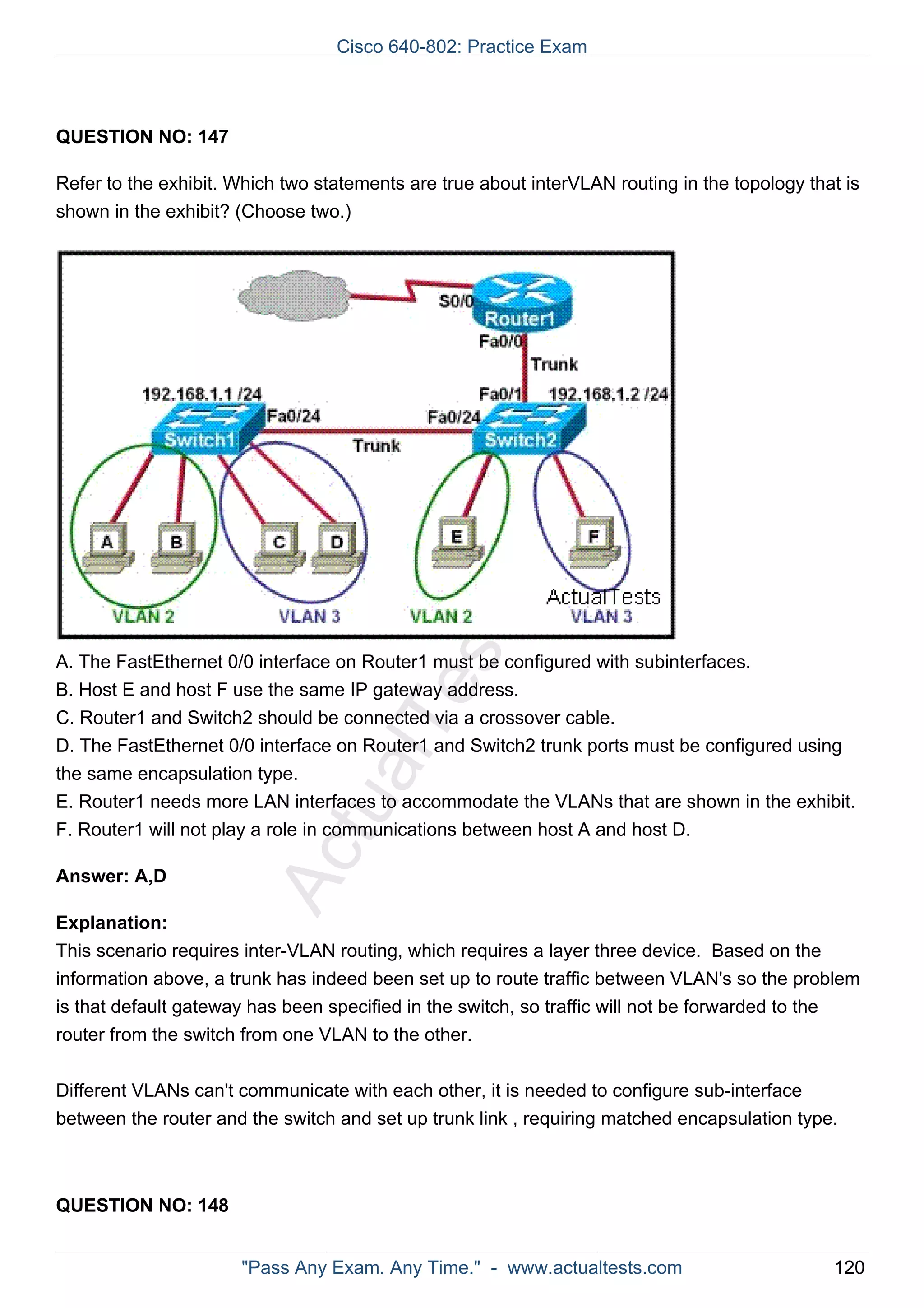
5. Input no shutdown under interface configure mode to activate interface
6. Use command ip address to configure IP address, and sets the switch management
7. Use command ip default-gateway to configure default gateway
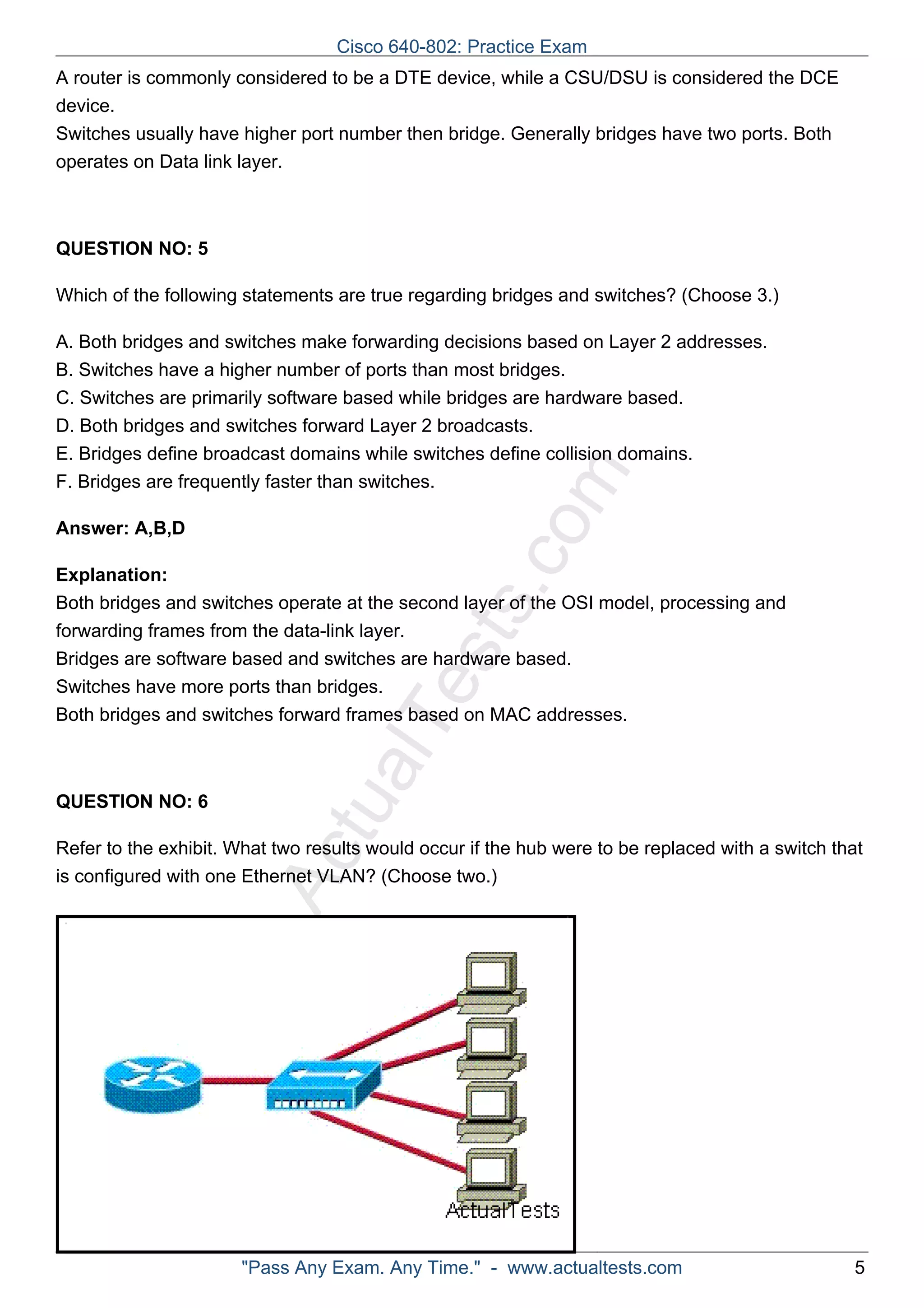
ActualTests.com
QUESTION NO: 77
The system LED is amber on a Cisco Catalyst 2950 series switch. What does this indicate?
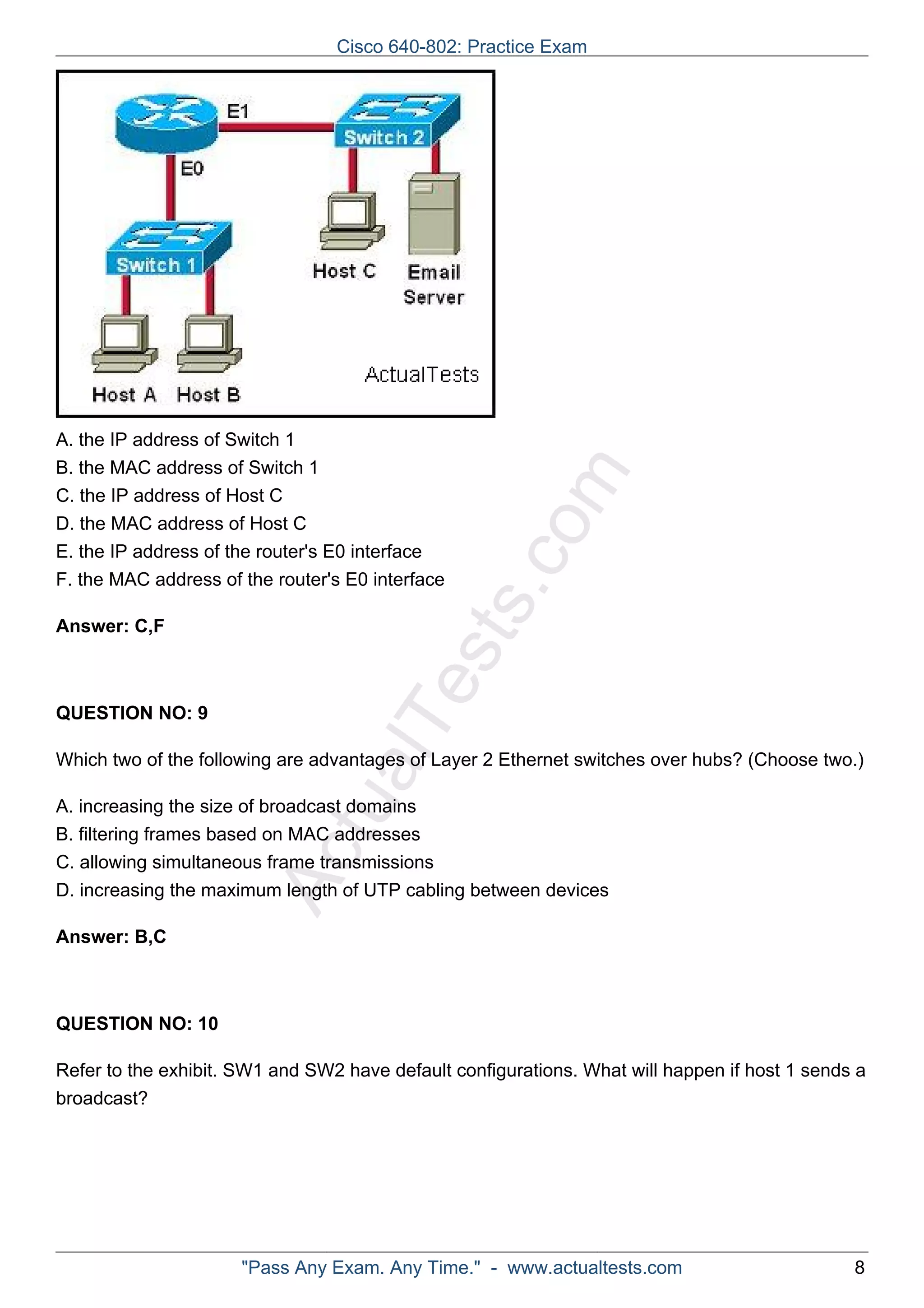
A. The system is powered up and operational.
B. The system is forwarding traffic.
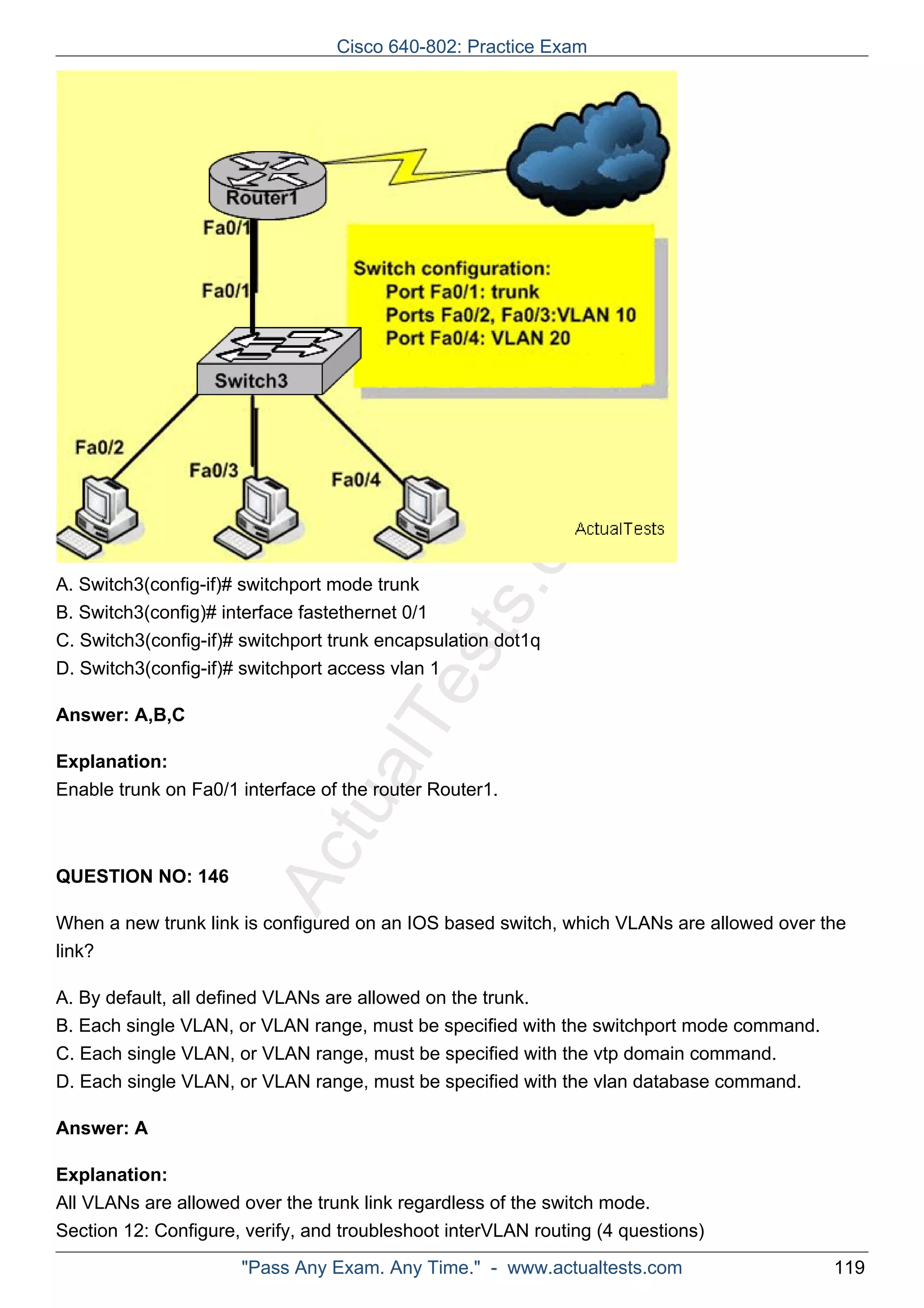
C. The system is malfunctioning.
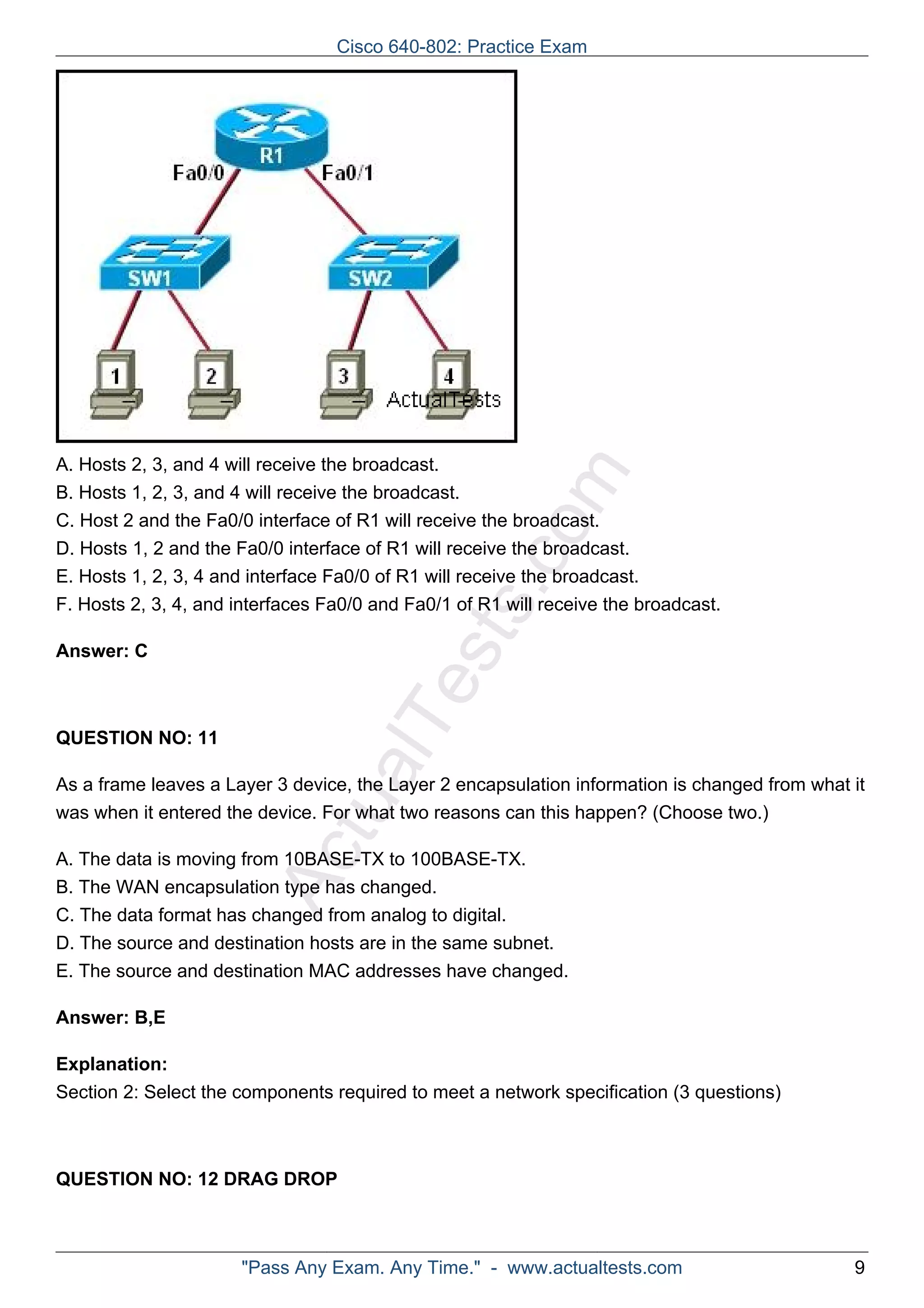
D. The system is not powered up.
Answer: C
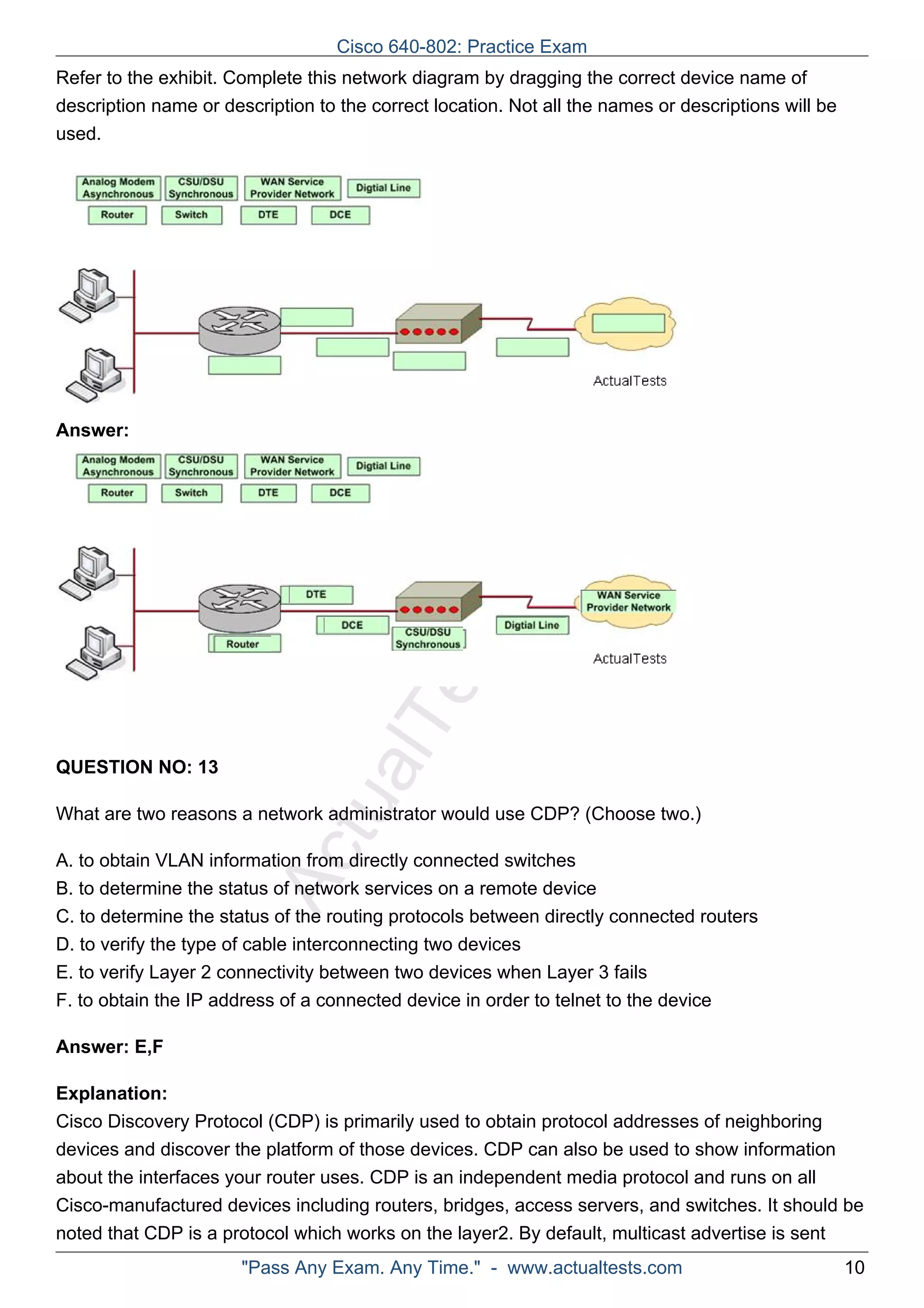
Explanation:
While the switch powers on, it begins POST, a series of tests. POST runs automatically to verify
that the switch functions properly. When the switch begins POST, the system LED is off. If POST
completes successfully, the LED turns green. If POST fails, the LED turns amber.
Note : POST failures are usually fatal. Call Cisco Systems if your switch does not pass POST.
QUESTION NO: 78
A Catalyst 2950 needs to be reconfigured. What steps will ensure that the old configuration is
erased?
A. Erase the running configuration.
B. Restart the switch.
C. Modify the configuration register.
D. Delete the VLAN database.
Answer: B,D
Explanation:
For switches such as the 2950, the process is much the same as a router, but you should delete
the VLAN.DAT file before reloading the router. This file contains VLAN information and is kept in
flash, so it will still be present after a reload.
switch1#delete vlan.dat
Delete filename [vlan.dat]?
Delete flash:vlan.dat? [confirm]
switch1#reload
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 70](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-70-2048.jpg)



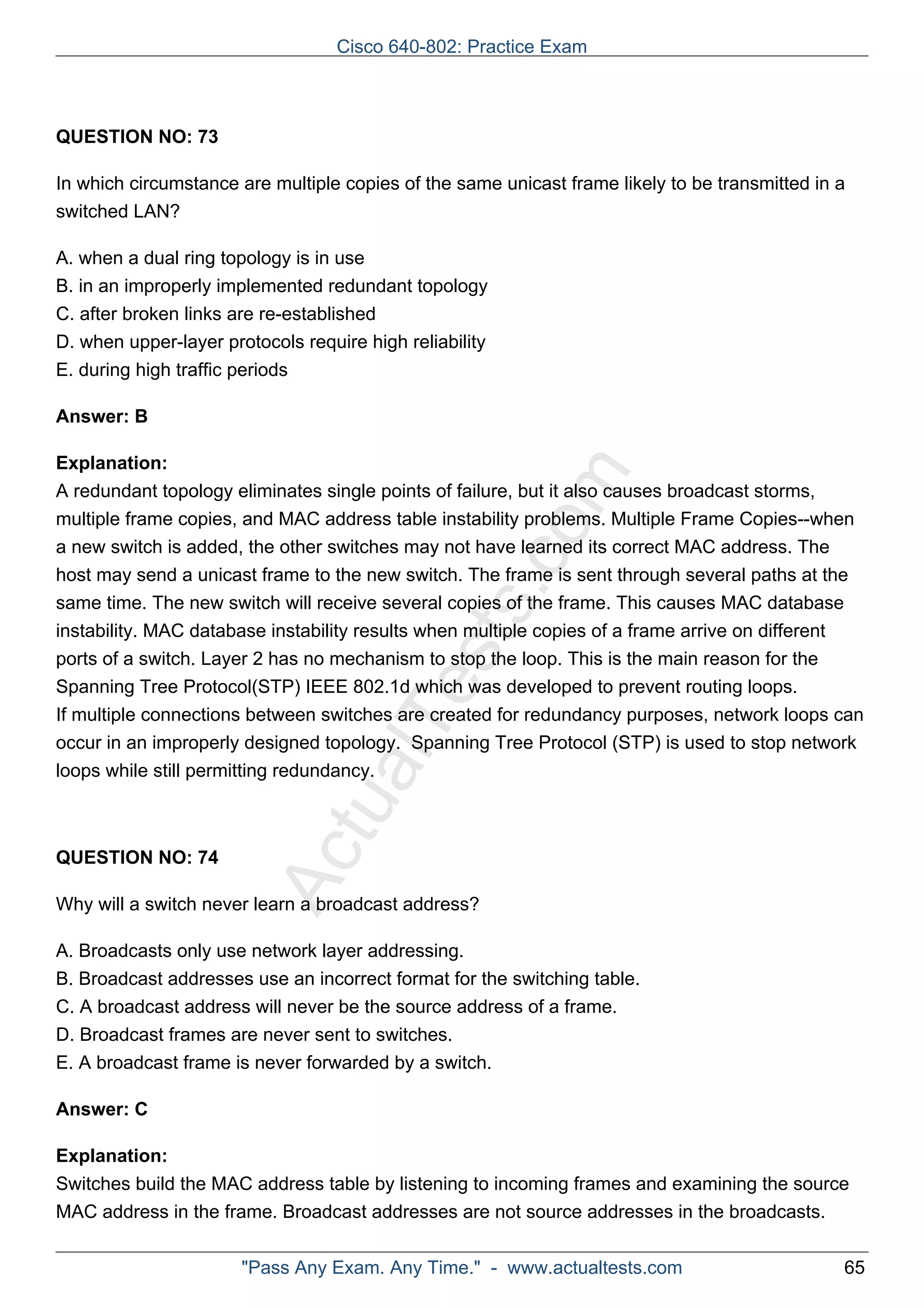
![B. destination IP address
C. destination port address
D. destination MAC address
Cisco 640-802: Practice Exam
ActualTests.com
Answer: D
Explanation:
Switches use port address table to find locations of the receiving station. When a port receives a
frame, switch will first study and then forward. Switches will check destination MAC addresses on
the frame head, and search for the corresponding entries in port address table. If matching entry is
found, switch will forward the frame from the designated port. If the port is the same port that
receives this frame (sending and receiving stations are connected to the same port), switch will
discard the frame. If no entry is found, or destination MAC address is broadcast address or multi-cast
address, switch will flood out the frame from all the rest ports.
QUESTION NO: 85
A Catalyst 2950 needs to be reconfigured. What steps will ensure that the old configuration is
erased? (Choose three.)
A. Erase flash.
B. Restart the switch.
C. Delete the VLAN database.
D. Erase the running configuration.
E. Erase the startup configuration.
F. Modify the configuration register.
Answer: B,C,E
Explanation:
For switches such as the 2950, the process is much the same as a router, but you should delete
the VLAN.DAT file before reloading the router. This file contains VLAN information and is kept in
flash, so it will still be present after a reload.
switch1#delete vlan.dat
Delete filename [vlan.dat]?
Delete flash:vlan.dat? [confirm]
switch1#reload
Make sure to hit for the two questions regarding the deletion - if you answer "y" instead, the switch
thinks you're trying to erase a file named "y"!
After the reload is complete, you'll be prompted to enter setup mode. As you did with the router,
enter "N" and begin to configure the router from user exec mode.
"Pass Any Exam. Any Time." - www.actualtests.com 75](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-75-2048.jpg)



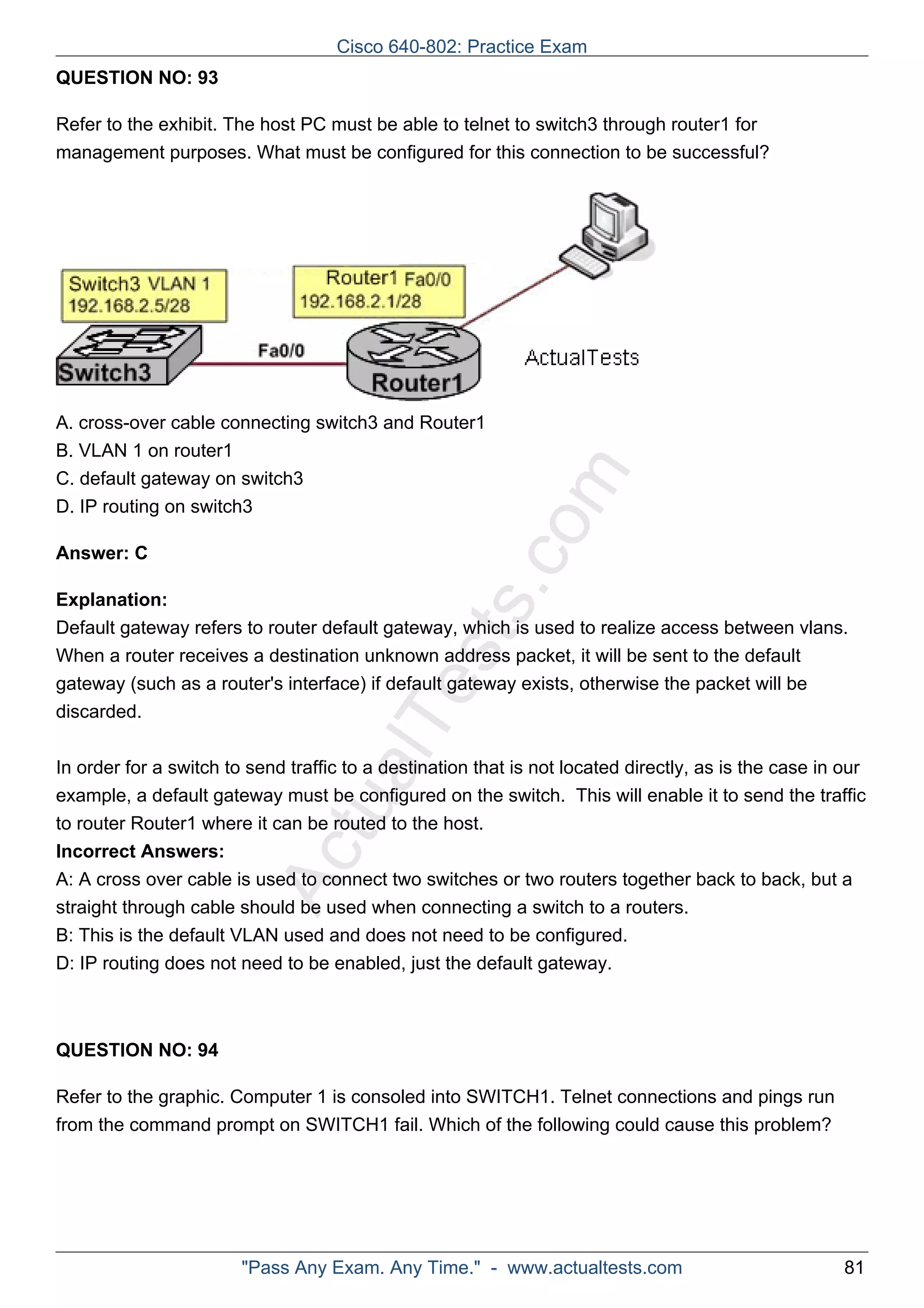










































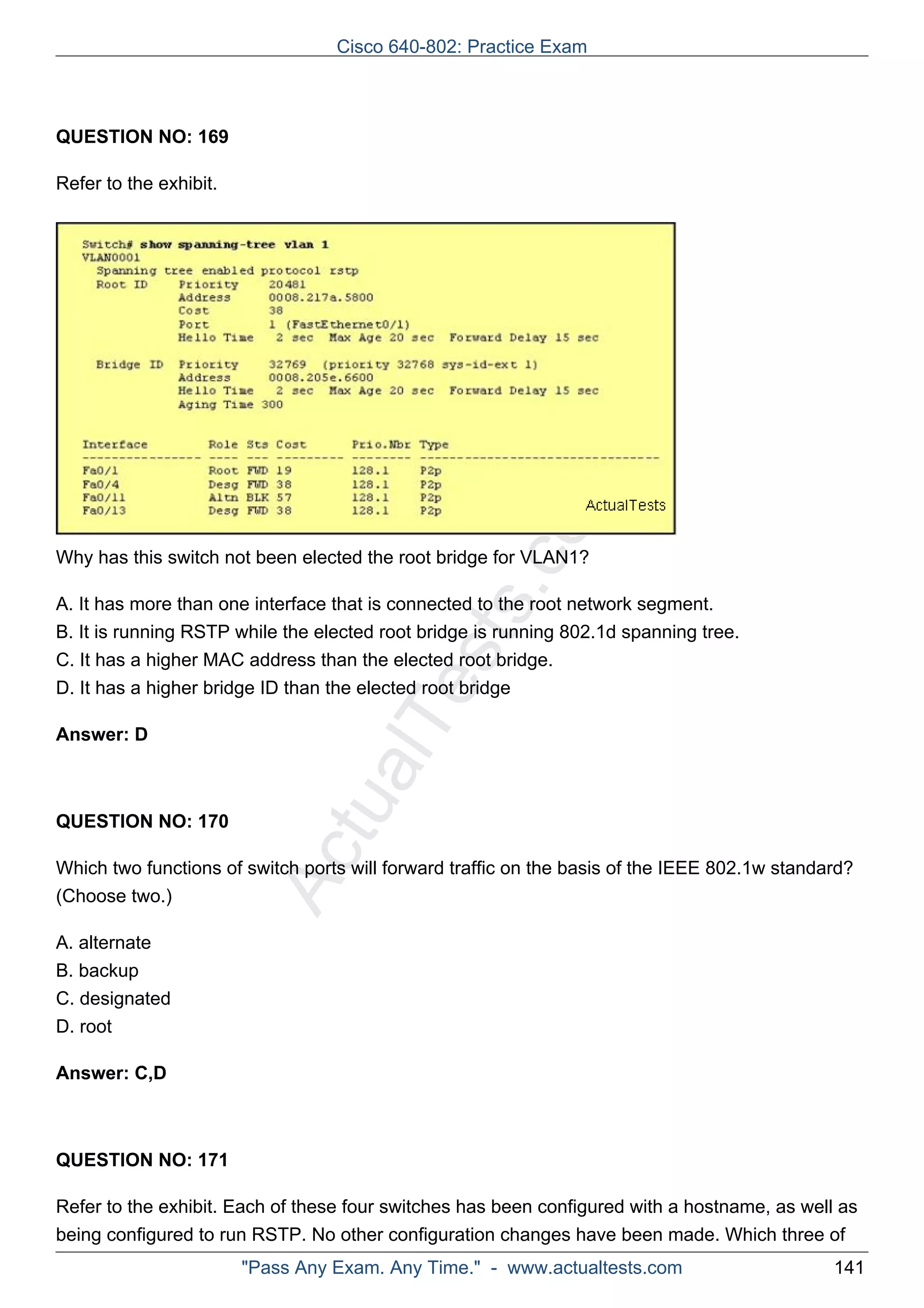














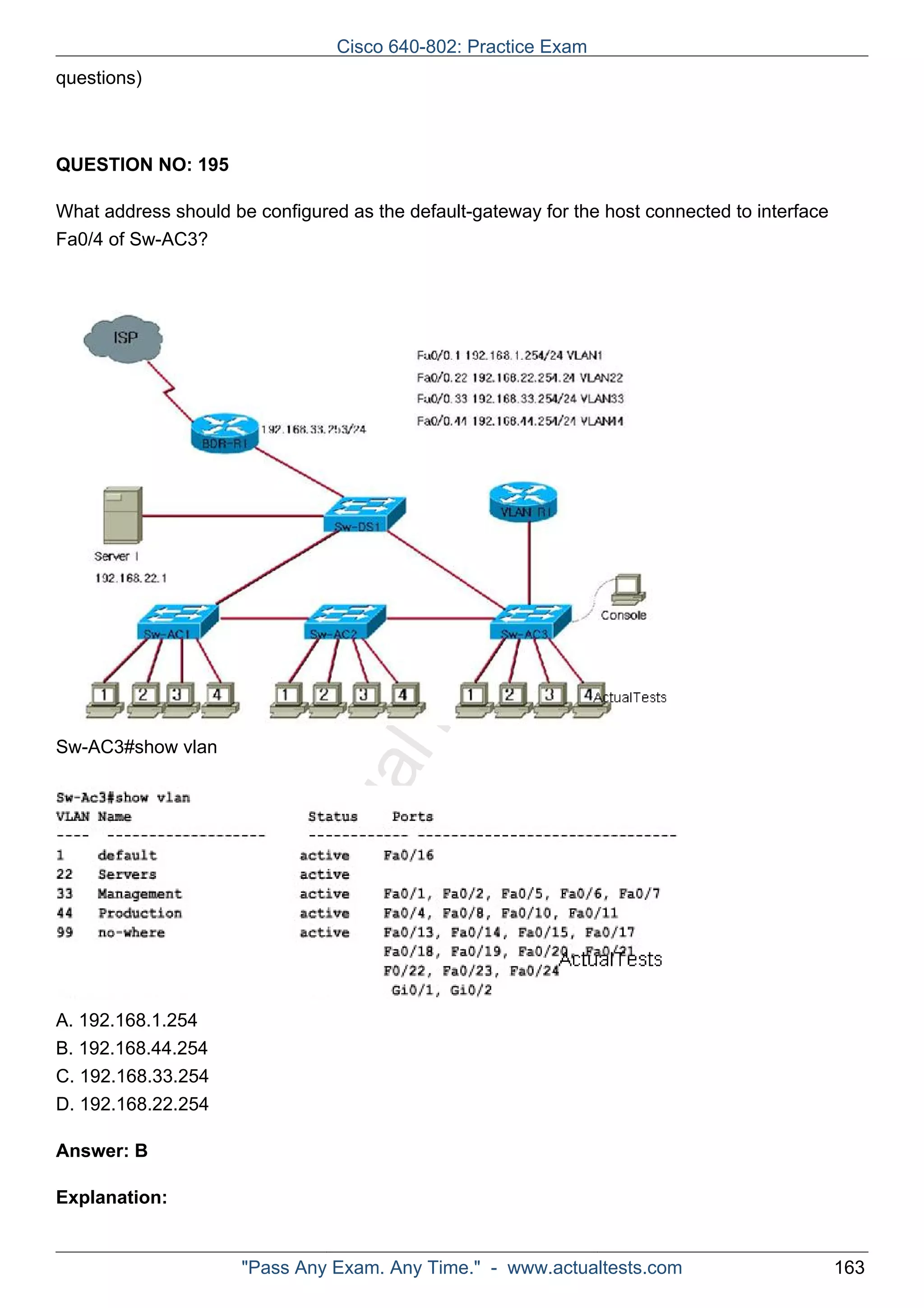
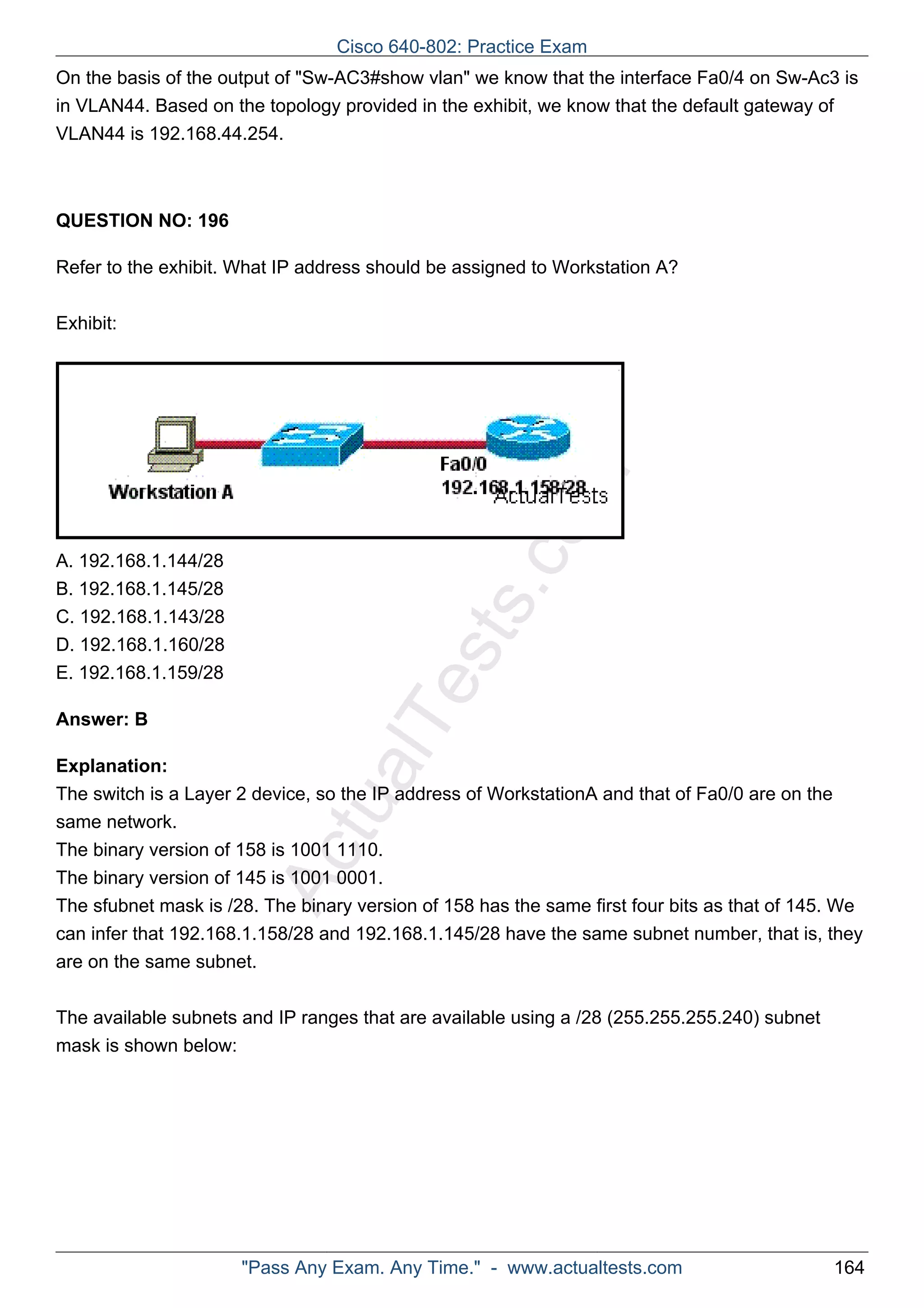





