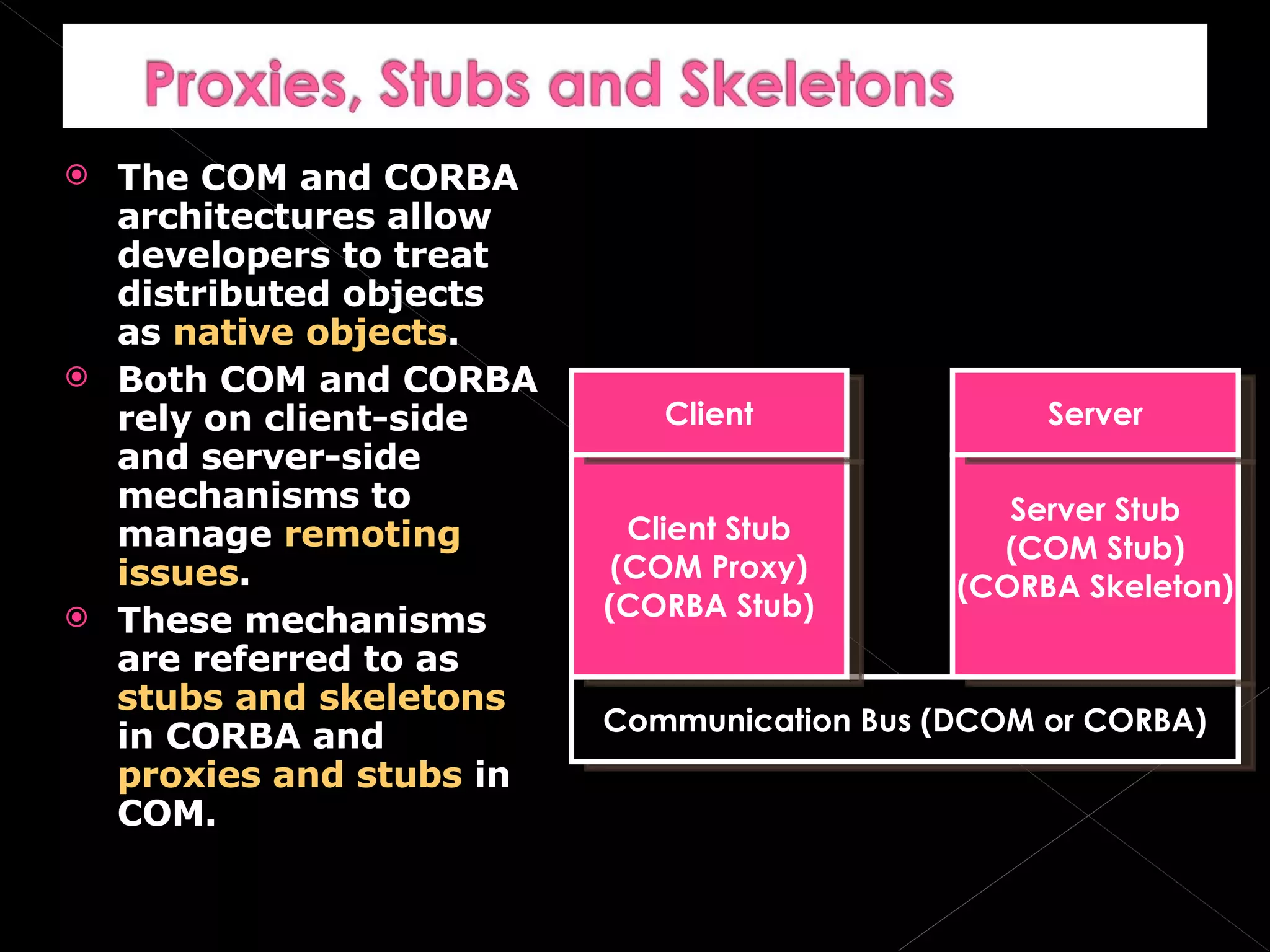
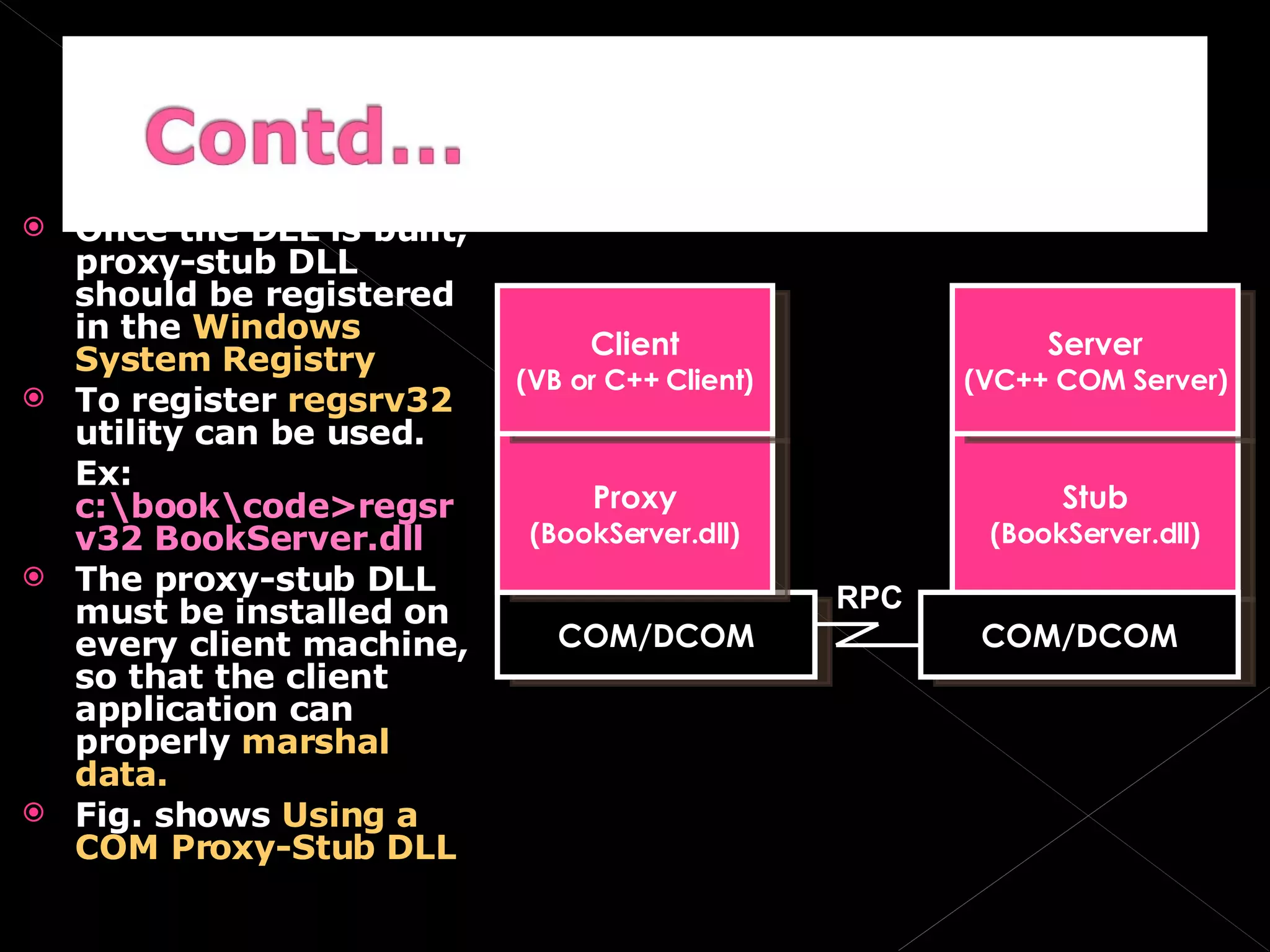
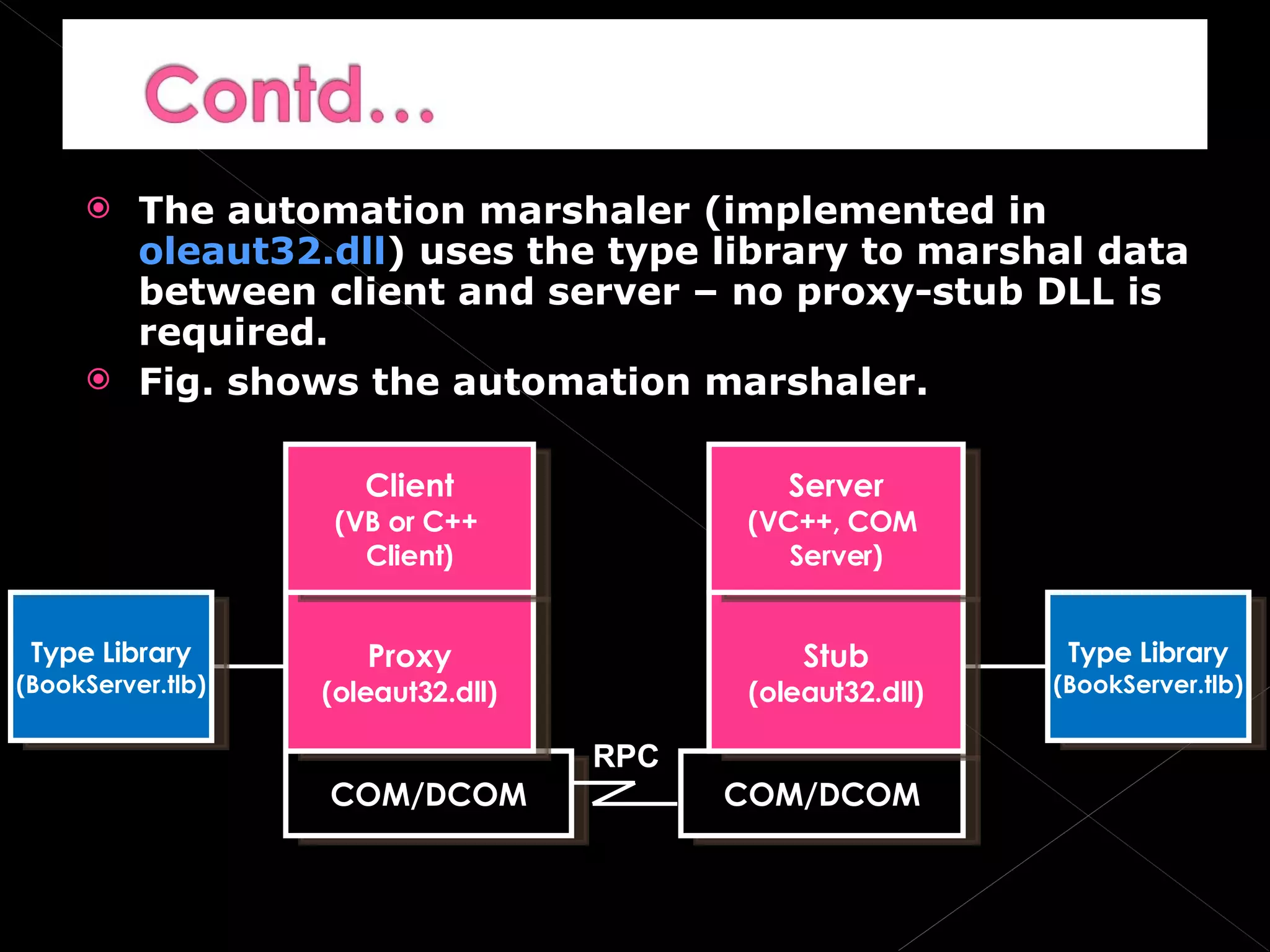
