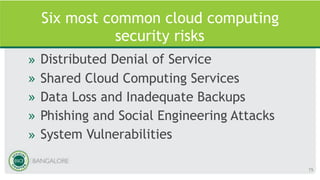
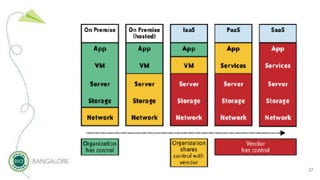
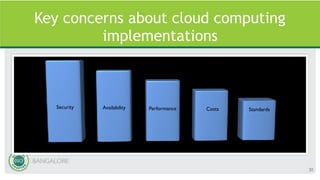
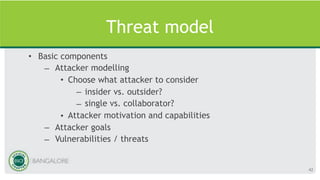
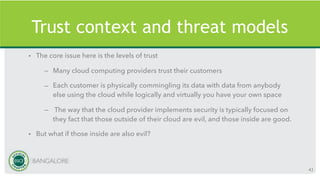
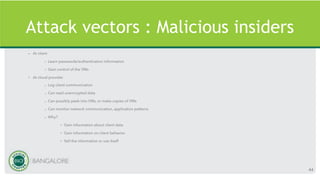
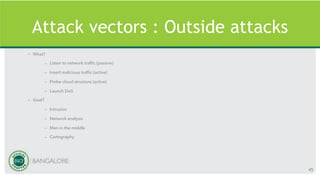
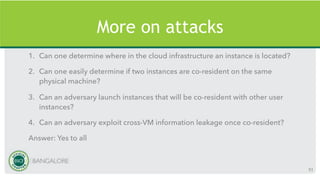
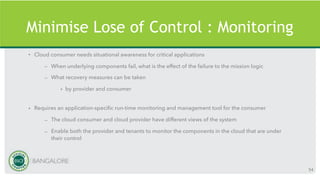
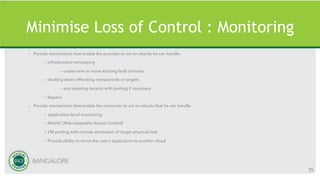
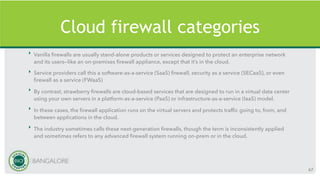
The document discusses emerging trends, statistics, and major breaches in cloud security, emphasizing the growth of security spending and the increasing focus on various aspects such as access management and incident response. Key case studies include Capital One's breach, highlighting insider threats and misconfigured resources, alongside notable earlier breaches from companies like Microsoft and Dropbox. Additionally, it examines common security risks, concerns of trust, and the challenges posed by multi-tenancy in cloud environments.