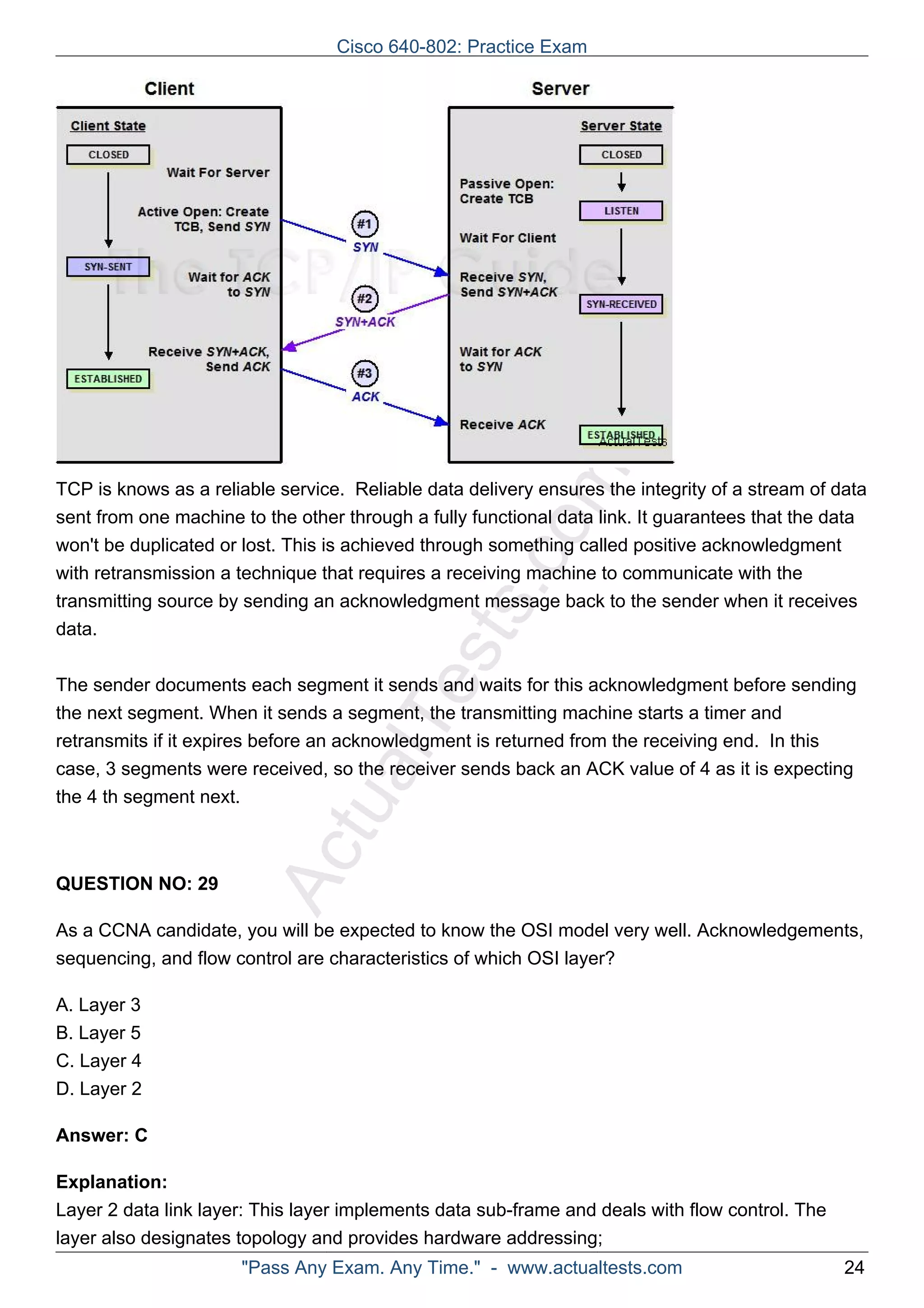
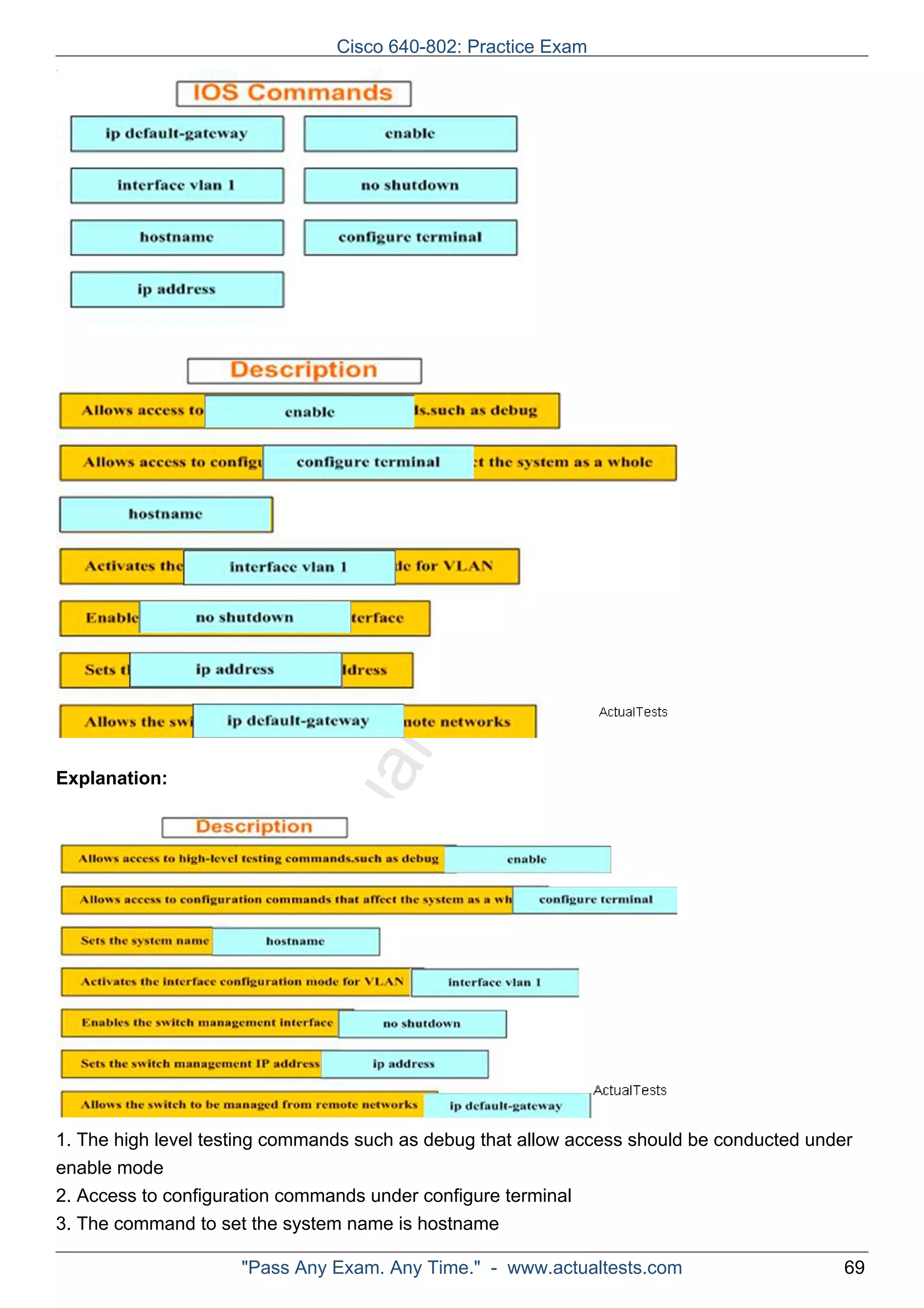
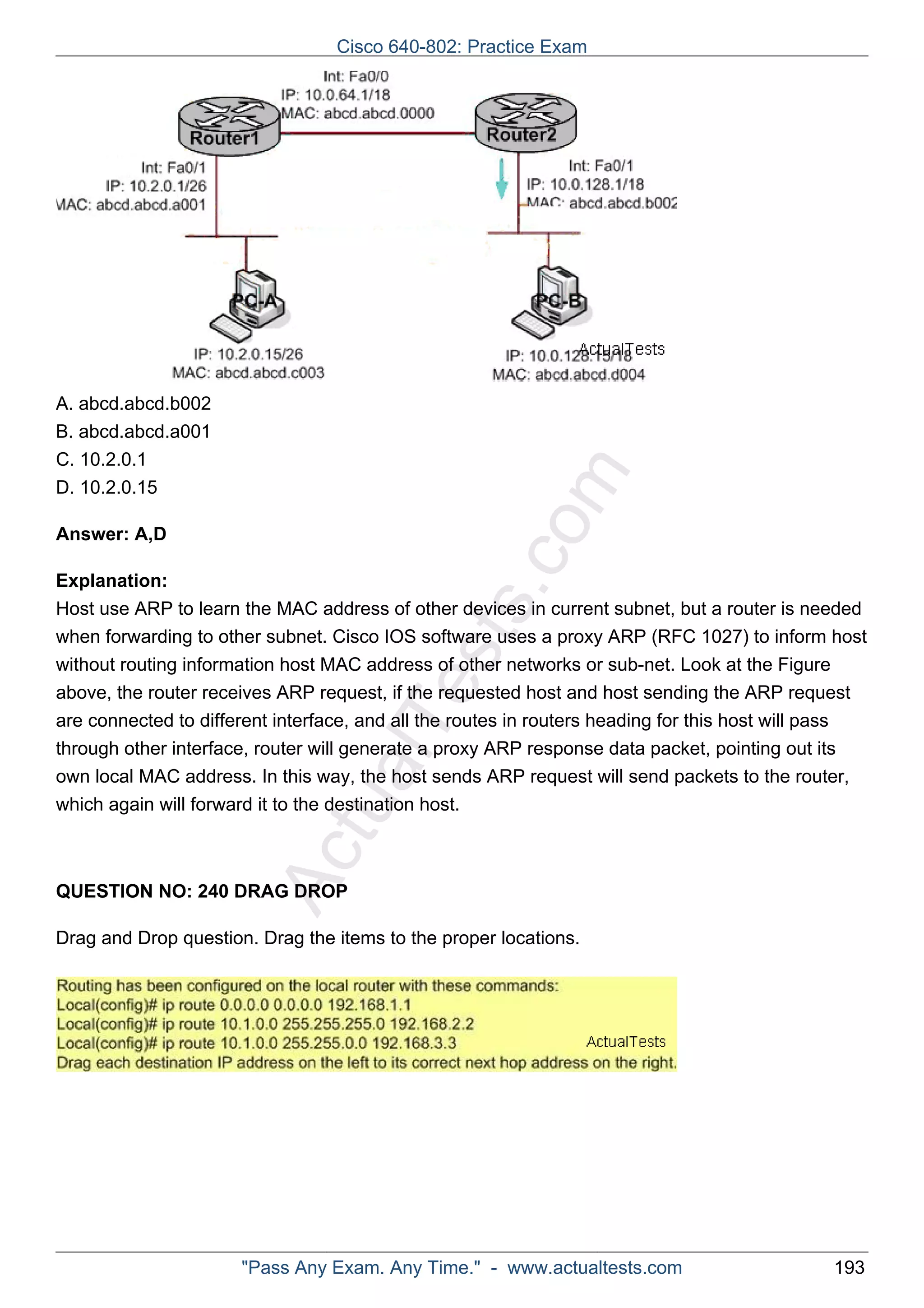
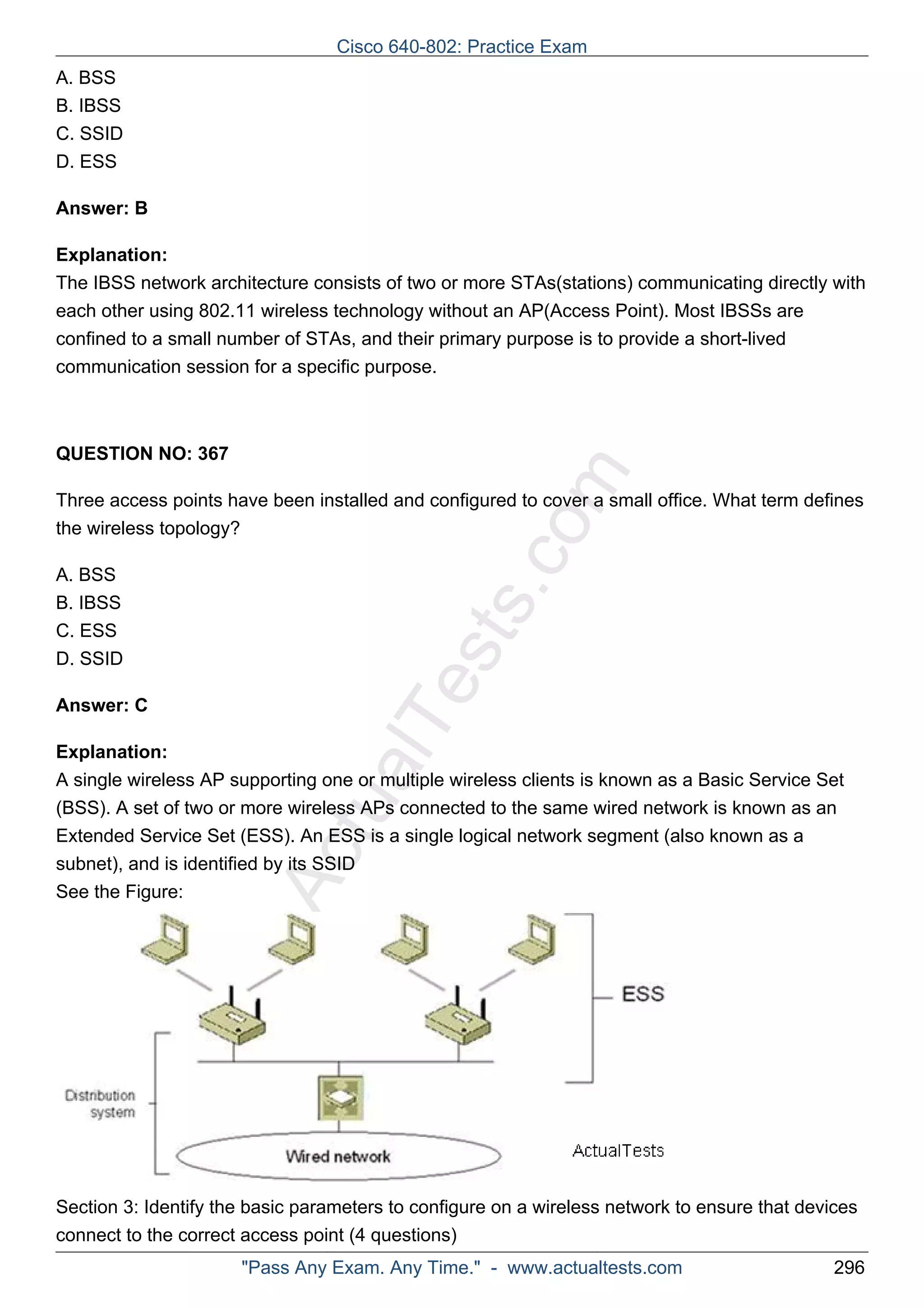
![Cisco 640-802: Practice Exam
We need to find the range for the 172.31.80.0/20 network. 1) Since this is a /20, convert the third
octet to binary: 172.31.0101 0000.0 2) Segregate the network and host address: 172.31. 0101
0000 .0 3) The network address will be: 172.31.80.0 4) The broadcast address will be: [convert all
the blue to one (1) plus the red colored] 172.31.95.255 That is now your range 172.31.80.0 -
172.31.95.255
ActualTests.com
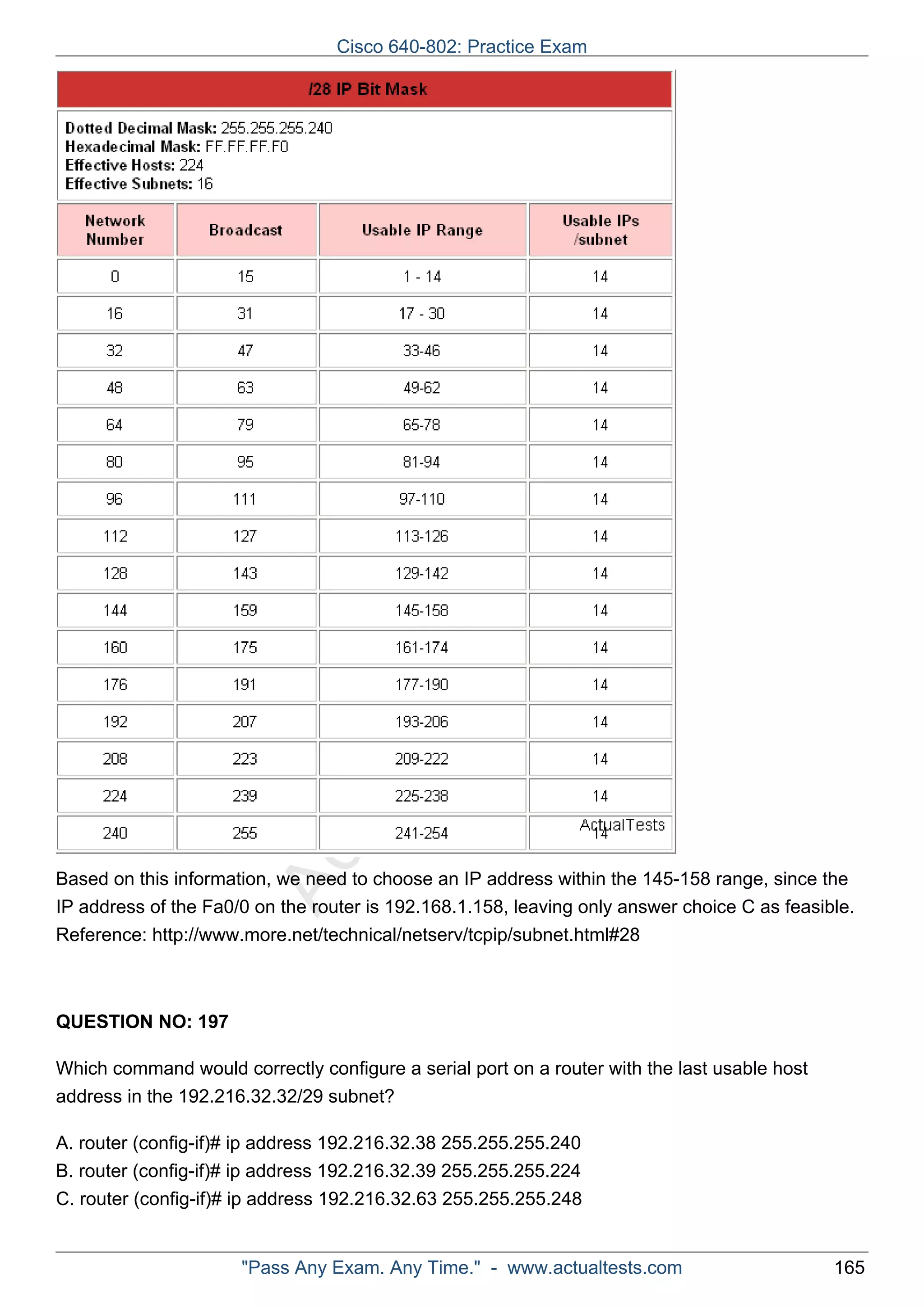
QUESTION NO: 210
Given the address 192.168.20.19/28, which host addresses are valid on this subnet? (Choose
two.)
A. 192.168.20.29
B. 192.168.20.31
C. 192.168.20.17
D. 192.168.20.0
Answer: A,C
QUESTION NO: 211
Refer to the exhibit. Which mask is correct to use for the WAN link between the routers that will
provide connectivity while wasting the least amount of addresses?
A. /23
B. /24
C. /25
D. /30
Answer: D
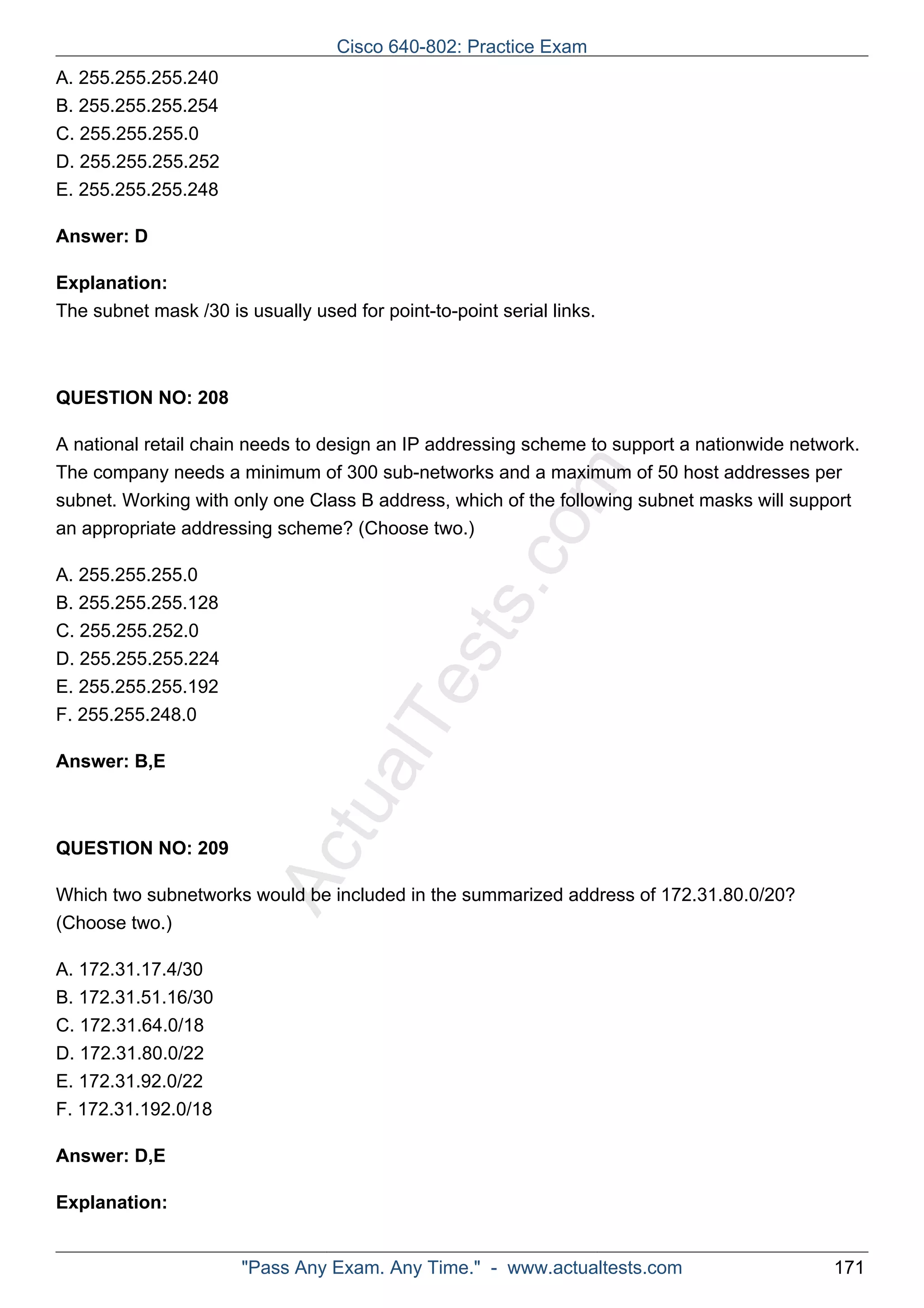
QUESTION NO: 212
The network 172.25.0.0 has been divided into eight equal subnets. Which of the following IP
addresses can be assigned to hosts in the third subnet if the ip subnet-zero command is
configured on the router? (Choose three.)
"Pass Any Exam. Any Time." - www.actualtests.com 172](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-172-2048.jpg)
















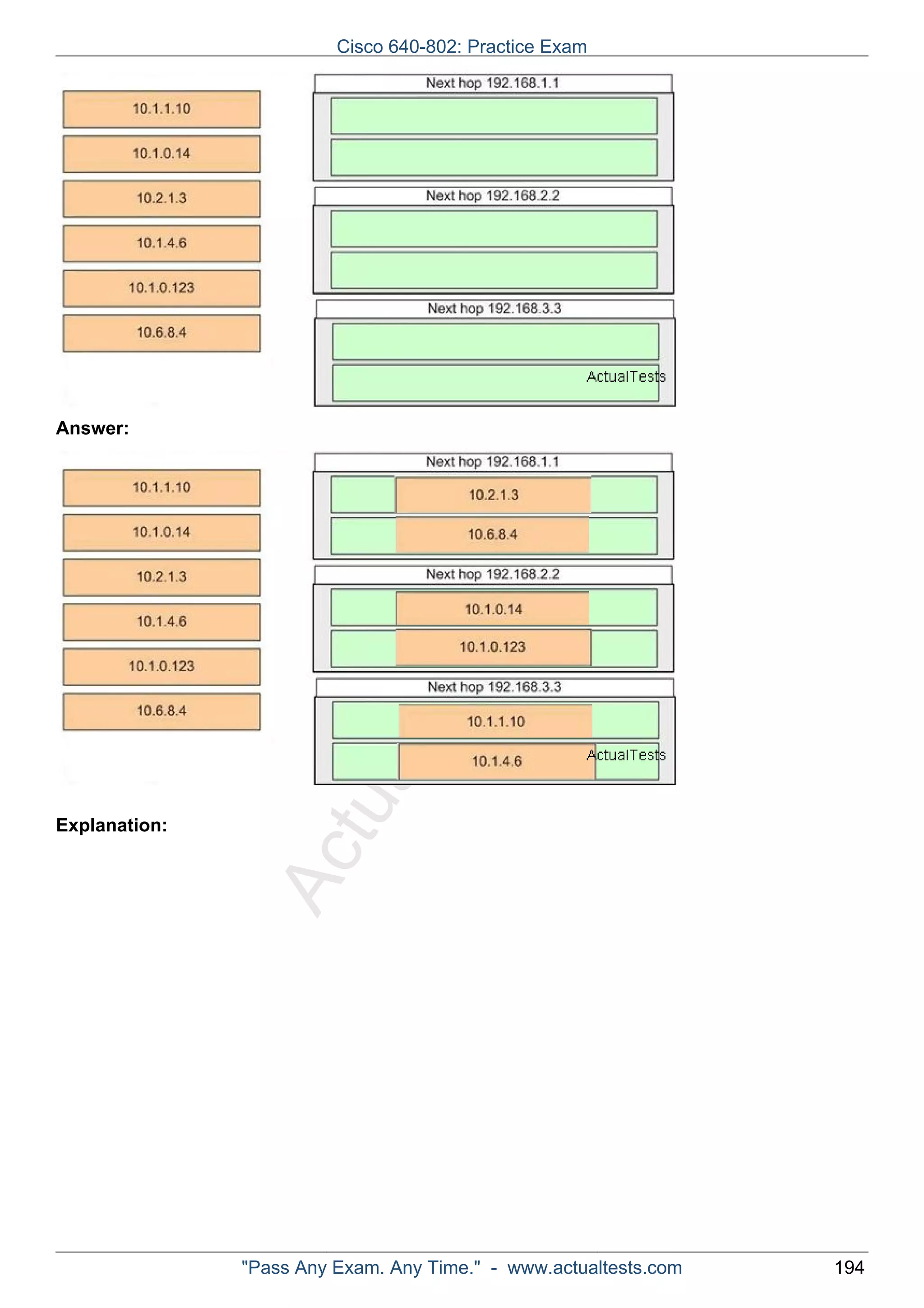



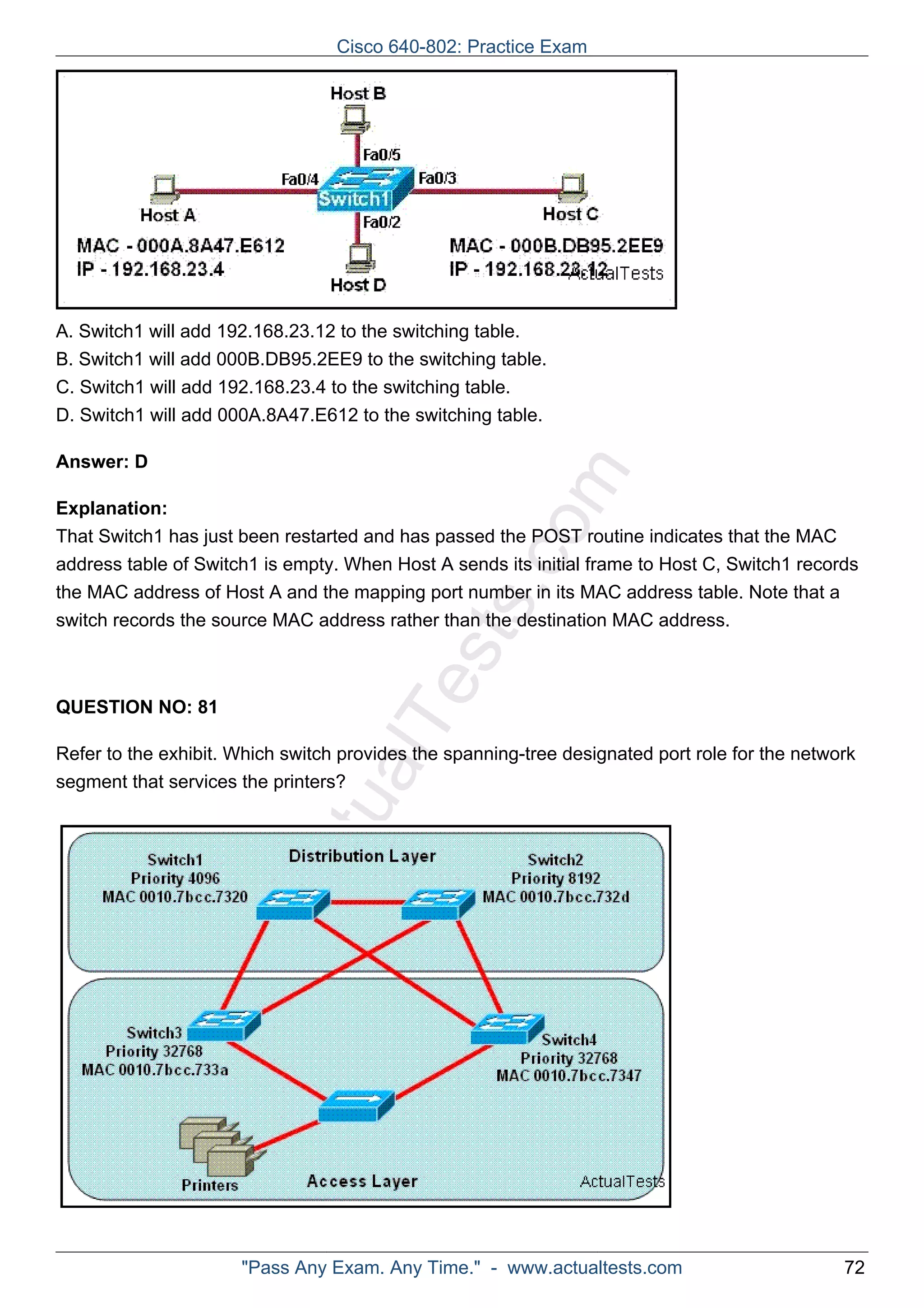
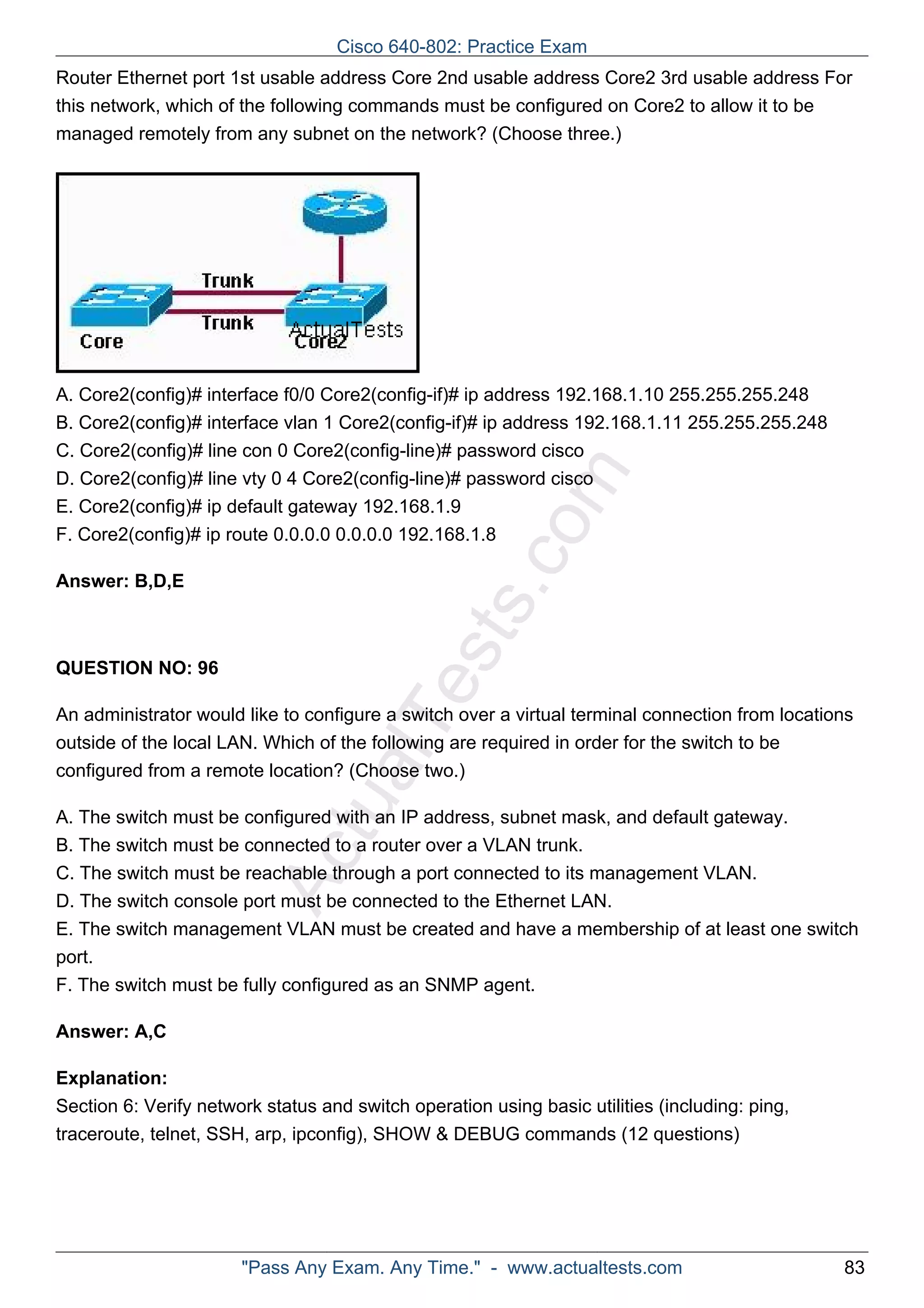
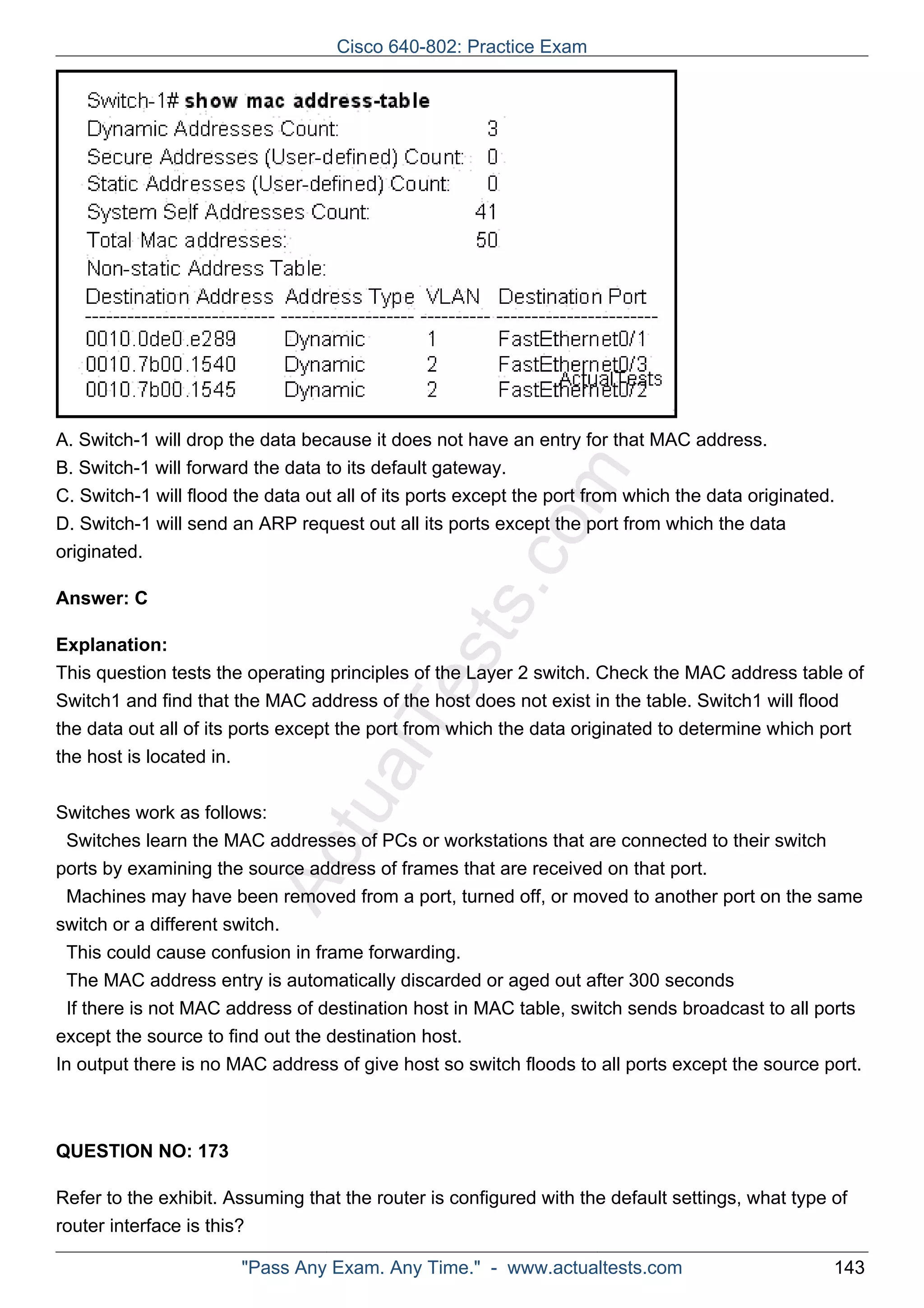
![D. Because of damaged flash memory, the router will fail the POST.
E. It will attempt to locate the IOS from a TFTP server. If this fails, it will initiate the setup dialog.
ActualTests.com
Answer: C
Explanation:
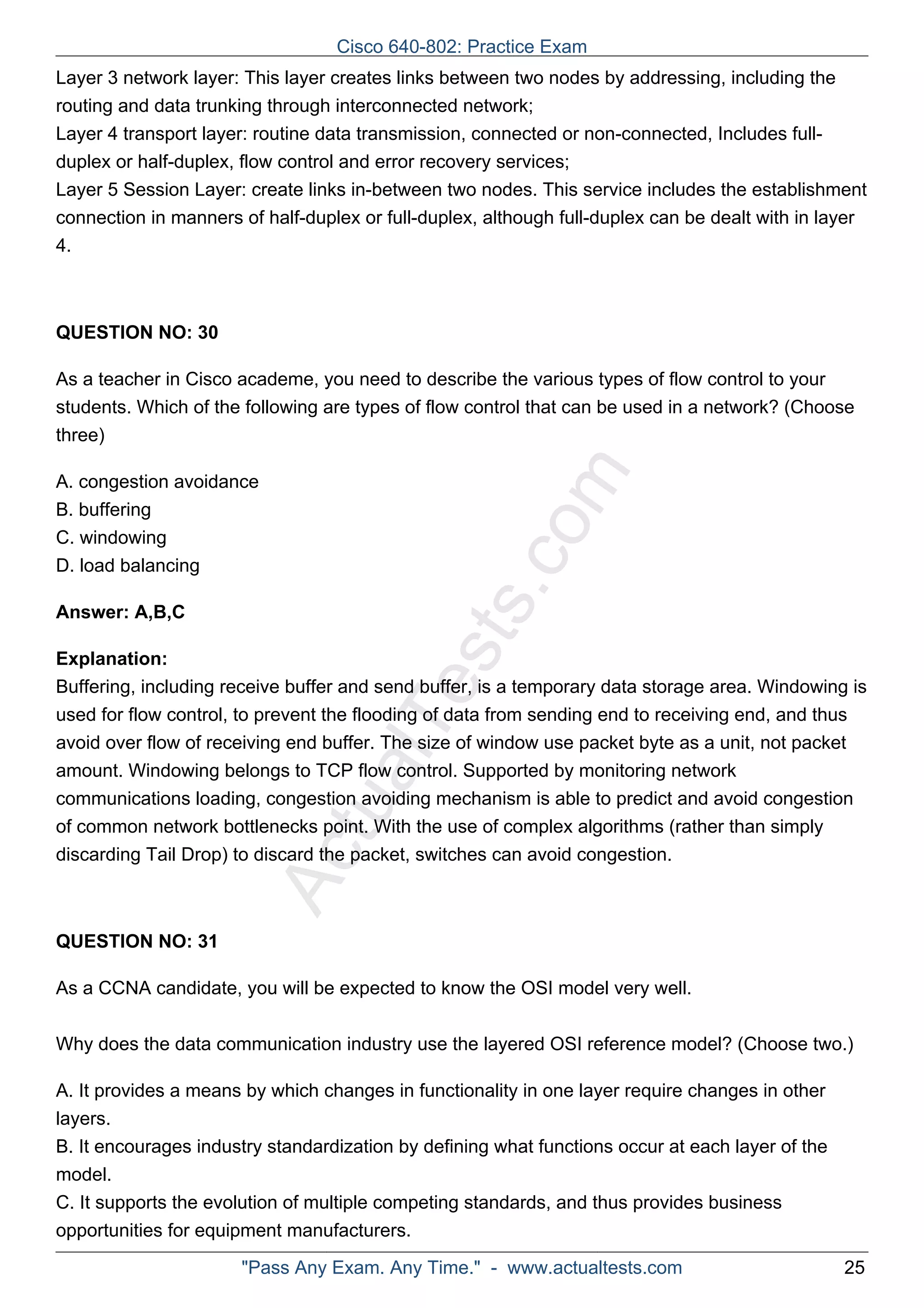
The boot sequence of a Cisco router is shown below:
Booting up the router and locating the Cisco IOS 1. POST (power on self test) 2. Bootstrap code
executed 3. Check Configuration Register value (NVRAM) which can be modified using the config-register
command 0 = ROM Monitor mode 1 = ROM IOS 2 - 15 = startup-config in NVRAM 4.
Startup-config file: Check for boot system commands (NVRAM) If boot system commands in
startup-config a. Run boot system commands in order they appear in startup-config to locate the
IOS b. [If boot system commands fail, use default fallback sequence to locate the IOS (Flash,
TFTP, ROM)?]
If no boot system commands in startup-config use the default fallback sequence in locating the
IOS: a. Flash (sequential) b. TFTP server (netboot) c. ROM (partial IOS) or keep retrying TFTP
depending upon router model 5. If IOS is loaded, but there is no startup-config file, the router will
use the default fallback sequence for locating the IOS and then it will enter setup mode or the
setup dialogue. 6. If no IOS can be loaded, the router will get the partial IOS version from ROM
Reference: http://www.svrops.com/svrops/documents/ciscoboot.htm
QUESTION NO: 246
Router#show flash exhibit:
Refer to the exhibit. The technician wants to upload a new IOS in the router while keeping the
existing IOS. What is the maximum size of an IOS file that could be loaded if the original IOS is
also kept in flash?
A. 3 MB
B. 5 MB
C. 7 MB
D. 4 MB
Answer: D
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 199](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-199-2048.jpg)
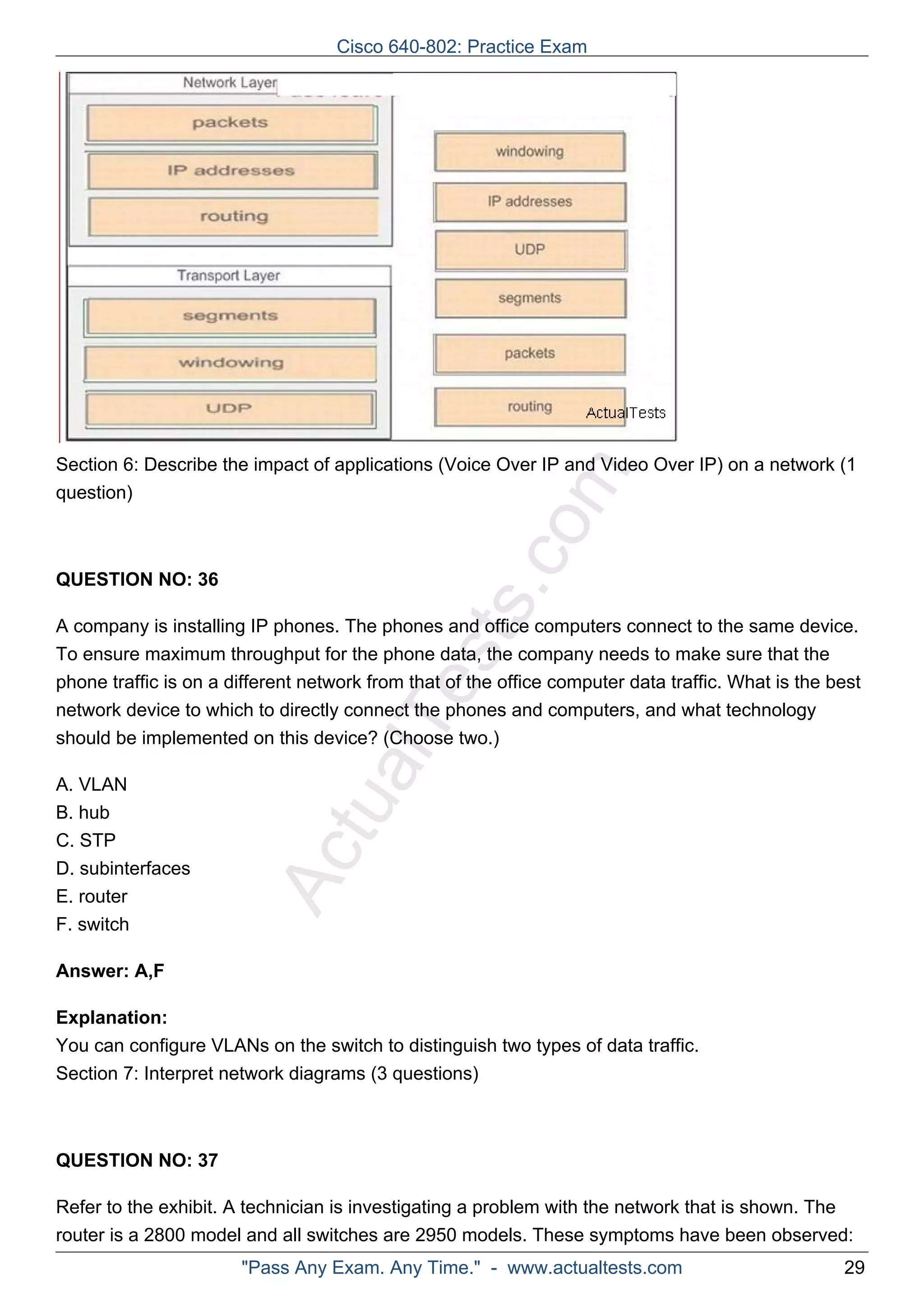
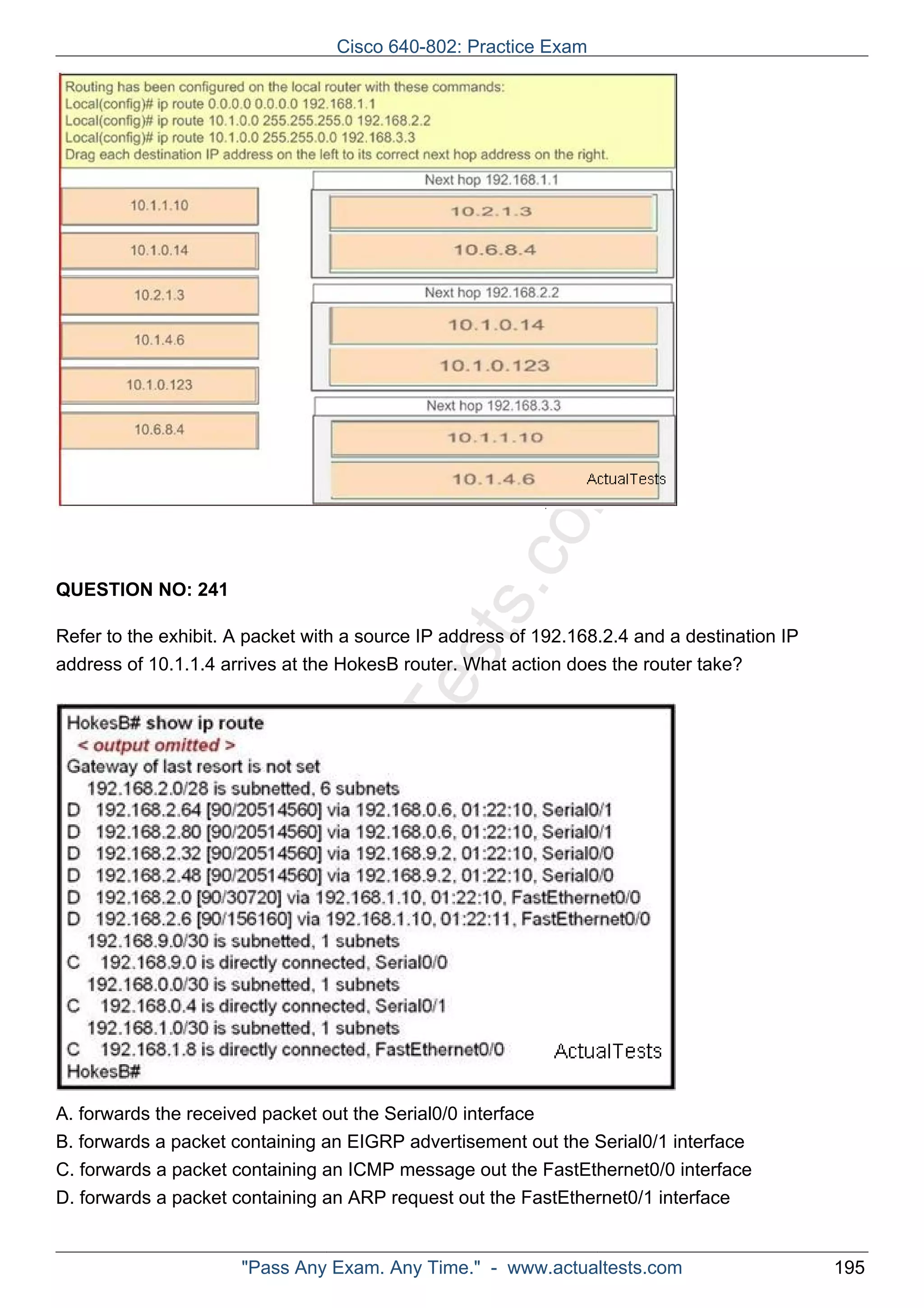
![Cisco 640-802: Practice Exam
4.Startup-config file: Check for boot system commands (NVRAM)
If boot system commands in startup-config
a. Run boot system commands in order they appear in startup-config to locate the IOS
b. [If boot system commands fail, use default fallback sequence to locate the IOS (Flash, TFTP,
ROM)?]
If no boot system commands in startup-config use the default fallback sequence in locating the
IOS:
a. Flash (sequential)
b. TFTP server (netboot)
c. ROM (partial IOS) or keep retrying TFTP depending upon router model
5. If IOS is loaded, but there is no startup-config file, the router will use the default fallback
sequence for locating the IOS and then it will enter setup mode or the setup dialogue.
ActualTests.com
6. If no IOS can be loaded, the router will get the partial IOS version from ROM
Default (normal) Boot Sequence
Power on Router - Router does POST - Bootstrap starts IOS load - Check configuration register to
see what mode the router should boot up in (usually 0x102 to 0x10F to look in NVRAM) - check
the startup-config file in NVRAM for boot-system commands (normally there aren't any) - load IOS
from Flash.
Boot System Commands
Router(config)# boot system flash IOS filename - boot from FLASH memory Router(config)# boot
system tftp IOS filename tftp server ip address - boot from a TFTP server
Router(config)# boot system rom - boot from system ROM
Configuration Register Command
Router(config)# config-register 0x10x (where that last x is 0-F in hex)
When the last x is:
0 = boot into ROM Monitor mode
1 = boot the ROM IOS
2 - 15 = look in startup config file in NVRAM
QUESTION NO: 248
What will a new router do during startup if a configuration file is not located in NVRAM?
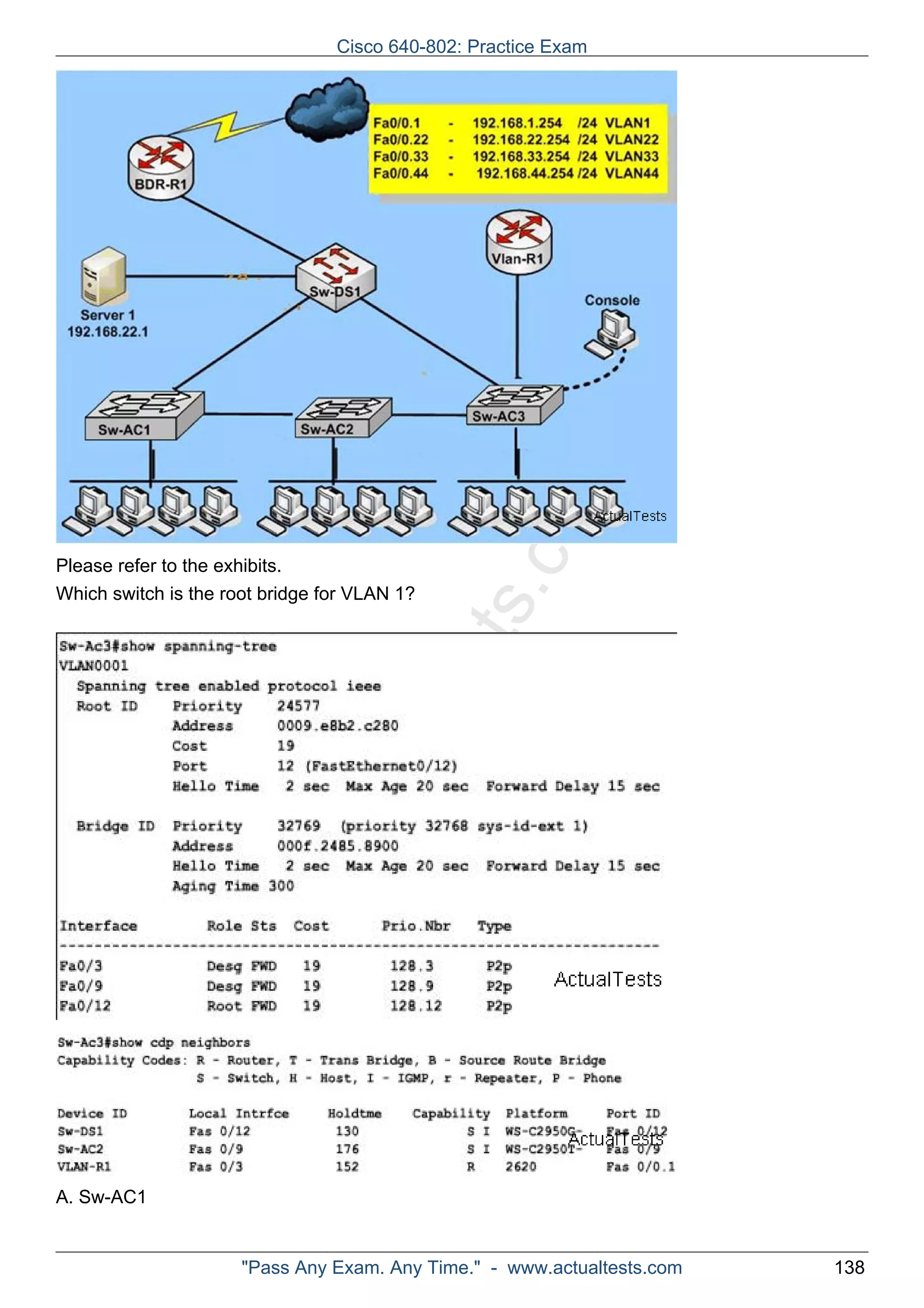
A. It will search for the configuration file in flash and if no configuration file is found there, it will
enter the setup dialog.
B. It will search for the configuration file on a TFTP server and if no configuration file is found
there, it will load a limited configuration file fromROM.
C. It will search for the configuration file on a TFTP server and if no configuration file is found
there, it will enter the setup dialog.
"Pass Any Exam. Any Time." - www.actualtests.com 201](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-201-2048.jpg)
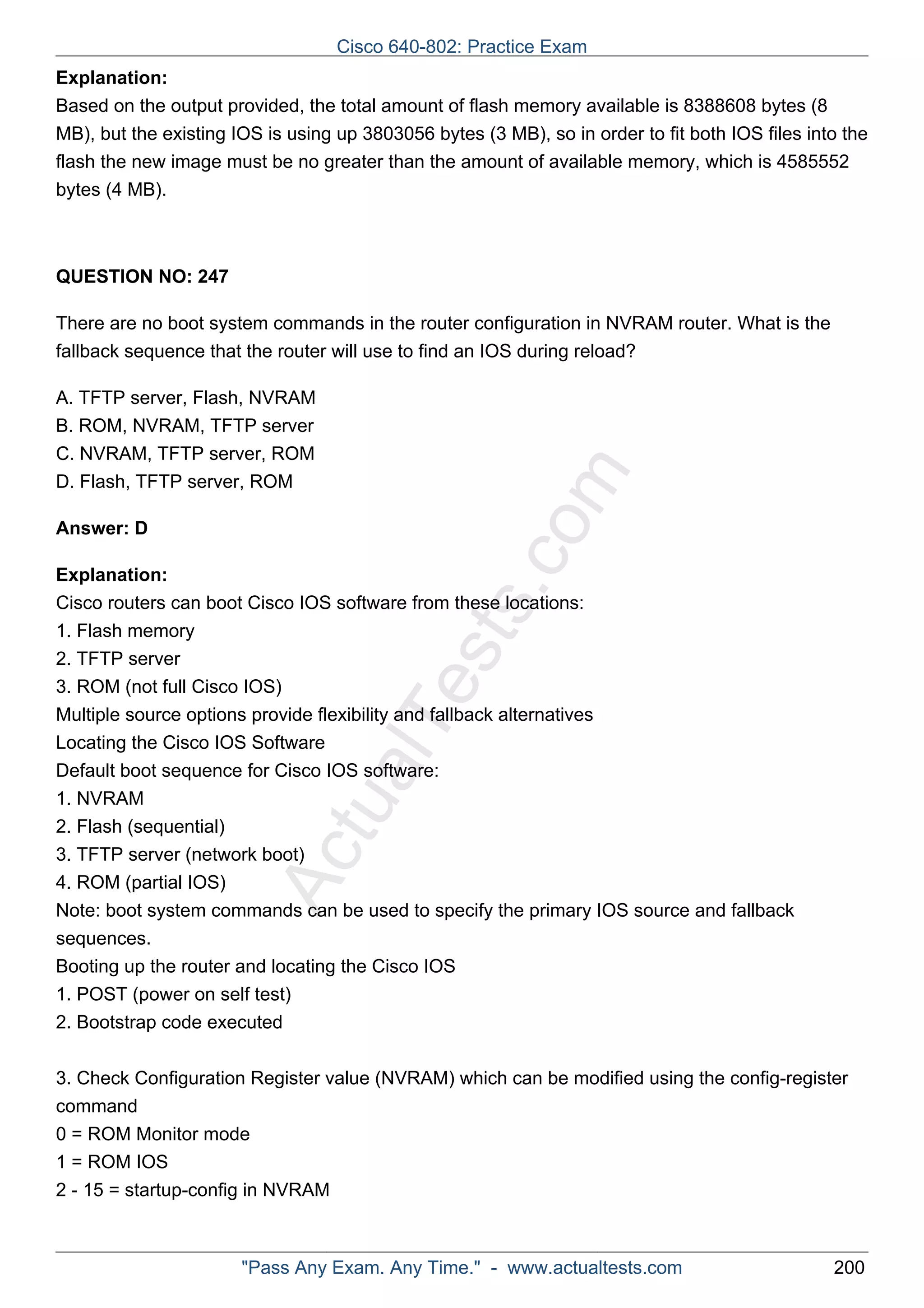
![3. Check Configuration Register value (NVRAM) which can be modified using the config-register
command
0 = ROM Monitor mode
1 = ROM IOS
2 - 15 = startup-config in NVRAM
4. Startup-config file: Check for boot system commands (NVRAM)
If boot system commands in startup-config
a. Run boot system commands in order they appear in startup-config to locate the IOS
b. [If boot system commands fail, use default fallback sequence to locate the IOS (Flash, TFTP,
ROM)?]
If no boot system commands in startup-config use the default fallback sequence in locating the
IOS:
a. Flash (sequential)
b. TFTP server (netboot)
c. ROM (partial IOS) or keep retrying TFTP depending upon router model
5. If IOS is loaded, but there is no startup-config file, the router will use the default fallback
sequence for locating the IOS and then it will enter setup mode or the setup dialogue.
6. If no IOS can be loaded, the router will get the partial IOS version from ROM
ActualTests.com
QUESTION NO: 250
A network administrator changes the configuration register to 0x2142 and reboots the router. What
are two results of making this change? (Choose two.)
A. The IOS image will be ignored.
B. The router will prompt to enter initial configuration mode.
C. The router will boot toROM.
D. Any configuration entries in NVRAM will be ignored.
E. The configuration in flash memory will be booted.
Answer: B,D
QUESTION NO: 251
Which two locations can be configured as a source for the IOS image in the boot system
command? (Choose two.)
A. RAM
B. NVRAM
C. flash memory
D. HTTP server
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 203](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-203-2048.jpg)