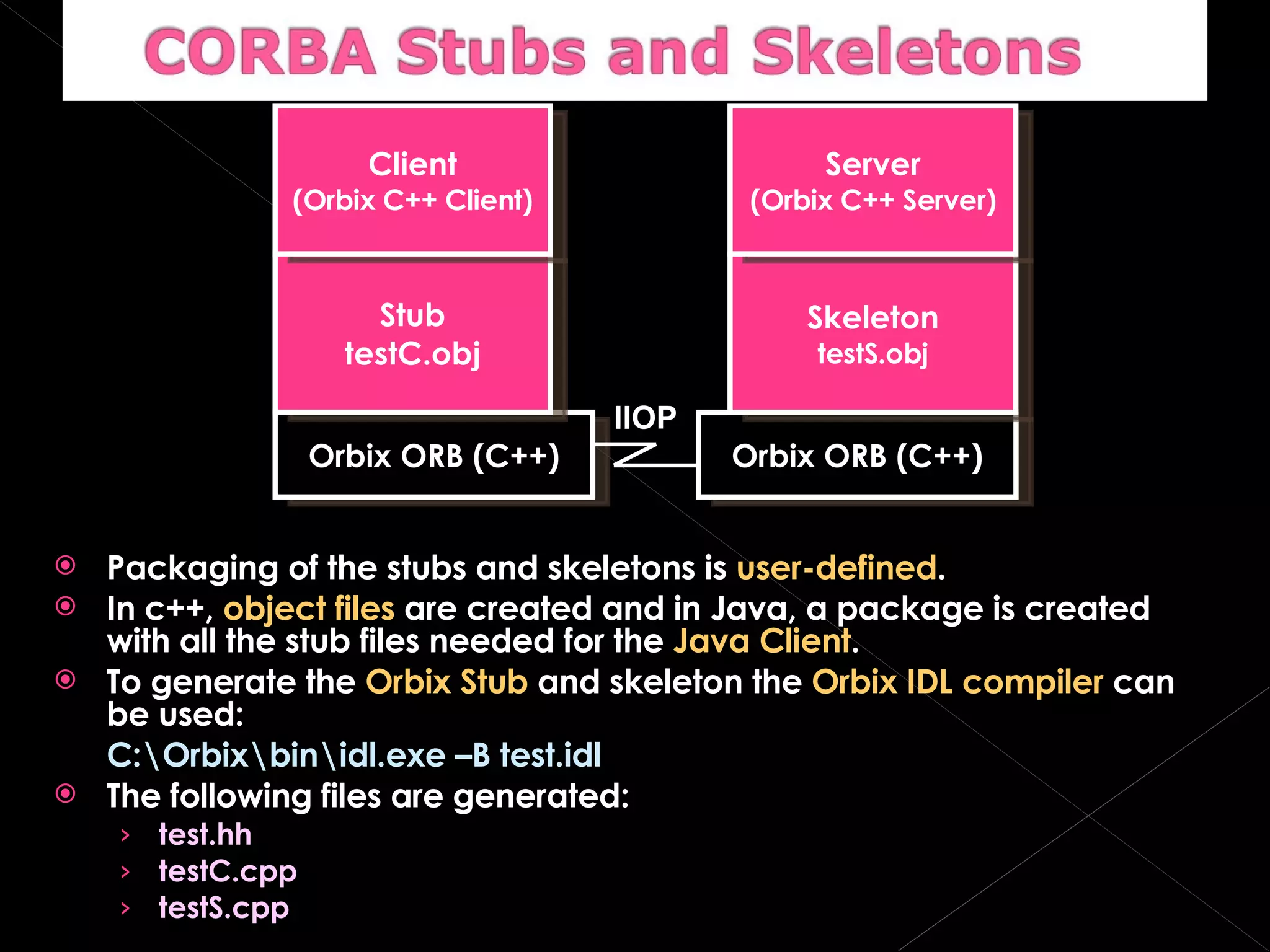
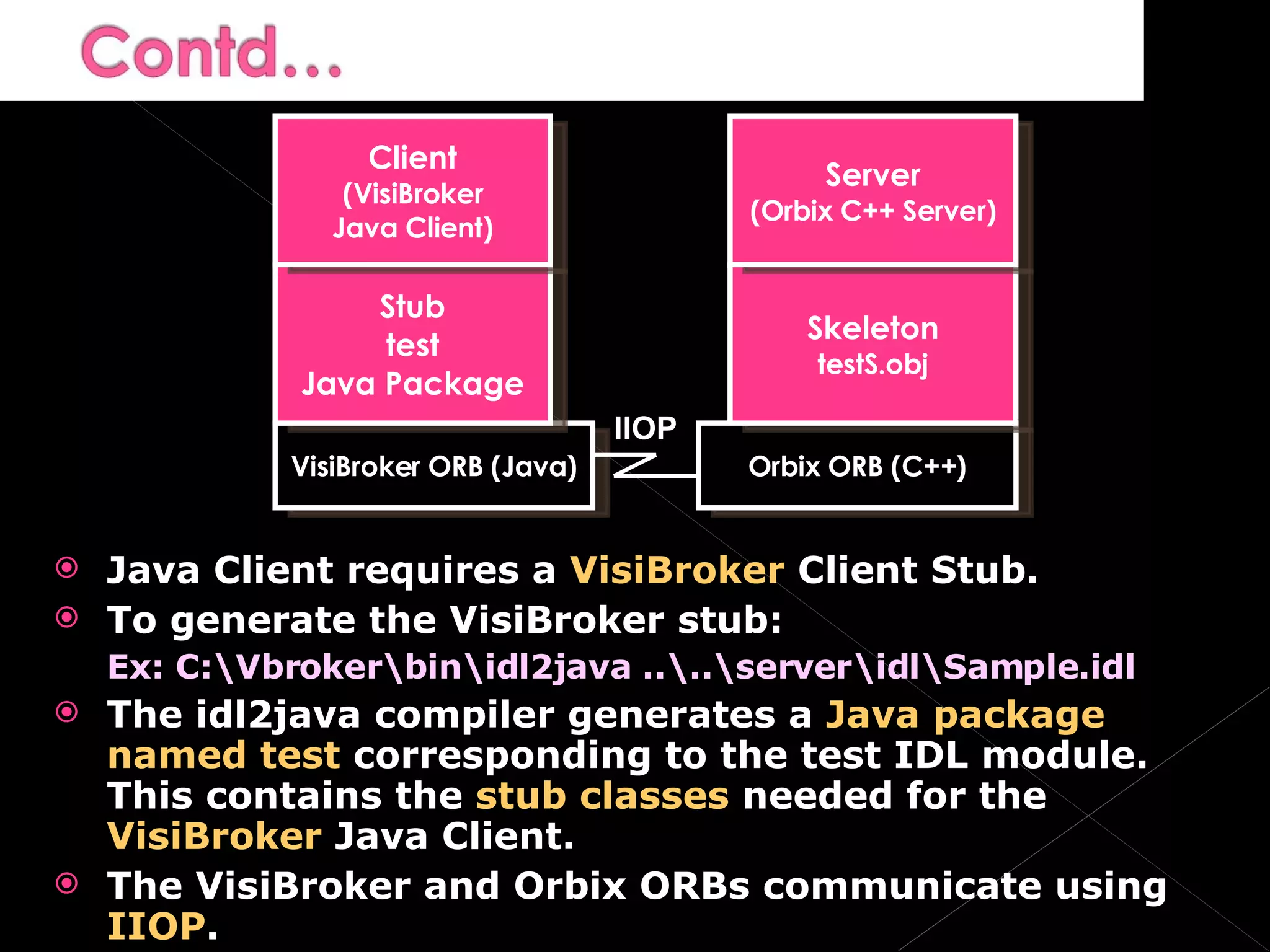
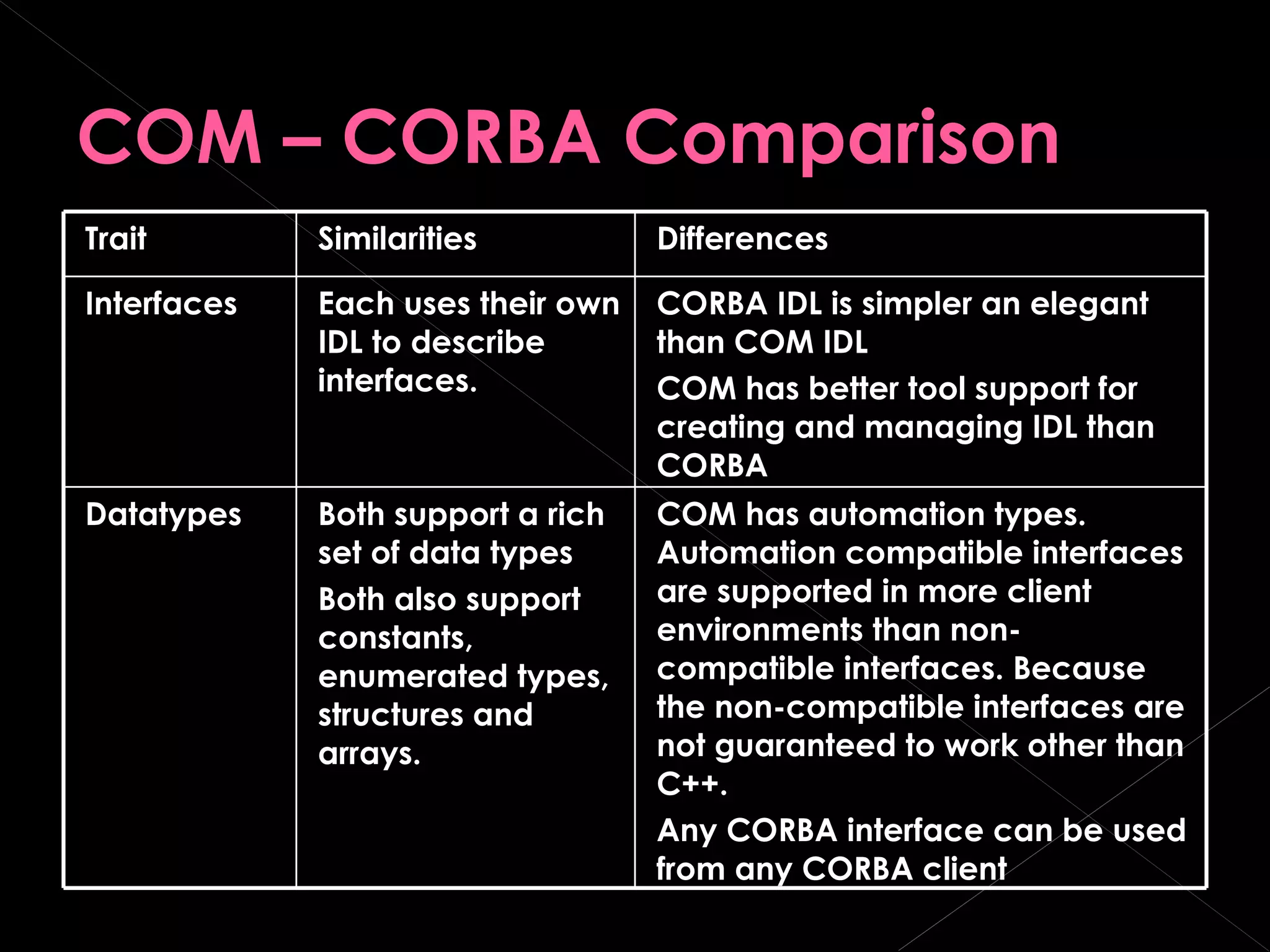
