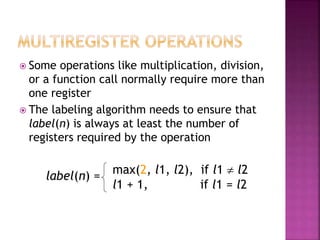
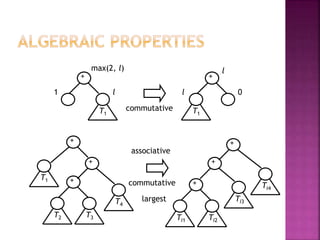
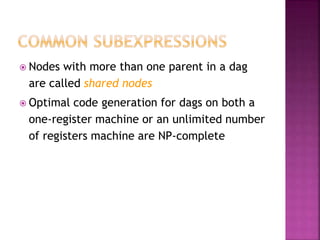
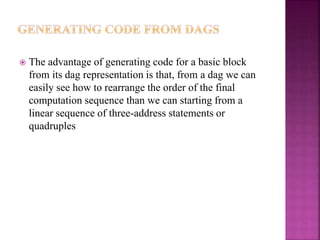
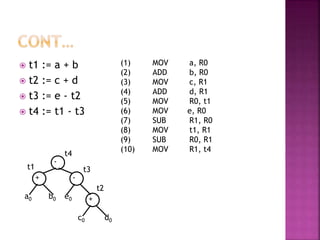
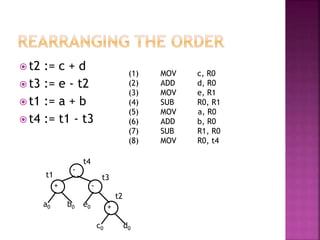
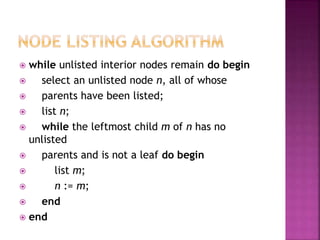
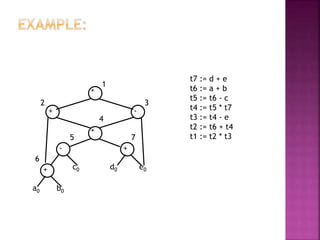
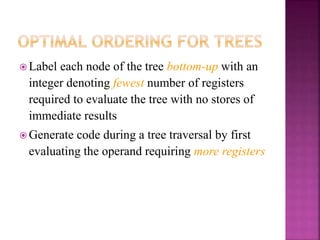
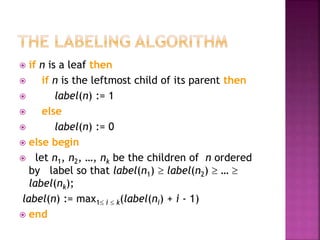
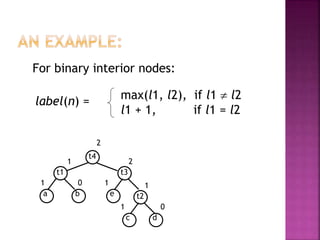
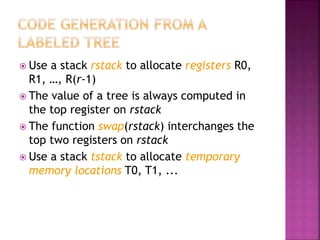
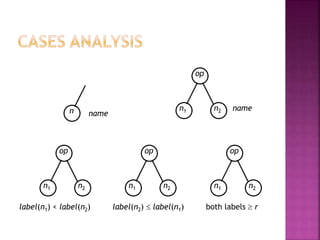
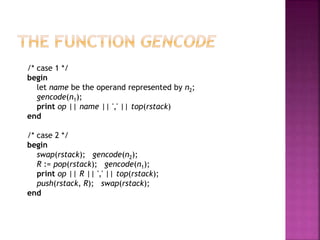
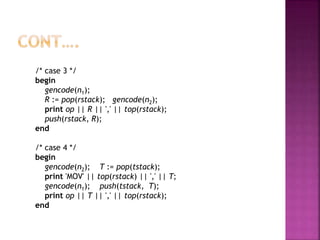
The document discusses code generation from a directed acyclic graph (DAG) representation of a basic block. It describes how a DAG makes rearranging the computation order easier than from a linear sequence. It also discusses labeling nodes in a tree representation with the minimum number of registers needed and generating code by evaluating nodes requiring more registers first. Finally, it discusses handling operations like multiplication that require multiple registers in the labeling algorithm.
![gencode(t4) [R1, R0] /* 2 */
gencode(t3) [R0, R1] /* 3 */
gencode(e) [R0, R1] /* 0 */
print MOV e, R1
gencode(t2) [R0] /* 1 */
gencode(c) [R0] /* 0 */
print MOV c, R0
print ADD d, R0
print SUB R0, R1
gencode(t1) [R0] /* 1 */
gencode(a) [R0] /* 0 */
print MOV a, R0
print ADD b, R0
print SUB R1, R0
t1
t4
t2a b
c
t3
d
e
1
2
1 2
0
1 0
11](https://image.slidesharecdn.com/generatingcodefromdags-170315040854/85/Generating-code-from-dags-15-320.jpg)