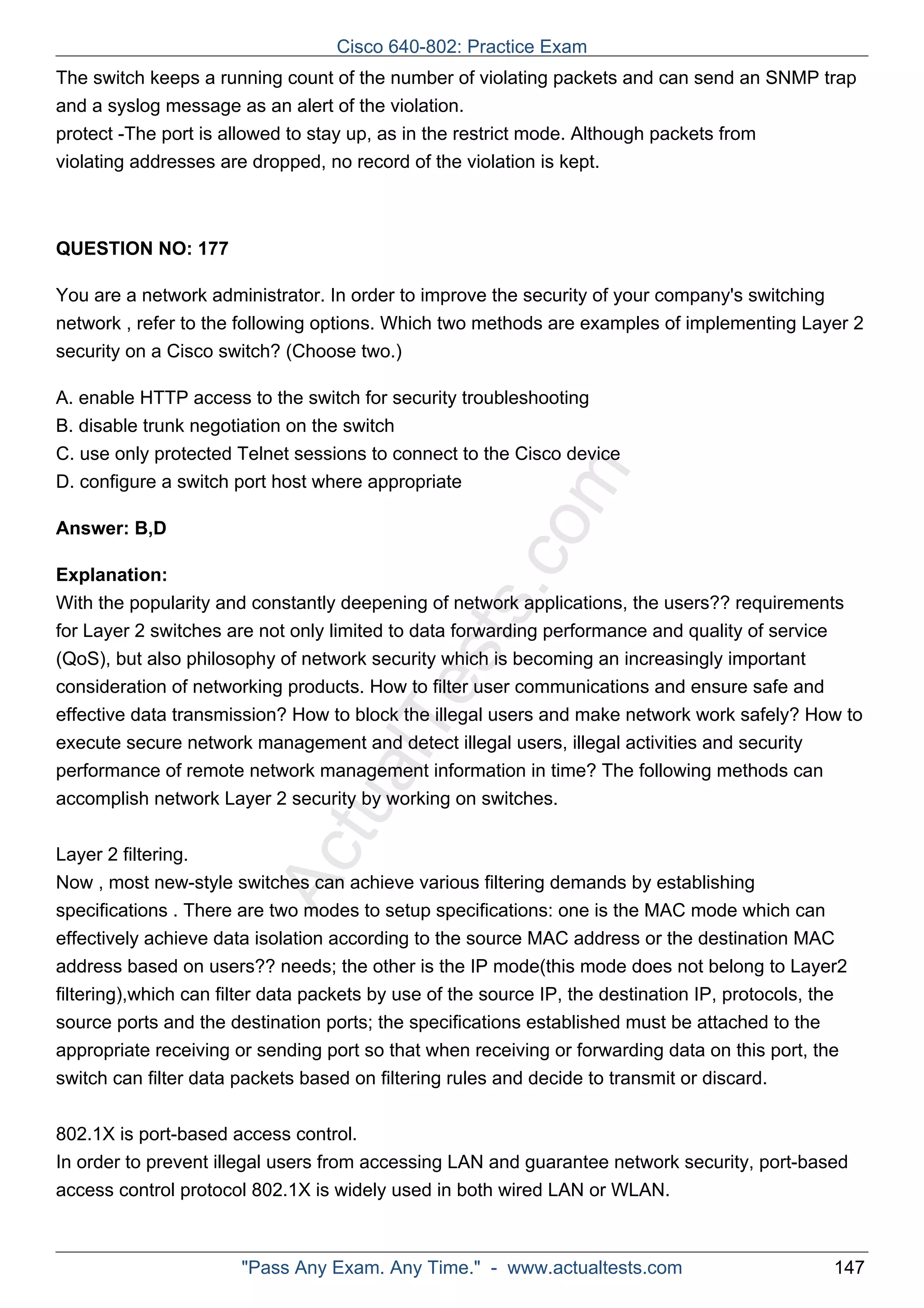
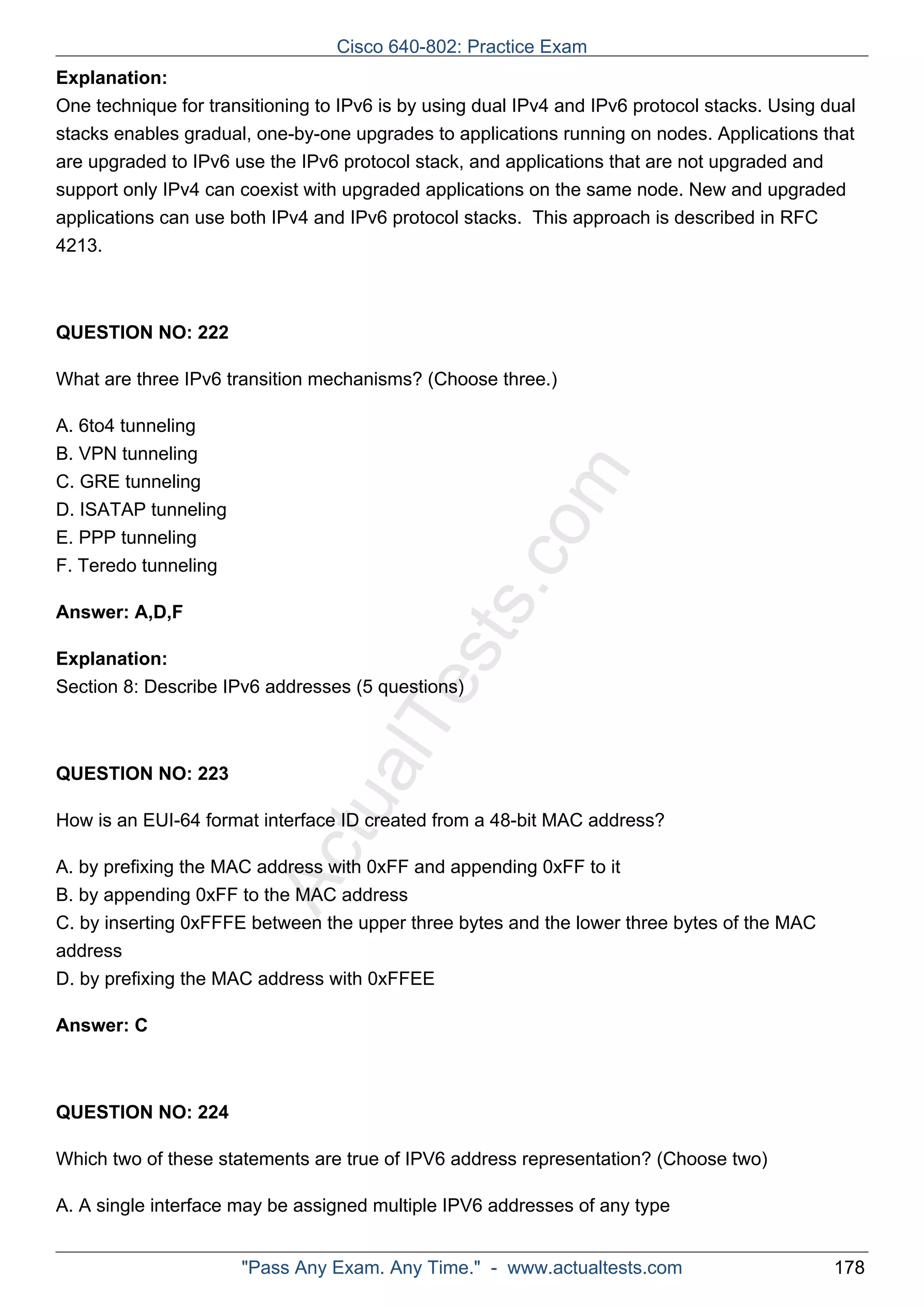
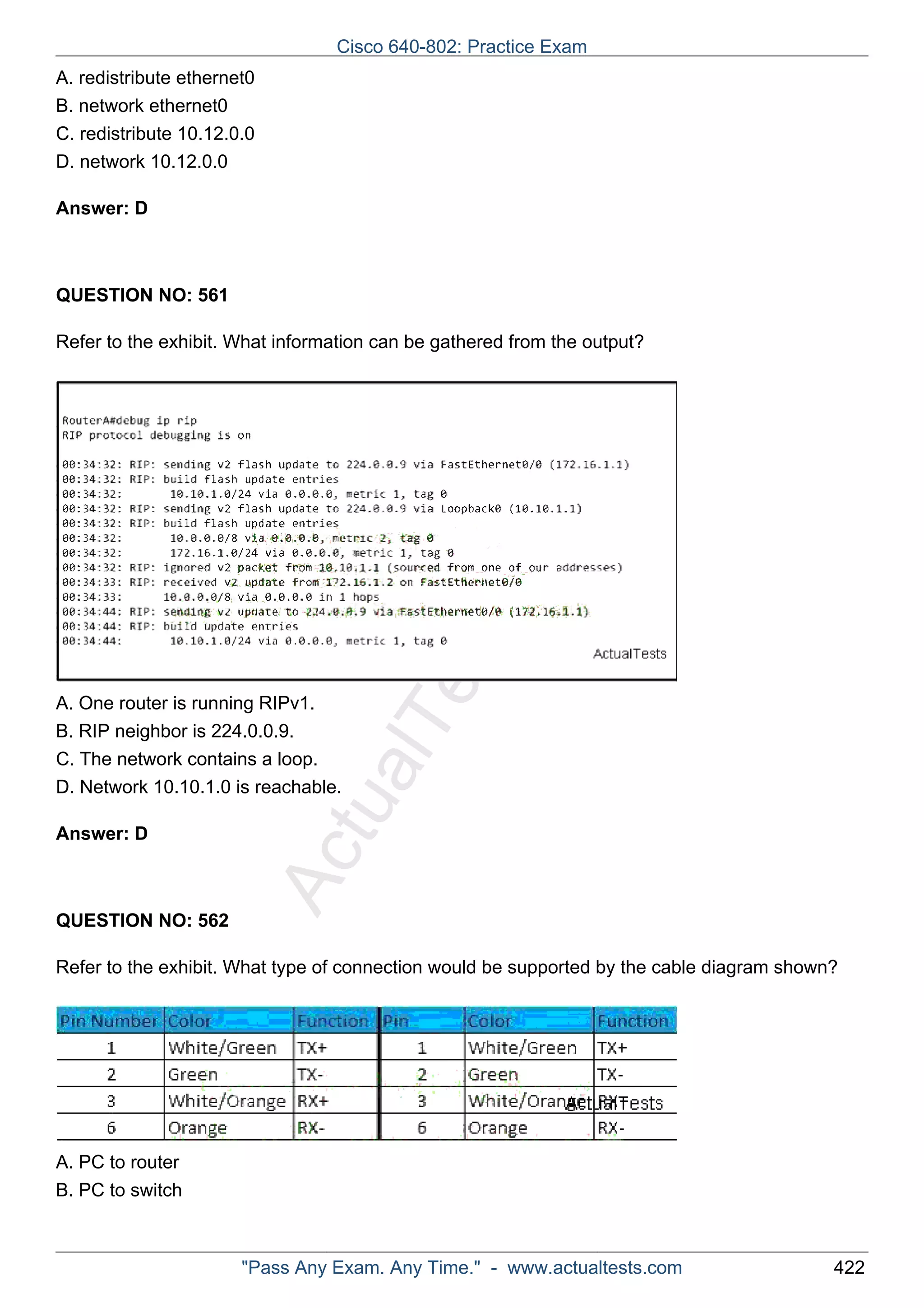
![Cisco 640-802: Practice Exam
Regarding the extended ping command; which of the statements below are true?(Choose two)
A. With the extended ping command you can specify the TCP and UDP port to be pinged.
B. With the extended ping command you can specify the timeout value.
C. The extended ping command is supported from user EXEC mode.
D. The extended ping command is available from privileged EXEC mode.
ActualTests.com
Answer: B,D
Explanation:
The extended ping command works only at the privileged EXEC command line.
Some of the extended ping command values include the datagram size and timeout value as
shown:
Datagram size [100]: Size of the ping packet (in bytes). Default: 100 bytes.
Timeout in seconds [2]: Timeout interval. Default: 2 (seconds). The ping is declared successful
only if the ECHO REPLY packet is received before this time interval.
The extended ping command works only at the privileged EXEC command line.
Some of the extended ping command values include the datagram size and timeout value as
shown:
Datagram size [100]: Size of the ping packet (in bytes). Default: 100 bytes.
Timeout in seconds [2]: Timeout interval. Default: 2 (seconds). The ping is declared successful
only if the ECHO REPLY packet is received before this time interval.
Incorrect Answers:
A: Ports can not be specified.
C: Regular pings are available in both user and privileged mode, but not extended pings.
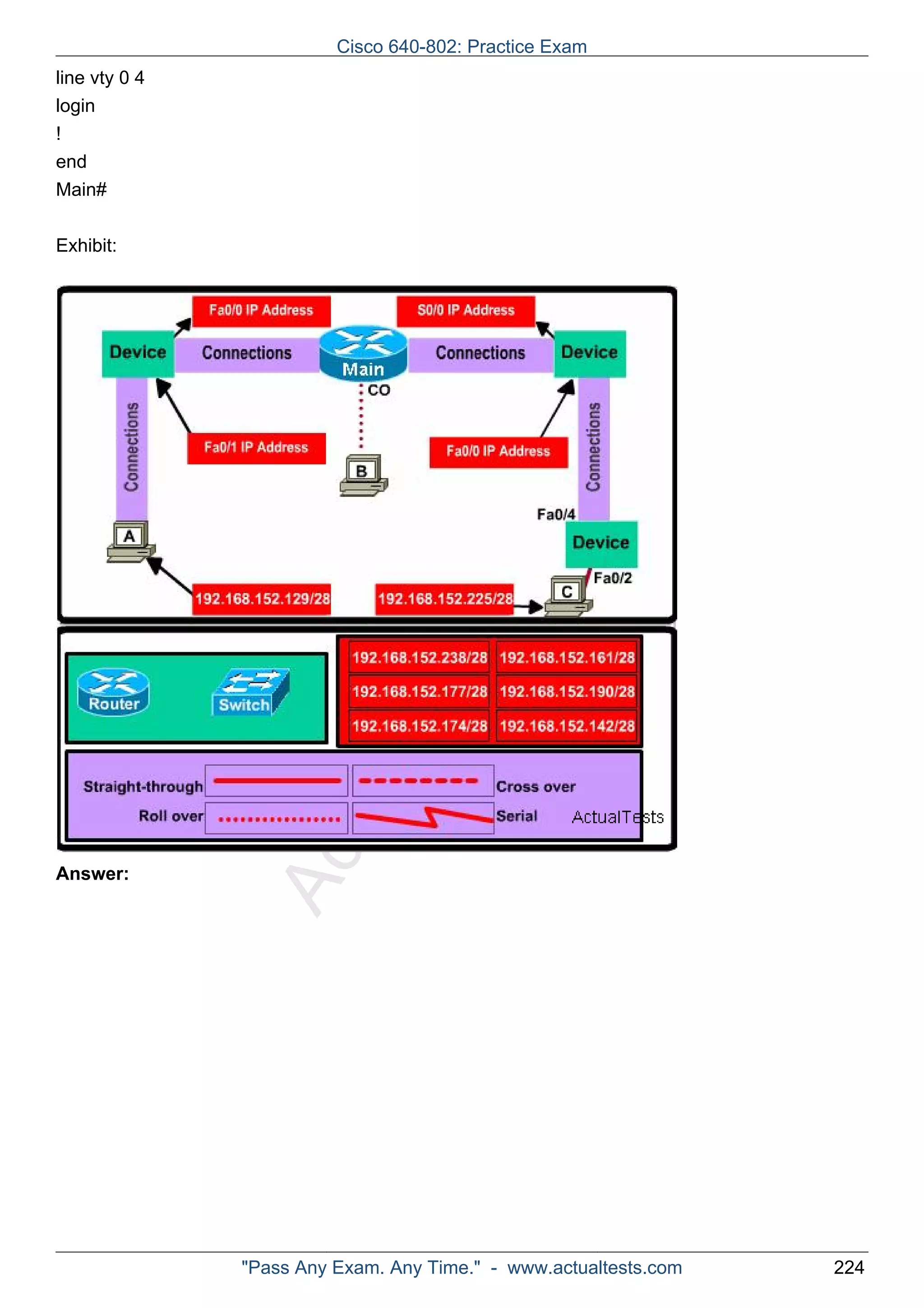
QUESTION NO: 275
The following output was seen on a network device:
This graphic shows the result of an attempt to open a Telnet connection to router access1 From
Remote27. Which of the following command sequences will correct this problem?
"Pass Any Exam. Any Time." - www.actualtests.com 226](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-226-2048.jpg)

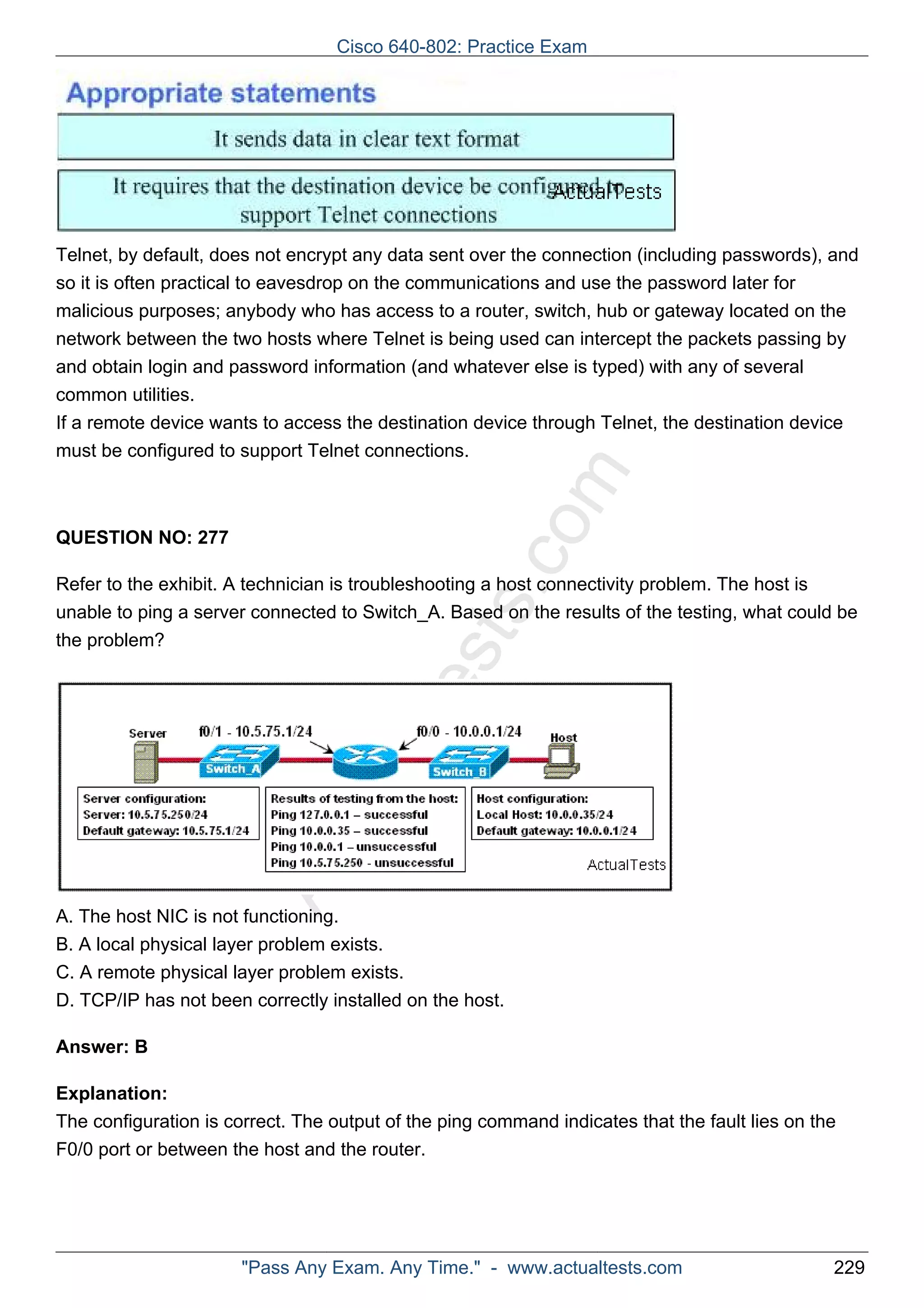

![Cisco 640-802: Practice Exam
D. It configures the router to send any traffic for an unknown destination to the 172.16.3.0 network.
E. It uses the default administrative distance.
F. It establishes a static route to the 172.16.3.0 network.
ActualTests.com
Answer: E,F
Explanation:
The user can specify the path for accessing certain network by configuring static route. In a
relatively simple network architecture, and the route to a certain network is unique, the static route
will be used.
ip route prefix mask {address | interface} [distance] [tag tag] [permanent]
Prefix :the destination network
mask :subnet mask
address :The IP address of the next hop, that is the address of port on the adjacent router
interface :local network interface
distance : administrative distance(optional)
tag tag : tag value(optional)
permanent :The router is designed as follows : would rather to shut down this port than move.
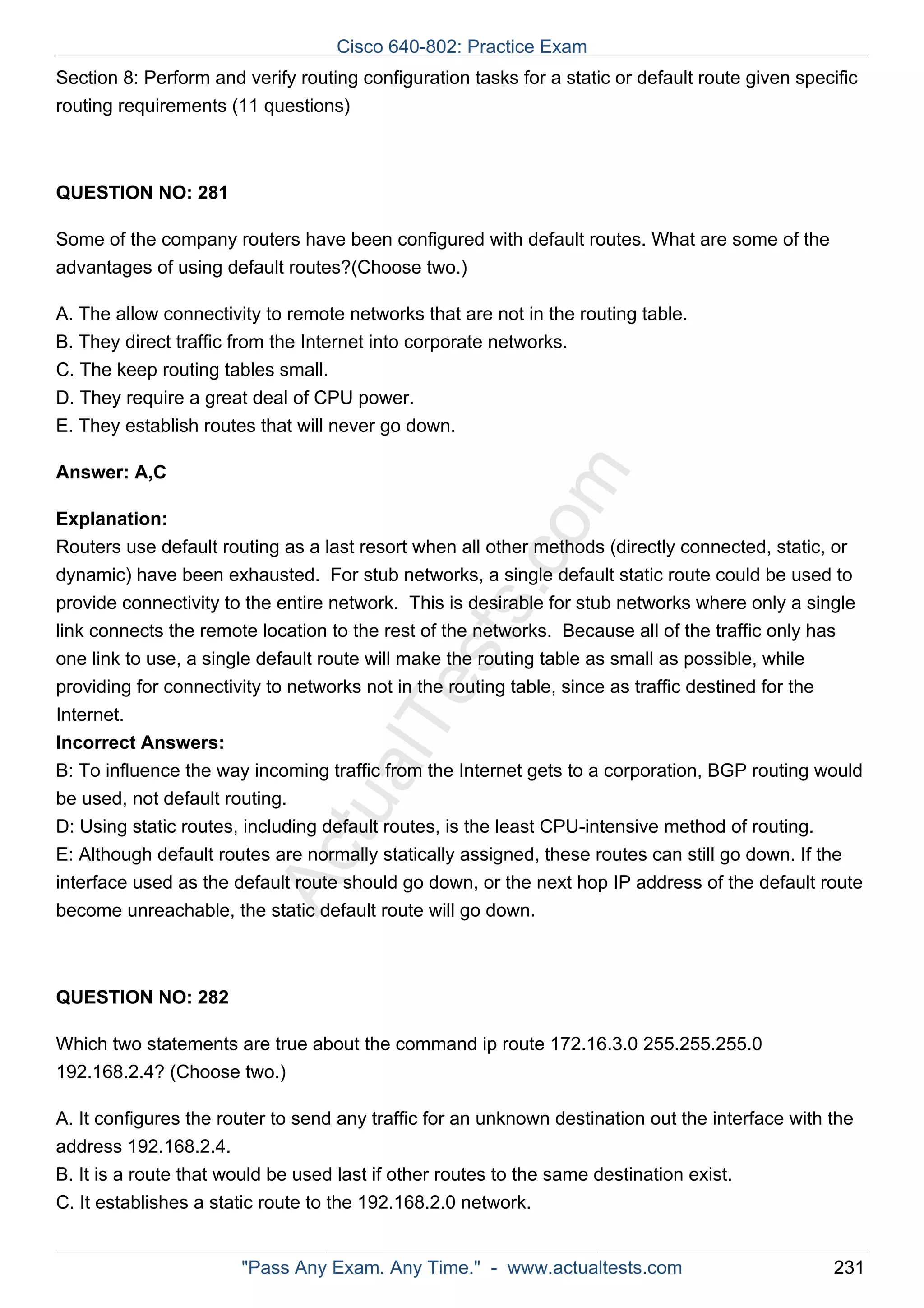
QUESTION NO: 283
You need to configure a default route on a router. Which command will configure a default route
on a router?
A. Router(config)# ip route 0.0.0.0 0.0.0.0 10.1.1.1
B. Router config)# ip default-gateway 10.1.1.0
C. Router(config)# ip default-route 10.1.1.0
D. Router(config)# ip route 0.0.0.0 10.1.1.0 10.1.1.1
Answer: A
Explanation:
The command "IP route 0.0.0.0 0.0.0.0 <ip-address of the interface>" command is used to
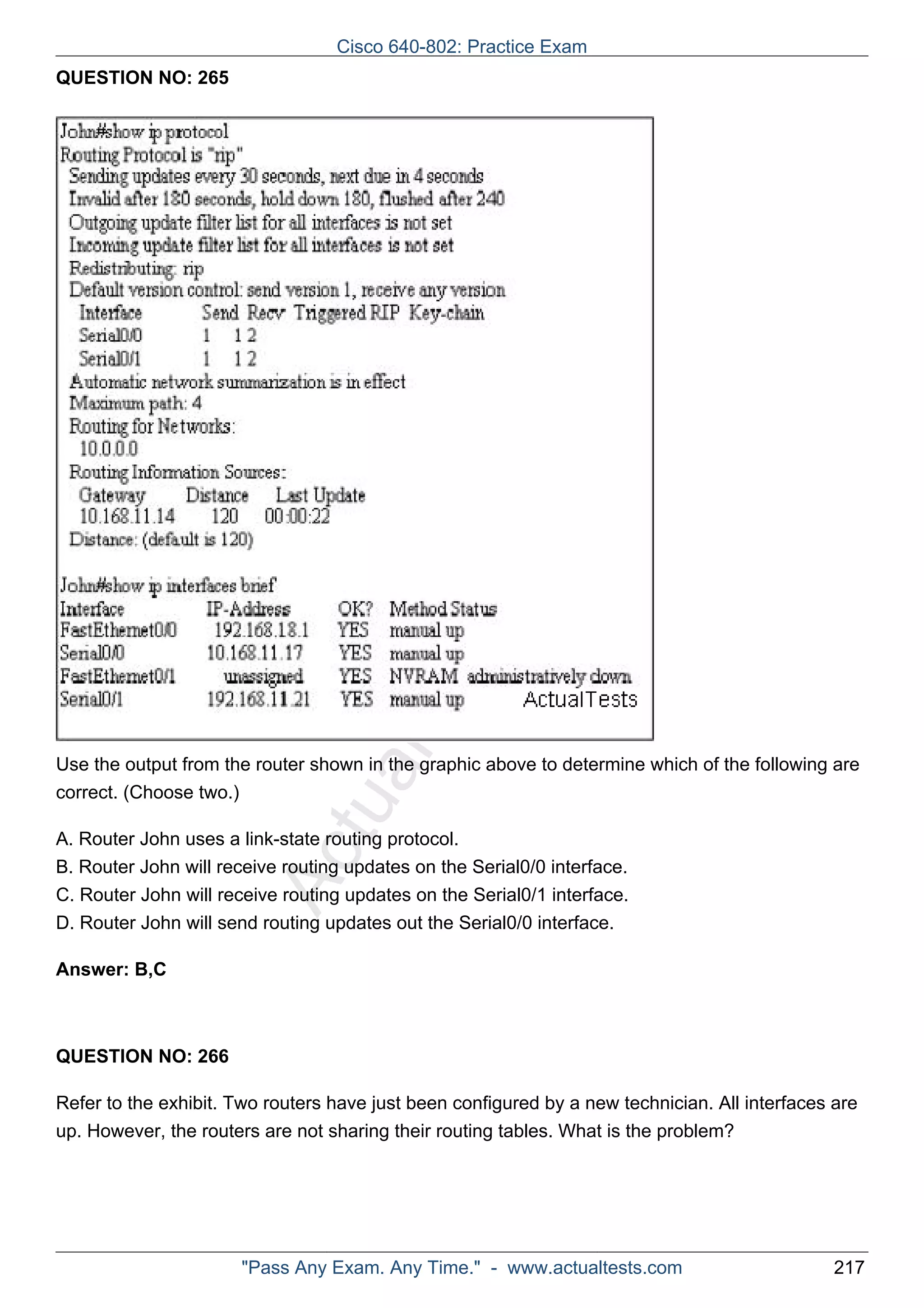
configure a default route on a router. In this case, a default route with a next hop IP address of
10.1.1.1 was configured.
Incorrect Answers:
B: These commands are invalid. The command "ip default-network" could be used, but not "ip
default-route" or "ip default-gateway". IP default-gateway is used on switches, not routers.
C: These commands are invalid. The command "ip default-network" could be used, but not "ip
default-route" or "ip default-gateway". IP default-gateway is used on switches, not routers.
D: This will be an invalid route, since the "10.1.1.0" value will specify the network mask, which in
this case is invalid.
"Pass Any Exam. Any Time." - www.actualtests.com 232](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-232-2048.jpg)


