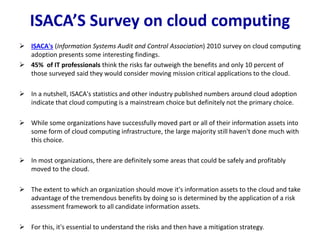
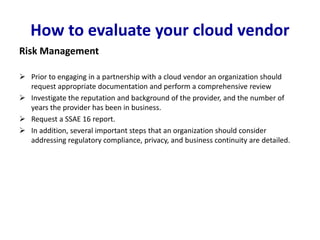
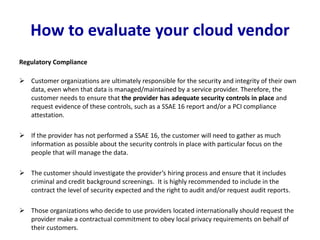
Risk management is essential for cloud computing due to security, privacy, availability and compliance risks. Organizations should thoroughly evaluate cloud vendors to ensure adequate controls over data access, regulatory compliance, privacy, disaster recovery, and contractual obligations. A risk-based approach is needed to determine which applications and data can be safely moved to the cloud. Major cloud providers like AWS have robust security and risk management programs, but due diligence is still required from organizations.