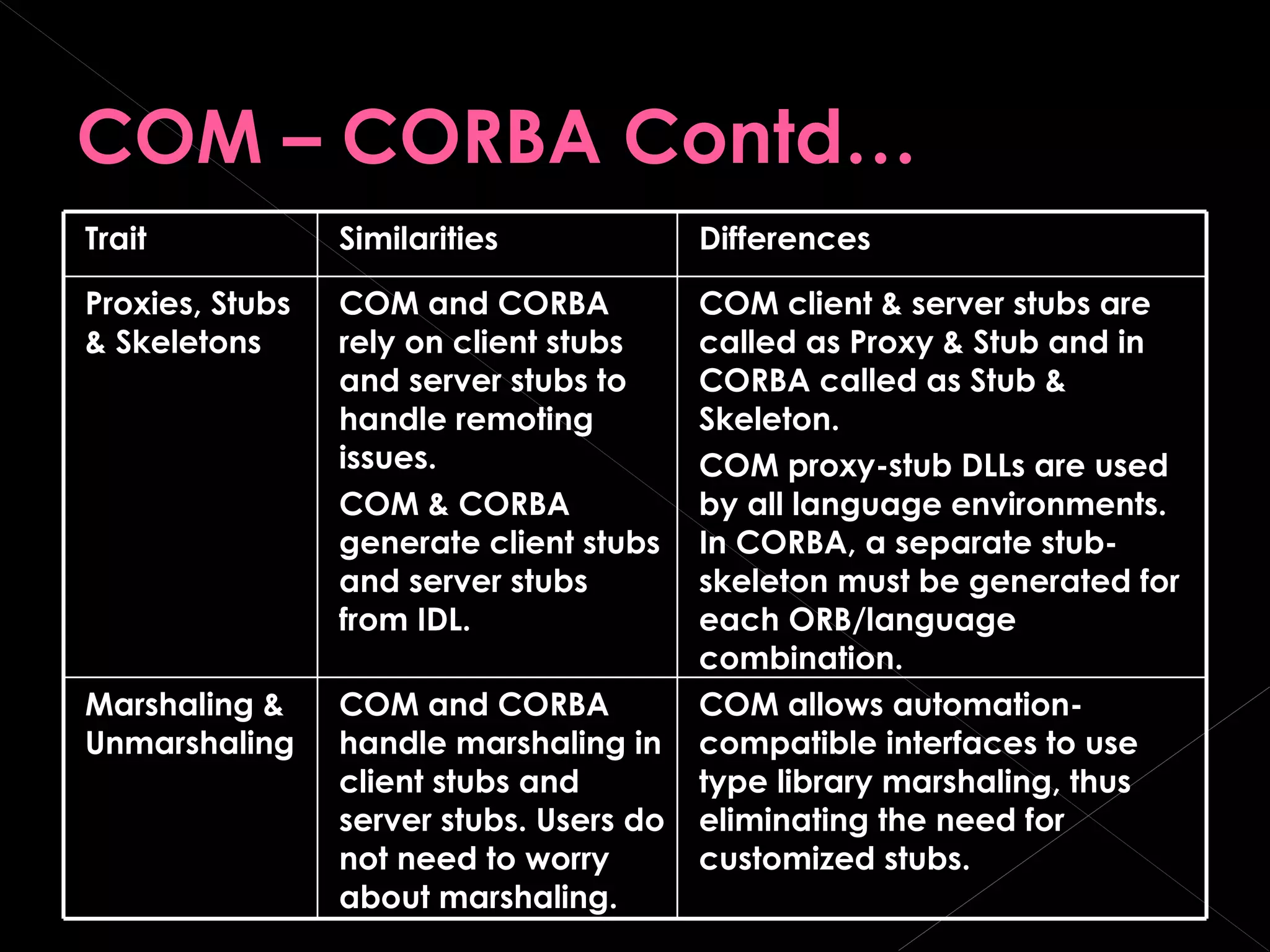
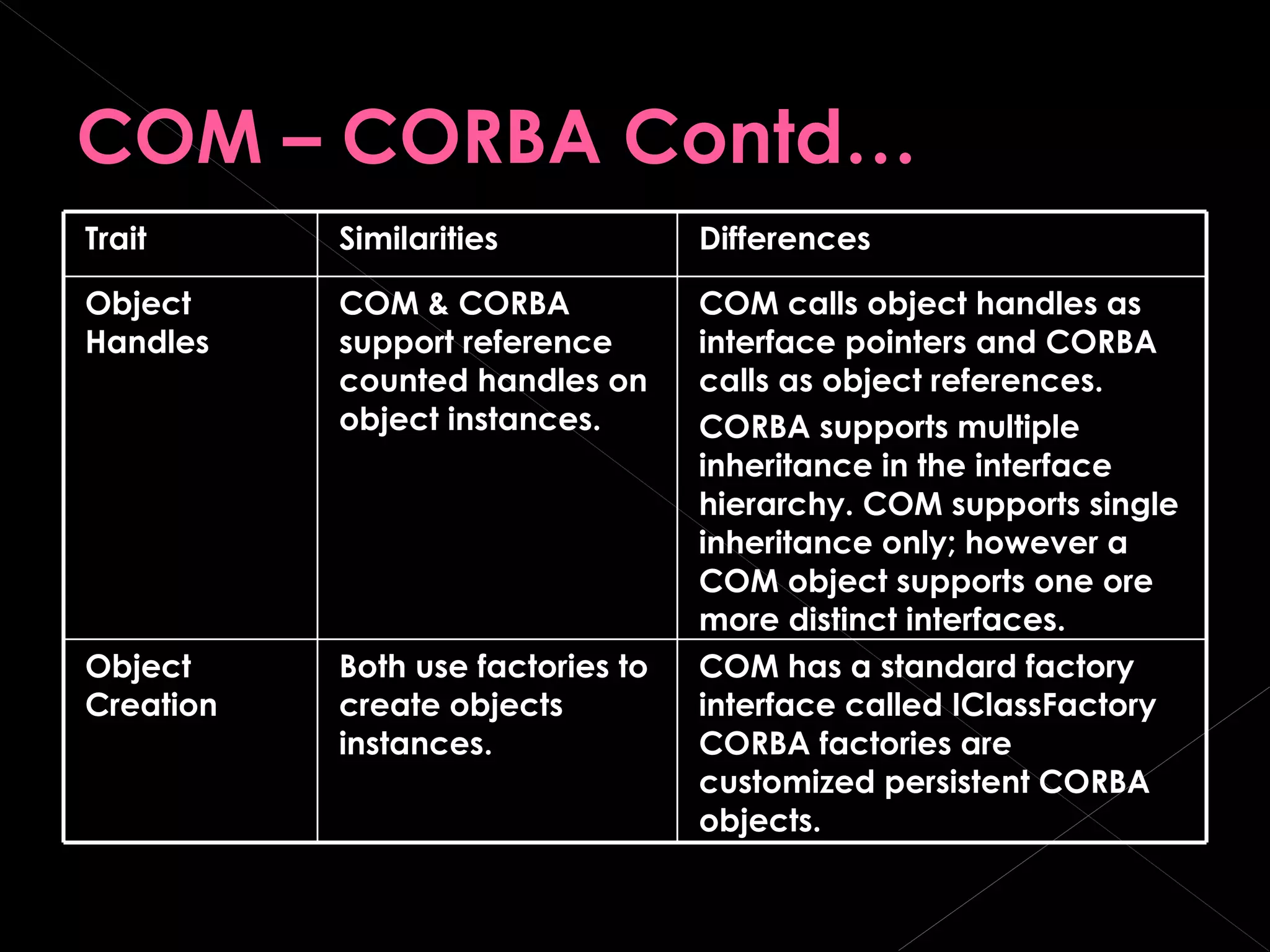
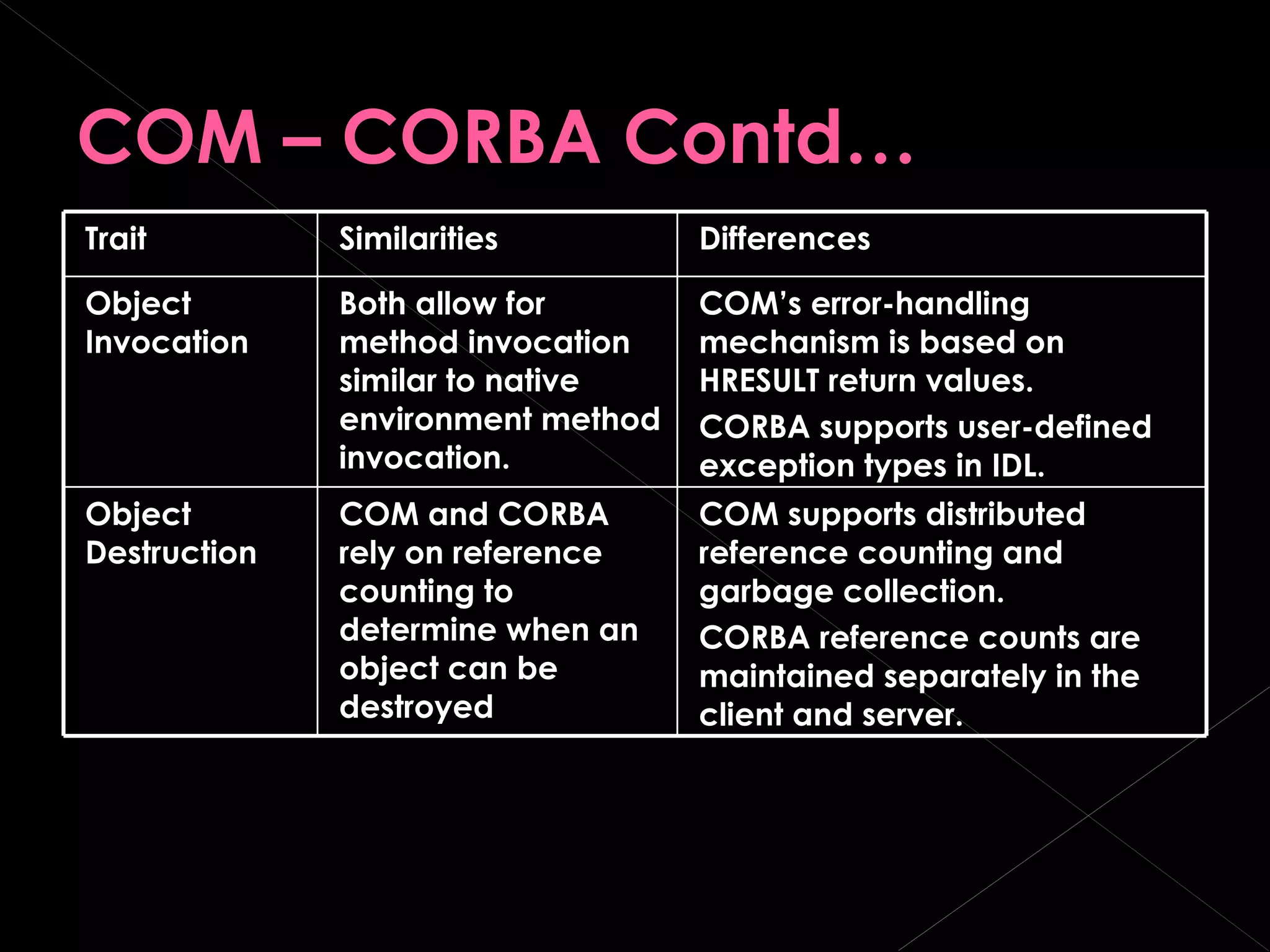