![Cisco 640-802: Practice Exam
ActualTests.com
A. It will hold the packet for 22 seconds.
B. It will forward the packet to 190.171.23.10.
C. It will forward the packet to 192.168.33.1.
D. It will forward the packet to 190.171.23.12.
E. It will discard the packet because there is no matching route.
F. It will hold the packet for 21 seconds.
Answer: C
Explanation:
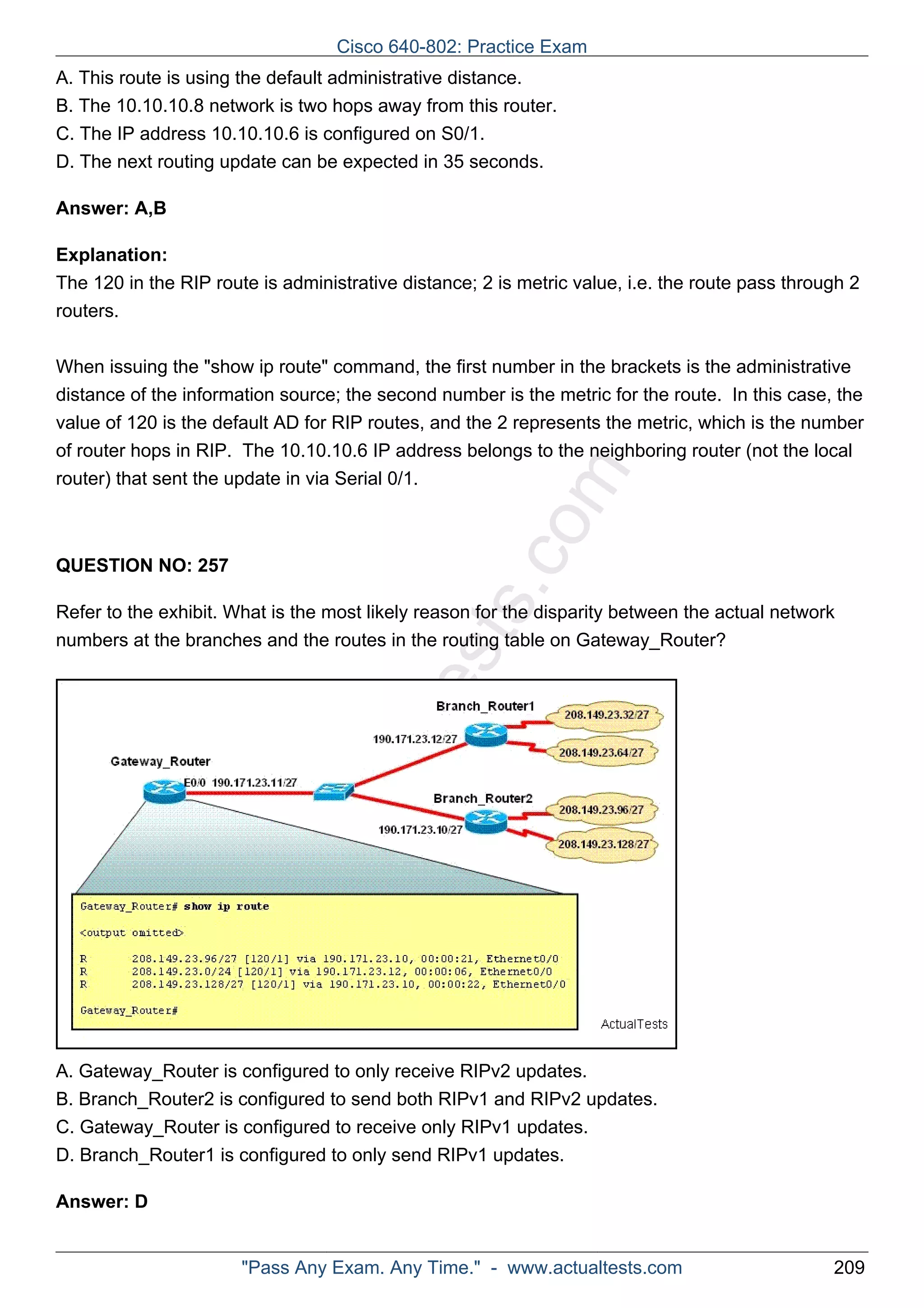
When the packet with the target address 208.149.23.91 reaches CentralRouter, CentralRouter
searches its routing table but cannot find the routing entry mapping 208.149.23.91, so the default
route is used:
S 0.0.0.0/0 [1/0] via 192.168.33.1
The packet is forwarded by CentralRouter to 192.168.33.1.
QUESTION NO: 287
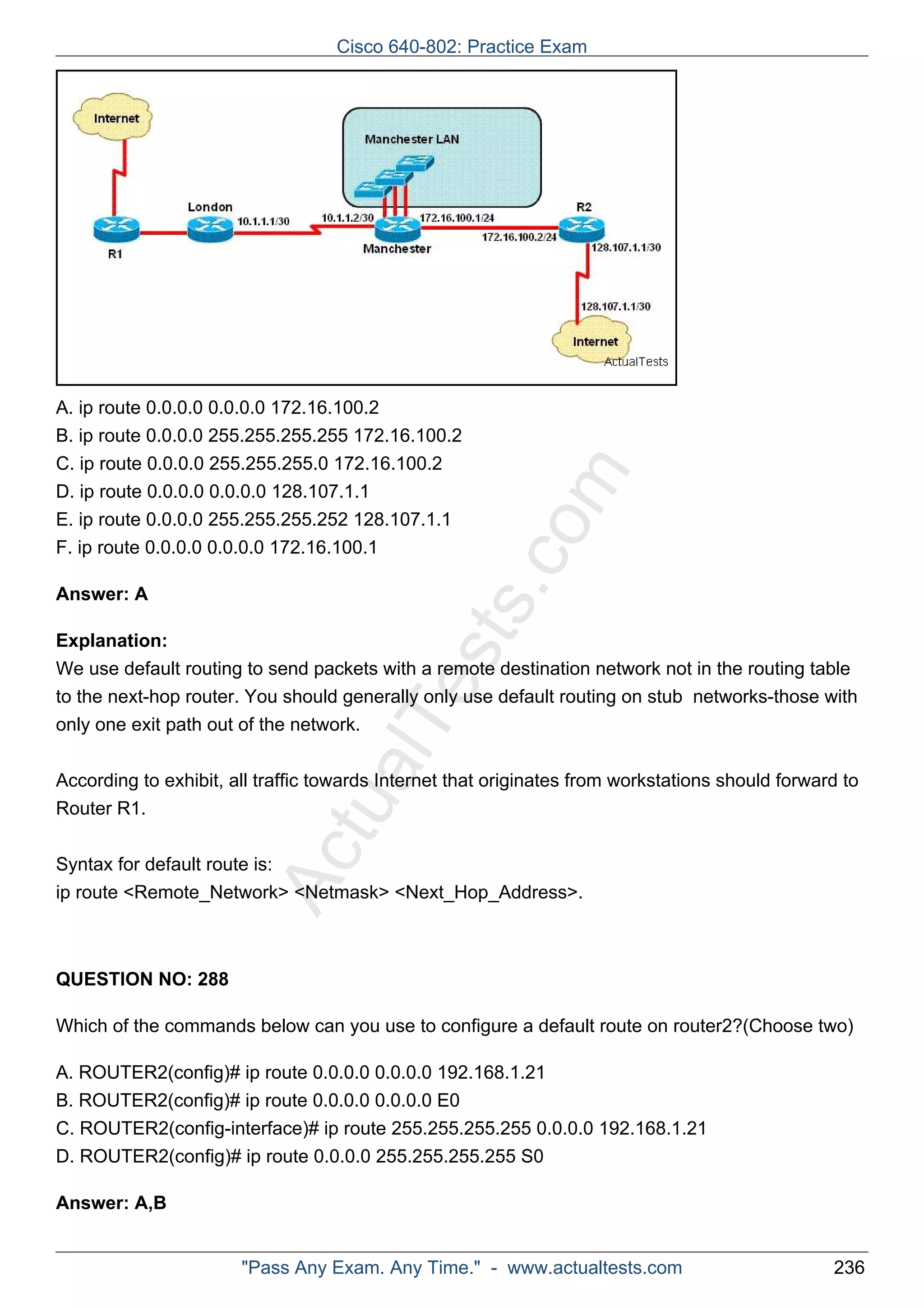
Refer to the exhibit. The speed of all serial links is E1 and the speed of all Ethernet links is 100
Mb/s. A static route will be established on the Manchester router to direct traffic toward the Internet
over the most direct path available. What configuration on the Manchester router will establish a
route toward the Internet for traffic that originates from workstations on the Manchester LAN?
"Pass Any Exam. Any Time." - www.actualtests.com 235](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-235-2048.jpg)
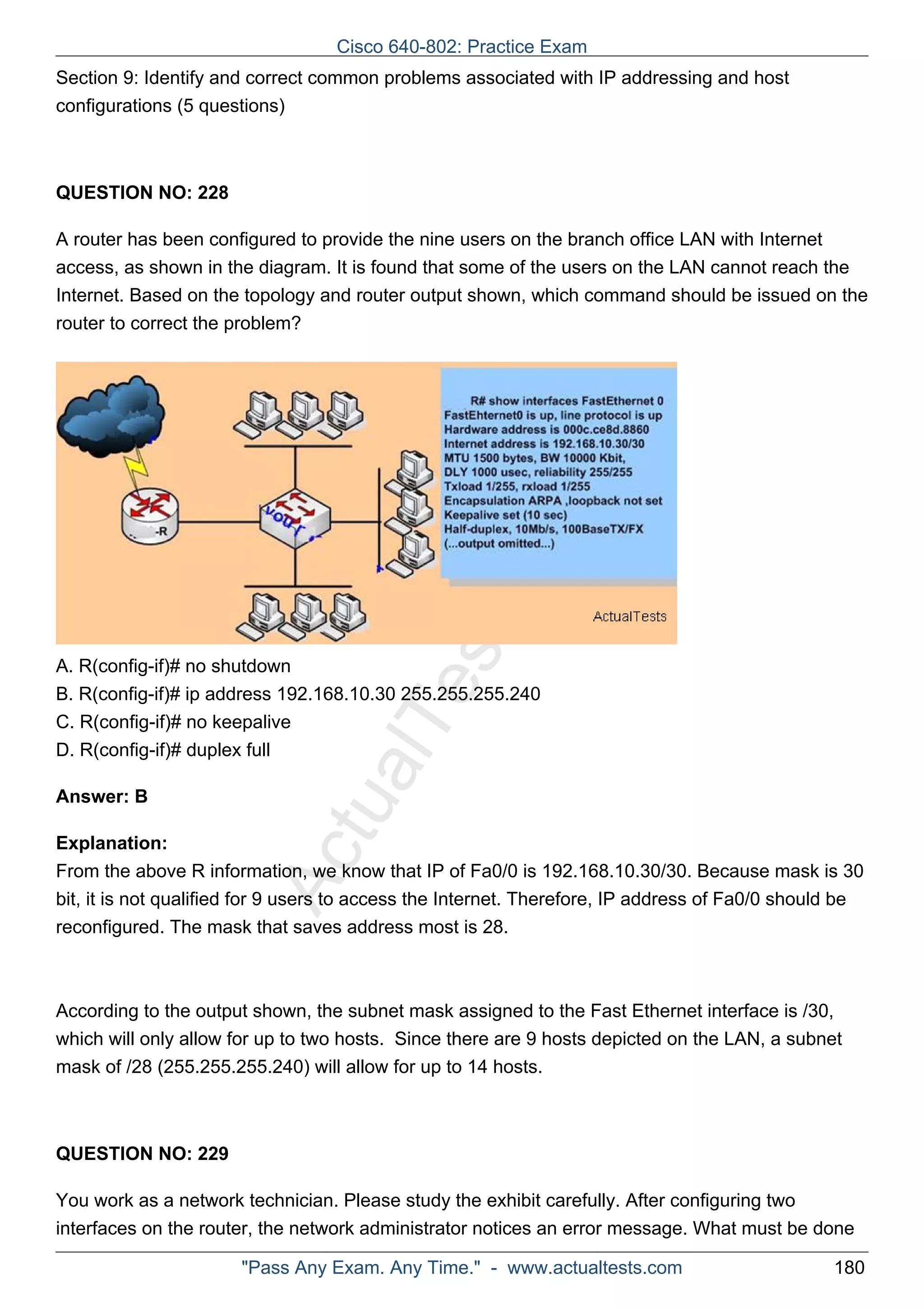
![Cisco 640-802: Practice Exam
Explanation:
There are two ways to specify a default static route. One is to specify the interface to use for
forwarding packets, like the example in A. The other way is to specify the IP address of the next
hop router, such as the example in D. The ip route 0.0.0.0 0.0.0.0 command uses the fact that
network 0.0.0.0 is used by Cisco IOS software to represent the default network.
Reference: CCNA ICND Exam Certification Guide By Wendell Odem Pg.524
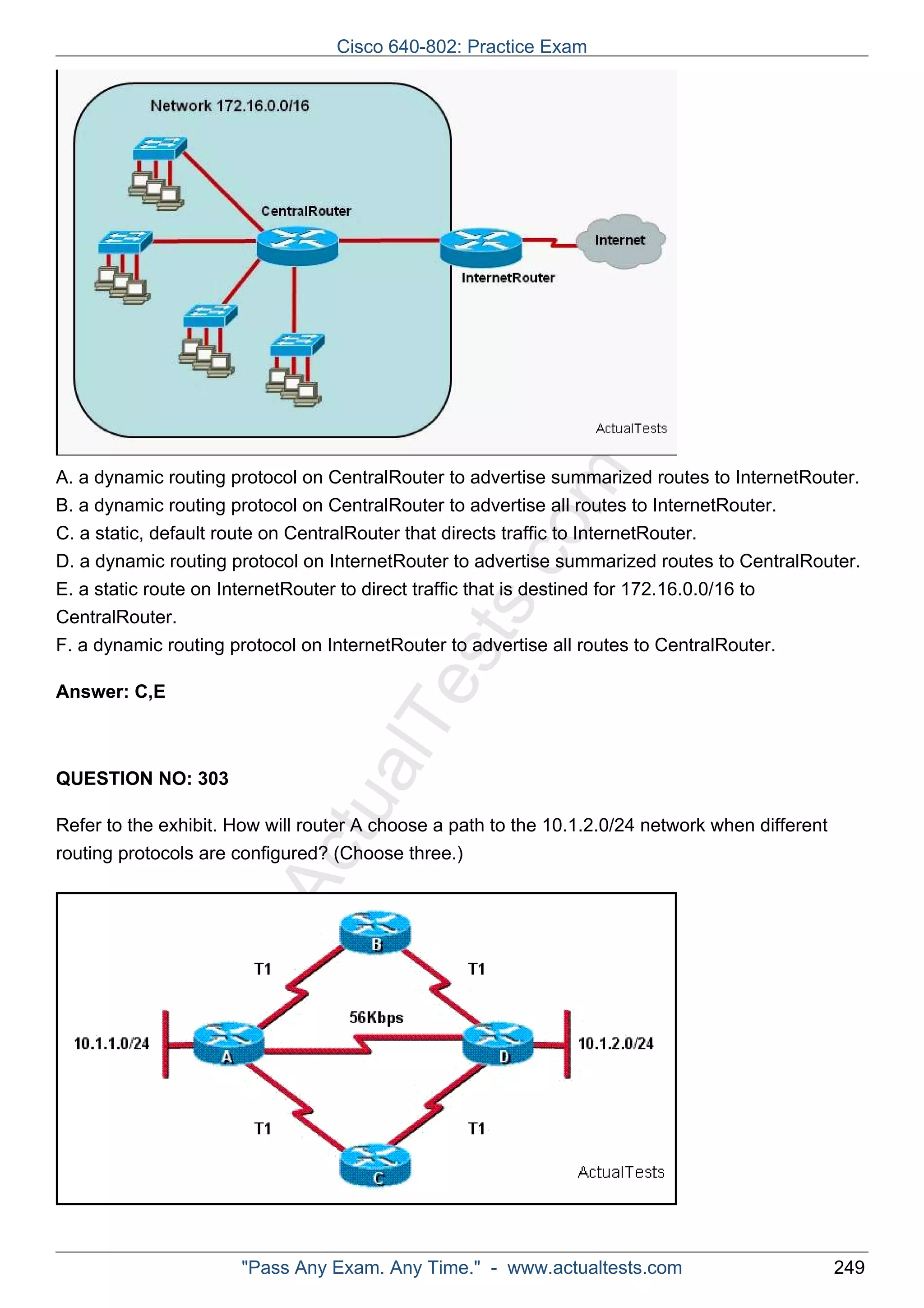
Incorrect Answers:
C: The default route is made in global configuration mode.
D: All zero's must used for the subnet mask of a default route, not all 1's.
ActualTests.com
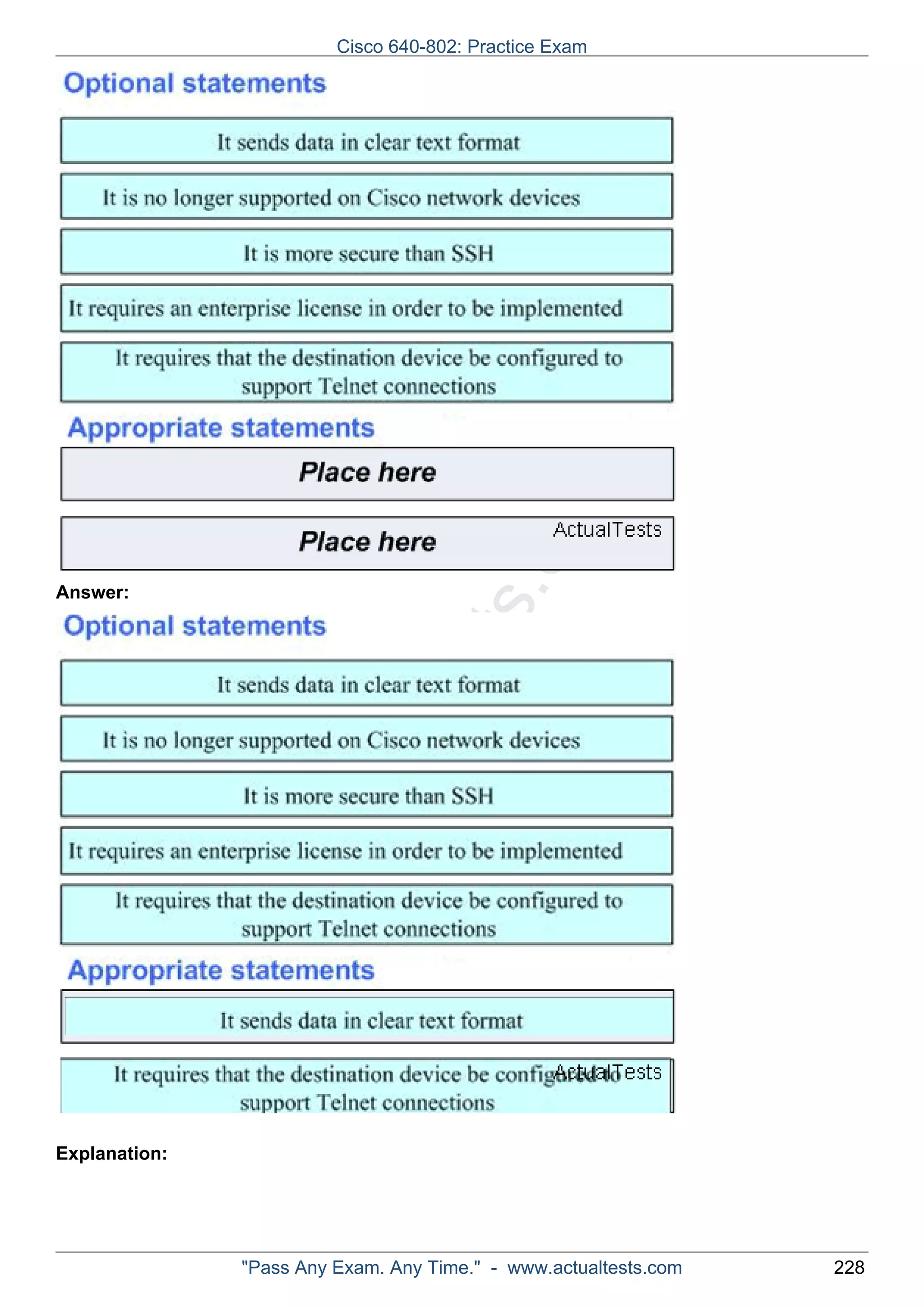
QUESTION NO: 289
Users on the 172.17.22.0 network cannot reach the server located on the 172.31.5.0 network. The
network administrator connected to router Coffee via the console port, issued the show ip route
command, and was able to ping the server. Based on the output of the show ip route command
and the topology shown in the graphic, what is the cause of the failure?
A. The neighbor relationship table is not correctly updated.
B. A static route is configured incorrectly.
C. The routing table on Coffee has not updated .
D. IP routing is not enabled.
E. The FastEthernet interface on Coffee is disabled.
F. The network has not fully converged.
Answer: B
Explanation:
The route S* 0.0.0.0[1/0]VIA 172.19.22.2 is not correct. We can infer that the static route is
configured incorrectly and the data cannot reach the external network from this address.
On the bottom line of the command output for 'show ip route' you can see that there is an asterisk
by the letter S. The S stands for static route, and the static route is incorrectly configured.
"Pass Any Exam. Any Time." - www.actualtests.com 237](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-237-2048.jpg)
![Cisco 640-802: Practice Exam
Incorrect Answers:
C: It appears that only a single static route is being used on the Coffee router. Neighbors do not
need to be established for static routes.
D: If this were true, then the users on the LAN would be unable to connect to anything outside of
their own network.
ActualTests.com
QUESTION NO: 290
The network administrator of the Oregon router adds the following command to the router
configuration: ip route 192.168.12.0 255.255.255.0 172.16.12.1. What are the results of adding
this command? (Choose two.)
A. Traffic for all networks is forwarded to 172.16.12.1.
B. This route is automatically propagated throughout the entire network.
C. Traffic for network 172.16.12.0 is forwarded to the 192.168.12.0 network.
D. Traffic for network 192.168.12.0 is forwarded to 172.16.12.1.
E. The command establishes a static route.
F. The command invokes a dynamic routing protocol for 192.168.12.0.
Answer: D,E
Explanation:
In order to configure a static route the router has to be in global configuration mode.
ip route network prefix mask {address | interface} [distance]
network - the destination network
mask - is the subnet mask for that network
address - IP address of the next hop router
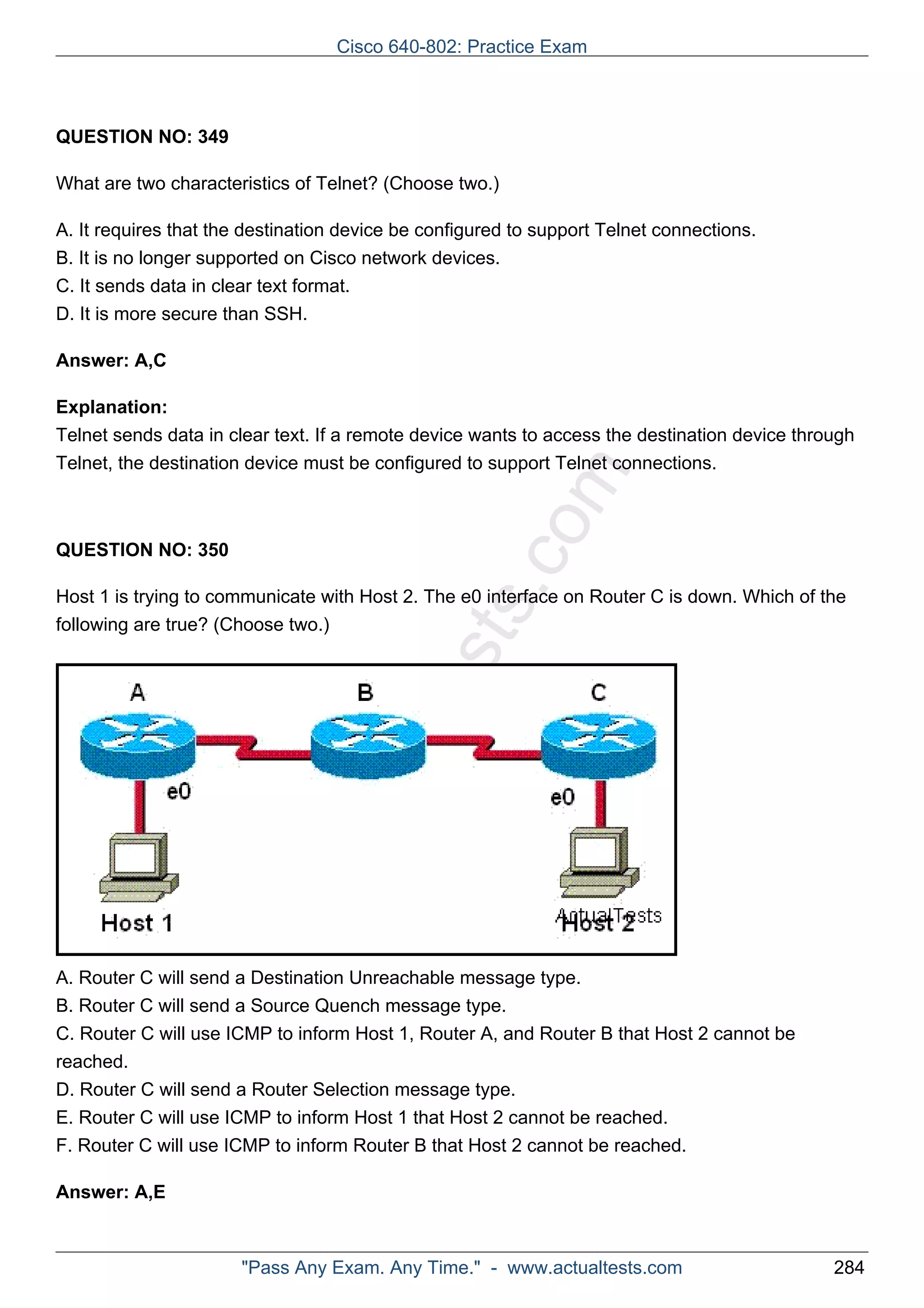
interface - or the interface the traffic is to leave by
distance - (optional) the administrative distance of the route
There are other parameters but these have been removed as they are not relevant to the CCNA
exam.
In order to configure a static route the router has to be in global configuration mode. ip route
network prefix mask { address | interface } [ distance ] network - the destination network mask -
is the subnet mask for that network address - IP address of the next hop router interface - or the
"Pass Any Exam. Any Time." - www.actualtests.com 238](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-238-2048.jpg)

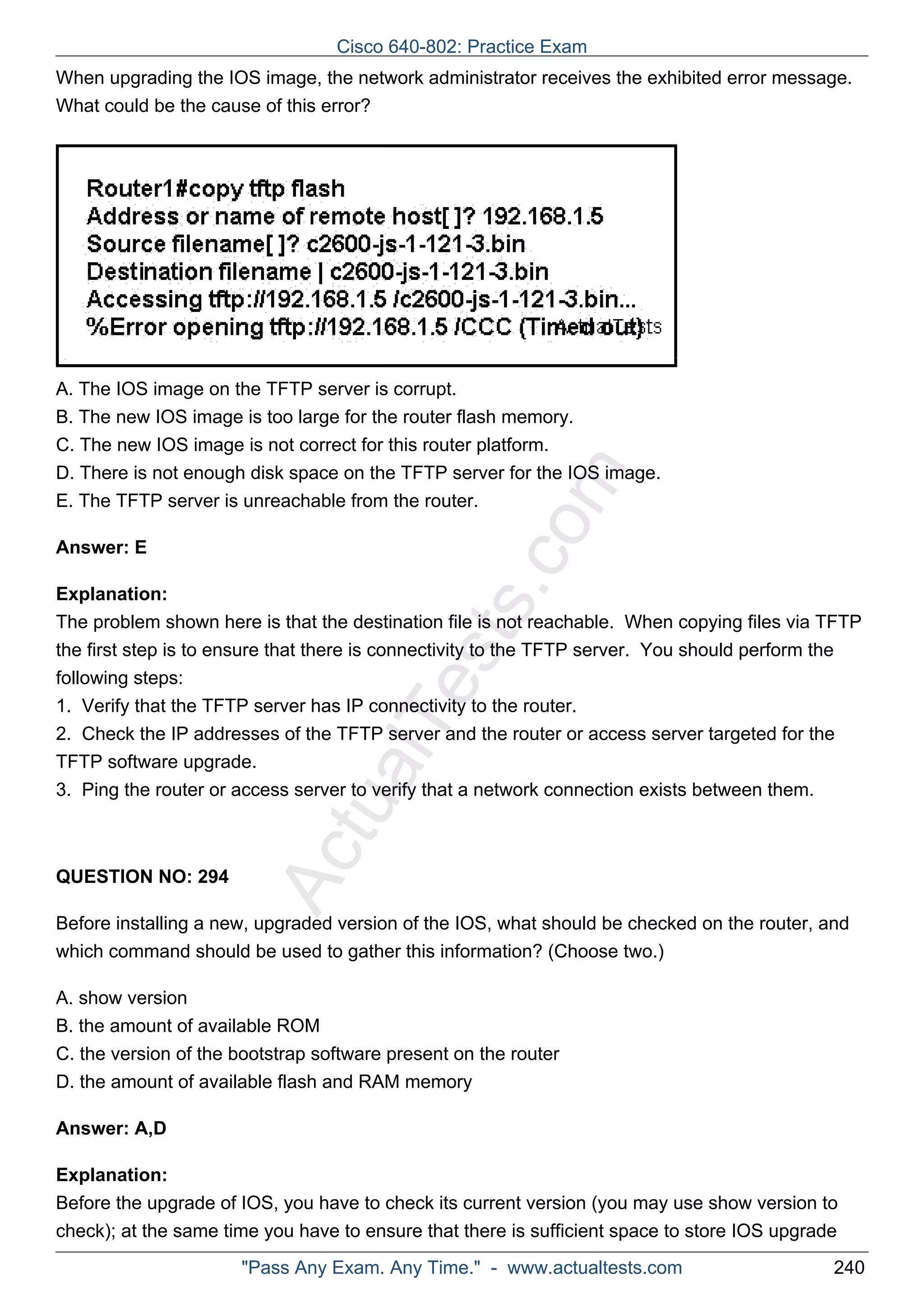
![Cisco 640-802: Practice Exam
ActualTests.com
QUESTION NO: 297
Which of the commands below would you enter if you wanted to see the configuration register of
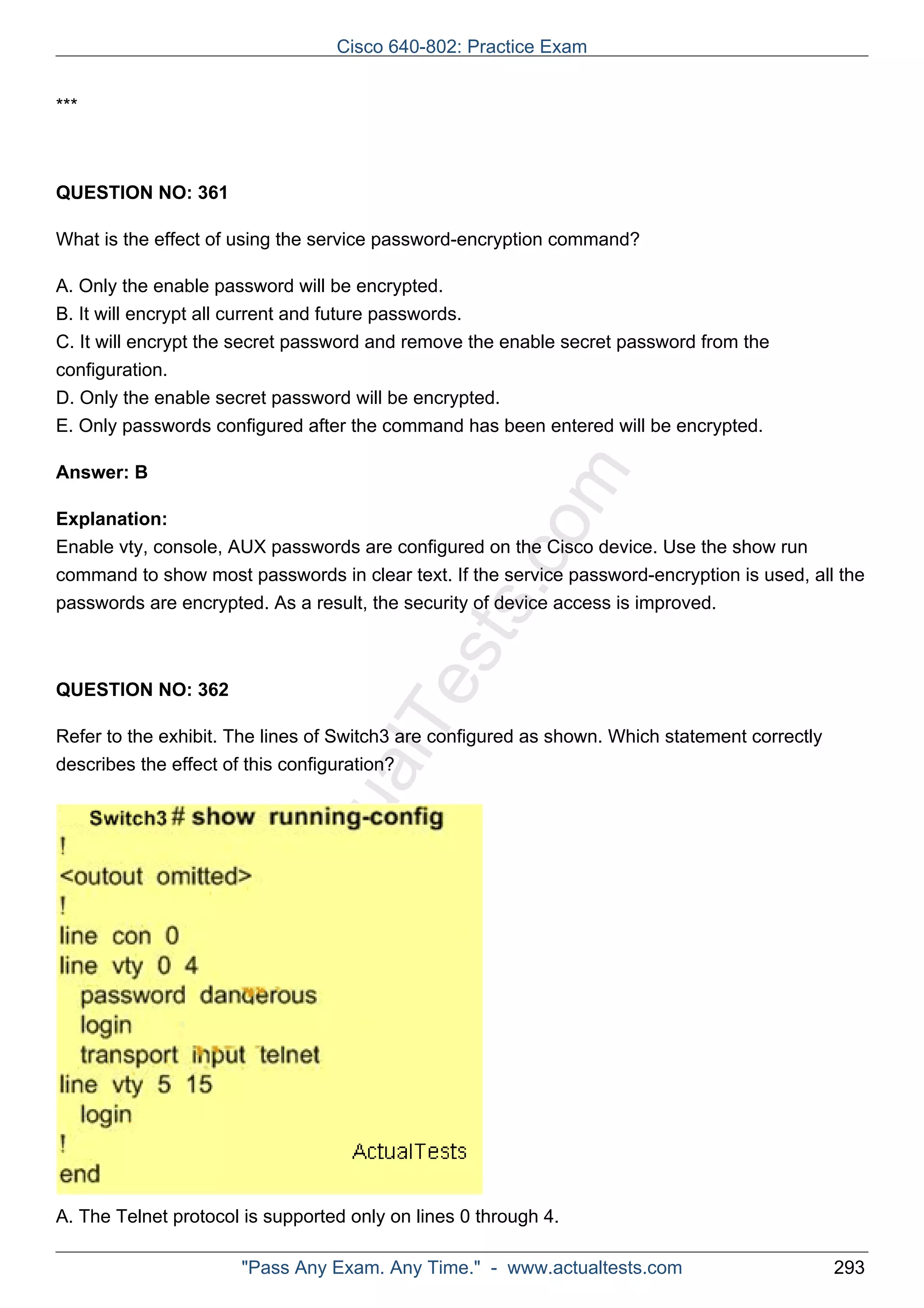
your router?
A. show boot
B. show version
C. show register
D. show config
E. show flash
Answer: B
Explanation:
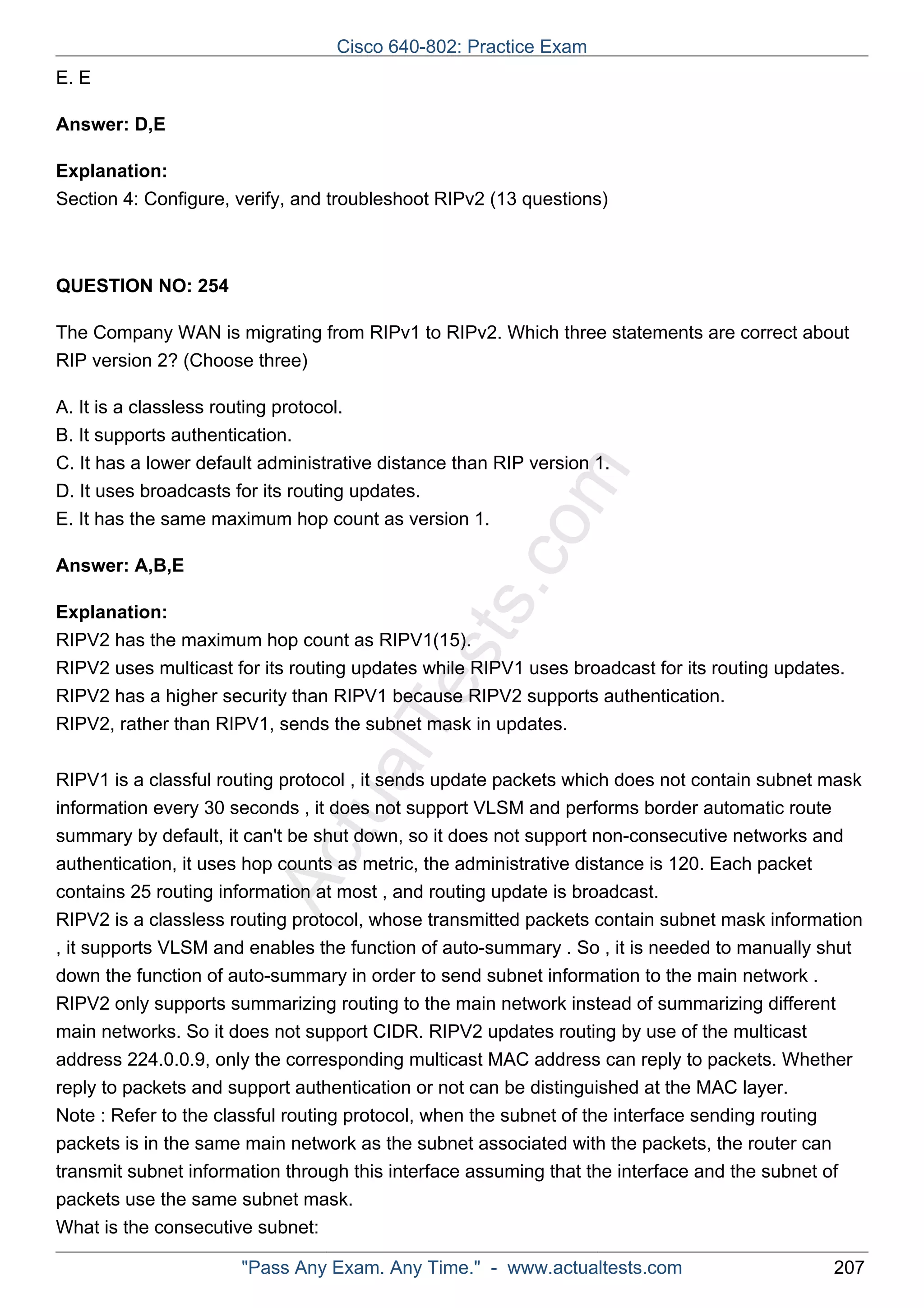
To display the configuration of the system hardware, the software version, the names and sources
of configuration files, and the boot images, use the show version command in EXEC mode.
Example:
The following is sample output from the show version command:
Router1> show version
Cisco Internetwork Operating System Software
IOS (tm) 7200 Software (C7200-J-M), Experimental Version 11.3(19970915:164752) [
hampton-nitro-baseline 249]
Copyright (c) 1986-1997 by cisco Systems, Inc.
Compiled Wed 08-Oct-97 06:39 by hampton
Image text-base: 0x60008900, data-base: 0x60B98000
ROM: System Bootstrap, Version 11.1(11855) [beta 2], INTERIM SOFTWARE
BOOTFLASH: 7200 Software (C7200-BOOT-M), Version 11.1(472), RELEASE
Router1 uptime is 23 hours, 33 minutes
cisco 7206 (NPE150) processor with 57344K/8192K bytes of memory.
R4700 processor, Implementation 33, Revision 1.0 (512KB Level 2 Cache)
Last reset from power-on
Bridging software.
X.25 software, Version 3.0.0.
SuperLAT software copyright 1990 by Meridian Technology Corp).
TN3270 Emulation software.
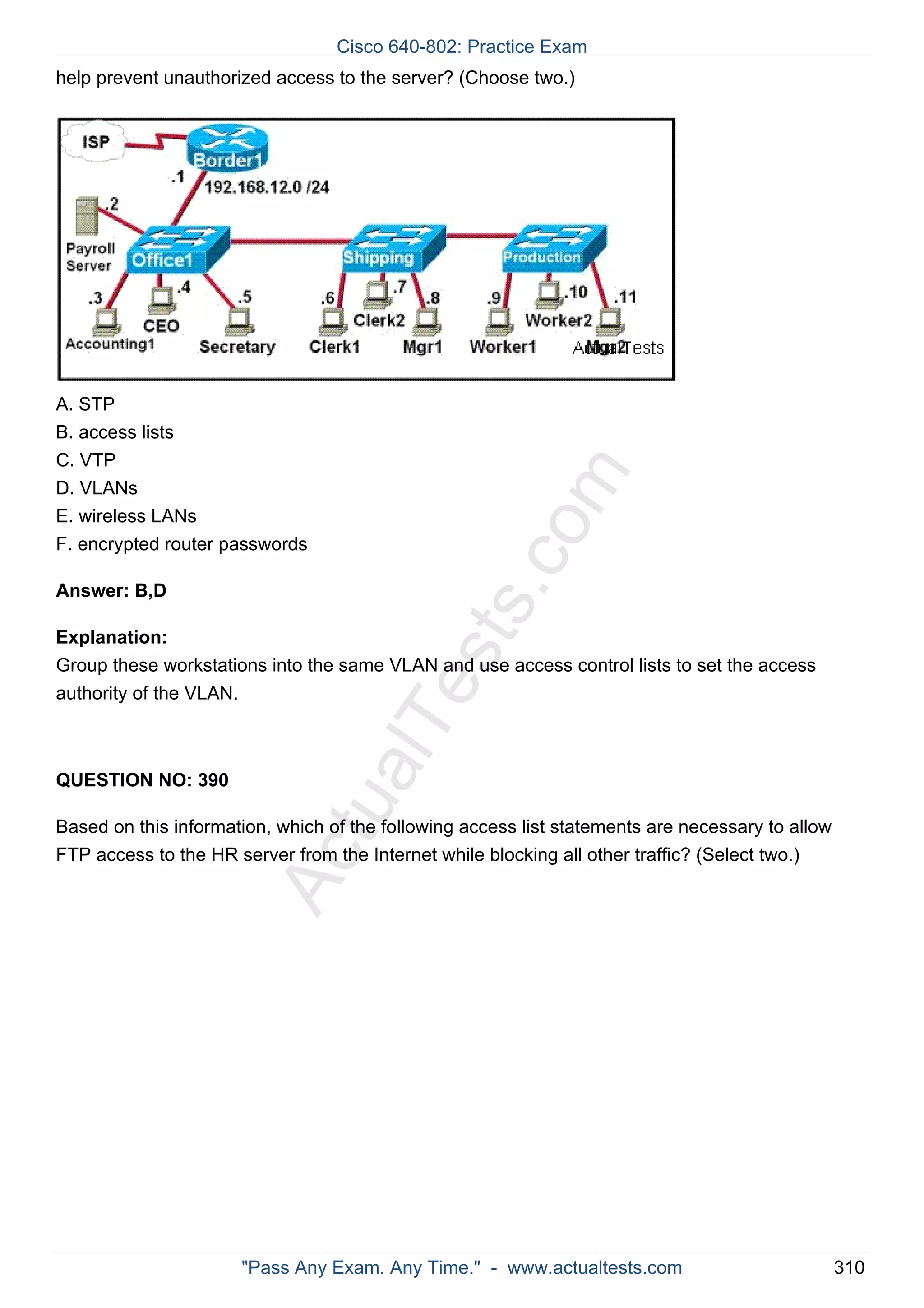
8 Ethernet/IEEE 802.3 interface(s)
2 FastEthernet/IEEE 802.3 interface(s)
4 Token Ring/IEEE 802.5 interface(s)
4 Serial network interface(s)
1 FDDI network interface(s)
125K bytes of non-volatile configuration memory.
1024K bytes of packet SRAM memory.
20480K bytes of Flash PCMCIA card at slot 0 (Sector size 128K).
"Pass Any Exam. Any Time." - www.actualtests.com 243](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-243-2048.jpg)
![20480K bytes of Flash PCMCIA card at slot 1 (Sector size 128K).
4096K bytes of Flash internal SIMM (Sector size 256K).
ActualTests.com
QUESTION NO: 298
You are a trainee technician. Your instructor tells you to backup an IOS image of a Cisco device to
a Windows 2003 server on the network. What should you do first? (Choose three)
A. Assure that the network server has adequate space for the code image.
B. Make sure that the network server can be accessed.
C. Verify any file naming and path requirements.
D. Check that the authentication for access is set.
Answer: A,B,C
Explanation:
More often than not, when backing up IOS files, first , using the command PING to test whether
the server is reachable or not and whether the server has enough space to store the IOS backup
files or not. When the two needs are satisfied, you can use the command "copy flash tftp" to
backup on the router.
Router>enable
Router#copy flash tftp
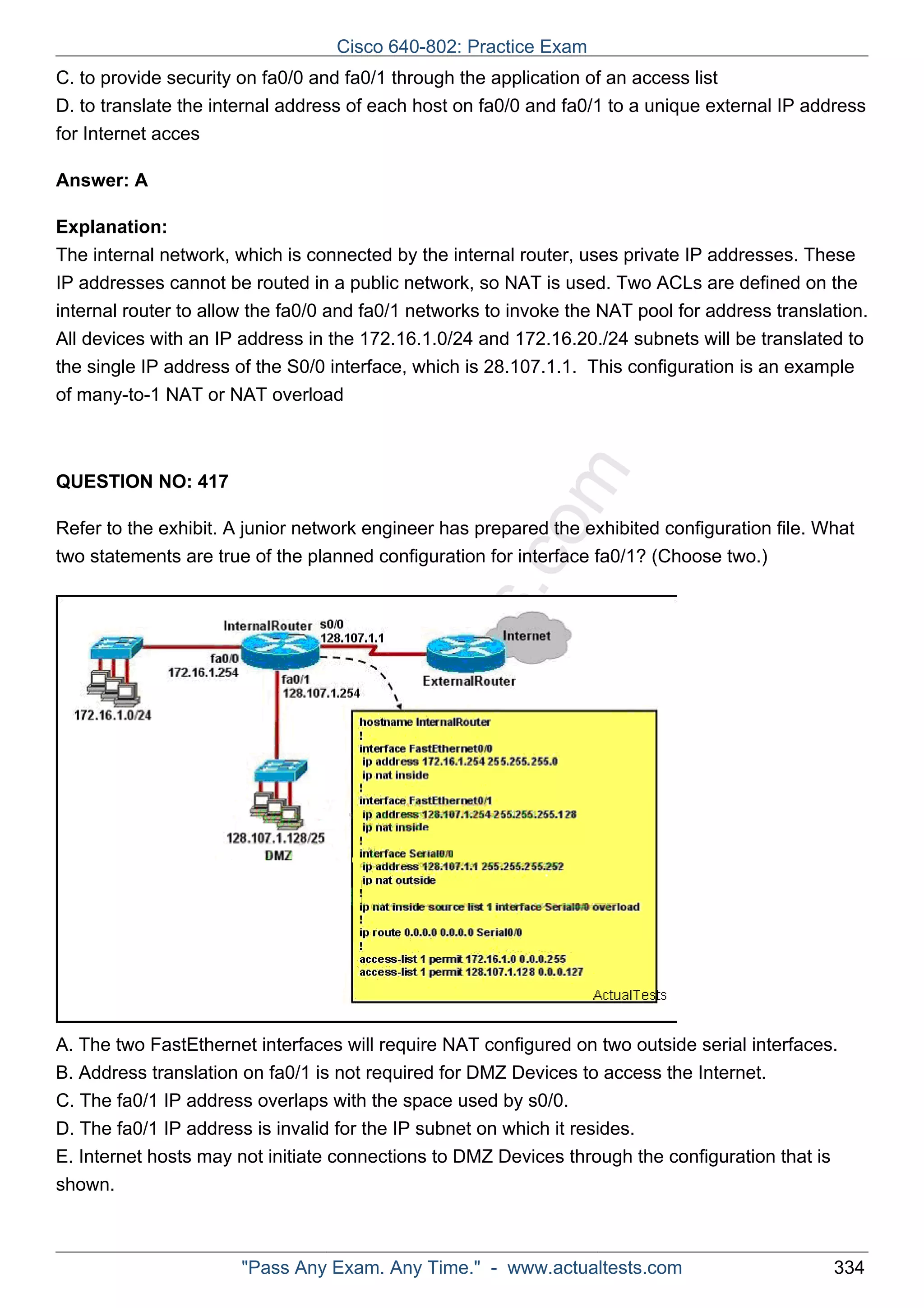
ip address of remote host:[255.255.255.255]?129.0.0.3
filename to write on tftp hose?c4500-l
writing c4500-l !!!!!!!!!!!!!!!!!!!!!!!!
successful tftp write
After inputting the command "copy flash tftp", the router will require you to input the IP address of
the remote TFTP server and IOS mapping name of the server. The router will remind you that
backup is successfully completed by a string of exclamation points.
In order to properly back up the Cisco IOS image onto a Windows server, you should ensure that
the server is reachable and that you have the proper permissions to save files to the server. In
addition to this, the server will need enough space to hold the backup file.
QUESTION NO: 299
You wish to upgrade the IOS of a router without removing the image currently installed. What
command will display the amount of memory that is being used by the current IOS image and
whether there is enough room available to hold both the current and new images?
A. Router# show version
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 244](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-244-2048.jpg)







































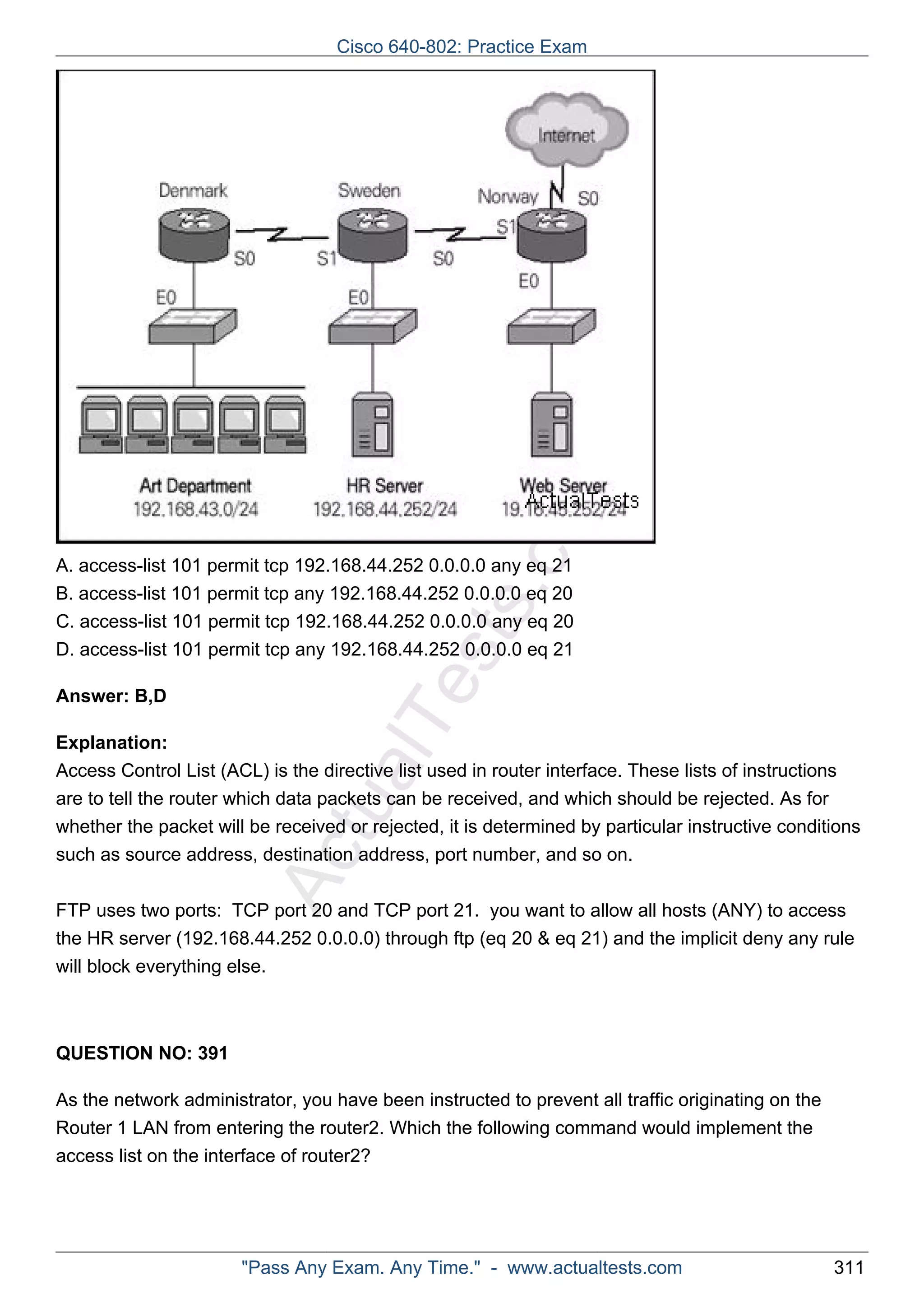


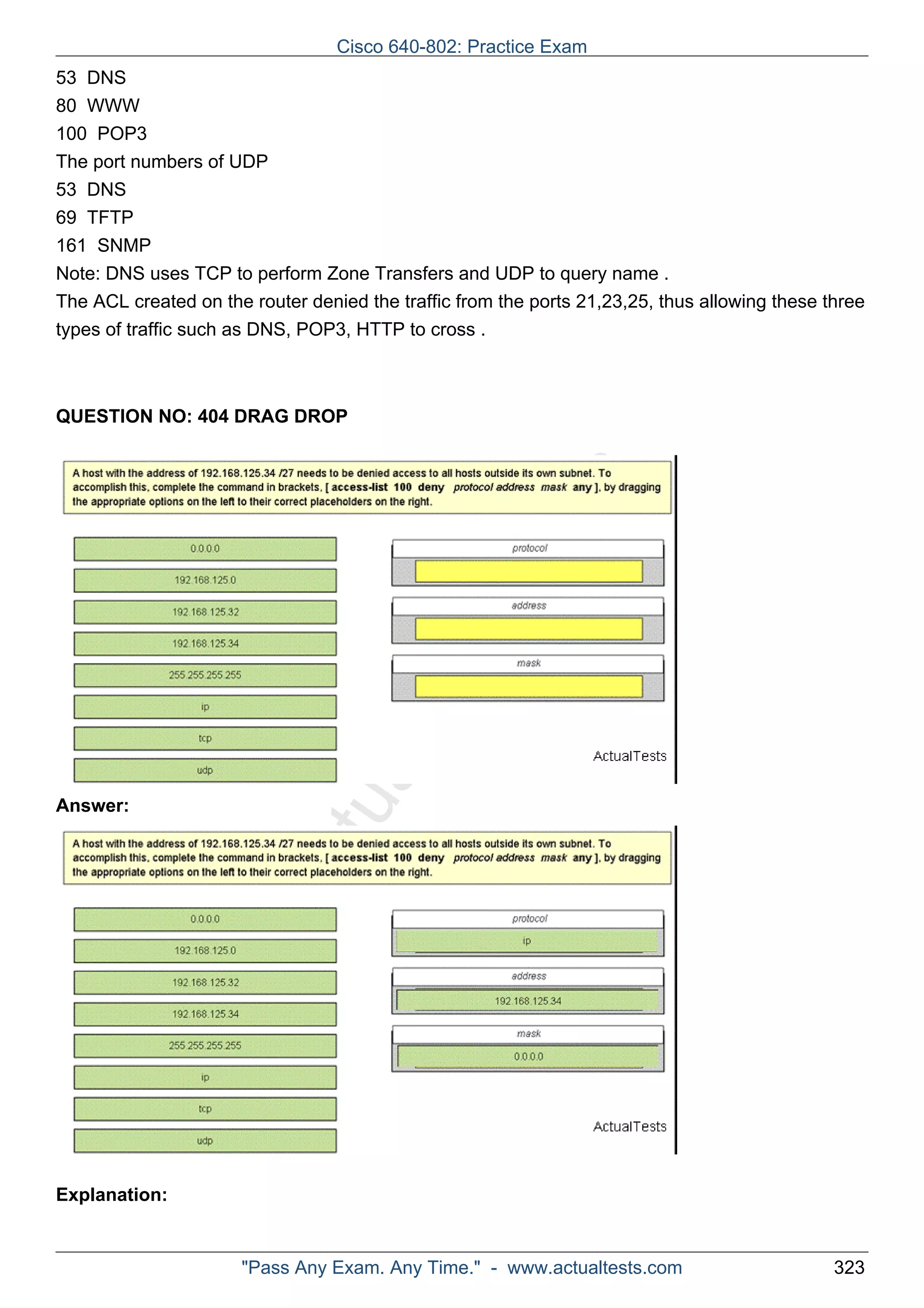
![Cisco 640-802: Practice Exam
method on the basis of savings routing resources. However, in the examination environment,
please complete the steps of answering questions according to options provided. We remind you
that the examination environment and the actual environment are not exactly the same.
To block communication between Workstation A and Server 1, we have to configure Extended
Access List.
To define an extended IP access list, use the extended version of the access-list command in
global configuration mode. To remove the access lists, use the no form of this command.
access-list access-list-number [dynamic dynamic-name [timeout minutes]] {deny | permit} protocol
source source-wildcard destination destination-wildcard
ActualTests.com
Source Address will be of the Workstation A i.e. 172.16.161.150 and destination address will be of
the Server 1 i.e. 172.16.162.163.
The access list will be placed on the FA0/0 of Router Router1.
QUESTION NO: 394
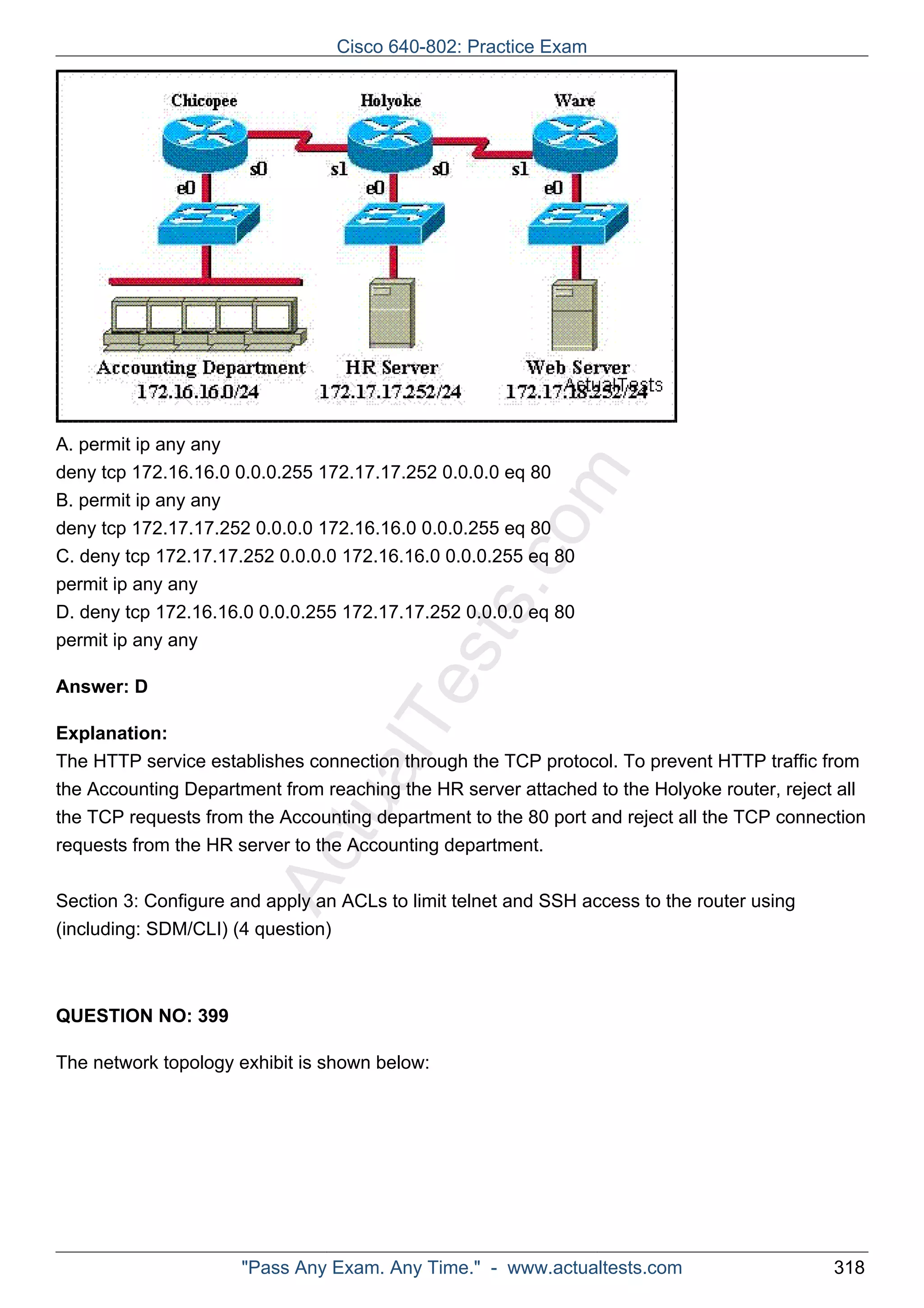
Refer to the graphic. Assuming the following goals:
1) allow Telnet from the Internet to the HR server
2) allow HTTP access from the Internet to the web server
3) all other traffic from the Internet should be blocked
Which of the following access list statements are necessary to accomplish these goals? (Select
two.)
"Pass Any Exam. Any Time." - www.actualtests.com 314](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-314-2048.jpg)






