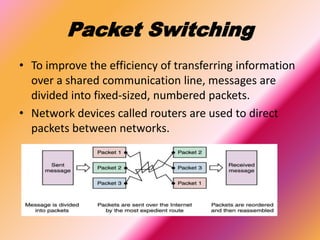
This document provides an overview of computer networks and the Internet. It defines a computer network as a collection of connected computing devices that share resources. The main advantages are sharing devices and files, communication capabilities, and centralized data backup. Challenges include high setup costs and risk of viruses or hacking. It describes common network models like client-server, and different types of networks by transmission range. The Internet is defined as a global network of networks using TCP/IP that links billions of devices worldwide. Key components that enable the Internet include backbone networks, ISPs, packet switching, and TCP and IP protocols.