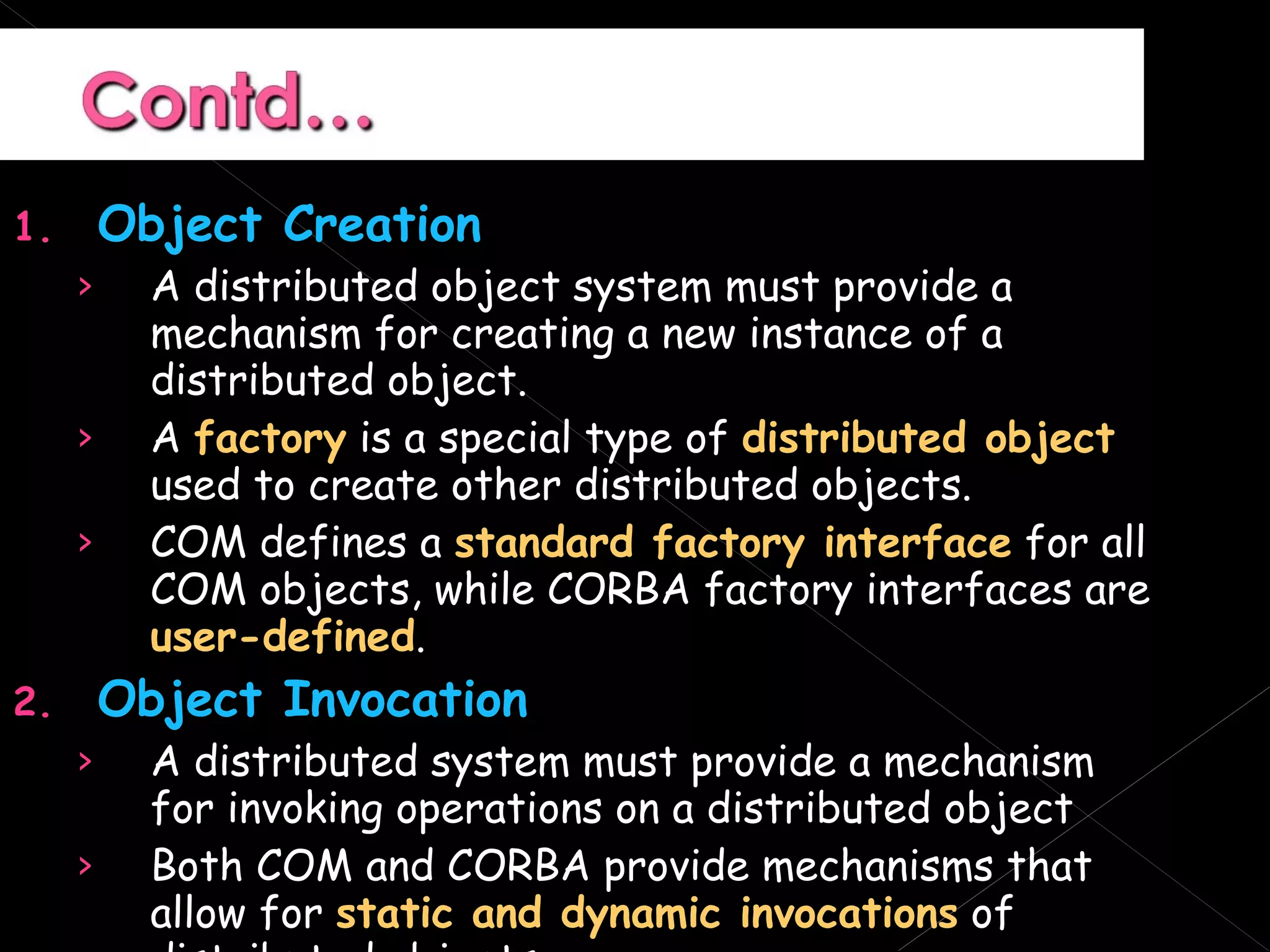
The document discusses the key similarities and differences between COM and CORBA distributed object systems. Both COM and CORBA provide mechanisms for remote object access through proxies, stubs, and skeletons. However, COM relies more on Windows registry registration and binary type libraries, while CORBA focuses on vendor-neutral interface definitions and does not depend on a specific operating system.