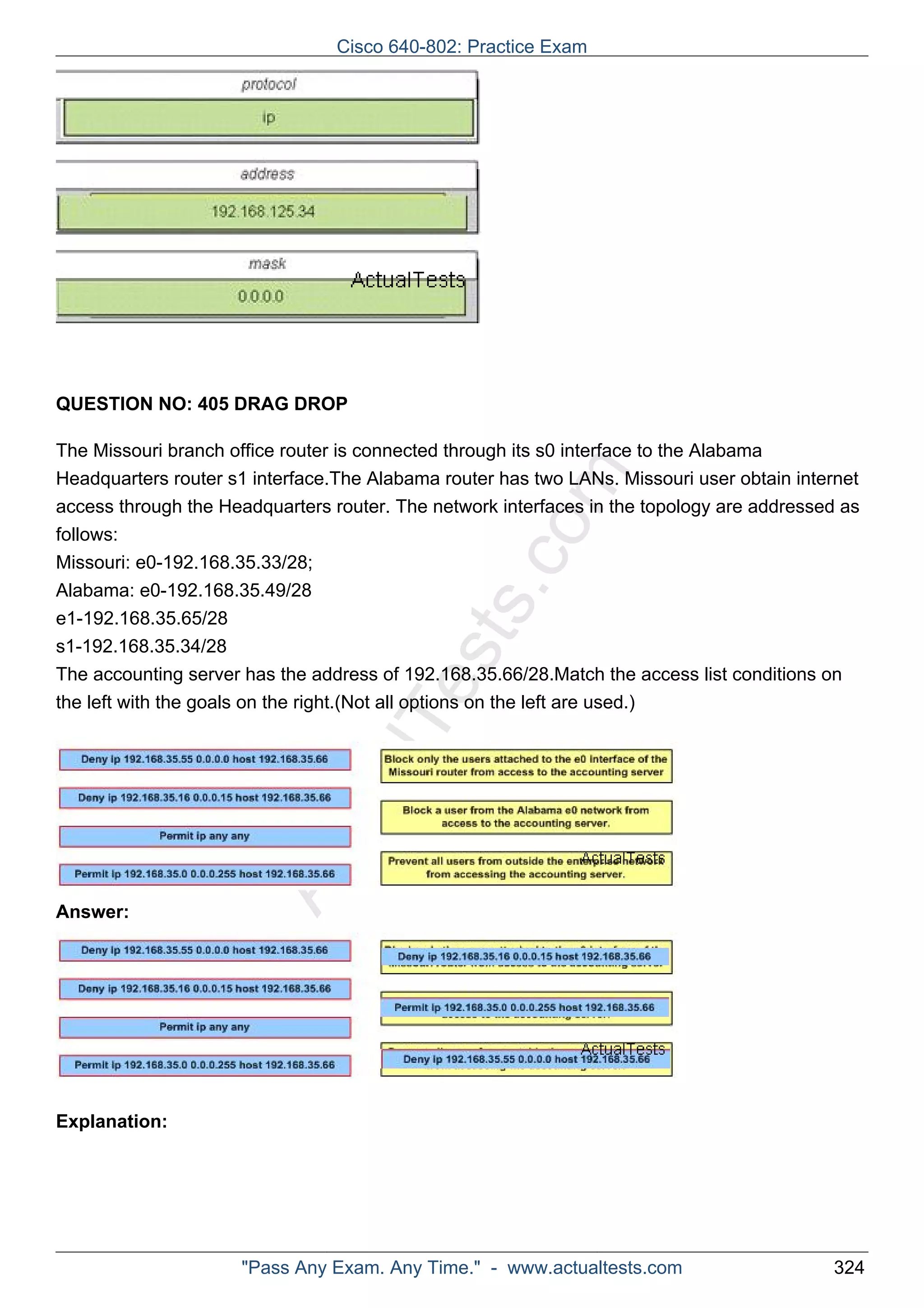

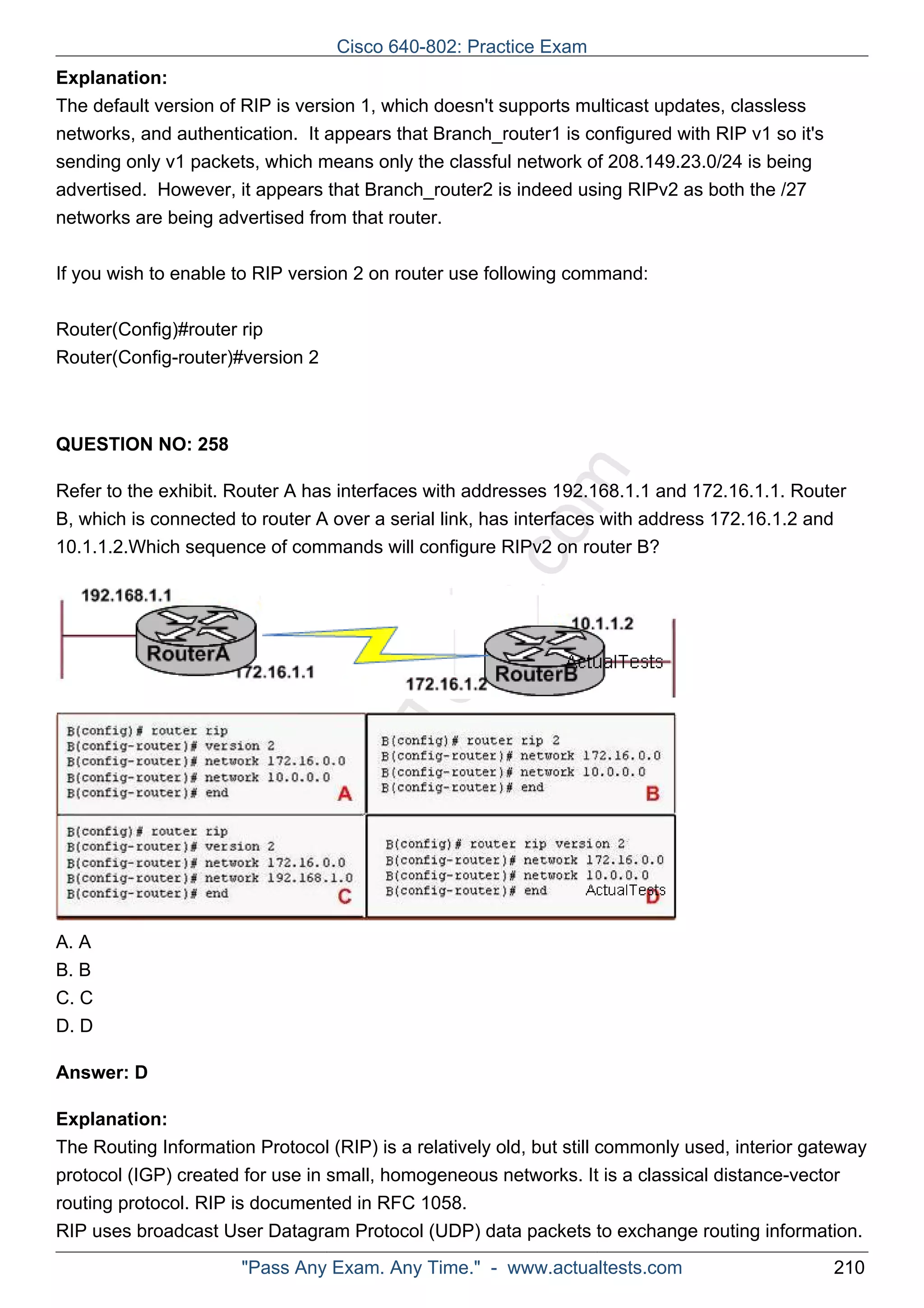
![Cisco 640-802: Practice Exam
ActualTests.com
QUESTION NO: 409
Which command shows if an access list is assigned to an interface?
A. show ip interface [interface] access-lists
B. show ip access-lists interface [interface]
C. show ip interface [interface]
D. show ip access-lists [interface]
Answer: C
Explanation:
Section 5: Troubleshoot ACL issues (2 question)
QUESTION NO: 410
What is the effect of the following access list condition?
access-list 101 permit ip 10.25.30.0 0.0.0.255 any
A. permit all packets matching the host bits in the source address to all destinations
B. permit all packets from the third subnet of the network address to all destinations
C. permit all packets matching the last octet of the destination address and accept all source
addresses
D. permit all packets to destinations matching the first three octets in the destination address
E. permit all packets matching the first three octets of the source address to all destinations
Answer: E
Explanation:
Standard IP Access Control Lists: a Standard IP Access Control List will match the source address
or part of the source address within IP packet; it may refuse or allow the matched packet. The
Access Control List with No. range from 1 to 99 is the Standard IP Access Control List. Extended
IP Access Control List: Extended IP Access Control List has more matching options than Standard
IP Access Control Lists, including protocol type, source address, destination address, source end,
destination end, connections establishing and IP priority, and so on. The access control list with
No. range from 100 to 199 is Extended IP Access Control Lists. Named IP Access Control Lists:
Named IP Access Control List is so called because list name is used instead of list number upon
the definition of IP Access Control Lists.
"Pass Any Exam. Any Time." - www.actualtests.com 327](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-327-2048.jpg)
























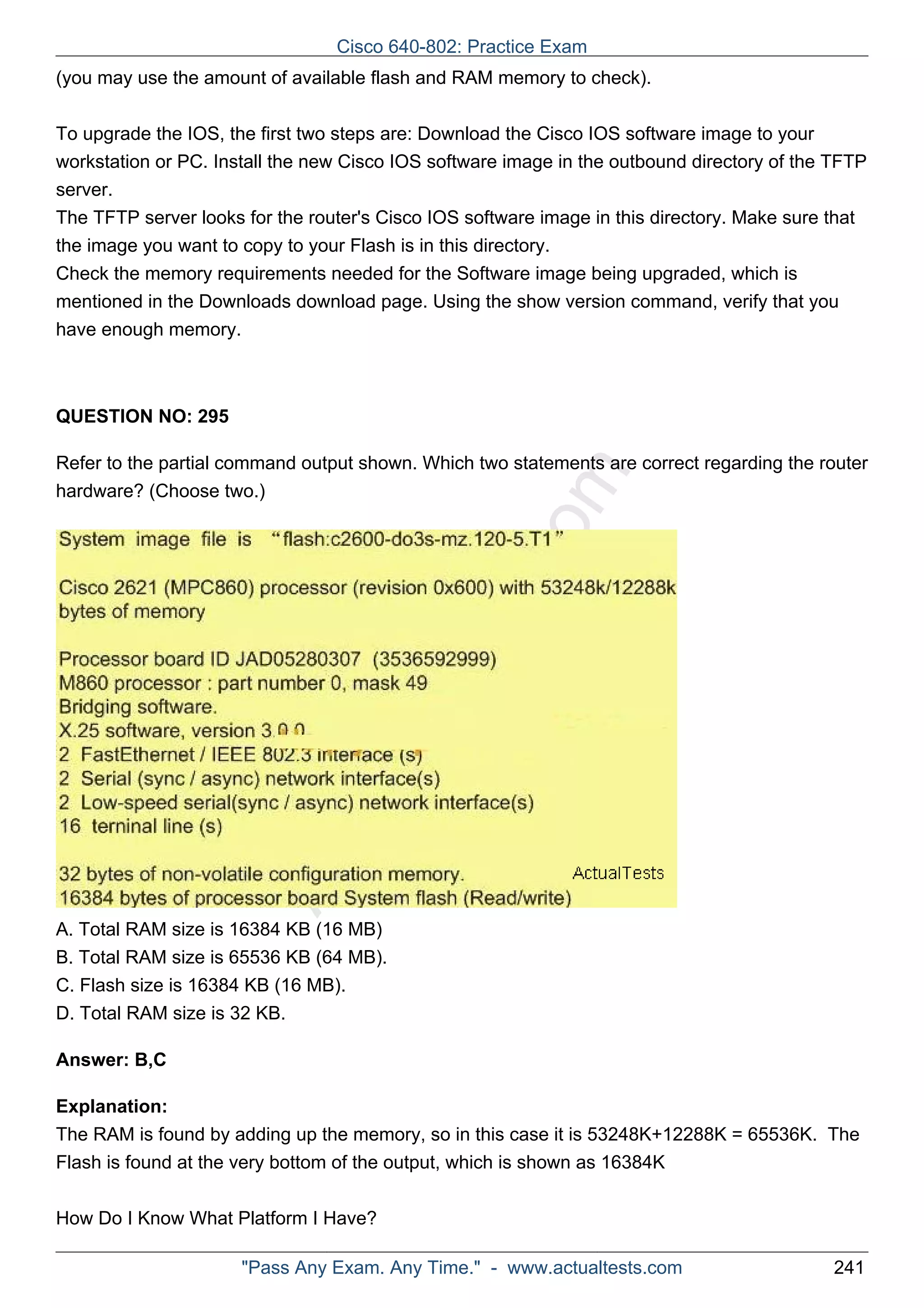
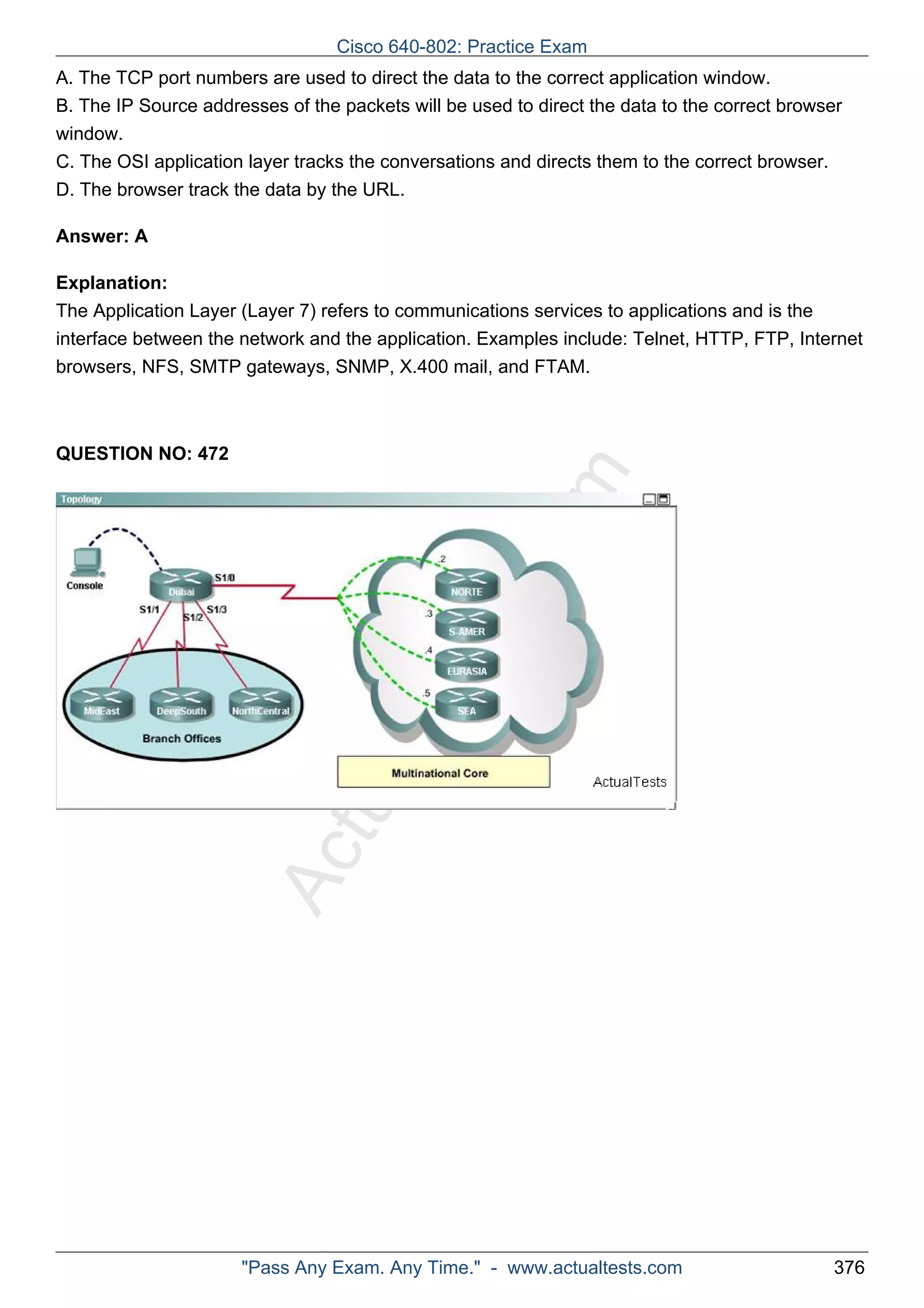
![Cisco 640-802: Practice Exam
ActualTests.com
Answer: B
Explanation:
In order to allow the network of 192.168.1.0/24 to access Serverl1, we need to establish a default
route. The format of this default route is as follows:
ip route prefix mask {ip-address interface-type interface-number [ip-address]} [distance] [name]
[permanent track number] [tag tag]
Based on the request of this subject, we need to configure the correct route as follows:
ip route 0.0.0.0 0.0.0.0 s0/0/0
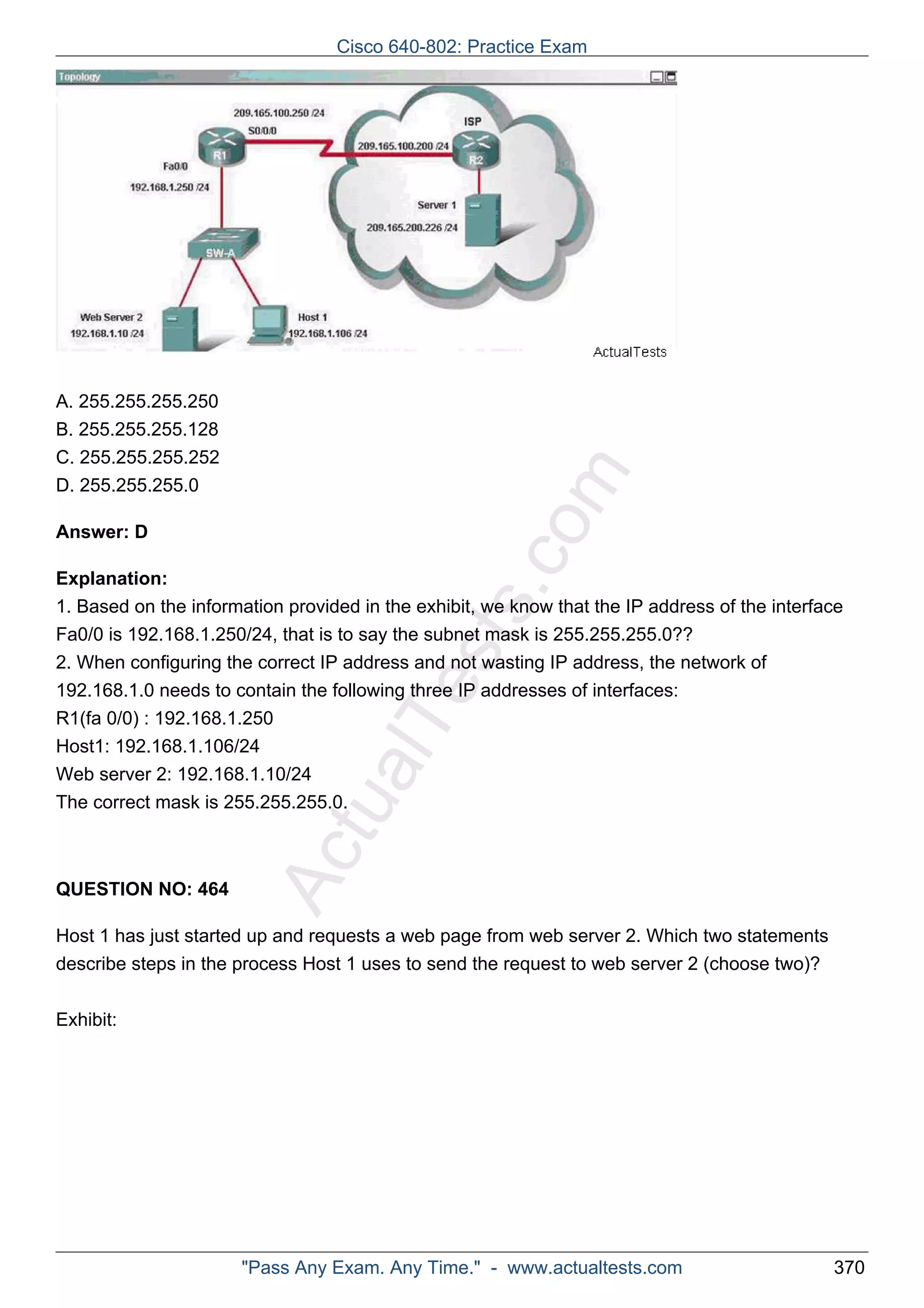
QUESTION NO: 466
What must be configured on the network in order for users on the Internet to view web pages
located on Web Server 2?
A. On router R1, configure a default static route to the 192.168.1.0 network.
B. On router R1, configure NAT to translate an address on the 209.165.100.0/24 network to
192.168.1.10
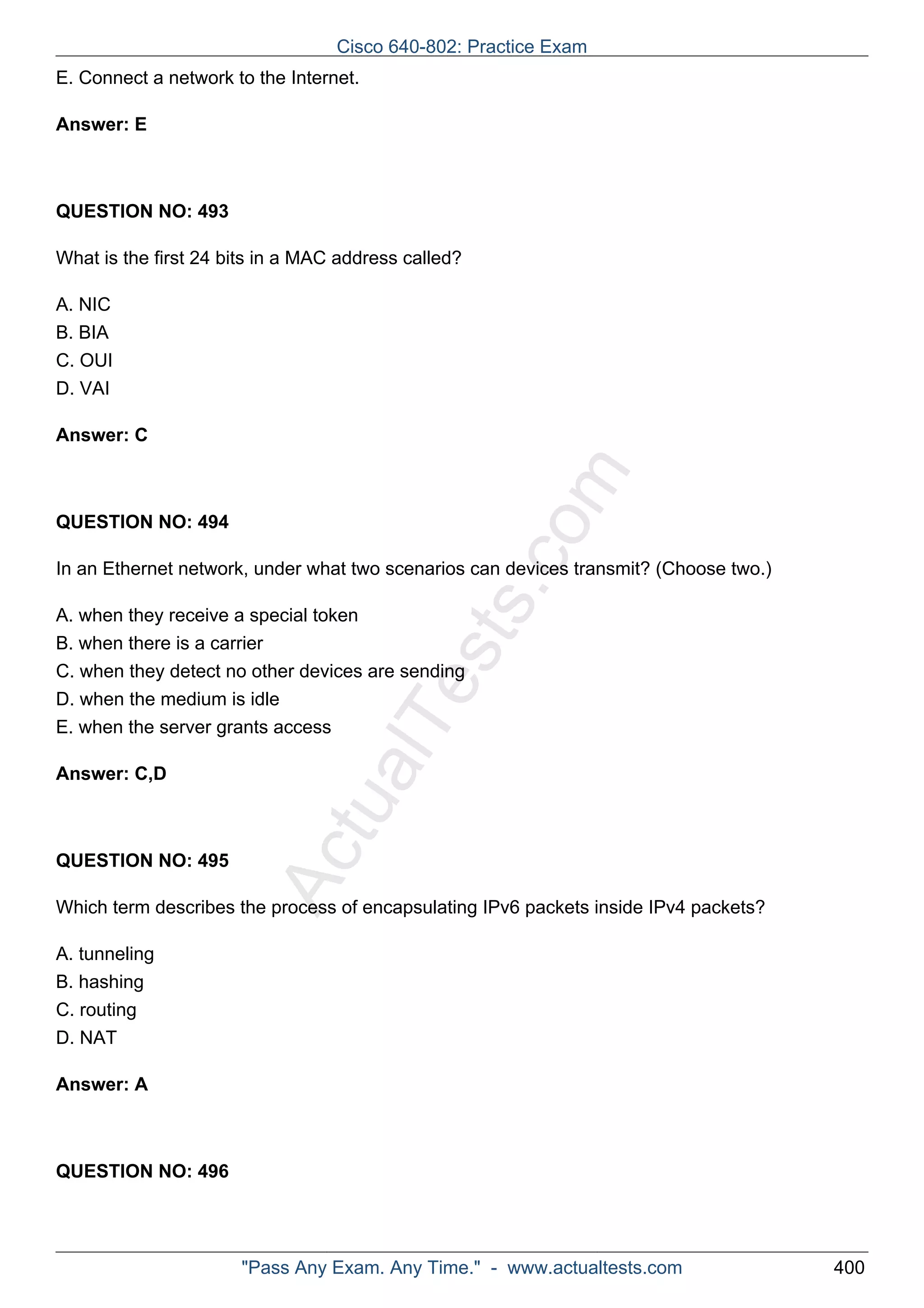
C. On router R1 ,configure DNS to resolve the URL assigned to Web Server 2 to the 192.168.1.10
address
D. On router R2, configure DHCP to assign a registered IP address on the 209.165.100.0/24
network to Web Server 2.
Answer: B
Explanation:
In order to allow internet users to access Web Server 2, we need to configure NAT address
translation on router R1.
"Pass Any Exam. Any Time." - www.actualtests.com 372](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-372-2048.jpg)
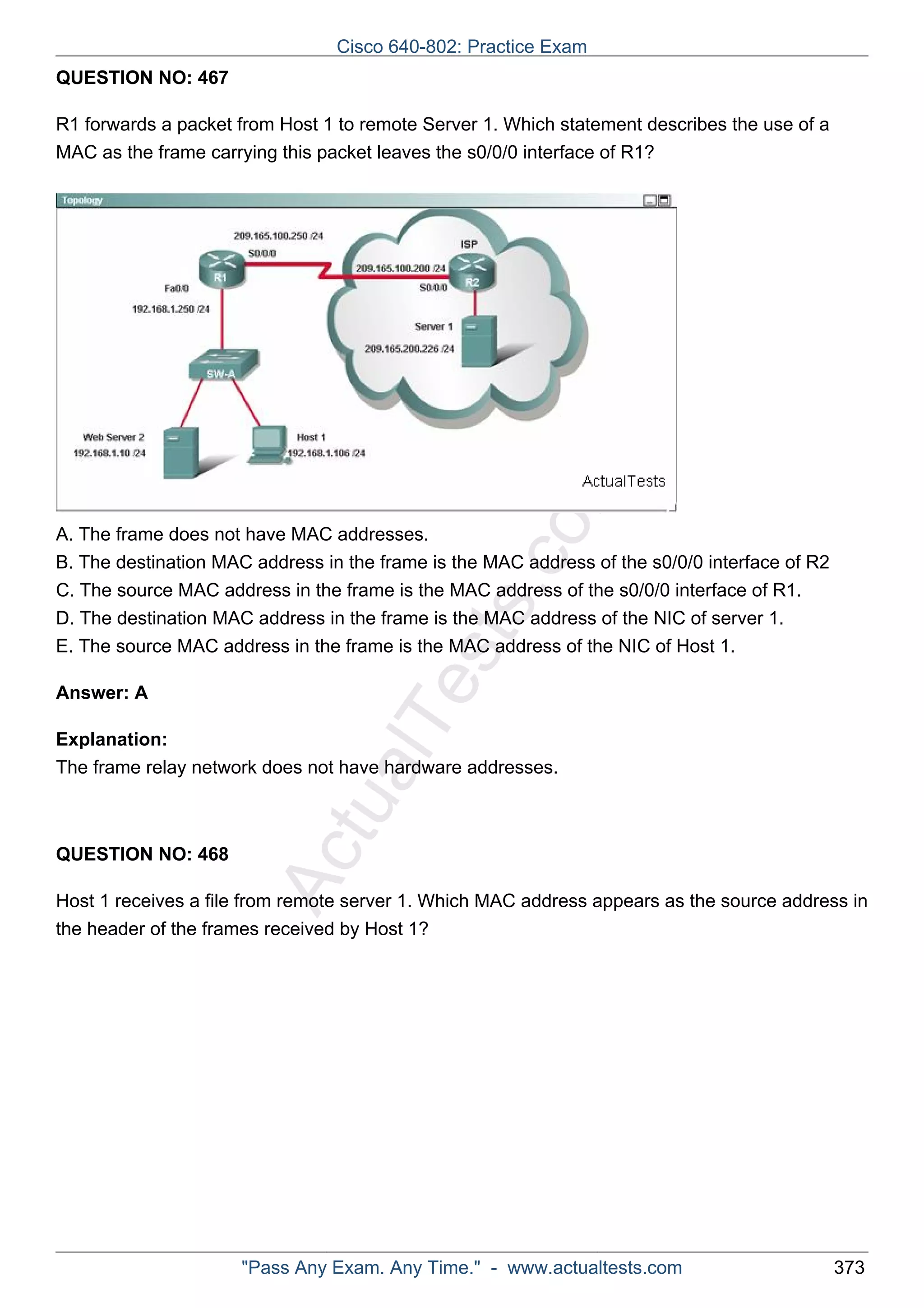


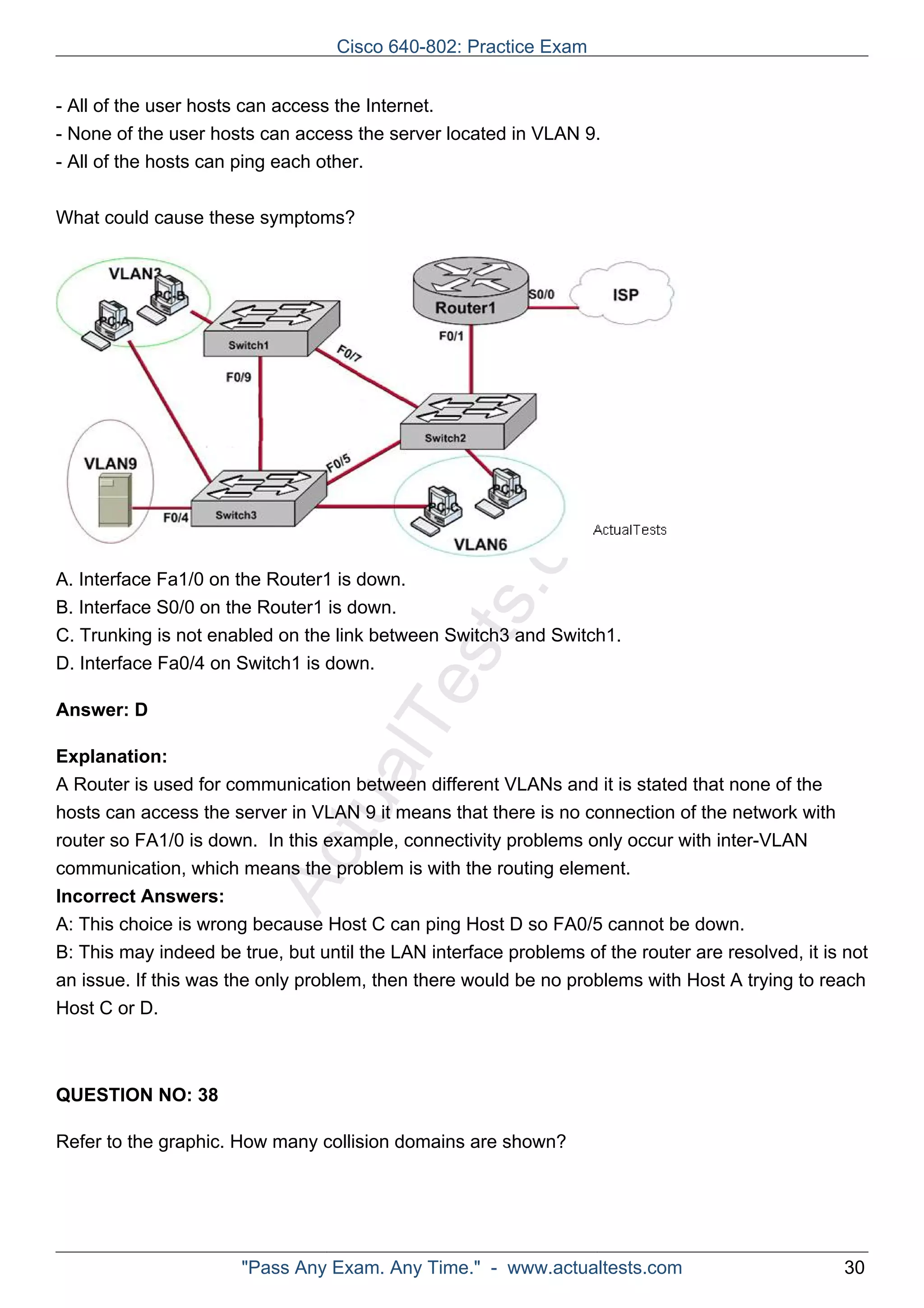
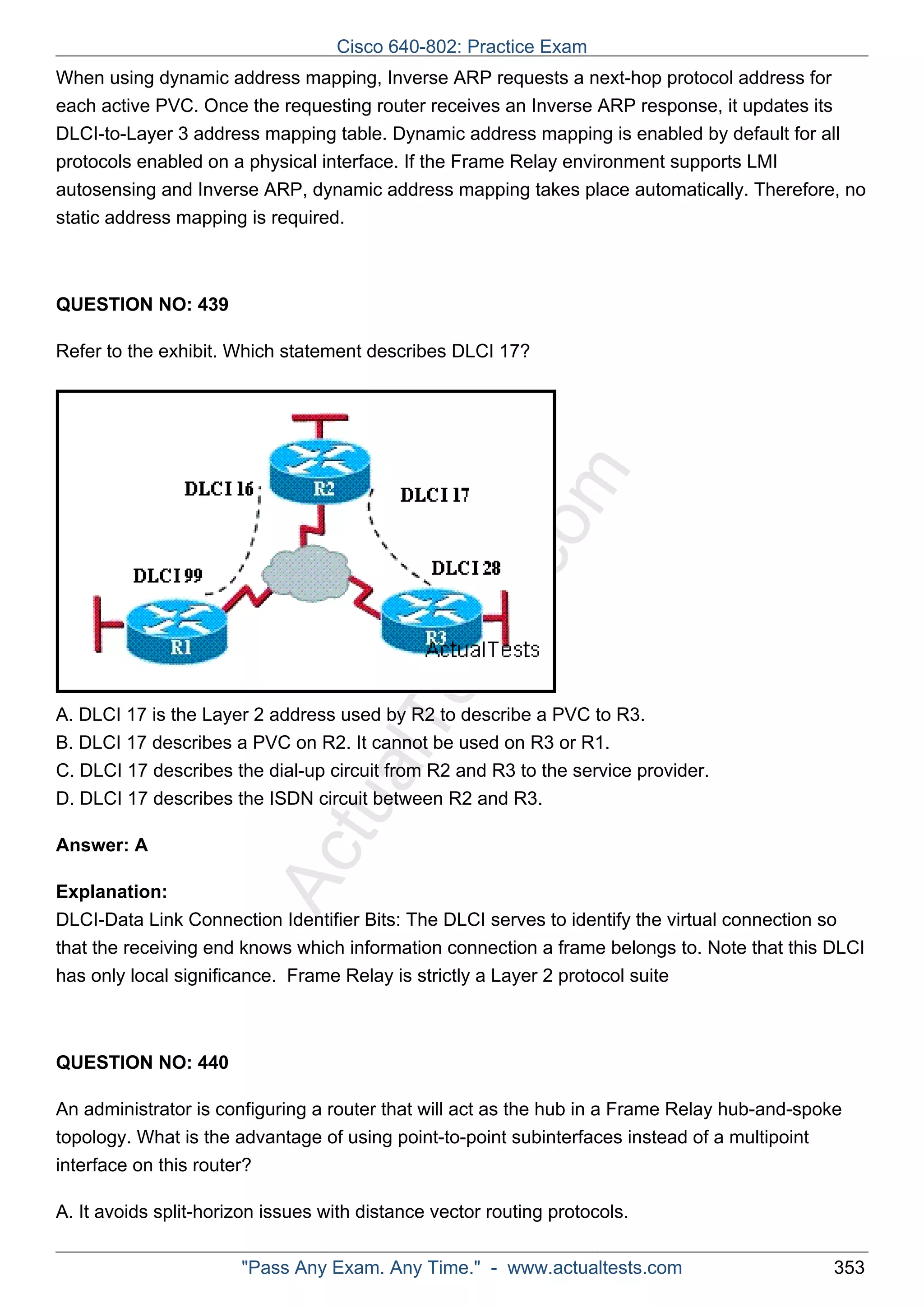
![Explanation:
Based on the output of the command "show frame-relay map", we know that DLCI mapped to the
router S-AMER is 196. (.3 In the above network topology, the complete layer3 IP address
is172.30.0.3)
Frame-relay map: The mapping command "Frame-relay map" can statically create a mapping
reaching the remote protocol address.
The format is :
frame-relay map protocol protocol-address dlci [ broadcast ][ ietf | cisco ]
Configuring a static Frame Relay map is optional unless you are using subinterfaces. The Frame
Relay map will map a Layer 3 address to a local DLCI. This step is optional because inverse-arp
will automatically perform this map for you.
Syntax for frame-relay map is:
ActualTests.com
frame-relay map protocol address dlci [broadcast] [cisco | ietf]
The broadcast option allows packets, such as RIP updates to be forwarded across the PVC. If you
are not using the broadcast option, you need to specify the neighbor to forward unicast packet
using neighbor command.
neighbor a.b.c.d
Specify RIP neighbor. When a neighbor doesn't understand multicast, this command is used to
specify neighbors. In some cases, not all routers will be able to understand multicasting, where
packets are sent to a network or a group of addresses. In a situation where a neighbor cannot
process multicast packets, it is necessary to establish a direct link between routers. The neighbor
command allows the network administrator to specify a router as a RIP neighbor. The no neighbor
a.b.c.d command will disable the RIP neighbor.
QUESTION NO: 473
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 378](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-378-2048.jpg)





























