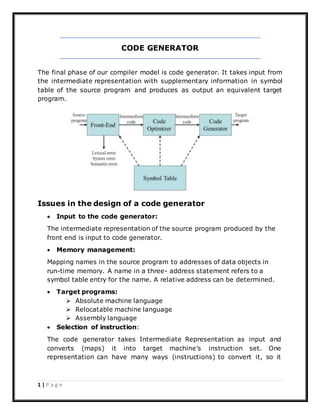
The document discusses code generation in compilers. It describes the code generator as taking an intermediate representation as input and producing target code. Key issues addressed include memory management, instruction selection and scheduling, and register allocation. The document also covers common compiler errors like lexical, syntactic, semantic and logical errors. It discusses different error recovery strategies used by parsers like panic mode, statement mode, and use of error productions.