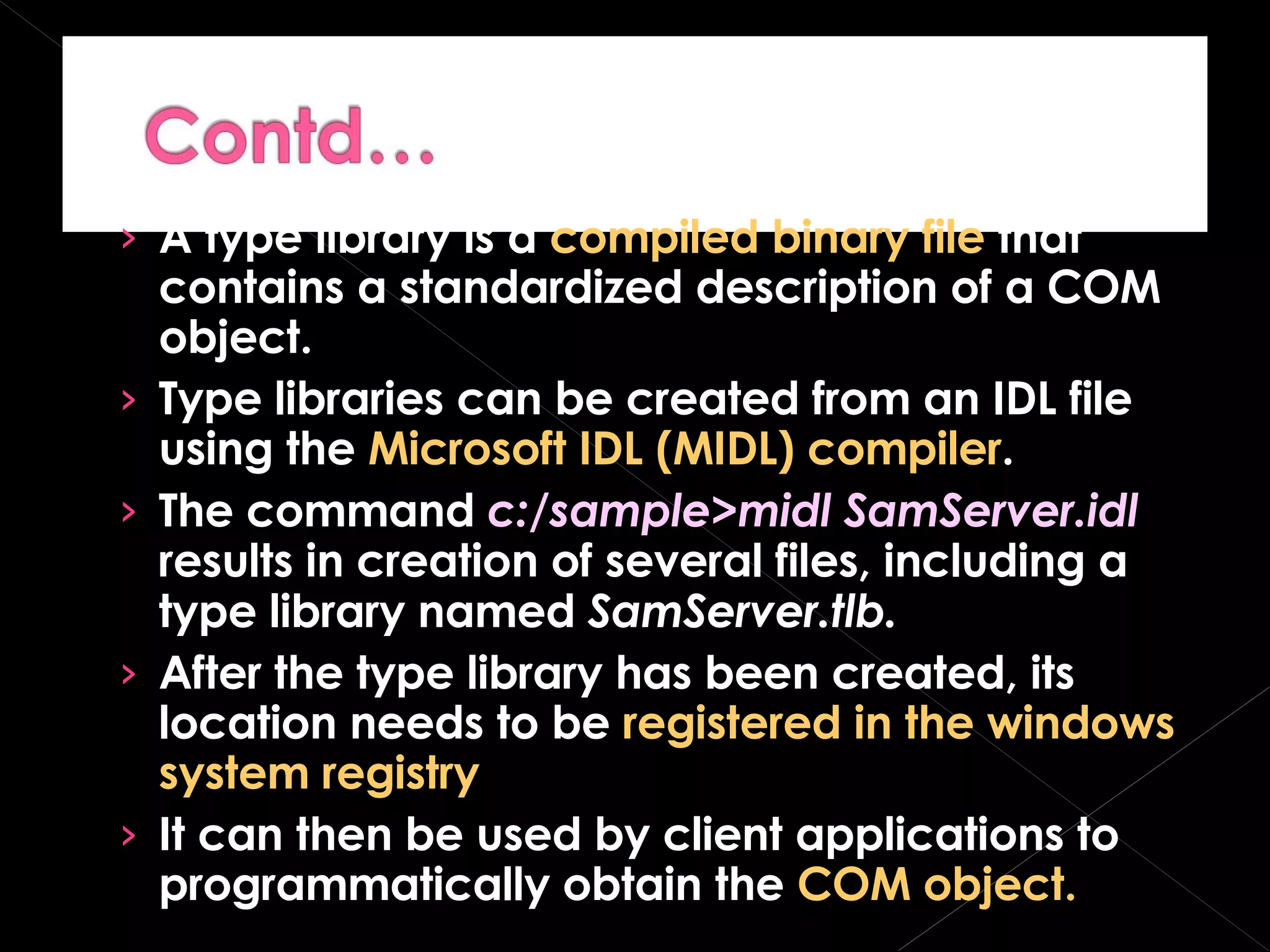
![IAccount Interface is given below, [ object, uuid(B5F3E2FE-B376-1101-BBIE-00207812E629), oleautomation, helpstring(“IAccount Interface”), pointer_default(unique) ] interface IAccount: IUnKnown { [propget, helpstring(“property Balance”) ] HRESULT Balance([out,retval] double *pVal); [propget, helpstring(“property Name”)] HRESULT Name([out,retval] BSTR *pVal); [helpstring(“method Deposit”)] HRESULT Deposit ([in] double amount); [helpstring (“method withdraw”)] HRESULT Withdraw ([in] double amount); };](https://image.slidesharecdn.com/com-1207055396497845-3/75/COM-13-2048.jpg)