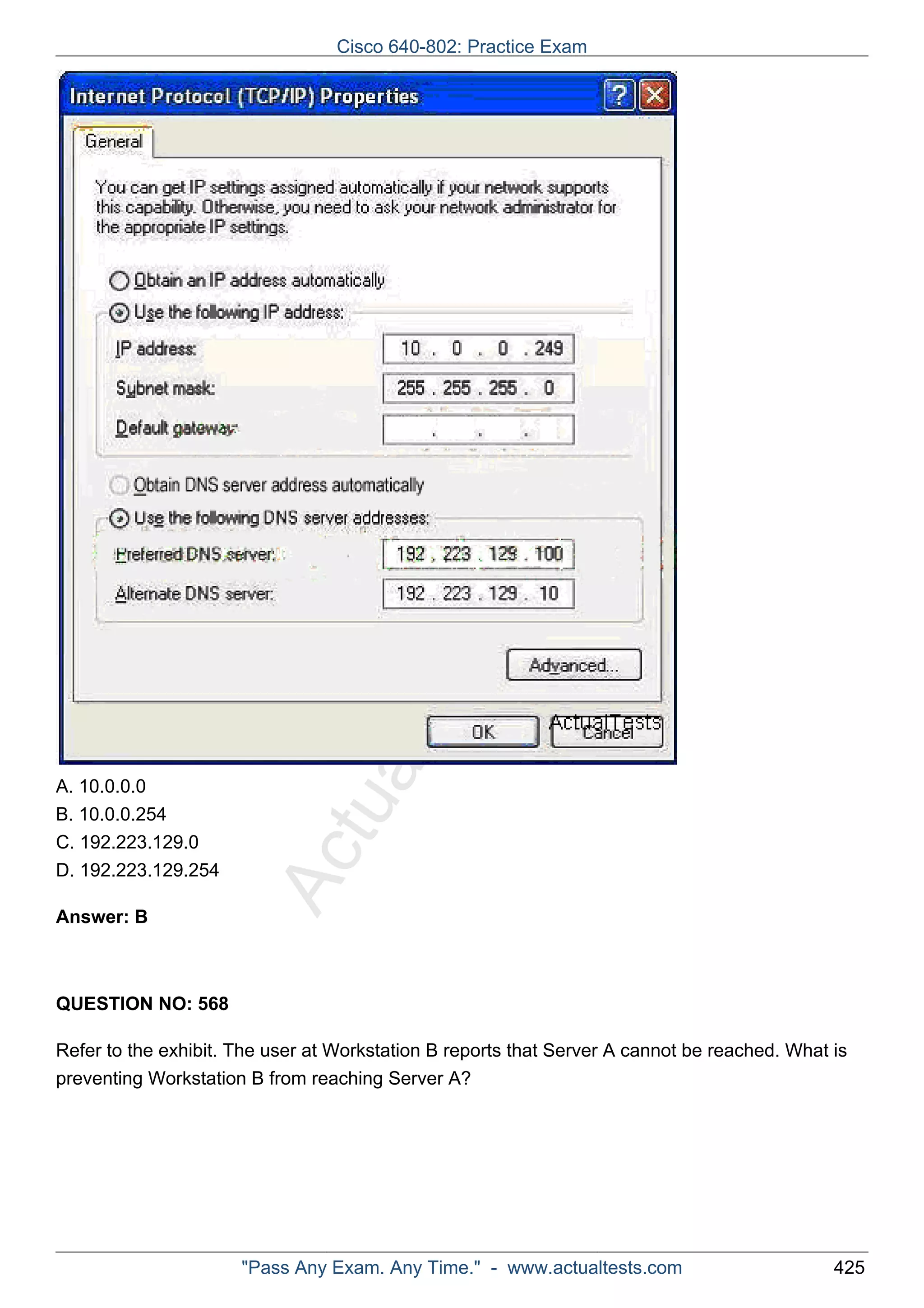


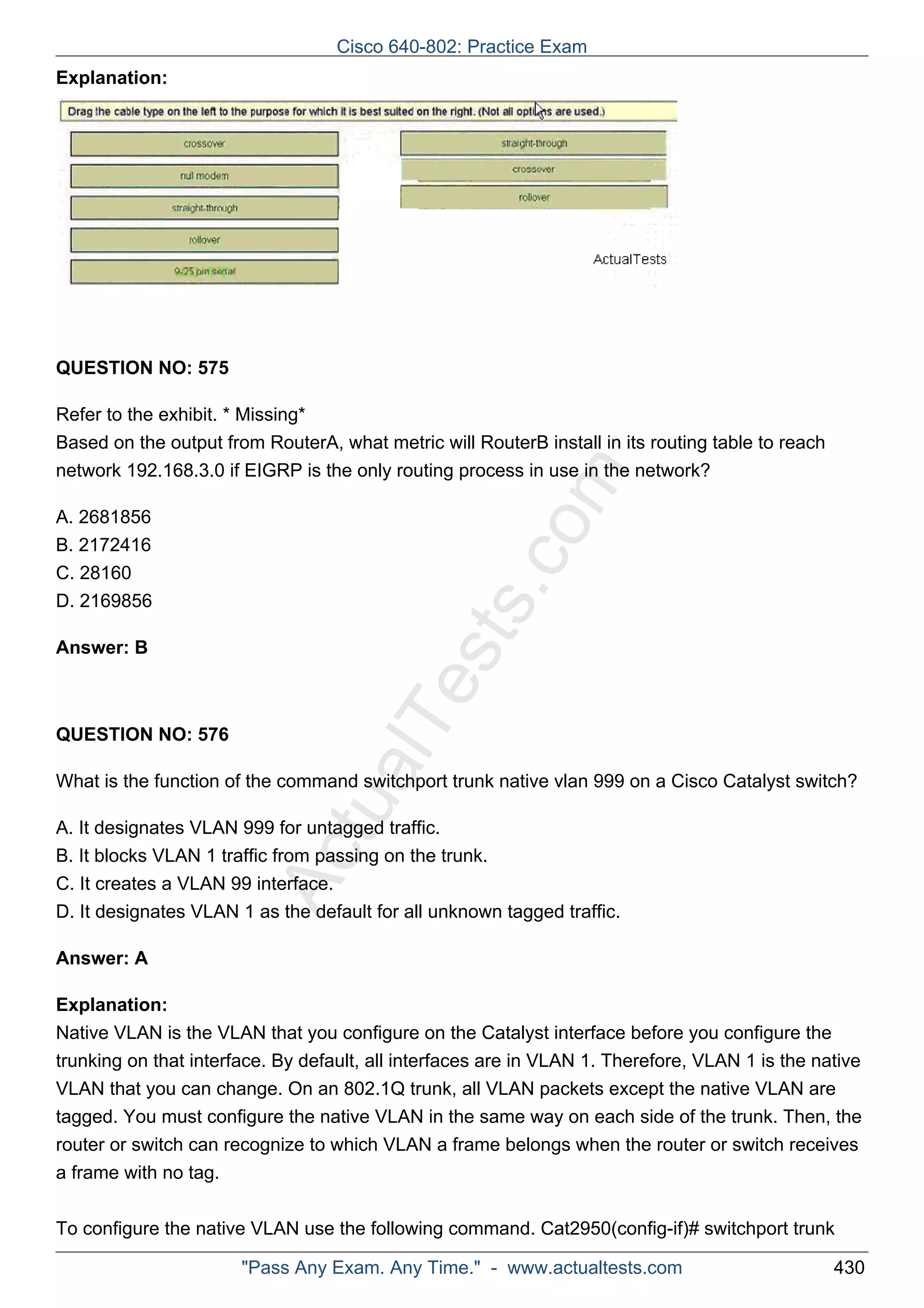
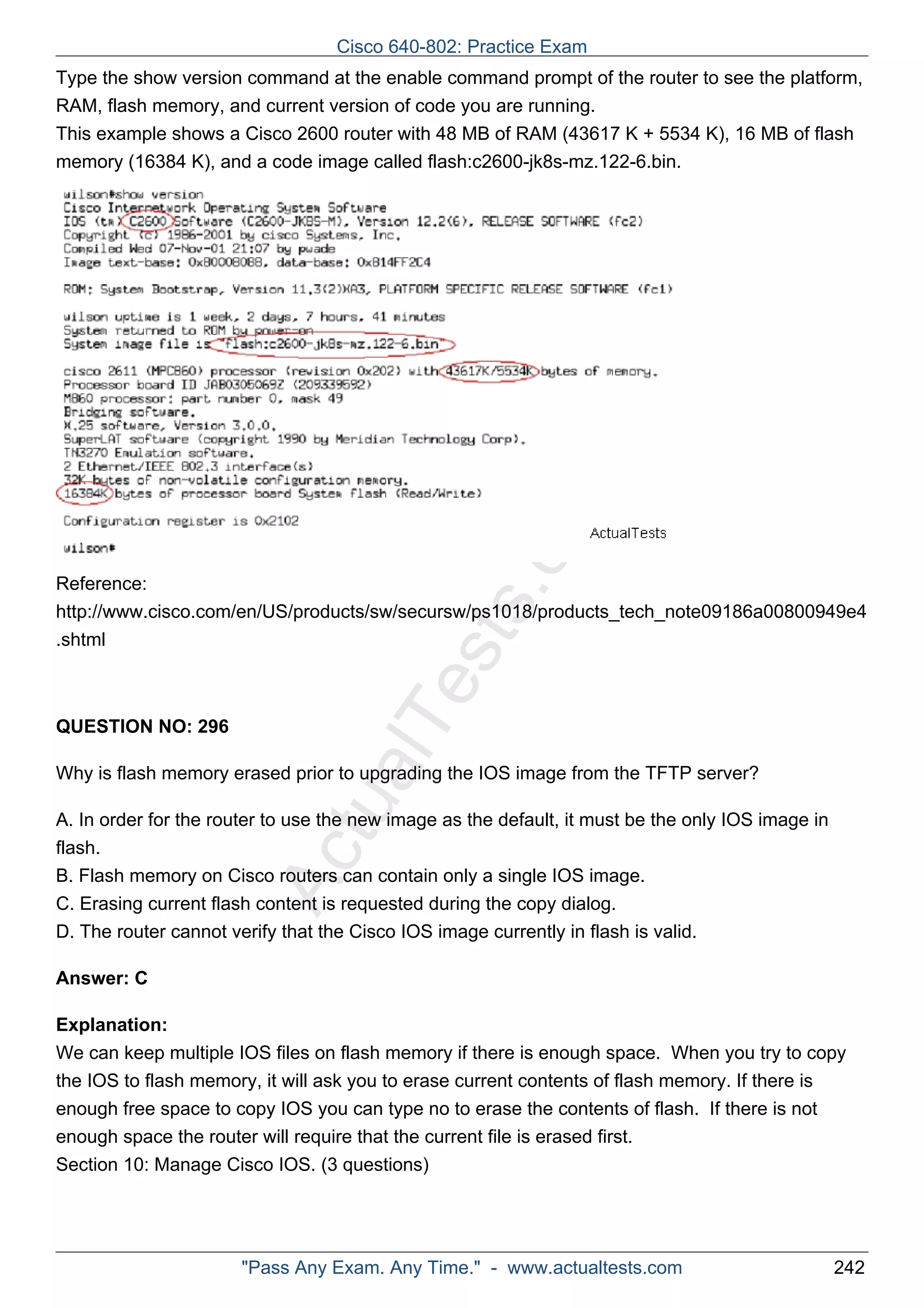
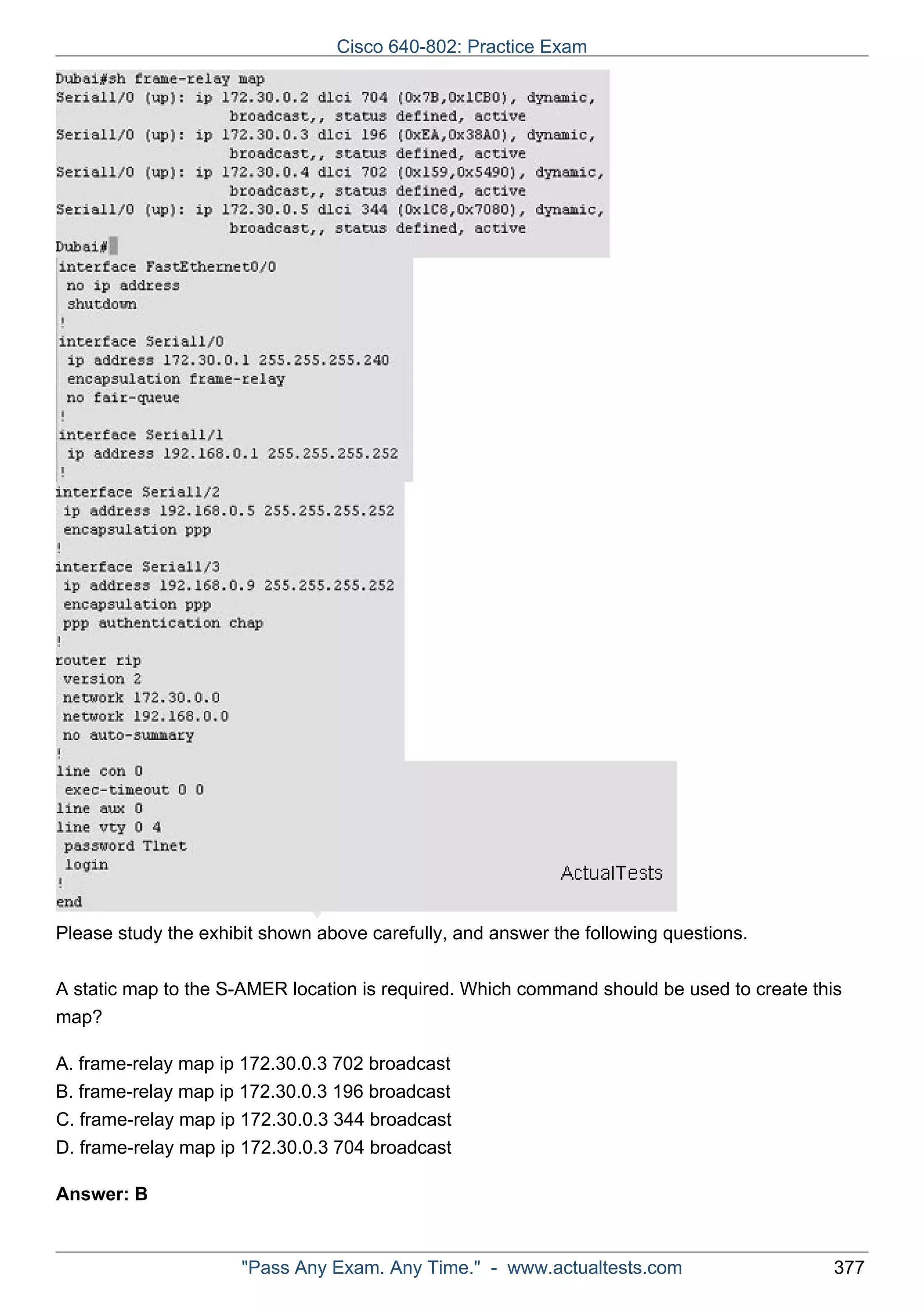
![Cisco 640-802: Practice Exam
ActualTests.com
native vlan 10
QUESTION NO: 577
Which of the following are valid VLAN Trunk Protocols over Fast Ethernet? [Select 2].
A. Inter-Switch Link
B. 802.10
C. LANE
D. 802.1Q
Answer: A,D
QUESTION NO: 578
Which of the following is not a valid VTP mode?
A. Server
B. Client
C. Transparent
D. Hybrid
Answer: D
QUESTION NO: 579
Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to
network hosts? (Choose three.)
A. 15.234.118.63
B. 92.11.178.93
C. 134.178.18.56
D. 192.168.16.87
E. 201.45.116.159
F. 217.63.12.192
Answer: D,E,F
QUESTION NO: 580 DRAG DROP
"Pass Any Exam. Any Time." - www.actualtests.com 431](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-431-2048.jpg)
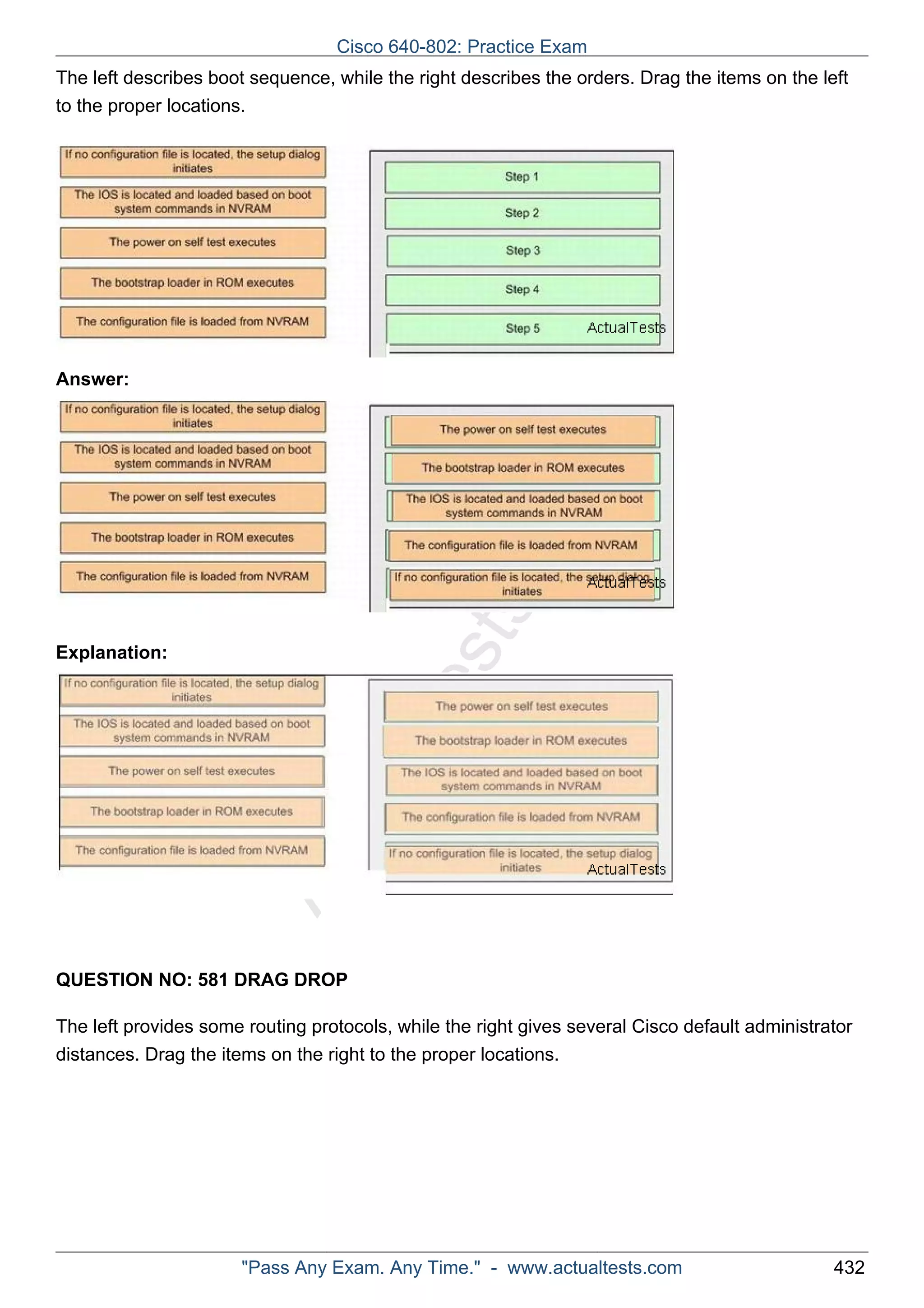









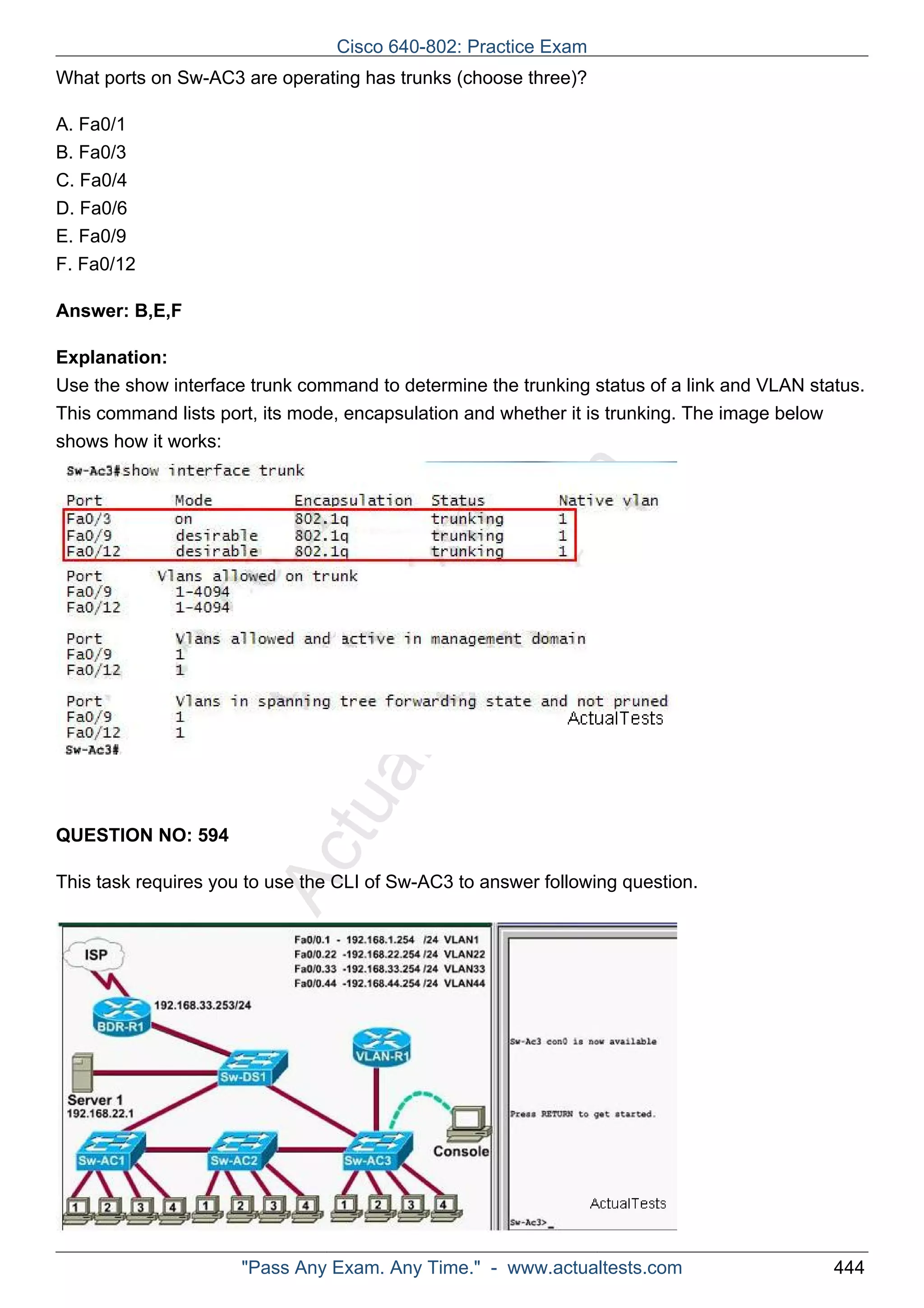




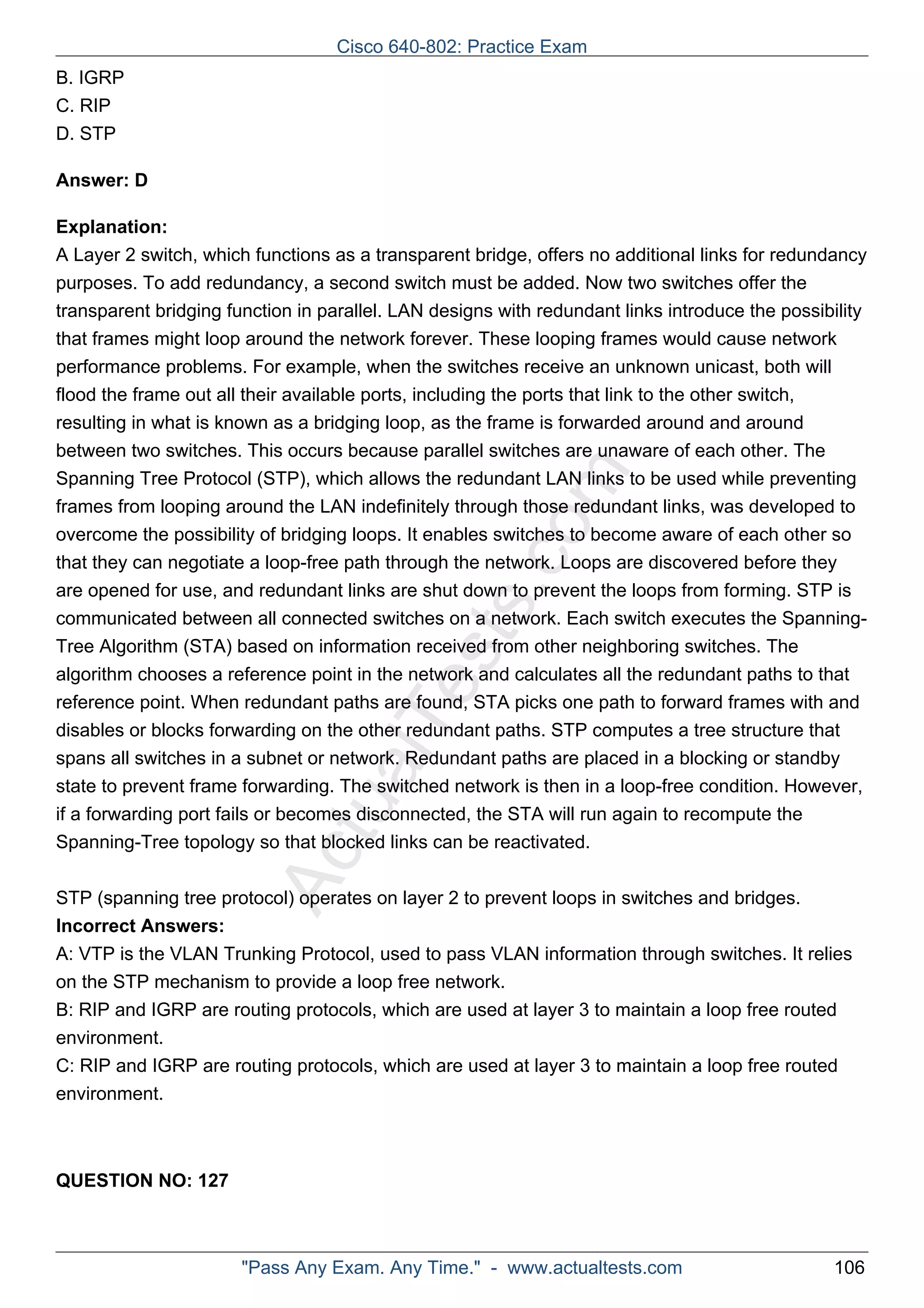
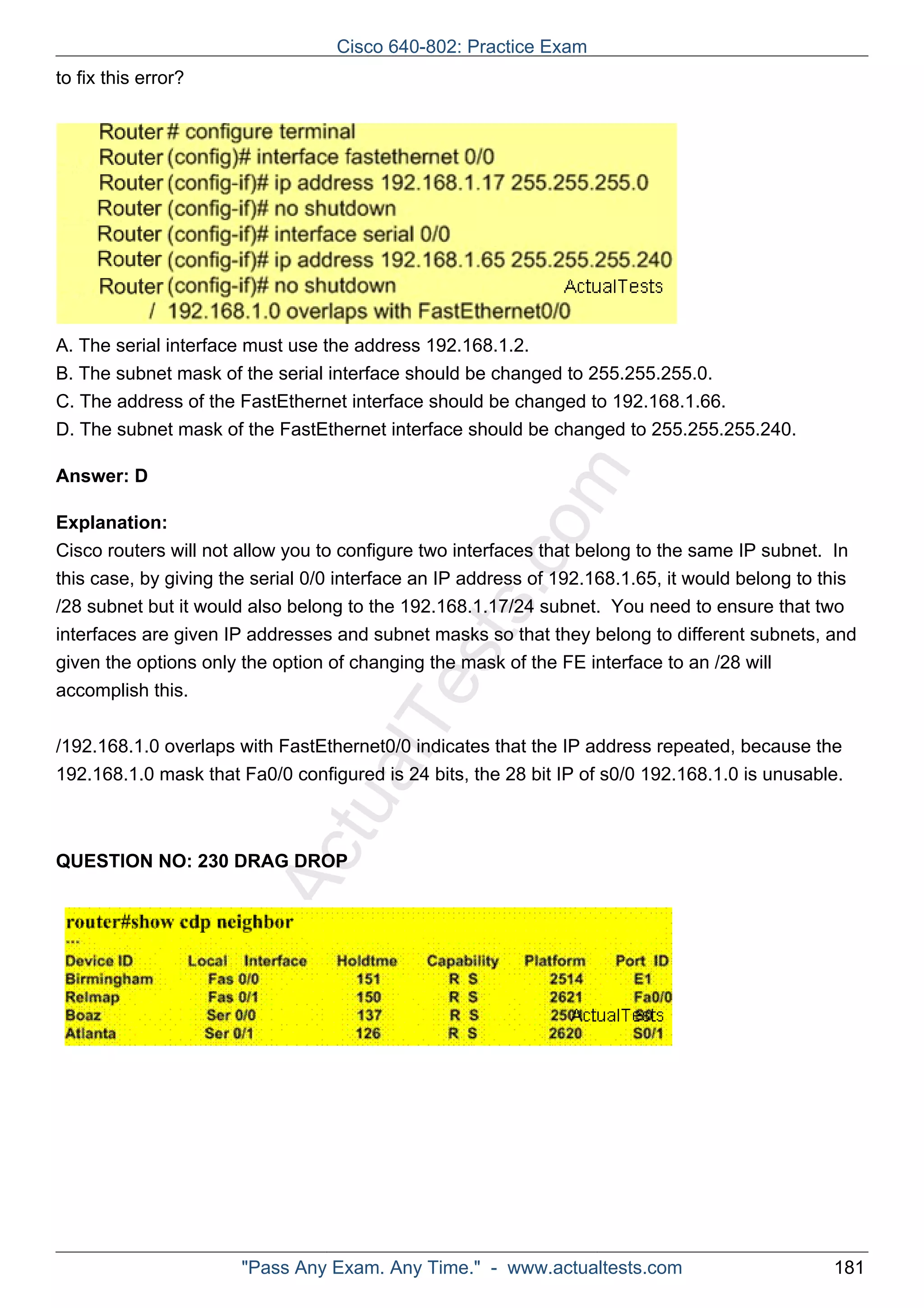
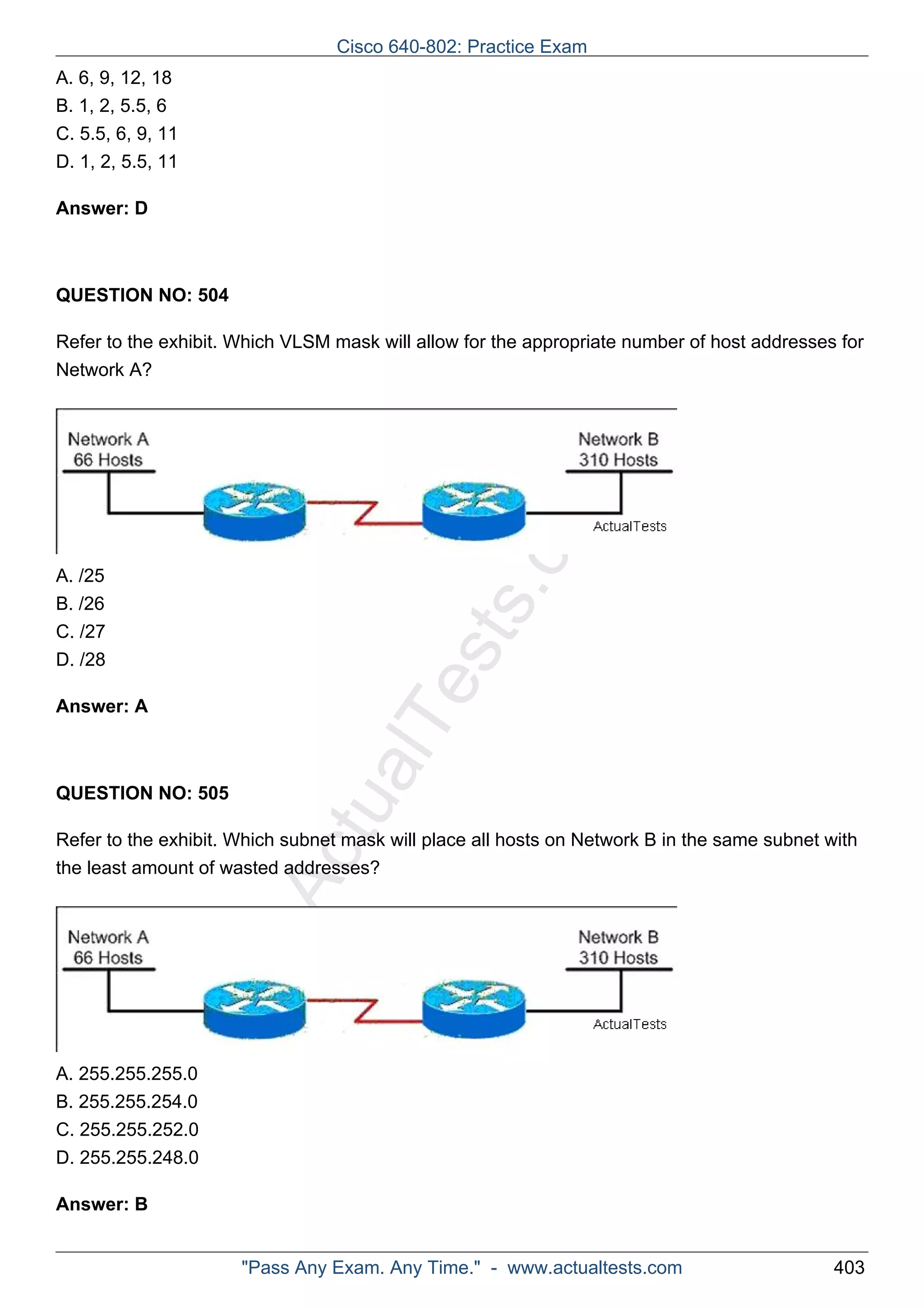
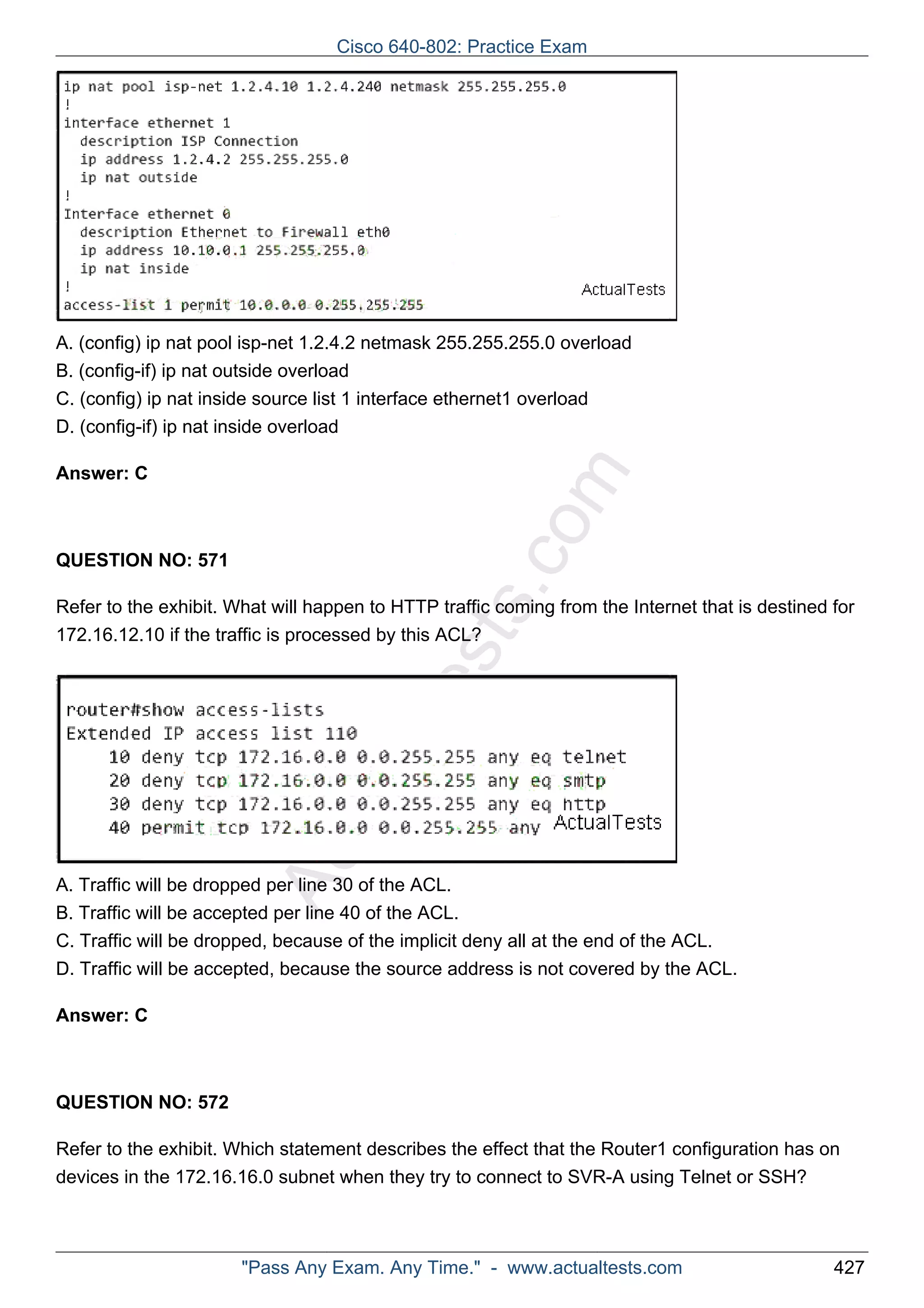
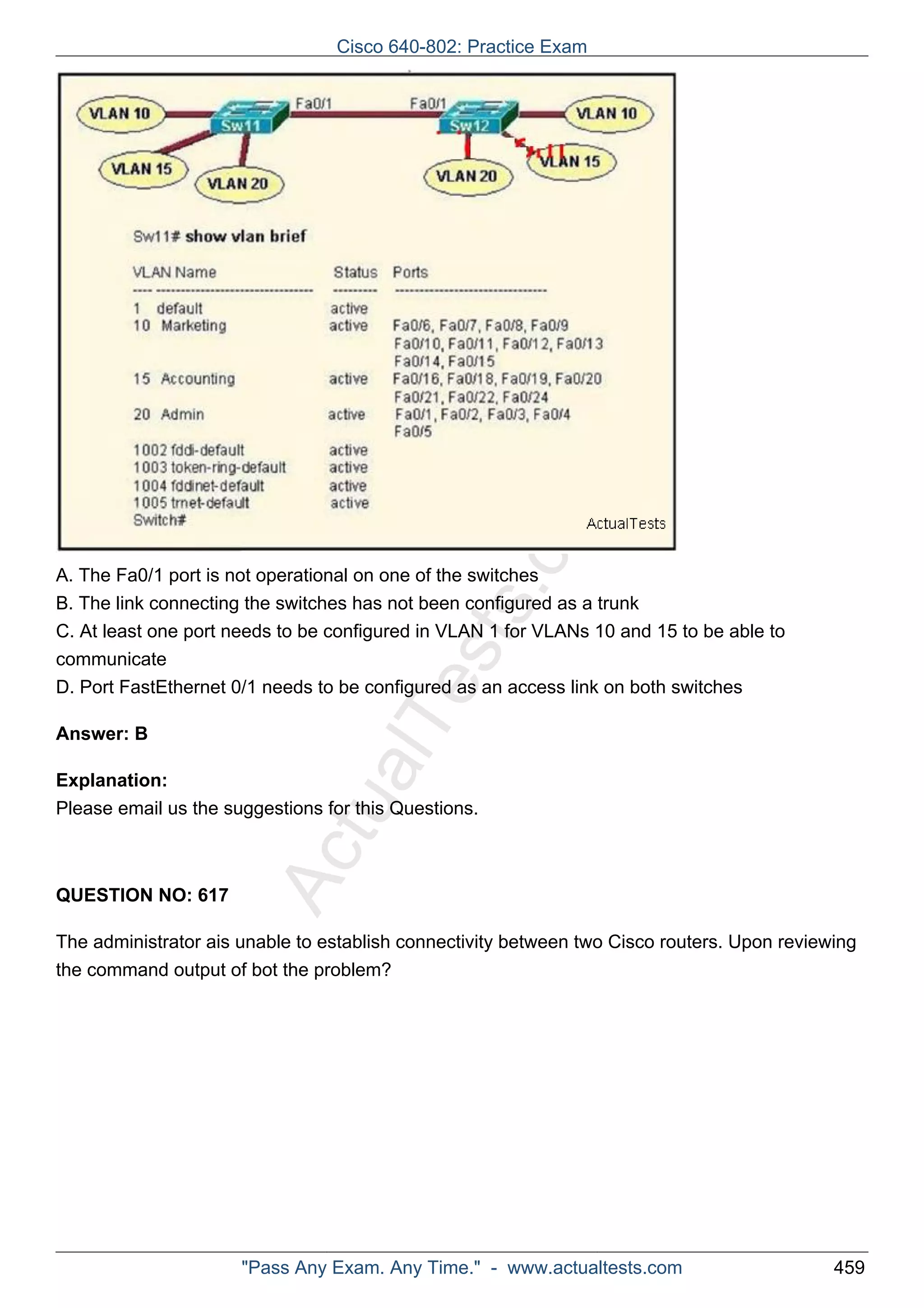
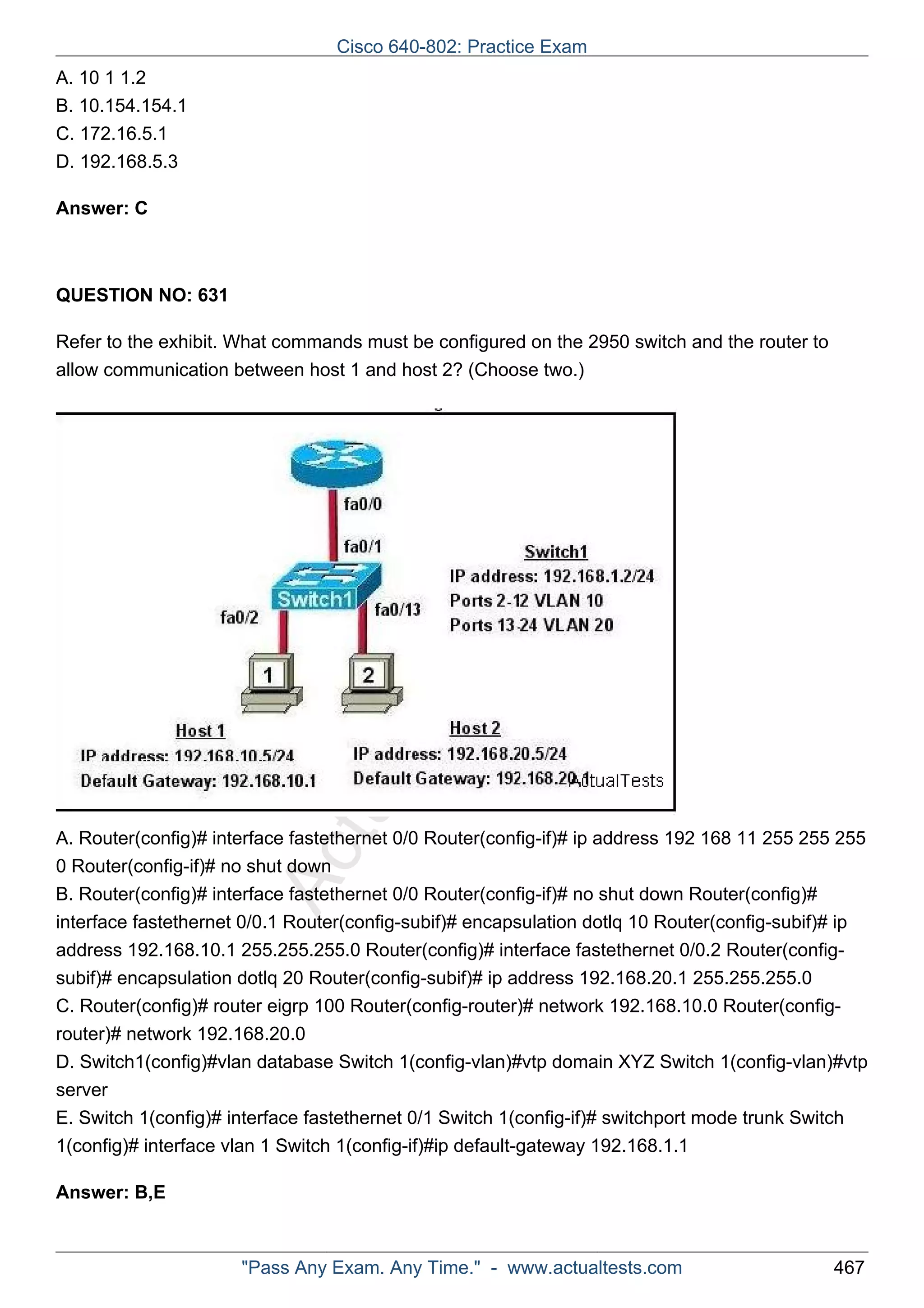
![Cisco 640-802: Practice Exam
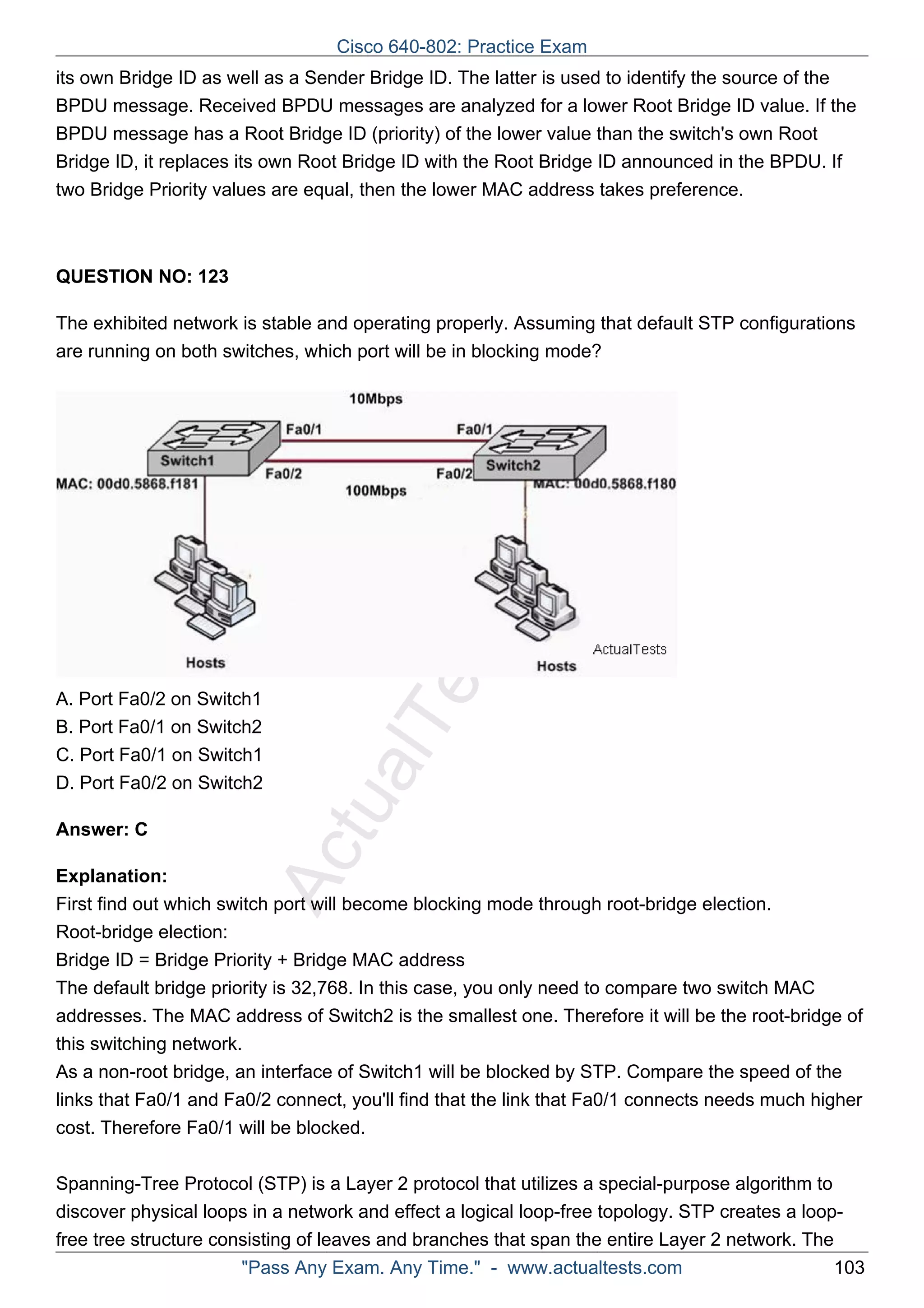
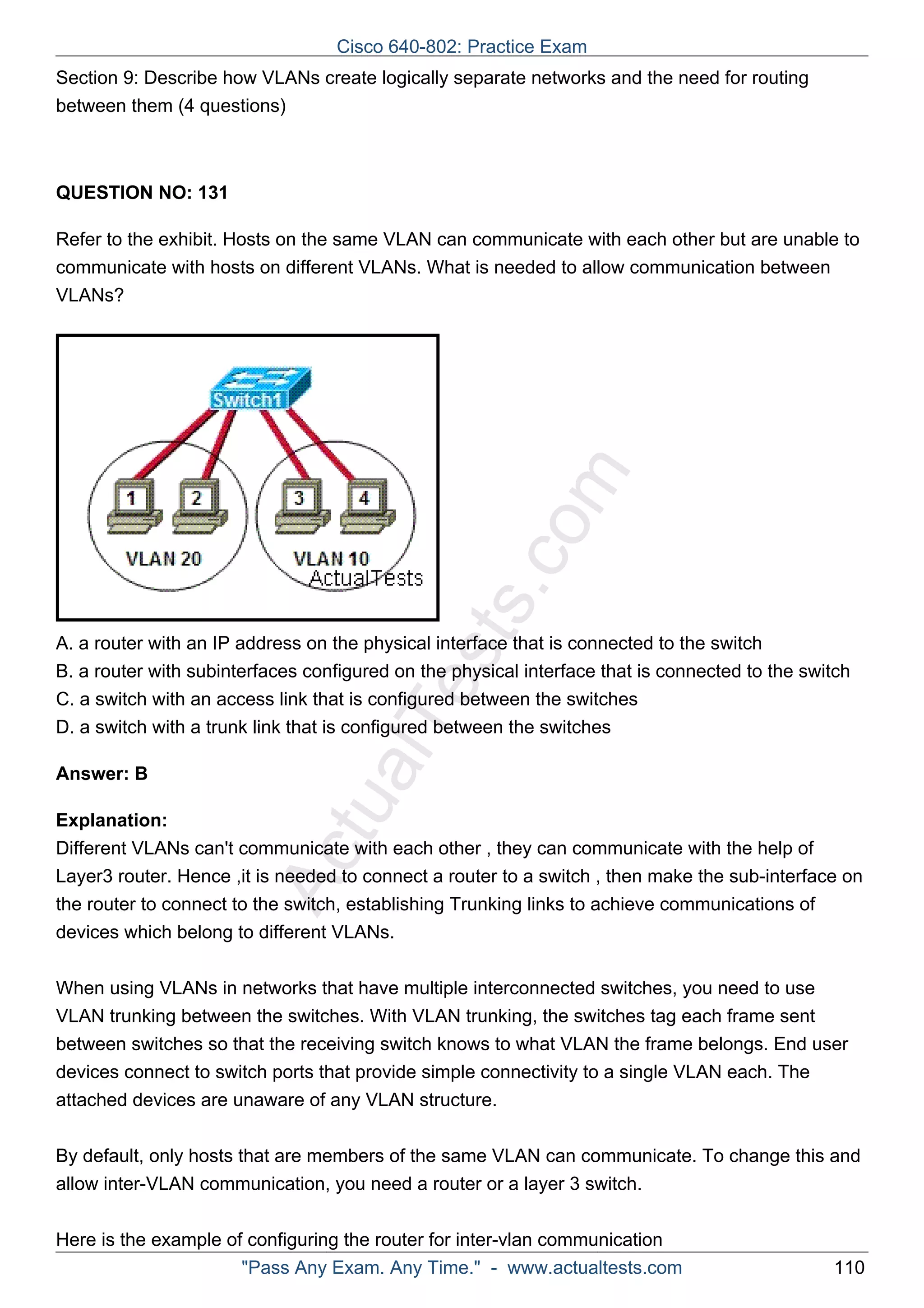
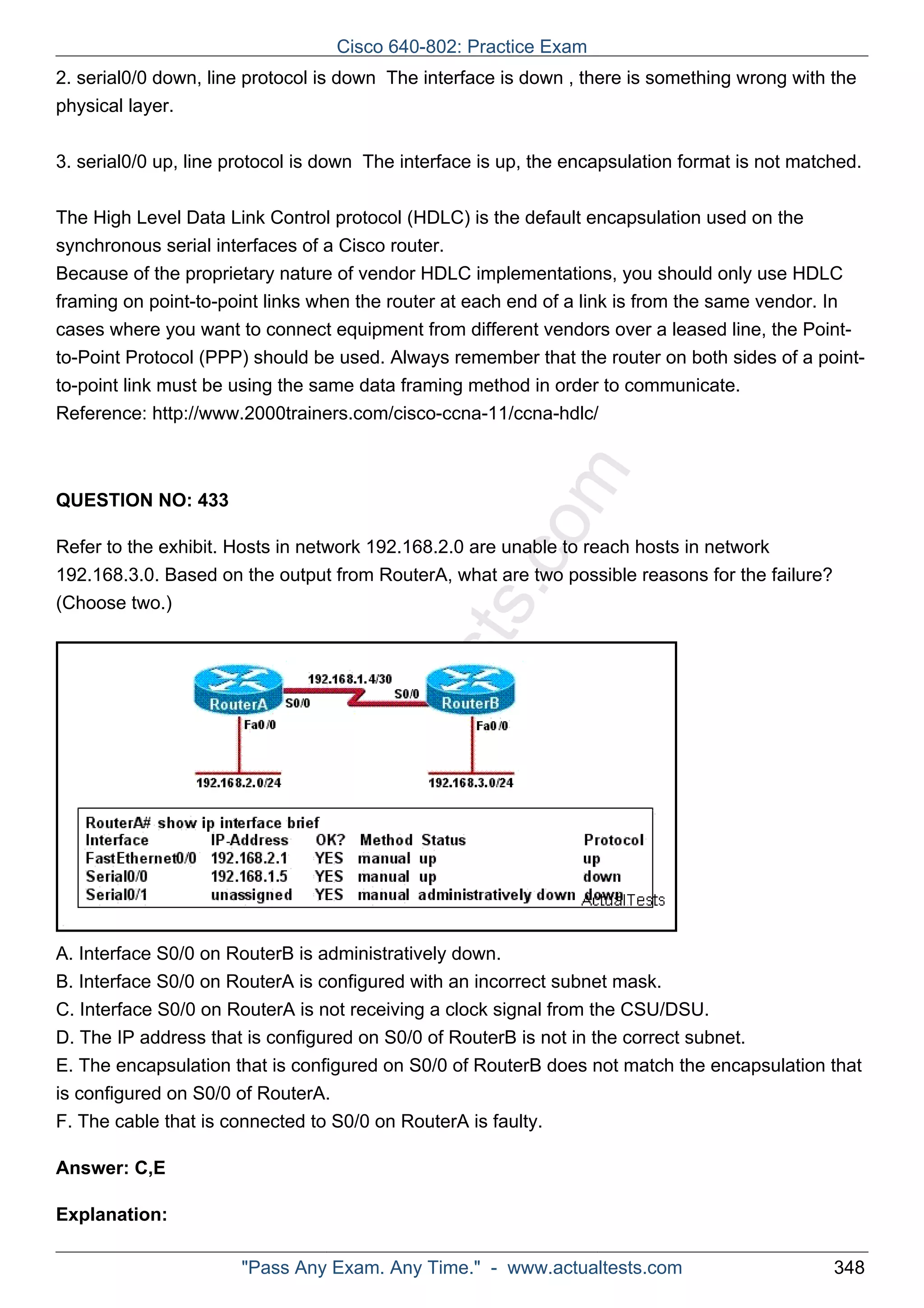
Refer to the exhibit. The network is con verged. After link-state advertisements are received from
Router_A, what information will Router_E contain in its routing table for the subnets 208.149.23.64
and 208.149.23.96?
ActualTests.com
A. 208.149.23.64(110/13] via 190.173.23.10,00:00:07, FastEthemet0/0
208.149.23.96(110/13] via 190.173.23.10,00:00:16, FastEthemet0/0
B. 208.149.23.64(110/1] via 190.172.23.10,00:00:07, Serial1/0
208.149.23.96(110/3] via 190.173.23.10,00:00:16, FastEthemetO/0
C. 208.149.23.64(110/13] via 190.173.23.10,00:00:07, Serial1/0
208.149.23.96(110/13] via 190.173.23.10,00:00:16, Serial1/0
208.149.23.96(110/13] via 190.173.23.10,00:00:16, FastEthemetO/0
D. 208.149.23.64(110/3] via 190.172.23.10,00:00:07, Serial1/0
208.149.23.96(110/3] via 190.173.23.10,00:00:16, Serial1/0
Answer: A
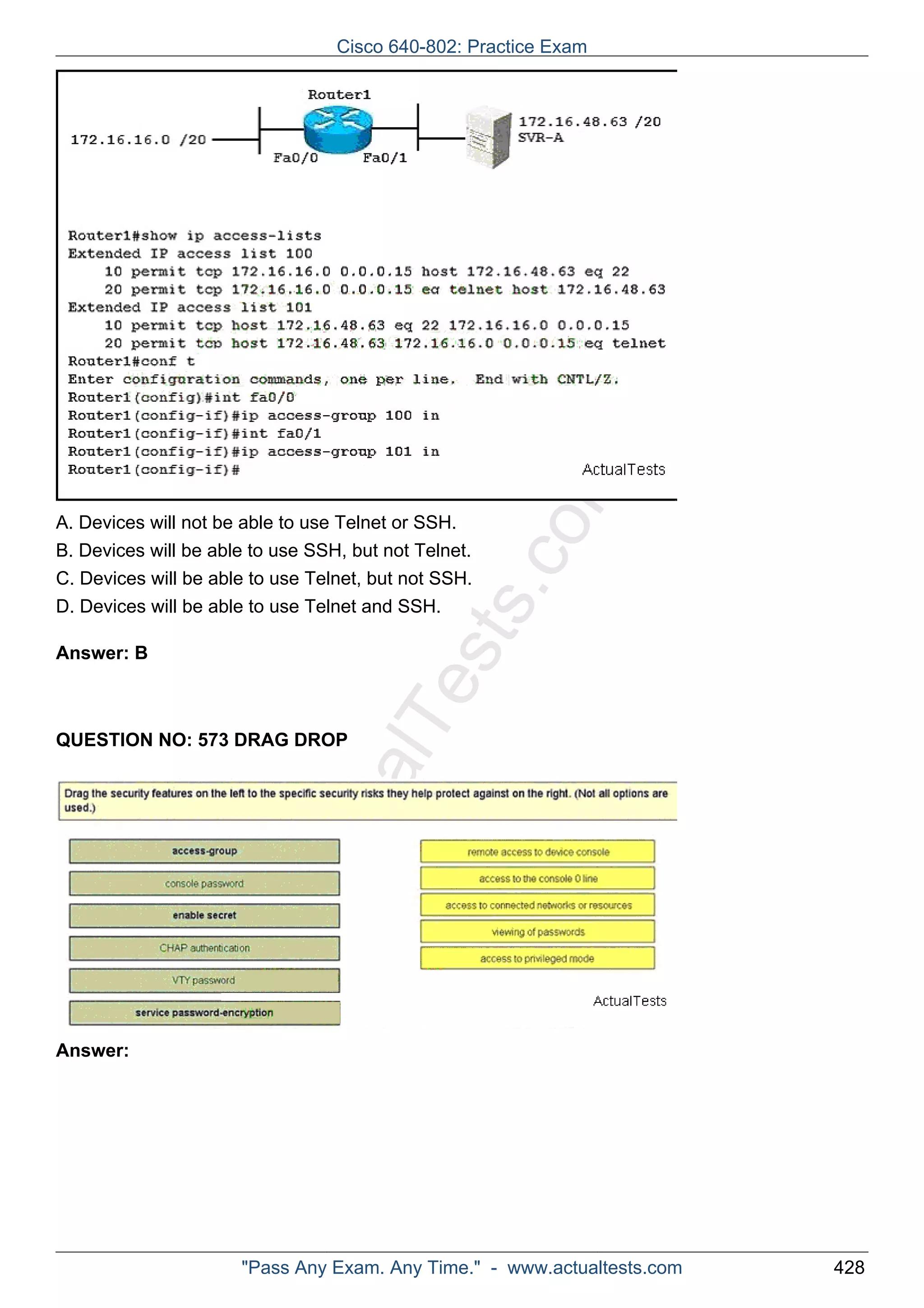
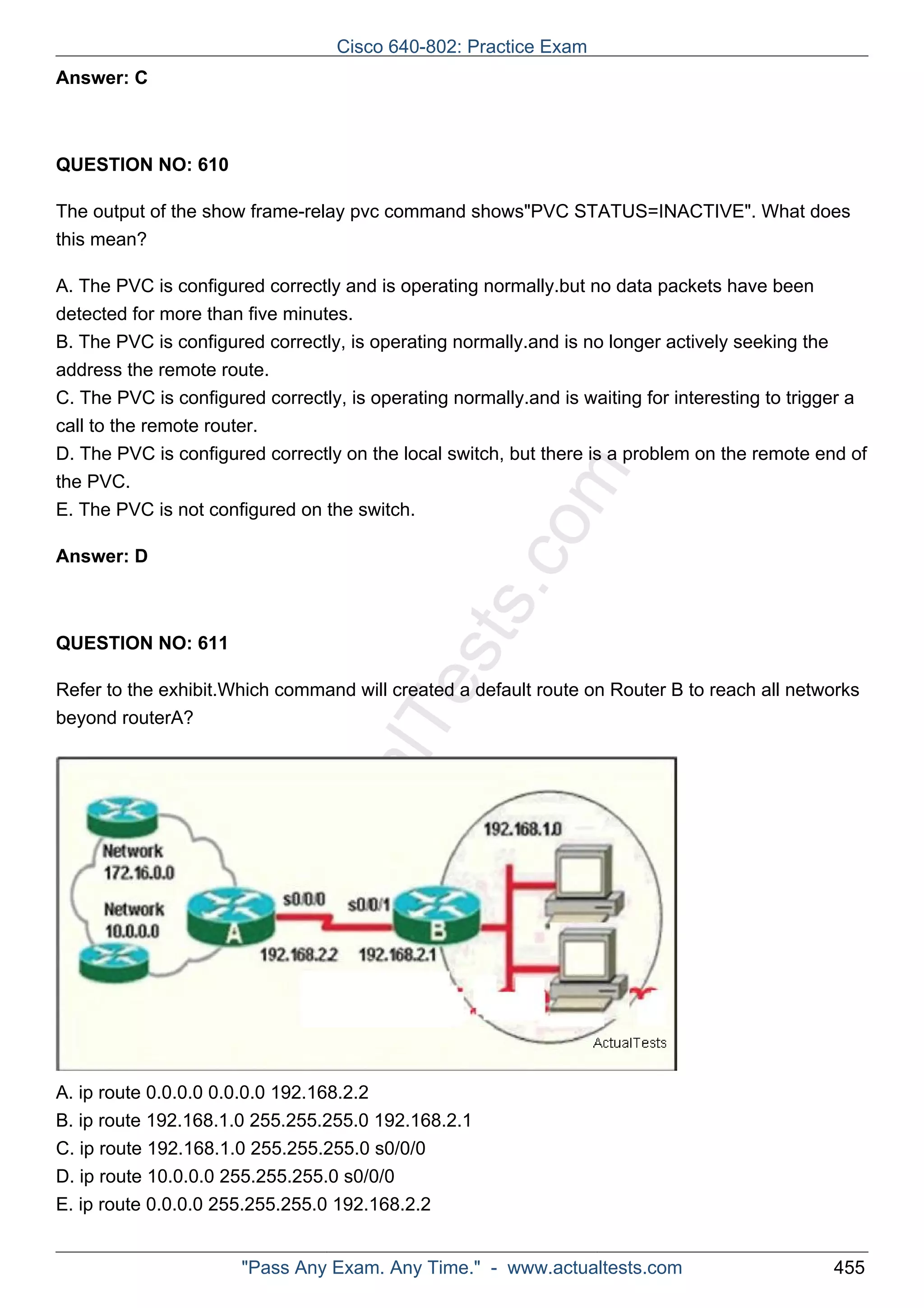
QUESTION NO: 608
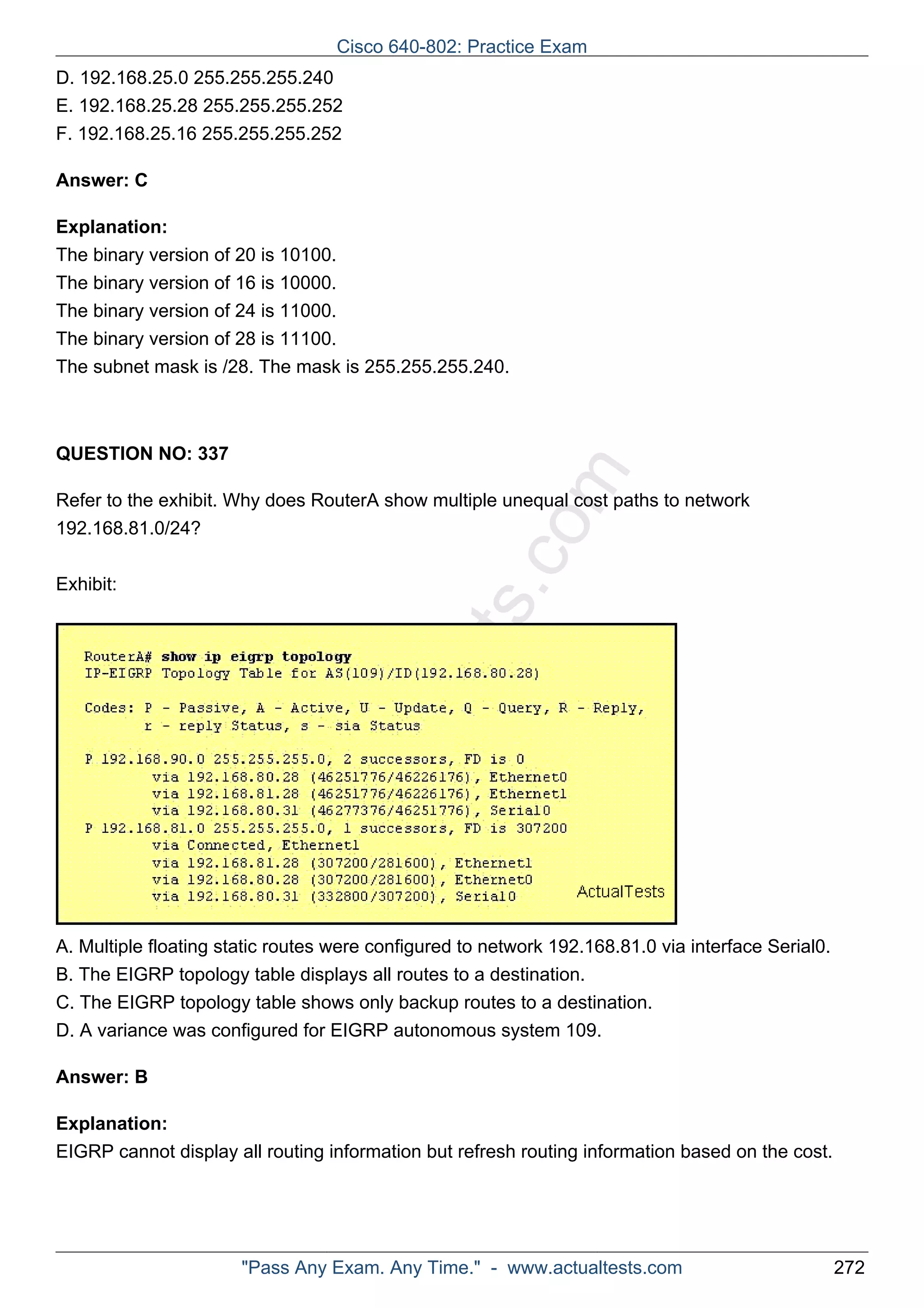
Refer to exhibit. The company uses EIGRP as the routing protocol. What path will packets take
from a host on 192.168.10.192/26 network to a host on the LAN attached to router R1?
"Pass Any Exam. Any Time." - www.actualtests.com 452](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-452-2048.jpg)


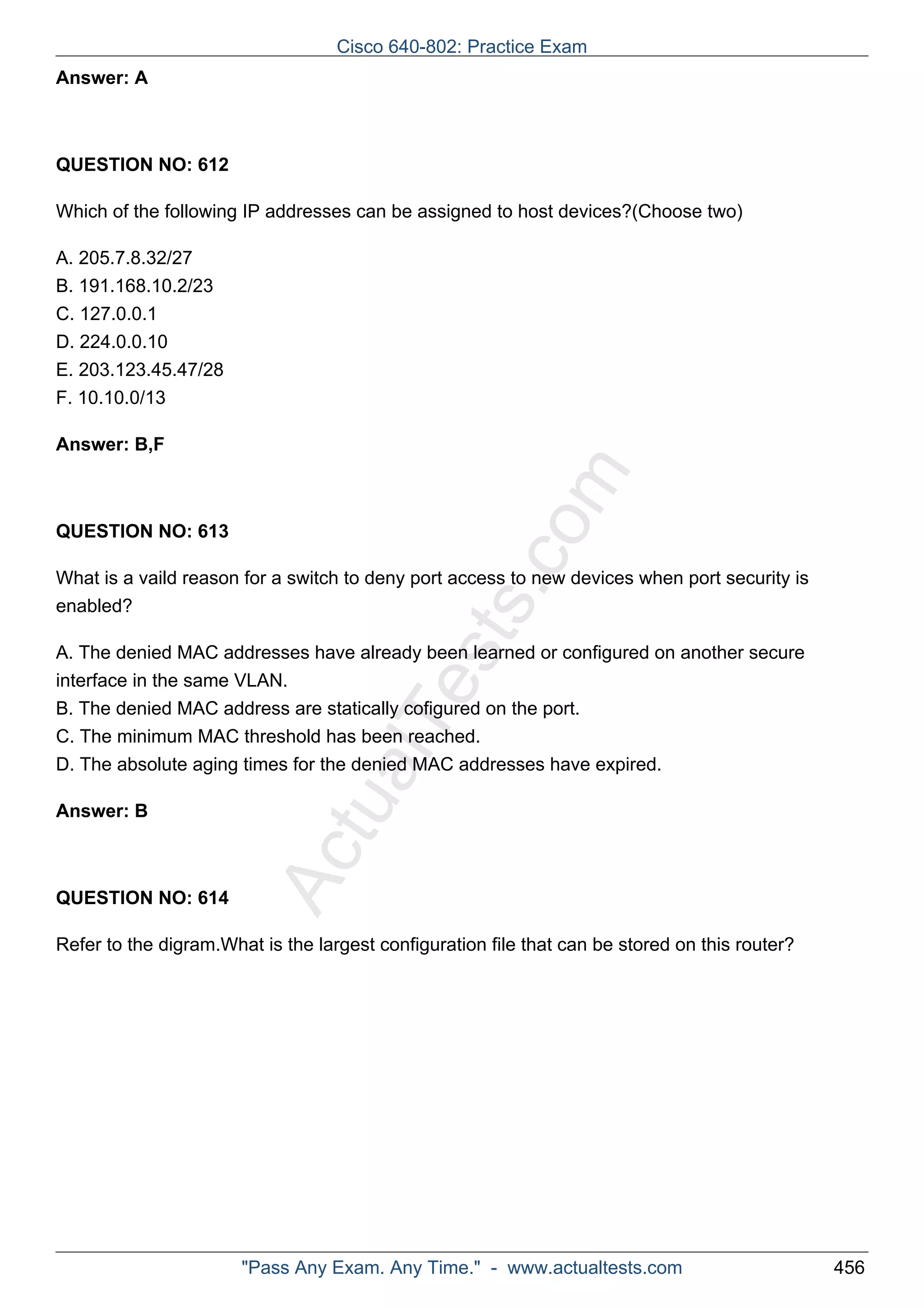
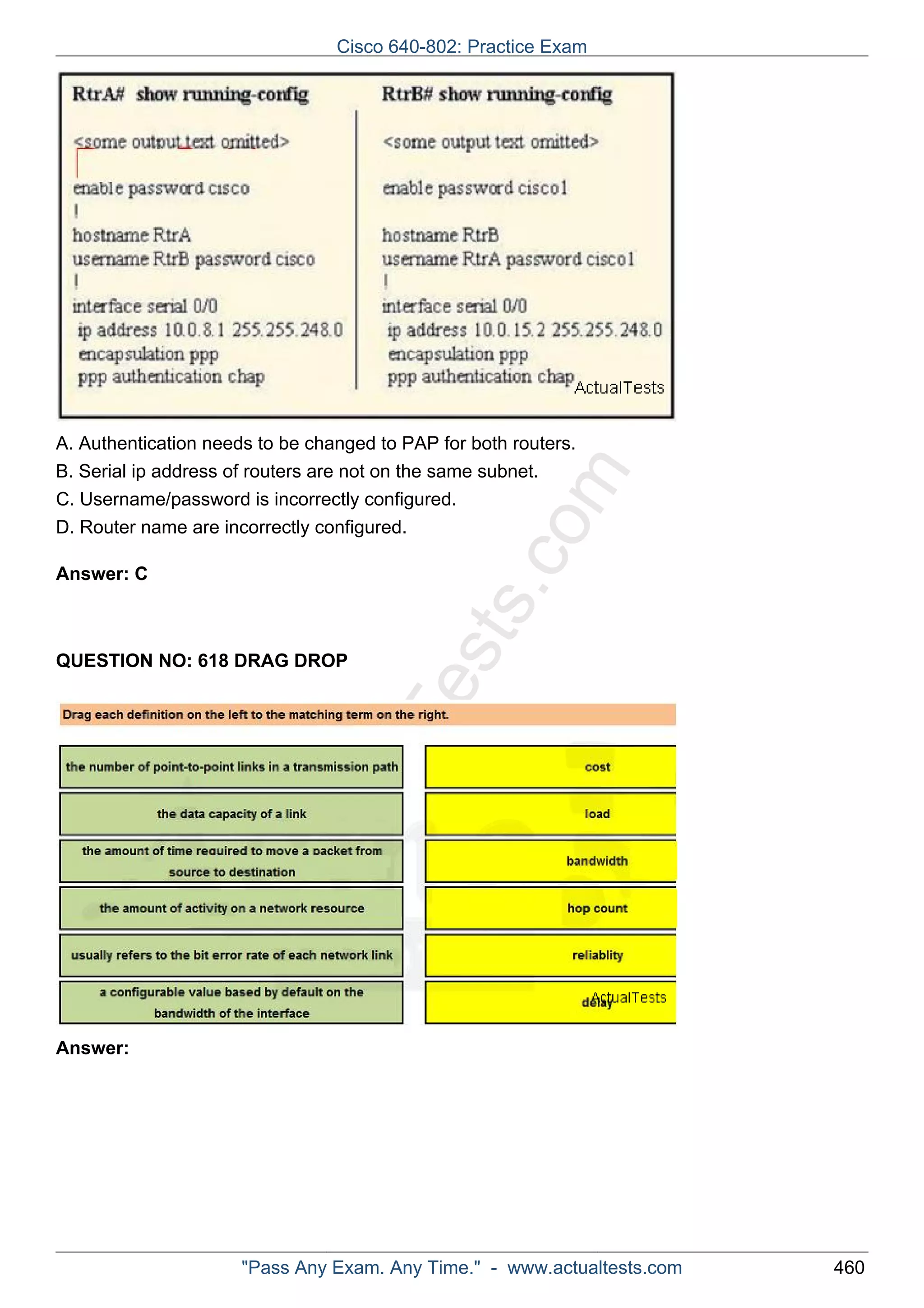





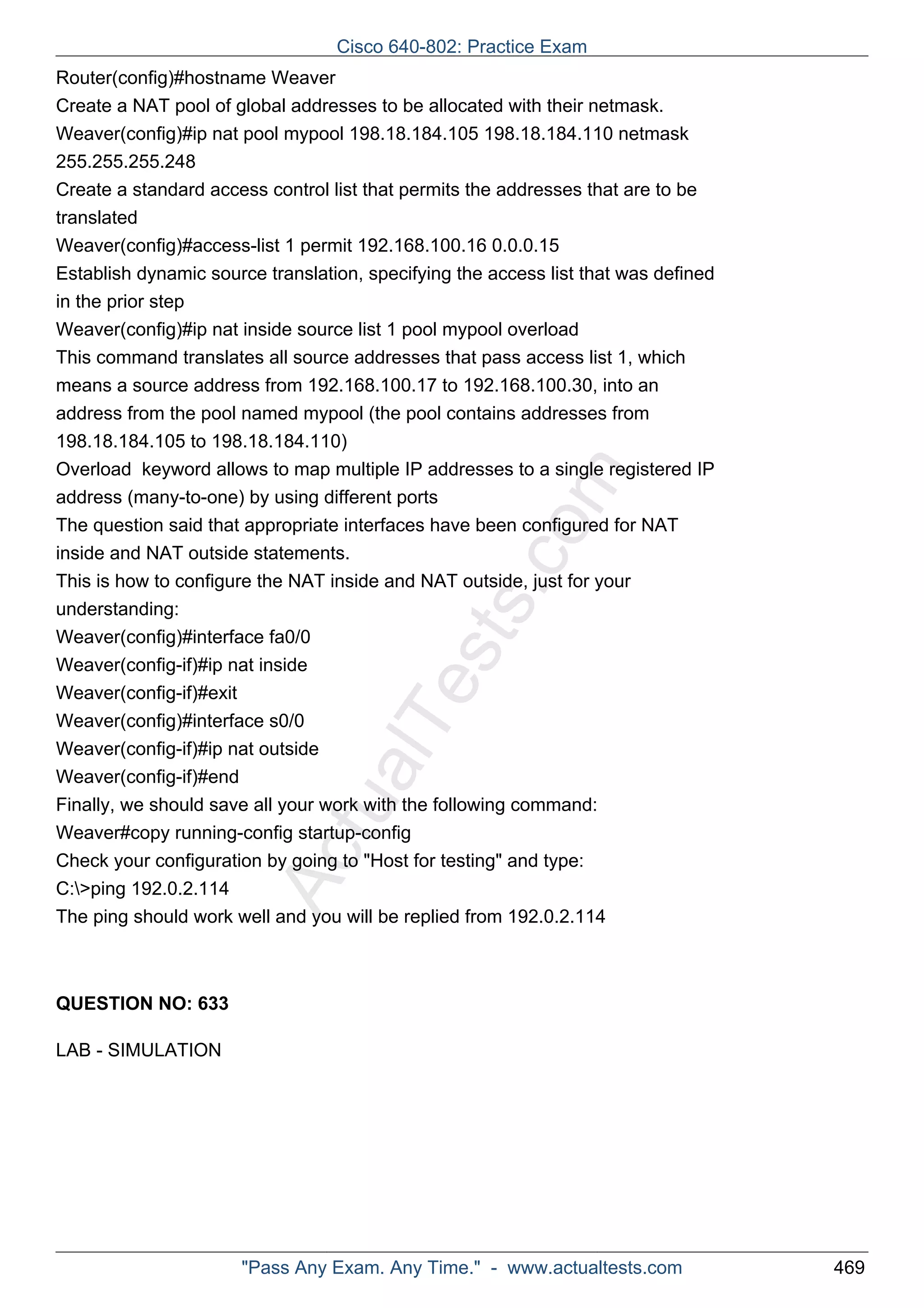



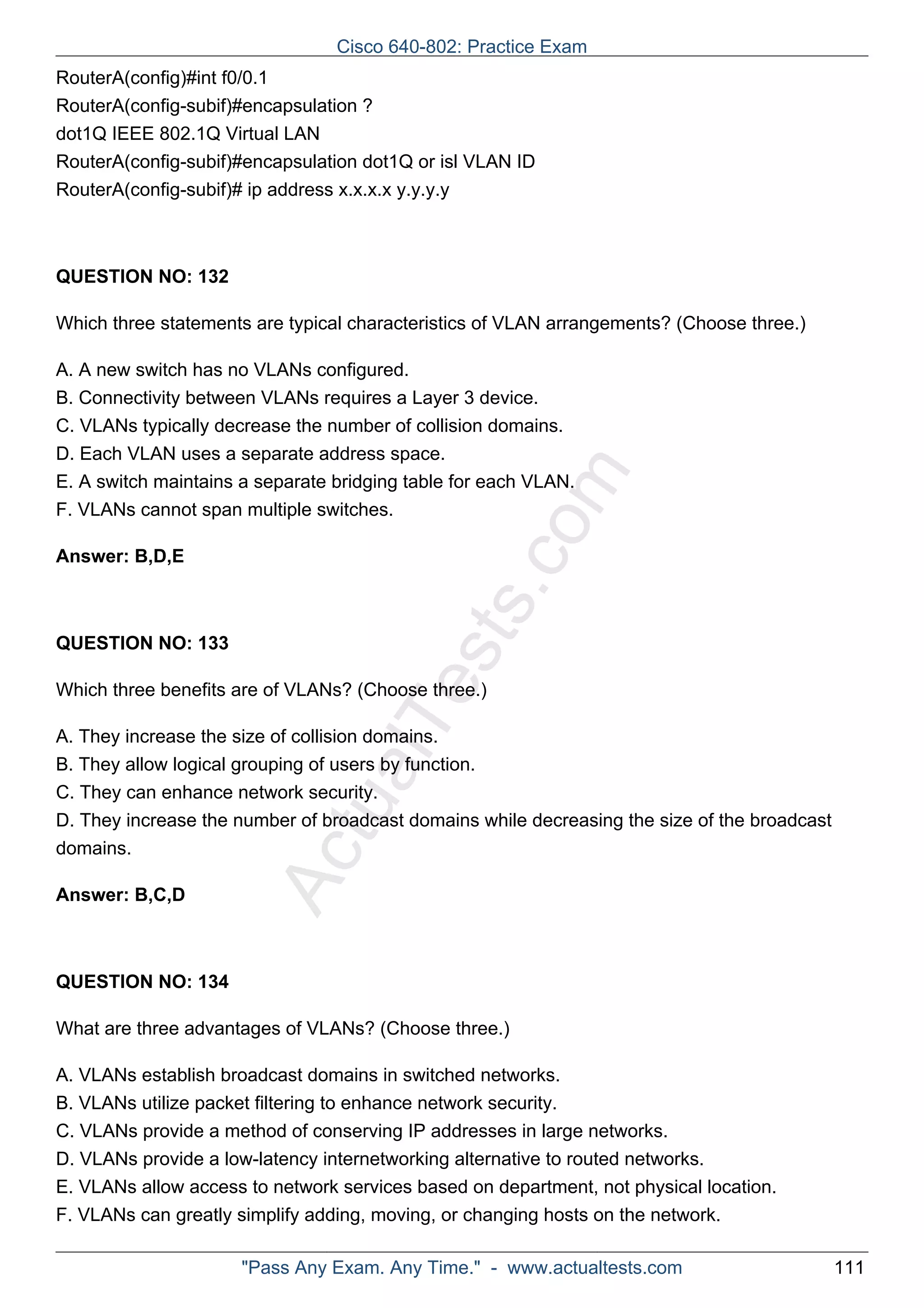
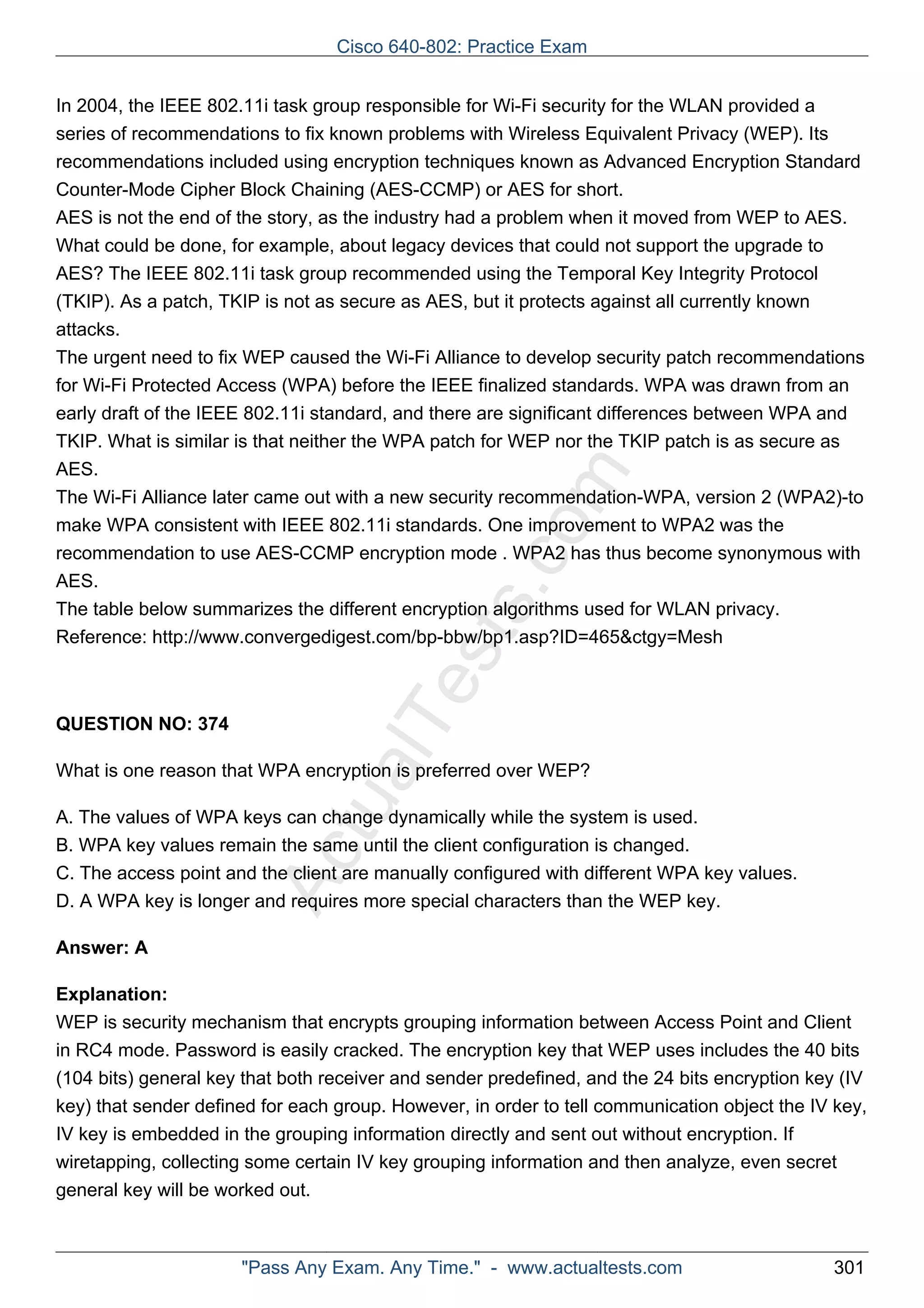
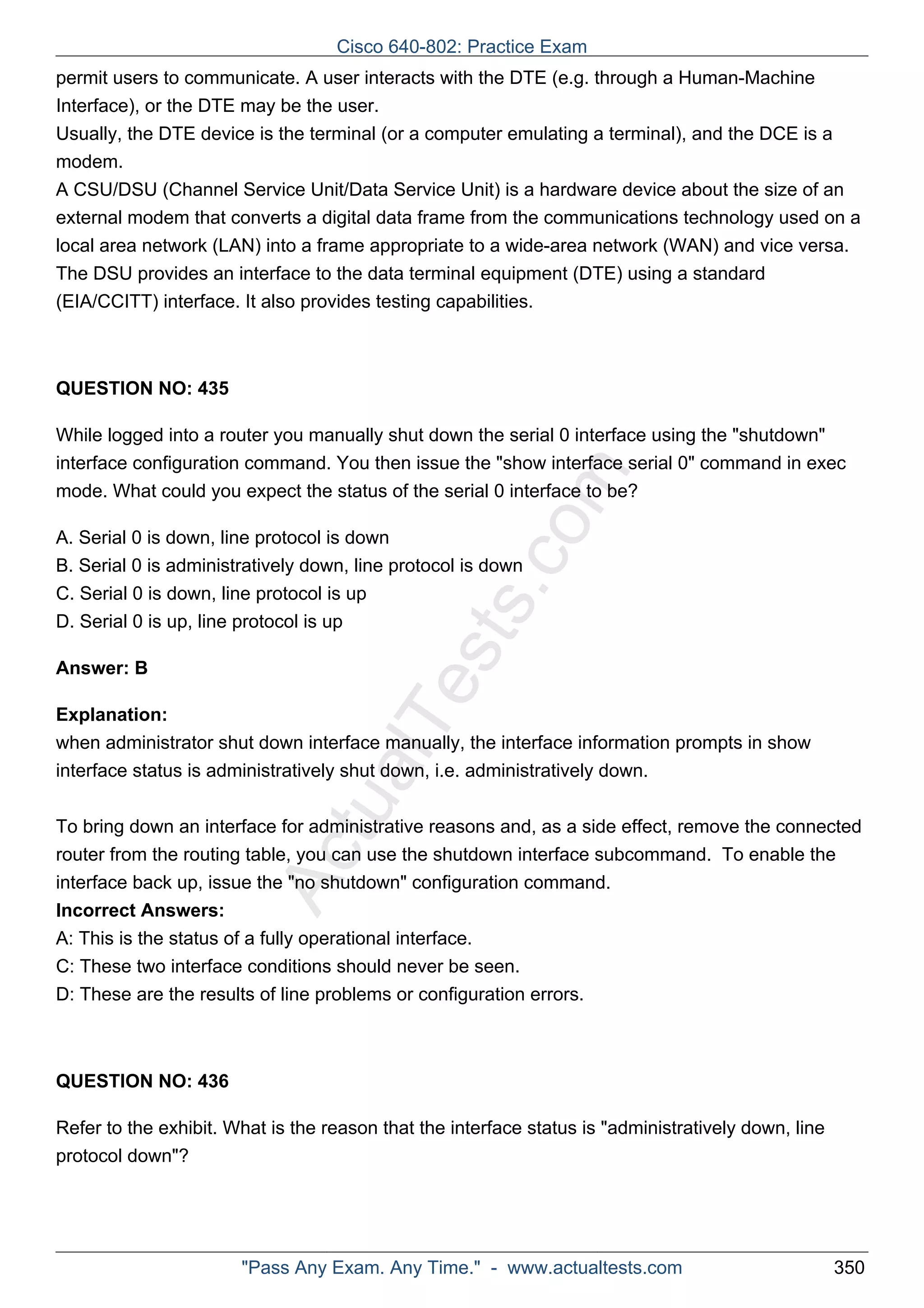
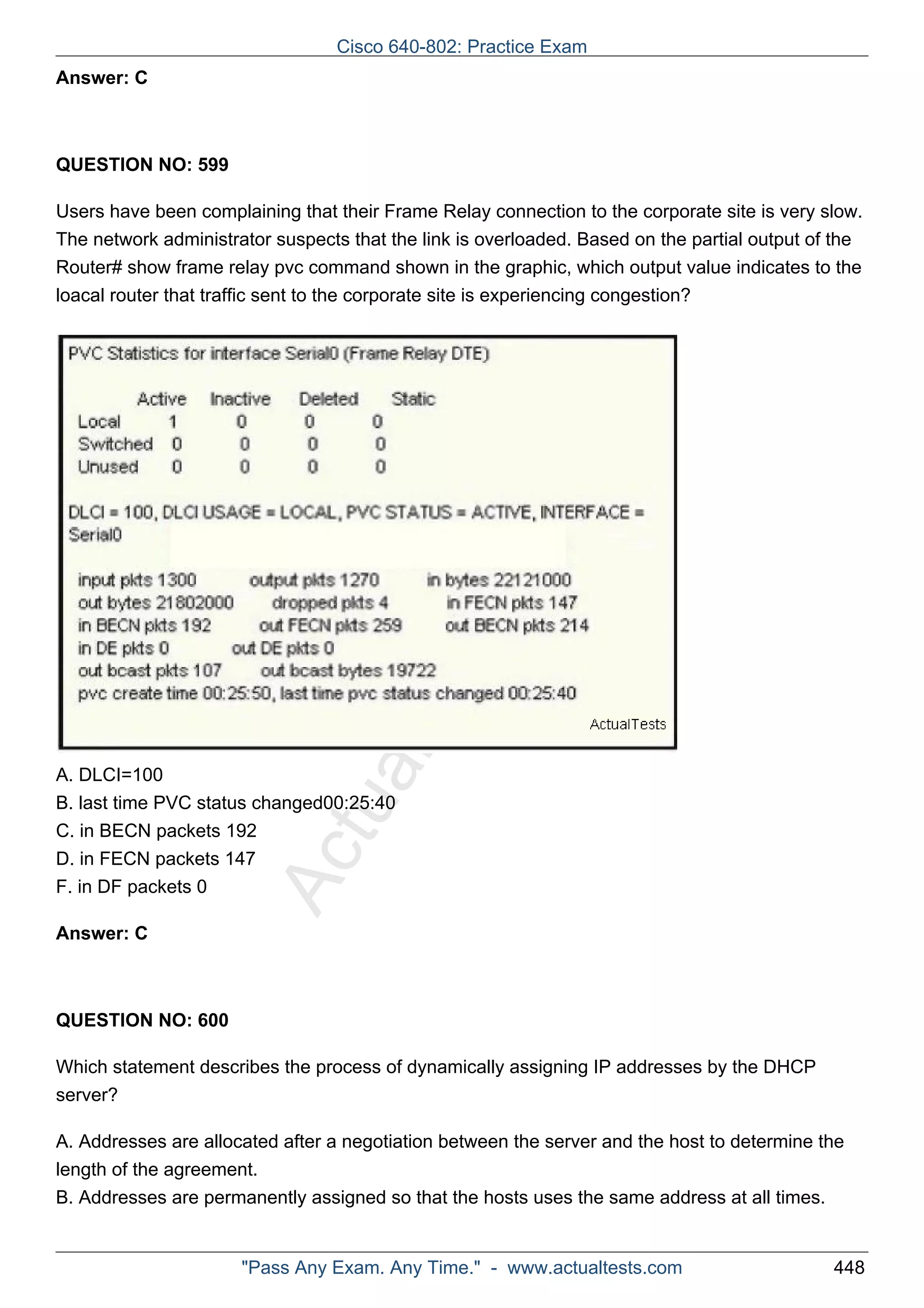
![Cisco 640-802: Practice Exam
interface Serial0/0
Ip address 192.168.36.14 255.255.255.252
Clockrate 64000
ActualTests.com
!
router eigrp 212
Network 192.168.36.0
Network 192.168.60.0
No auto-summary
!
RouterA# show ip route
192.168.36.0/30 is subnetted, 1 subnets
C 192.168.36.12 is directly connected, Serial0/0
192.168.60.0/24 is variably subnetted, 5 subnets, 2 masks
C 192.168.60.96/28 is directly connected, FastEthernet0/0
C 192.168.60.112/28 is directly connected, FastEthernet0/1
D 192.168.60.128/28 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial0/0
D 192.168.60.144/28 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial0/0
D 192.168.60.24/30 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial0/0
D* 198.0.18.0 [ 90/21024000 ] via 192.168.36.13, 00:00:57, Serial0/0
*********************************************************************************************************
Router2# show run
!
!
interface FastEthernet0/0
ip address 192.168.77.34 255.255.255.252
!
interface FastEtherner0/1
ip address 192.168.60.65 255.255.255.240
!
interface FastEthernet1/0
ip address 192.168.60.81 255.255.255.240
!
!
router eigrp 22
network 192.168.60.0
network 192.168.77.0
no auto-summary
"Pass Any Exam. Any Time." - www.actualtests.com 476](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-476-2048.jpg)
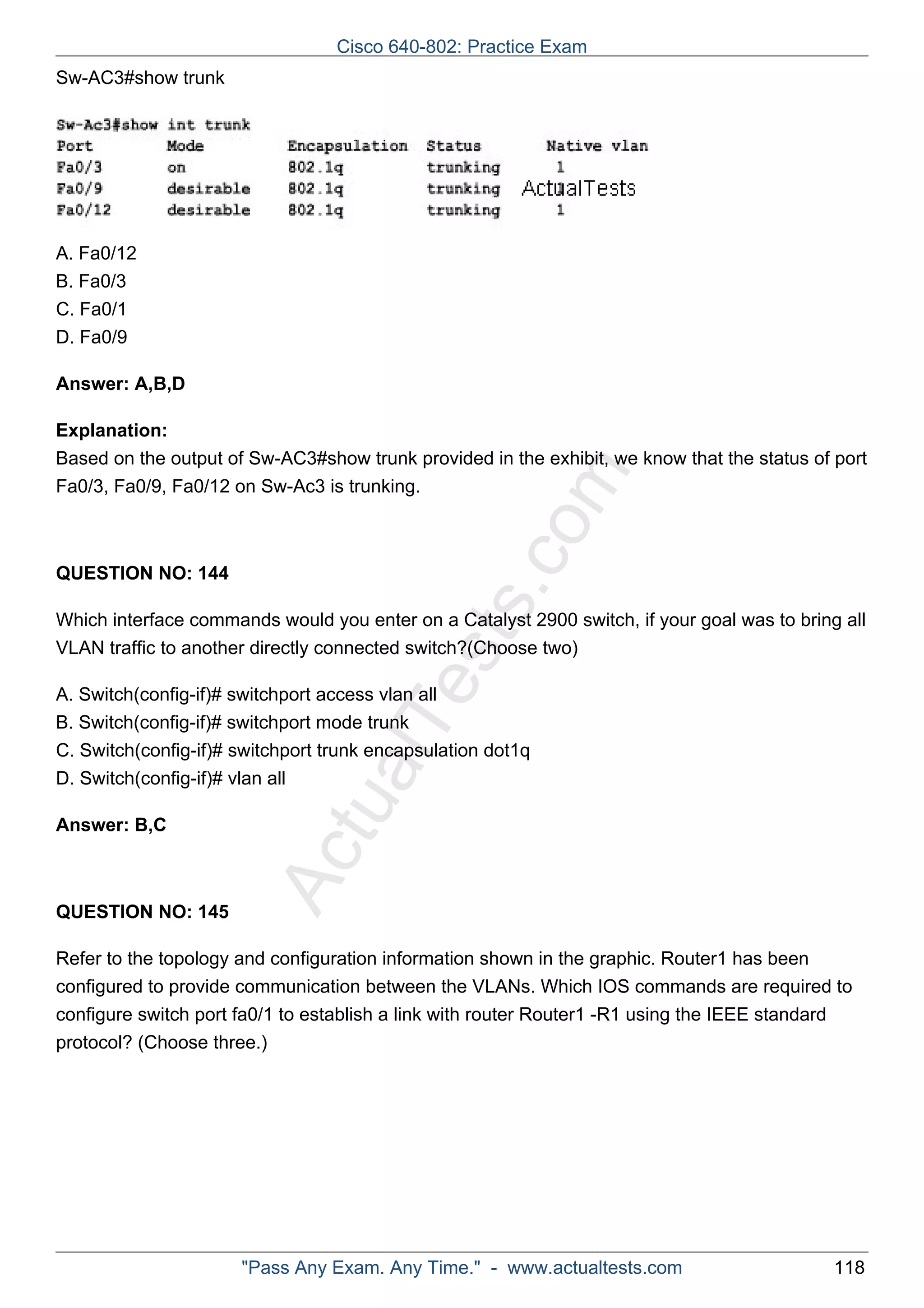
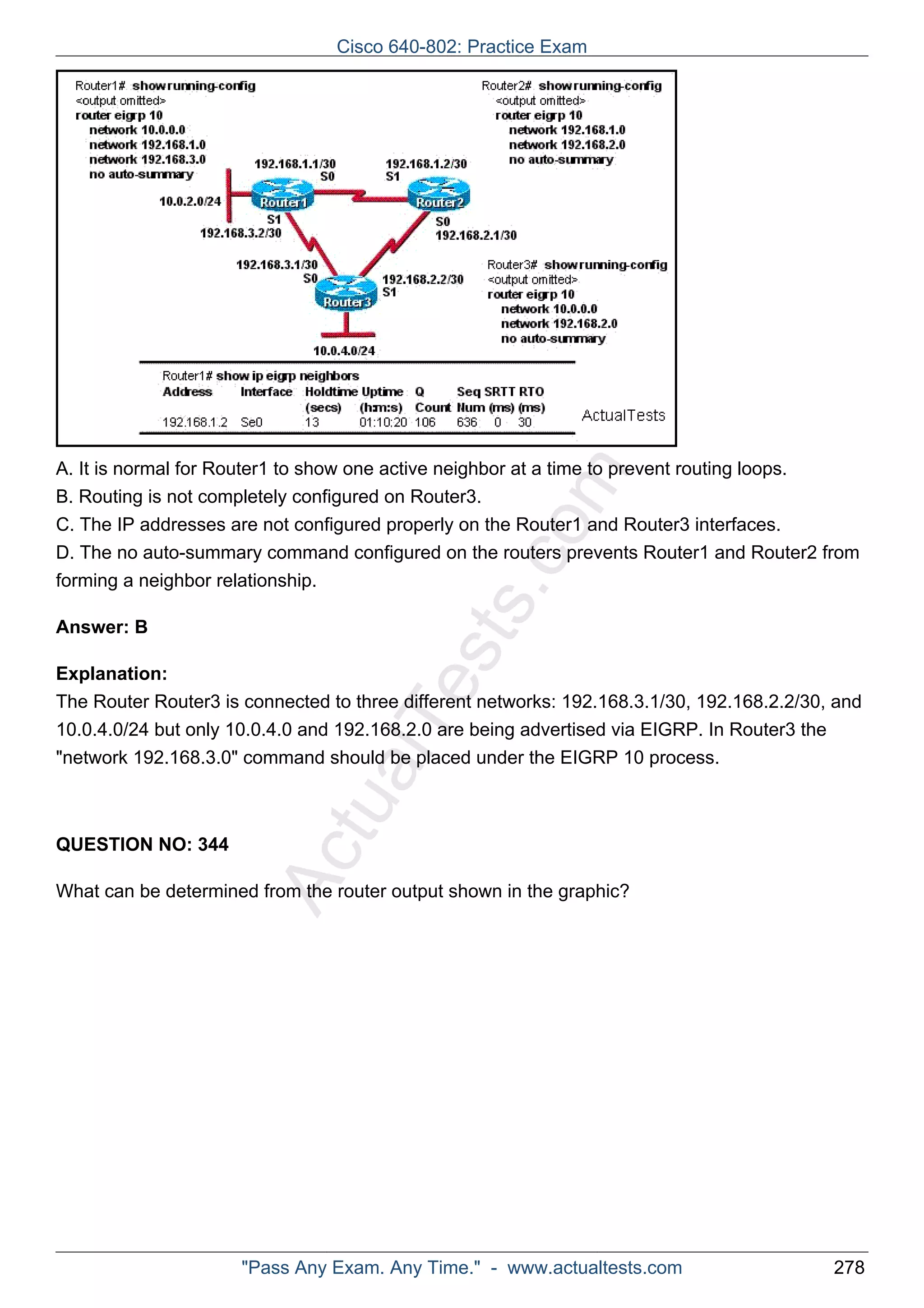
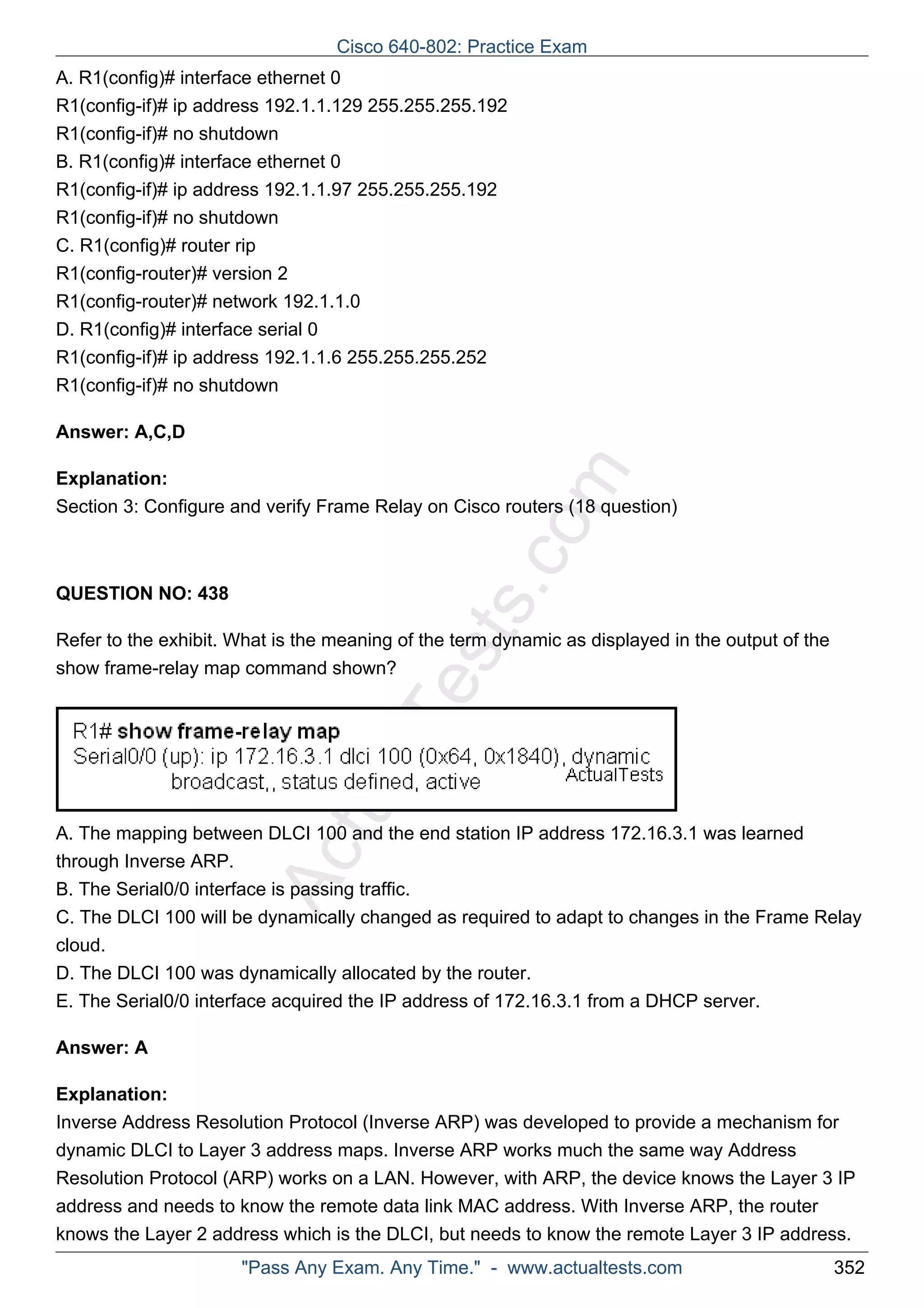
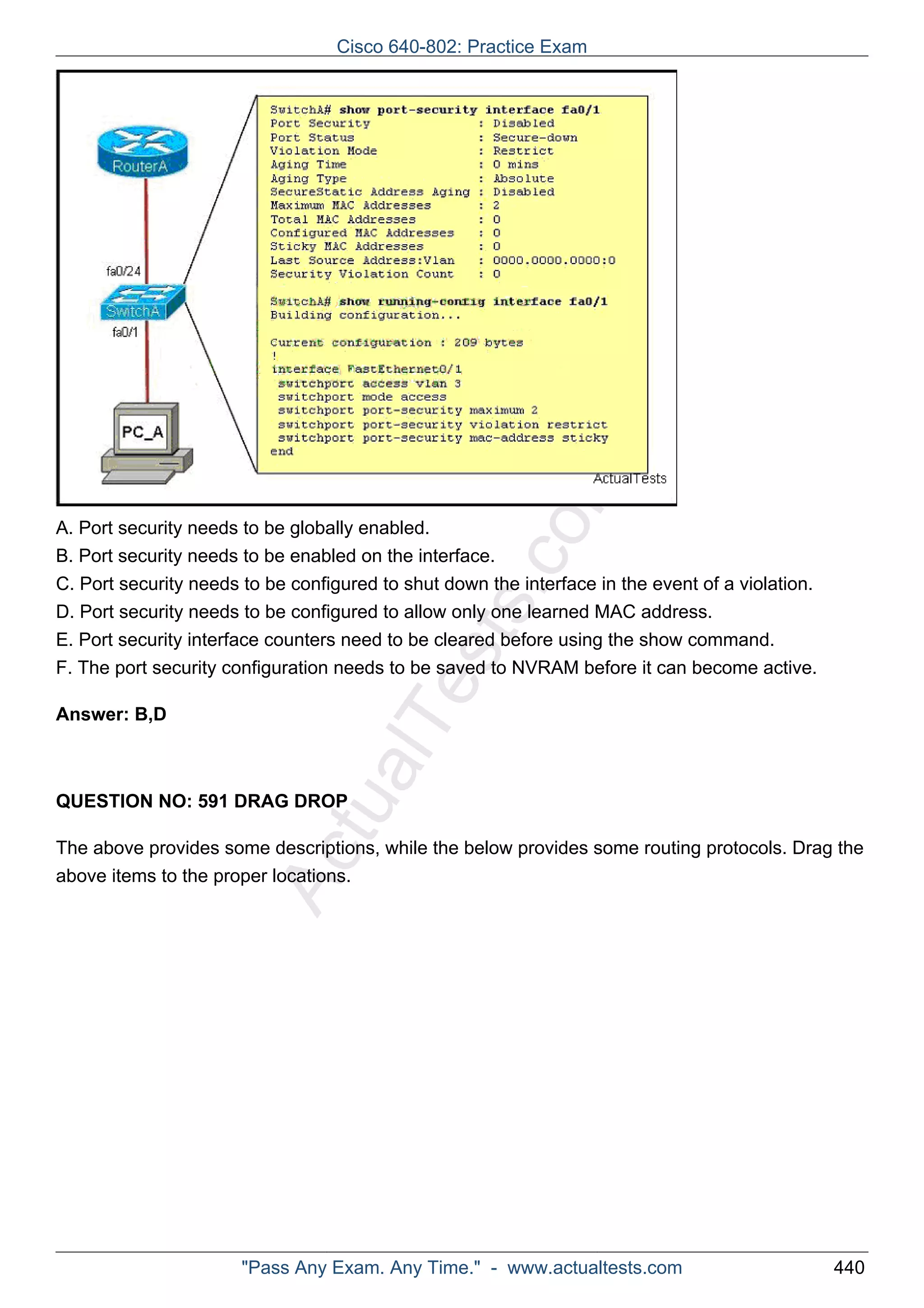
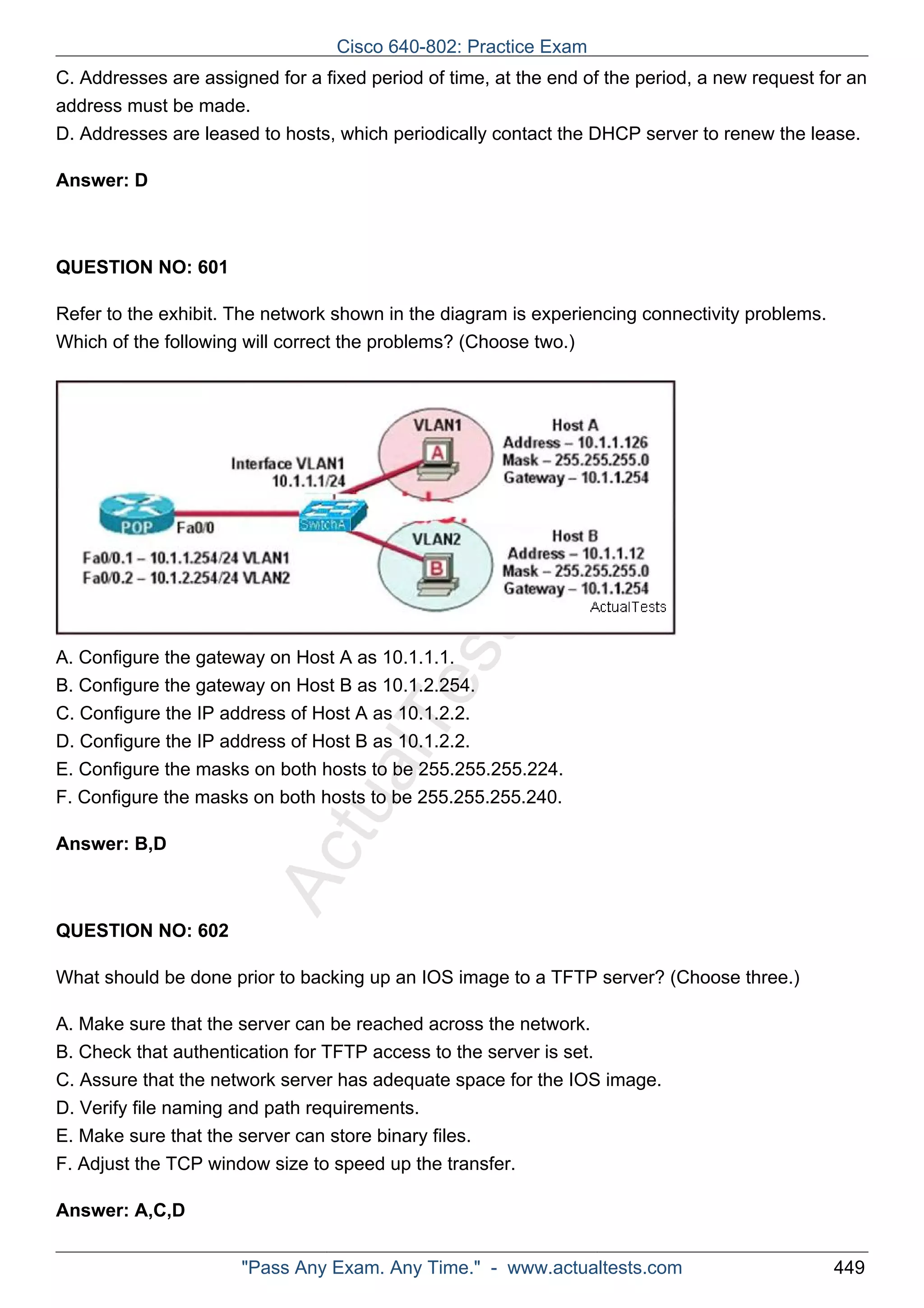
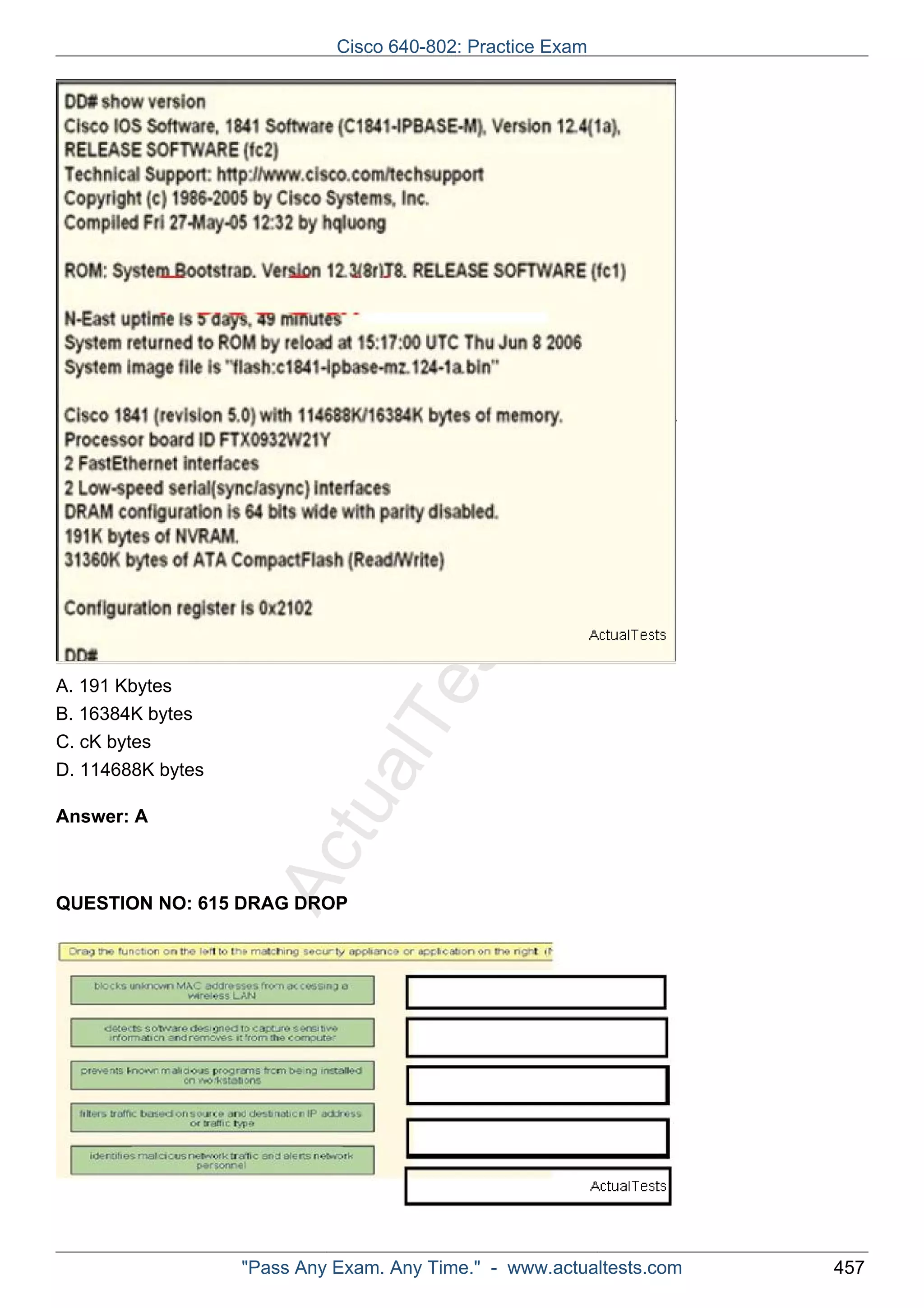
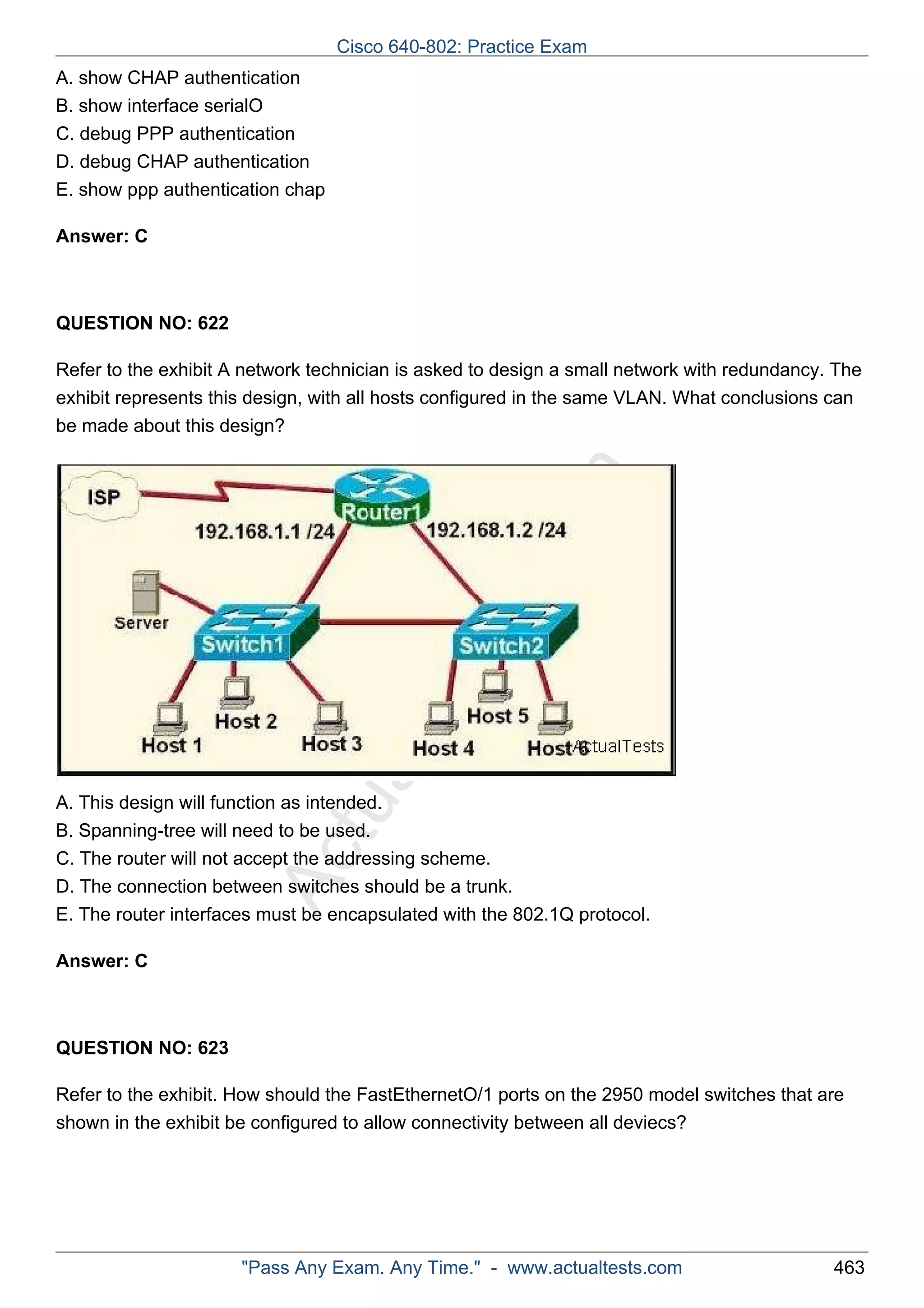
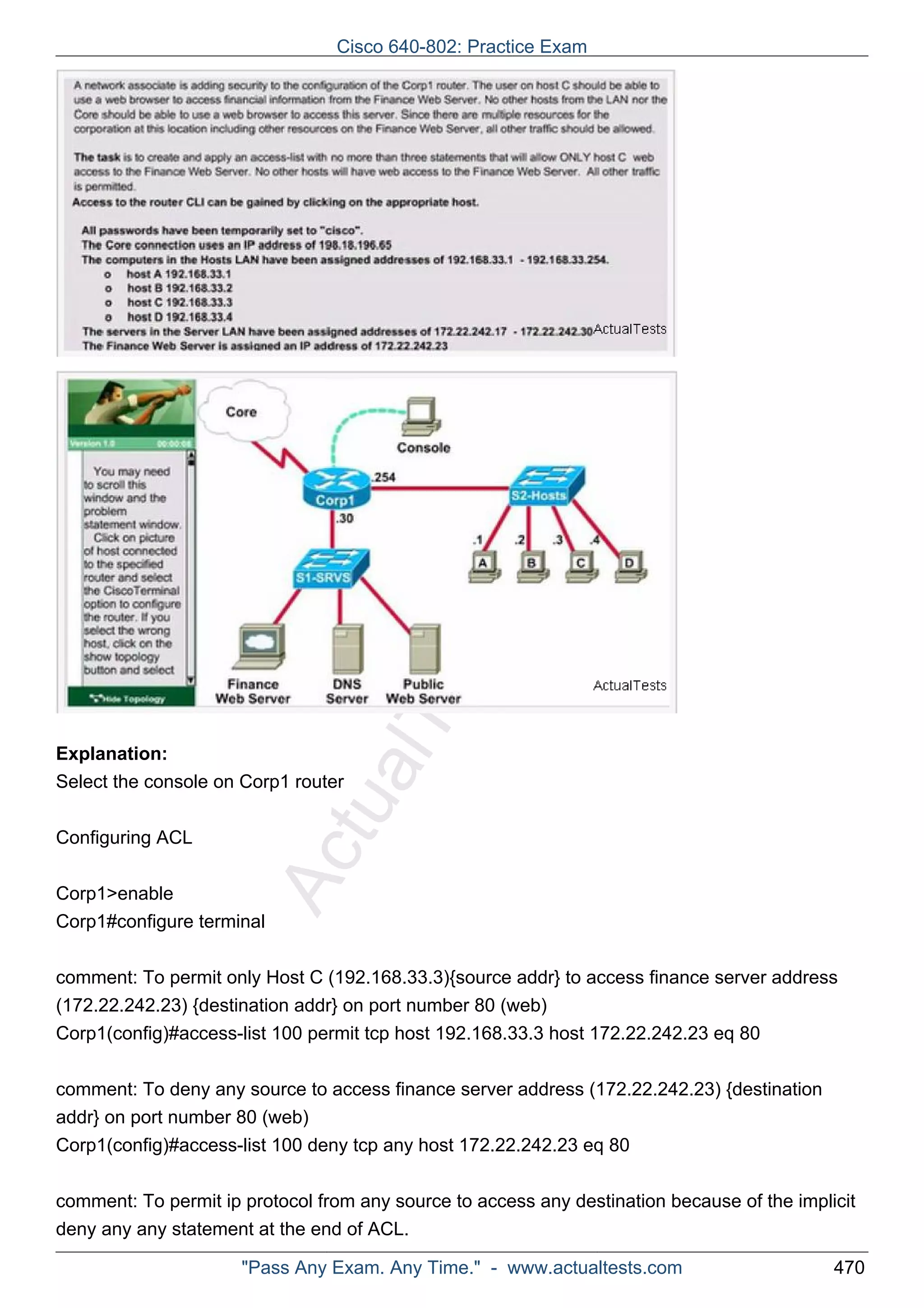
![Cisco 640-802: Practice Exam
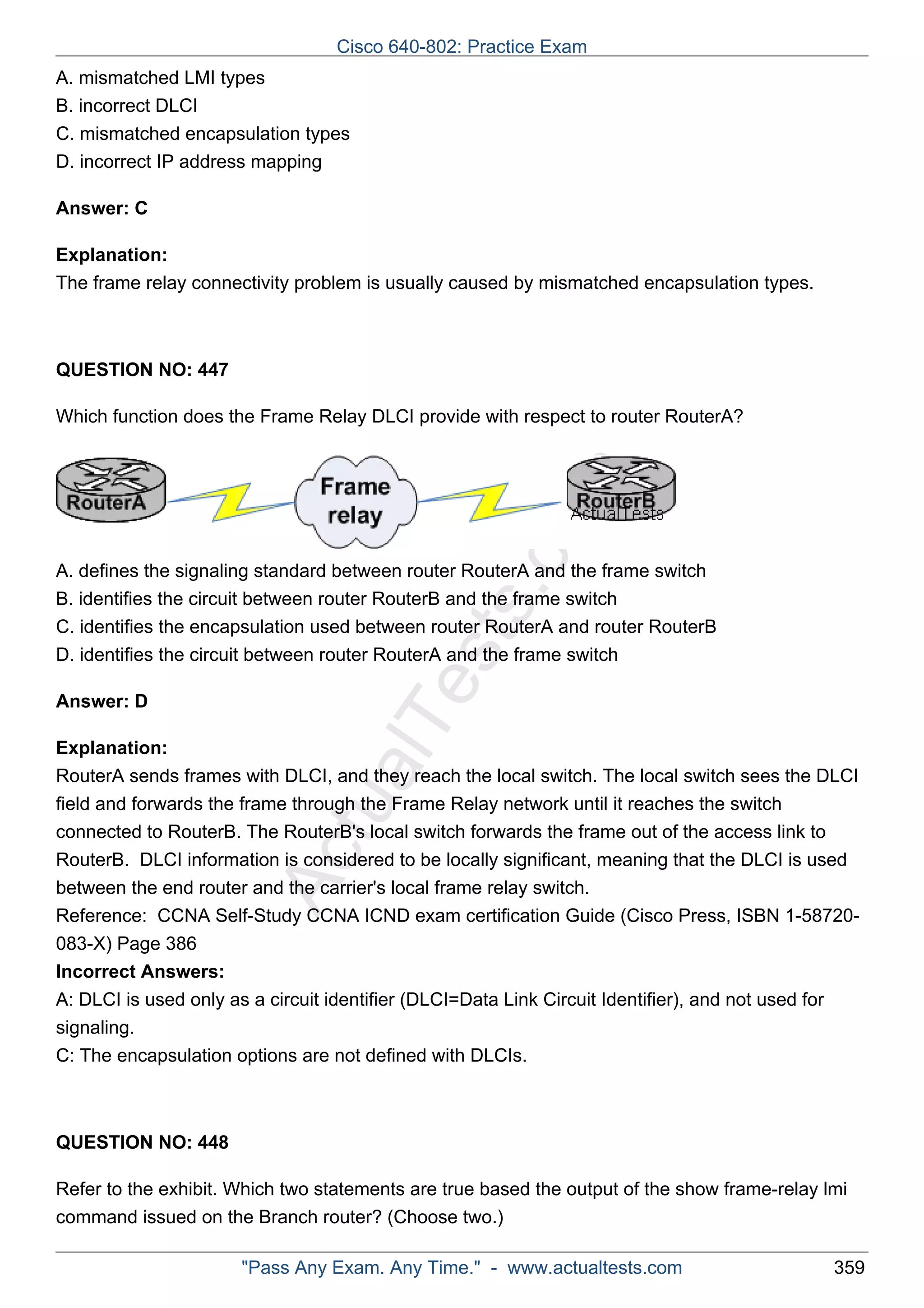
Router2# show ip route
192.168.60.0/28 is subnetted, 2 subnets
C 192.168.60.80 is directly connected, FastEthernet1/0
C 192.168.60.64 is directly connected, FastEthernet0/1
192.168.77.0/30 is subnetted, 1 subnets
C 192.168.77.32 is directly connected, FastEthernet0/0
*********************************************************************************************************
RouterB# show run
interface FastEthernet0/0
ip address 192.168.60.129 255.255.255.240
!
interface FastEthernet0/1
ip address 192.168.60.145 255.255.255.240
!
interface Serial0/1
ip address 192.168.60.26 255.255.255.252
ActualTests.com
router eigrp 212
network 192.168.60.0
network 192.168.60.0
RouterB# show ip route
192.168.60.0/24 is variably subnetted, 5 subnets, 2 masks
C 192.168.60.24/30 is directly connected, Serial0/1
C 192.168.60.128/28 is directly connected, FastEthernet0/0
C 192.168.60.144/28 is directly connected, FastEthernet0/1
D 192.168.60.96/28 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial0/1
D 192.168.60.112/28 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial0/1
192.168.36.0/30 is subnetted, 1 subnets
D 192.168.36.12 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial0/1
D* 198.0.18.0 [ 90/21024000 ] via 192.168.60.25, 00:00:57, Serial0/1
*********************************************************************************************************
ROUTER1# show run
!
interface FastEthernet0/0
ip address 192.168.77.33 255.255.255.252
!
"Pass Any Exam. Any Time." - www.actualtests.com 477](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-477-2048.jpg)
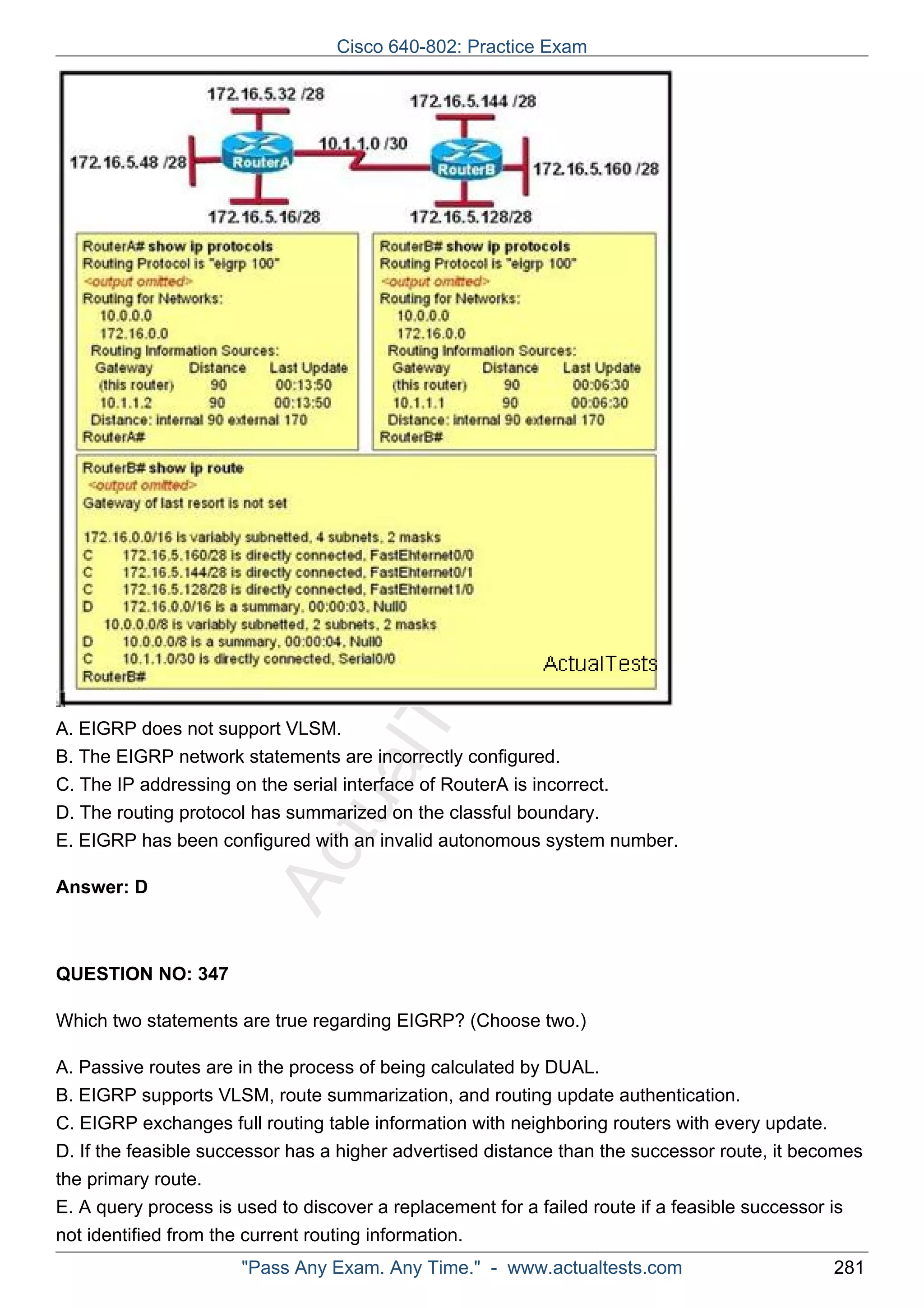
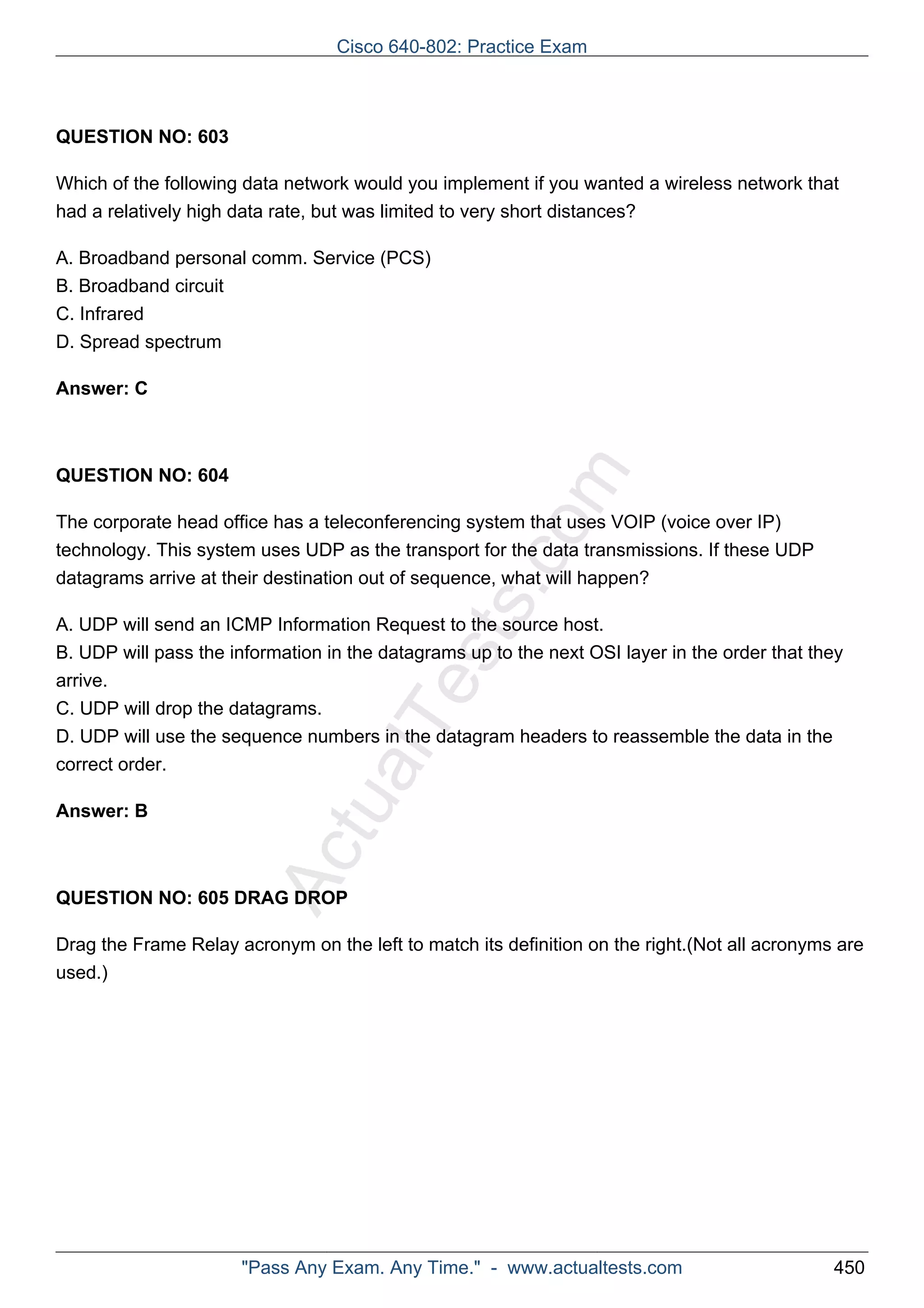
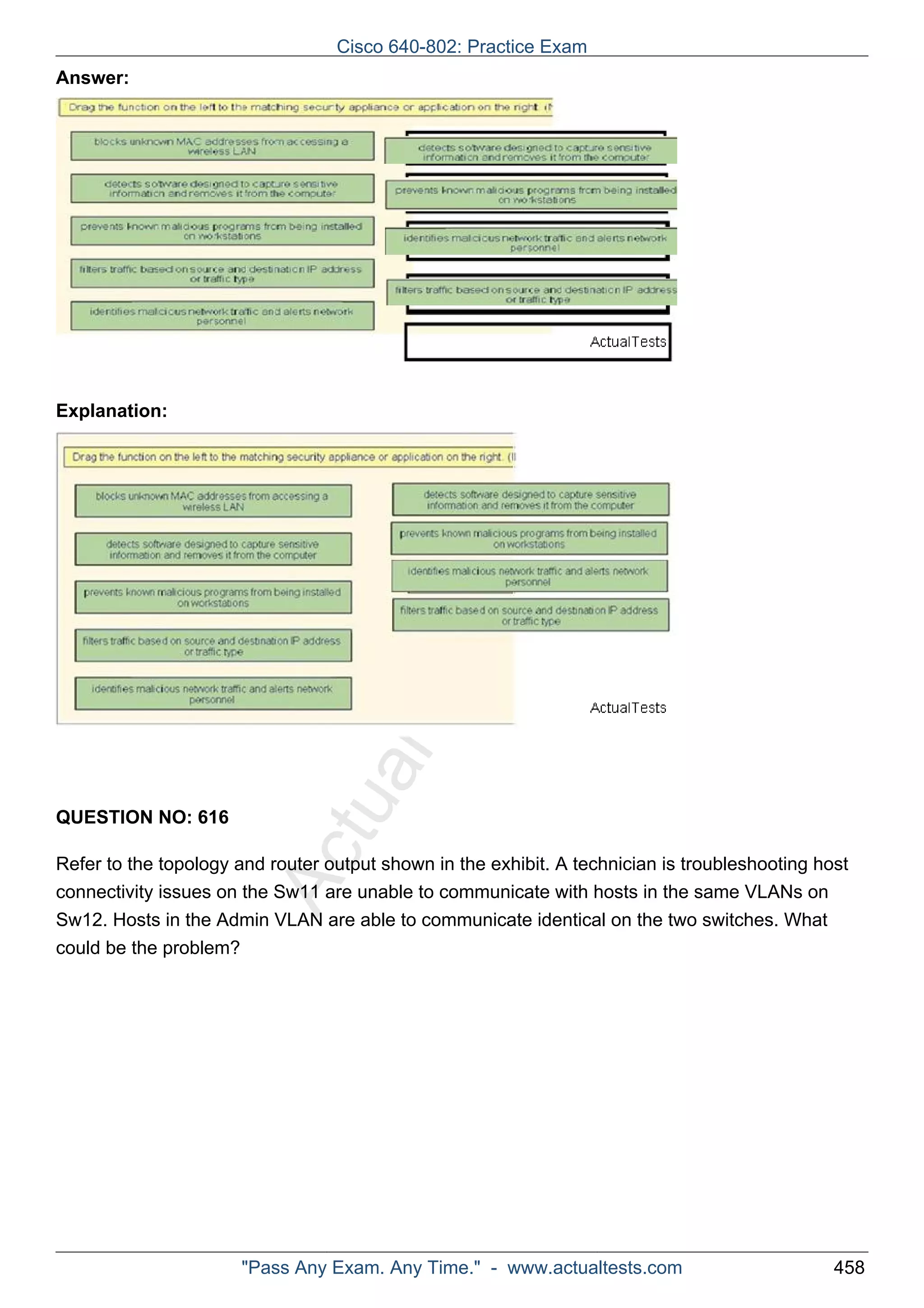
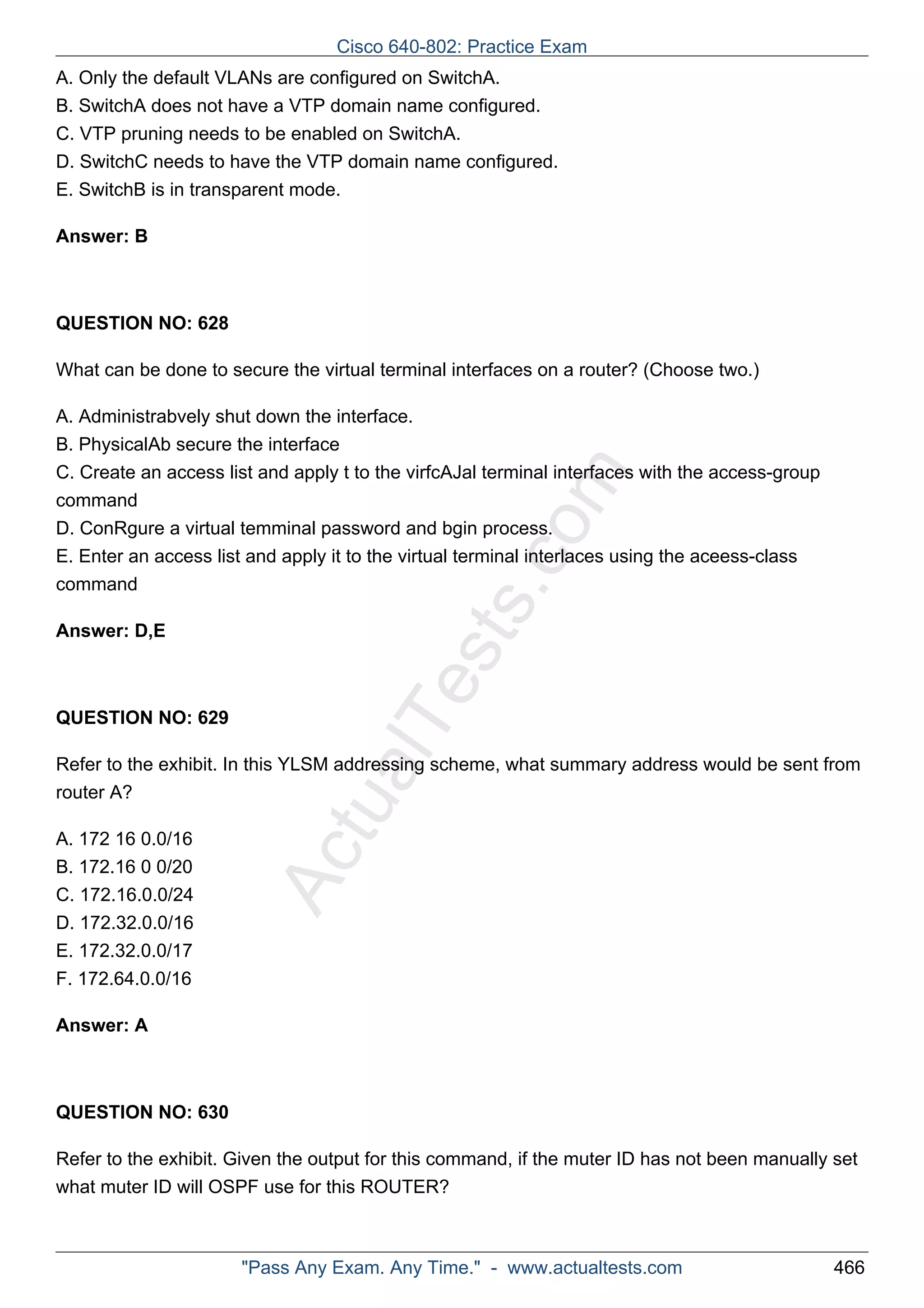
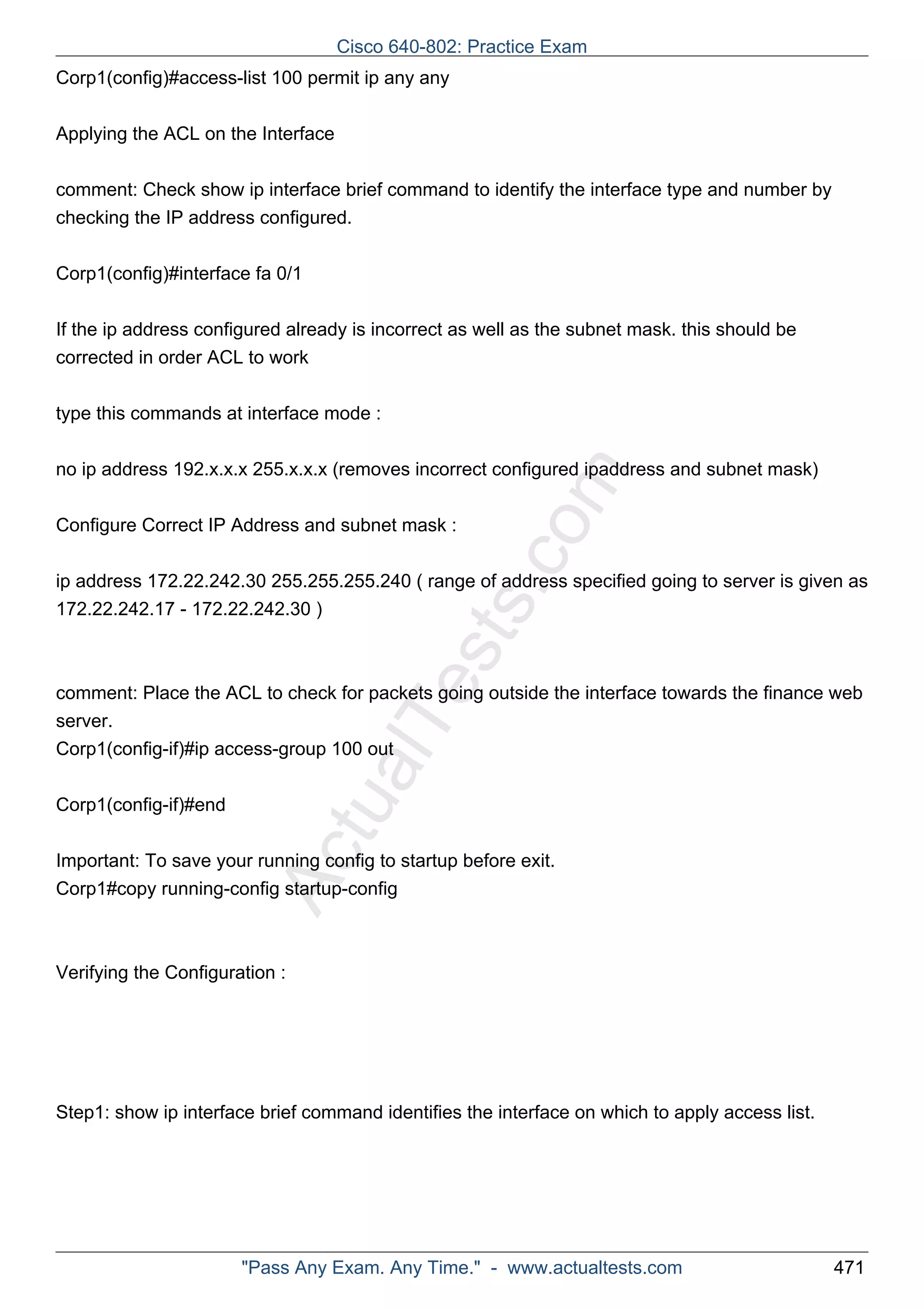
![interface Serial1/0
ip address 198.0.18.6 255.255.255.0
!
interface Serial0/0
ip address 192.168.36.13 255.255.255.252
clockrate 64000
!
interface Serial0/1
ip address 192.168.60.25 255.255.255.252
clockrate 64000
!
!
router eigrp 212
network 192.168.36.0
network 192.168.60.0
network 192.168.85.0
network 198.0.18.0
no auto-summary
!
ip classless
ip default-network 198.0.18.0
ip route 0.0.0.0 0.0.0.0 198.0.18.5
ip http server
ActualTests.com
ROUTER1# sh ip route
192.168.36.0/30 is subnetted, 1 subnets
C 192.168.36.12 is directly connected, Serial0/0
192.168.60.0/24 is variably subnetted, 5 subnets, 2 masks
C 192.168.60.24/30 is directly connected, Serial0/1
D 192.168.60.128/28 [ 90/21026560 ] via 192.168.60.26, 00:00:57, Serial0/1
D 192.168.60.144/28 [ 90/21026560 ] via 192.168.60.26, 00:00:57, Serial0/1
D 192.168.60.96/28 [ 90/21026560 ] via 192.168.36.14, 00:00:57, Serial0/0
192.168.77.0/30 is subnetted, 1 subnets
C 192.168.77.32 is directly connected, FastEthernet0/0
C 198.0.18.0/24 is directly connected, Serial1/0
*S 0.0.0.0 via 198.0.18.5
Explanation:
Please input commands here:
Router2>enable
Router2#config t
Cisco 640-802: Practice Exam
"Pass Any Exam. Any Time." - www.actualtests.com 478](https://image.slidesharecdn.com/640-802-141021071005-conversion-gate01/75/CCNA-DUMPS-640-802-478-2048.jpg)